Want to Block 1IP from using Internet when VPN goes down
-
ugh ill post picture.. like i said its nto offline
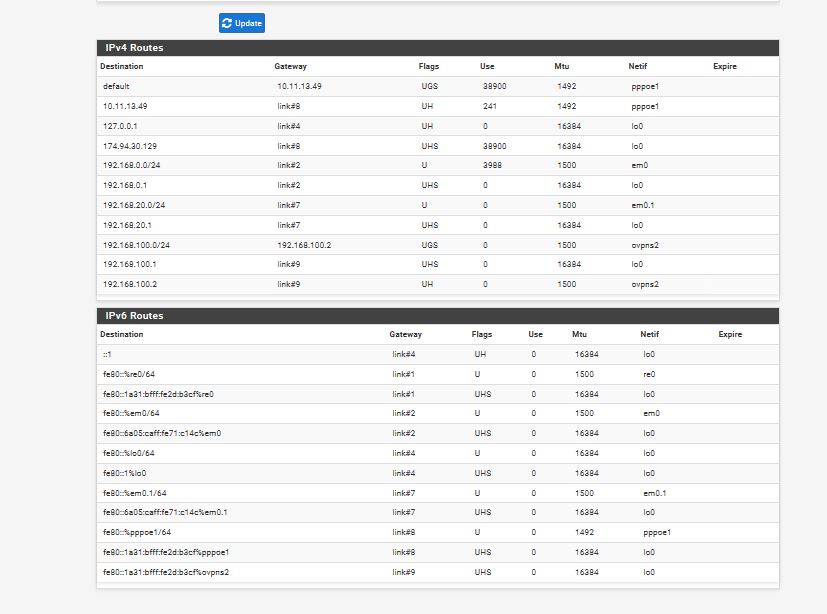
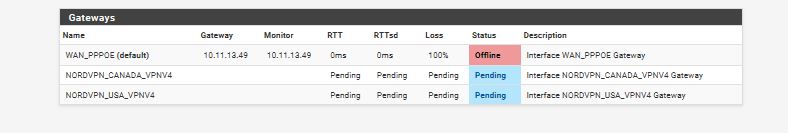
its up and you see 10.11.13.49 gateway monitor is 10.11.13.49
so its up but just a sec ill get you a photo
thats why i ask where else could it be blocking? -
Post the routing table from Diagnostics > Routes.
-
if i upload the config file is there an editor for you or diagnostic program to see whats wrong?
as reboots dont help
sorry takes a bit to send back pics
as i restore the few days ago config to send you the pics but load up the config file we worked on in this topic and it just glitched or something and i wanna be able to figure it out incase it has happened again.. as its happened in 2 other times last year but all i did was format and started over... but since i have bunch of stuff setup i dont wanna format.. i wanna find out what went wrong -
could it be because i use a gaming computer motherboard and non ECC ram... and while it was doing a save it saved a corrupt setting to block the internet..
as i always hear you want ECC ram for a server is it possible .. as i was looking at 1U Server supermicro but at 1200 + just to make pfsesne... my gaming computer under 500 was cheaper way -
ok found the problem well kinda...
