CIDR IPs not accessible over the Internet
-
I was attempting to perform an update on pfSense earlier this morning and for whatever reason the update failed and when it came back up, everything was hosed. So I booted from CD to reinstall and now I'm running into issue with getting my CIDR set up working again.
I have 3 NICs, one for the WAN, one for the LAN, and the other for my CIDR block.
From the LAN, I am able to access the Internet just fine. In addition to that, I'm able to access web sites that are available on an IP address that is part of the CIDR block.
From a device that does not reside on the network however, I'm not able to access the web sites that are on the CIDR network. I tested this by turning WiFi off on my phone and I'm not able to access the sites.
For a while, I was unable to even ping the CIDR gateway from a server that is part of the CIDR, but I'm able to now.
I've been pulling my hair out all day and can't think of anything else to try. Can anyone supply any suggestions?
-
What do you mean by "CIDR"? As far as I know, CIDR is just a way of expressing subnets and addresses, instead of the old class A, B & C method.
-
I received a CIDR block from my ISP that I can use to assign IPs to my servers behind the pfSense box.
-
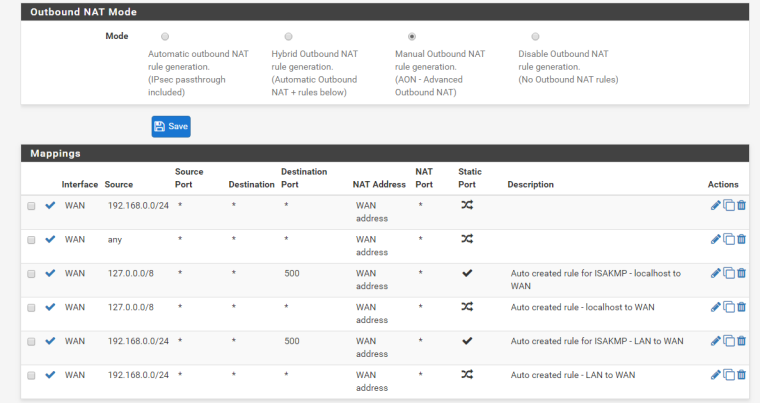
So you got a public IP block that is routed to you.. Say a /29 and you put this on an OPT interface on pfsense. What rules did you put on the interface? Did you turn off automatic outbound nat for this block.. Or pfsense might try to nat it to the public IP you have on the wan.
Post up your outbound nat and your firewall rules on your wan and your optX where you put this cidr block
-
My NAT rules
Source Source Port Destination Destination Port NAT Address NAT Port Static Port Description
WAN 192.168.0.0/24 * * * WAN address *
WAN any * * * WAN address *
WAN 127.0.0.0/8 * * 500 WAN address * Auto created rule for ISAKMP - localhost to WAN
WAN 127.0.0.0/8 * * * WAN address * Auto created rule - localhost to WAN
WAN 192.168.0.0/24 * * 500 WAN address * Auto created rule for ISAKMP - LAN to WAN
WAN 192.168.0.0/24 * * * WAN address * Auto created rule - LAN to WANFor my firewall rules, I currently have everything open until I get this worked out.
Protocol Source Port Destination Port Gateway Queue Schedule
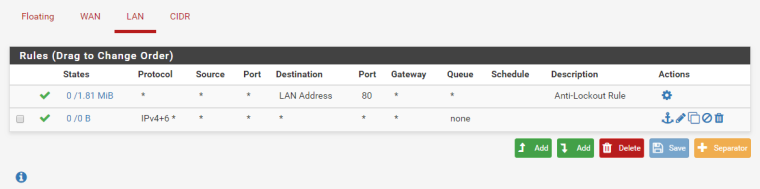
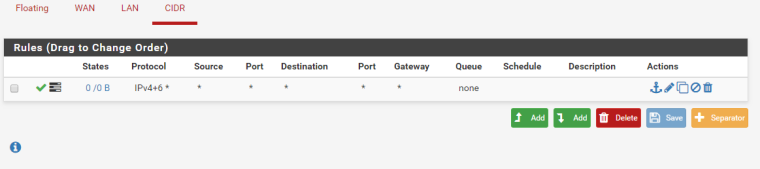
IPv4+6 * * * * * * noneI have the same rule for all 3.
-
How hard is a screenshot vs trying to read your ascii art.. This looks like your trying to NAT anything traffic you see to your wan
WAN any * * * WAN address *Which you would NOT want to do if your have some public 1.2.3.0/29 block
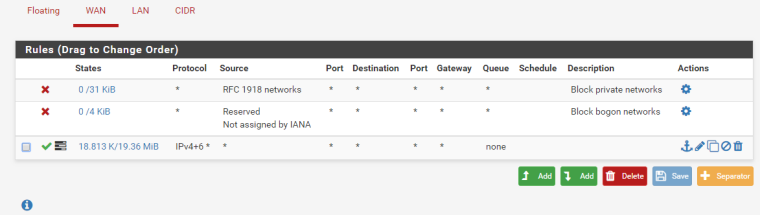
You have a ANY ANY rule on your wan?
-
-
Yup wan rules BROKEN.. You would never put a wan any any rule..
Your outbound nat is Broken as well - your saying hey take that 1.2.3.x IP that is my routed cidr and NAT it to what my WAN IP is.. -
Sorry, I'm somewhat new to this. So what would you recommend?
-
Remove that outbound nat that says ANY... Can put in firewall rules on wan that allow what you want to allow inbound to your cidr network.. If that is nothing then there should be no rules on your wan.
You sure this is routed to you? What do you have /? What is on your wan - this is a transit network?
So for example your wan IP is what 1.2.3.x/? and your routed cidr is what 4.5.6.0/? you sure they routed this to you and not just gave you this netblock..
-
Thank you very much for your help.
-
Yes, this was working this morning just fine. The problem occurred when my pfSense update failed and I was forced to reinstall. You got me up and running once again with your suggestions, so thank you.
Now, I can take steps to lock it down.
-
Never outbound NAT from source any either.