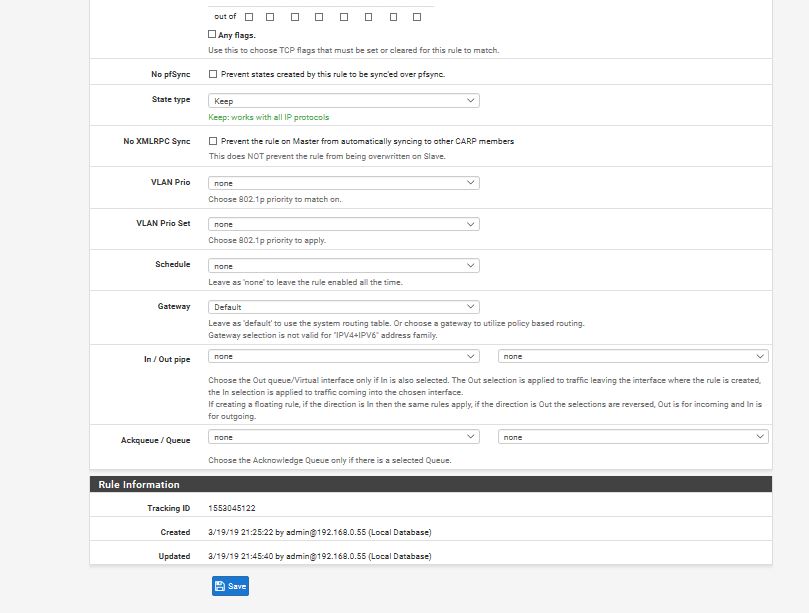
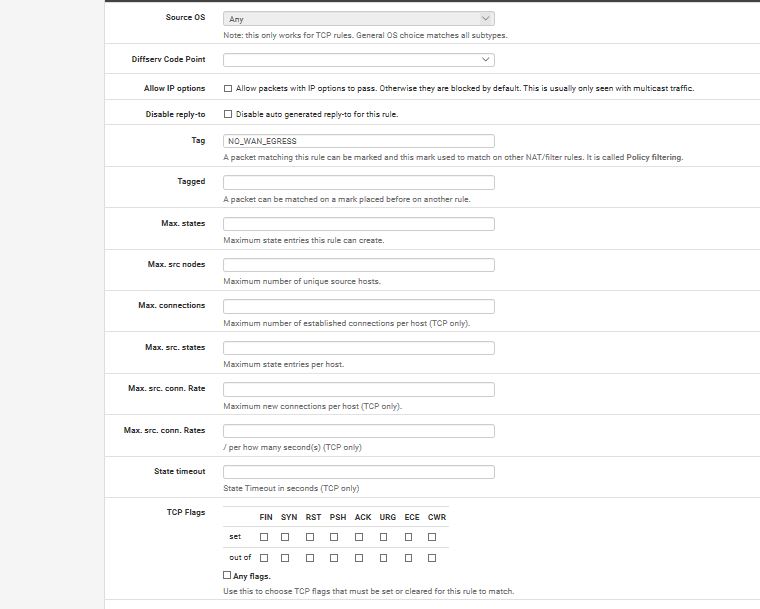
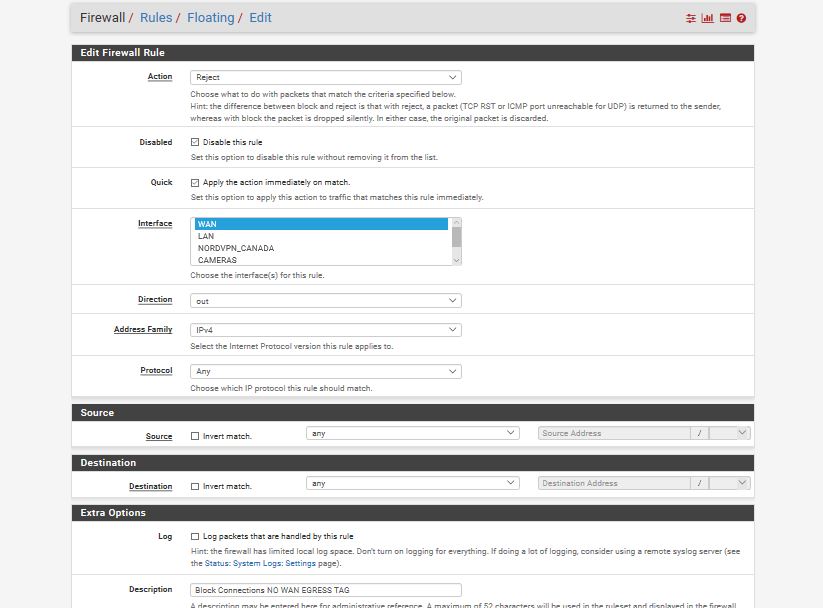
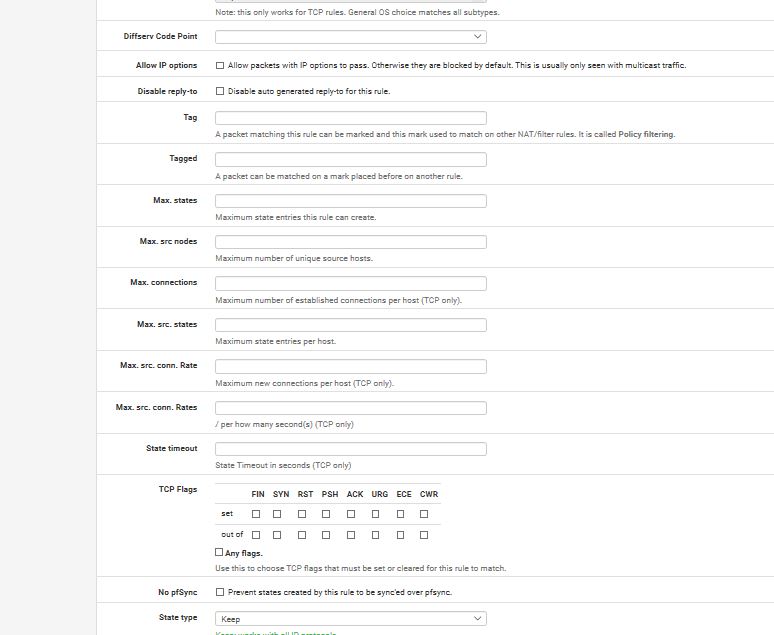
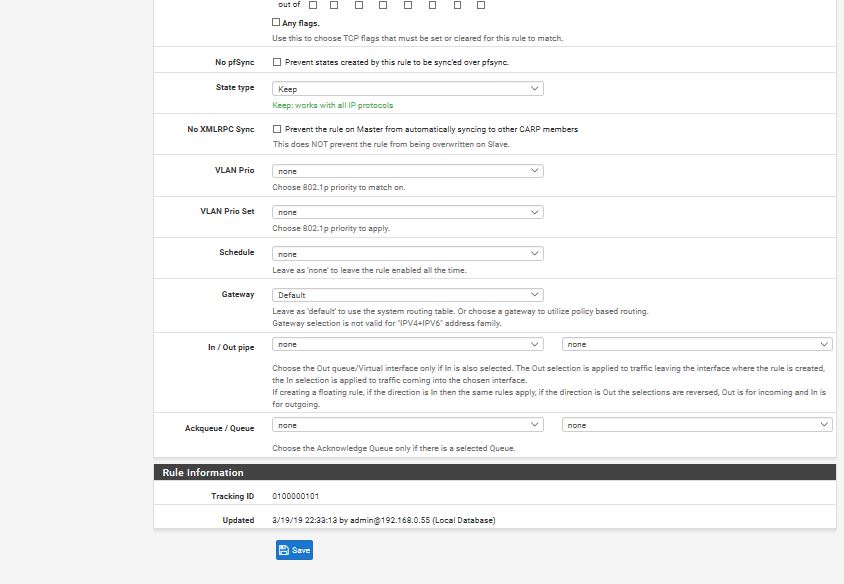
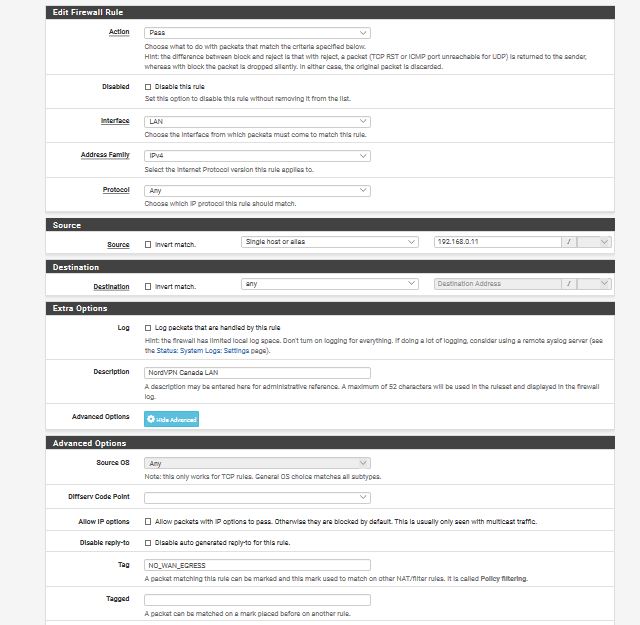
That Floating No WAN Egress is being applied when its not supposed to be calledand i tried scrolling up but i cant see the settings you told me but this is what i have.. ...
so even though no TAG is being called on any of the rules other then the 2 for 192.168.0.11
its like the rules are calling Tag No Wan Egress by default and not when its supposed to
-
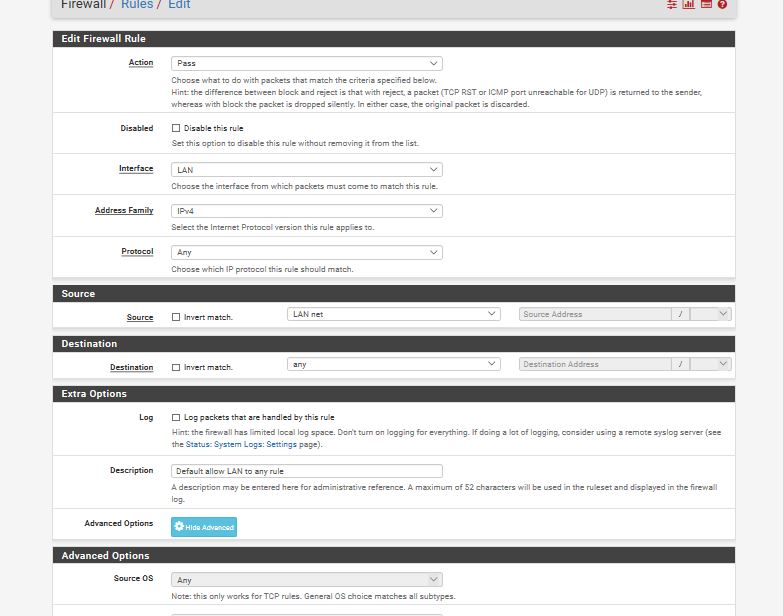
here is that default lan settings... even though the tag is blank its still calling that floating no wan egress because if i un disable no wan egress tag under floating
internet is blocked
its like its being called hidden in the background
-
here is the one ip rule that calls the tag that should only be called when vpn is down but seems to being called whenever it wants to
-
so what i found is
if i reactivate the Floating Rule No Wan EGRESS
internet works fine..but if i Do a reboot of Pfsense.. then that No Wan Egresss gets automaticlly loaded by default then blocks internet
then when i Disable Floating Rule
i get the internet backthen if i enable it internet seems to work fine and when i set to run VPN and then choose to disable VPN and restart it.. WAN is now 100% packet loss again
so i re disabled the Floating Wan Egressit seems it loads it up like a windows service without being asked to... is there another setting to set so it doesnt do that?
maybe something i didnt check off
-
Again, my suggestion is to save a backup copy of your current config and reset to defaults and start over. I really have no idea what you put where to break this and these screen captures of irrelevant data are solving nothing.
But before you do that, just put a LEGIBLE copy of /tmp/rules.debug in a chat to me please.
Diagnostics > Command Prompt
Execute
cat /tmp/rules.debugCopy / paste.
Thanks. -
ugh
well i gave you screen shots of
-Tag No Wan Egress you told me to type
-LAN Net Default of Pfsense
-NordVPN 192.168.0.11 with TAG No Wan Egressi was showing you each break down to show you that the Tag No Wan Egreess and i didnt do anything wrong..
and was showing you that No Wan Egress Tag gets loaded automaticlly not just when its supposed tobut ugh reset defaults then i gotta do all the Static Ip renamings i have too didnt wanna reset.. i wanted to fix this why
but ok ill get you the copy just a moment.. just frustrated
-
well you cant post rules its considered spam by your spam program forum.. i attached a text file of it hope it worksrules.txt
-
i didnt un gray the floating no wan egress so i dont know if that rule will show up
-
here is rules 2.. I enabled Floating No Wan Egress and re ran that debug cat thing you told me to do... hopefully you find my error as your smarter then me at this stuff
-
so 5 min after i enabled the No Wan Egreess Tag under floating options to do the rules2 for you
i lost internet to 100 percent loss
so its still loading it some how
-
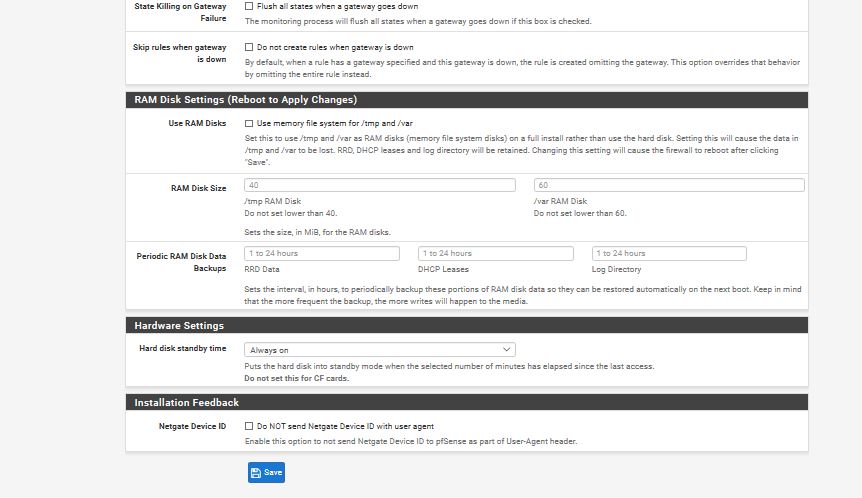
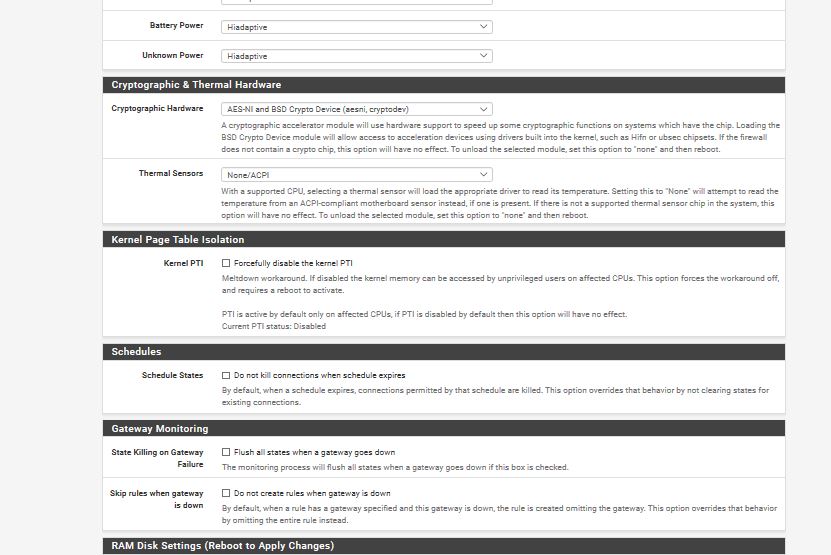
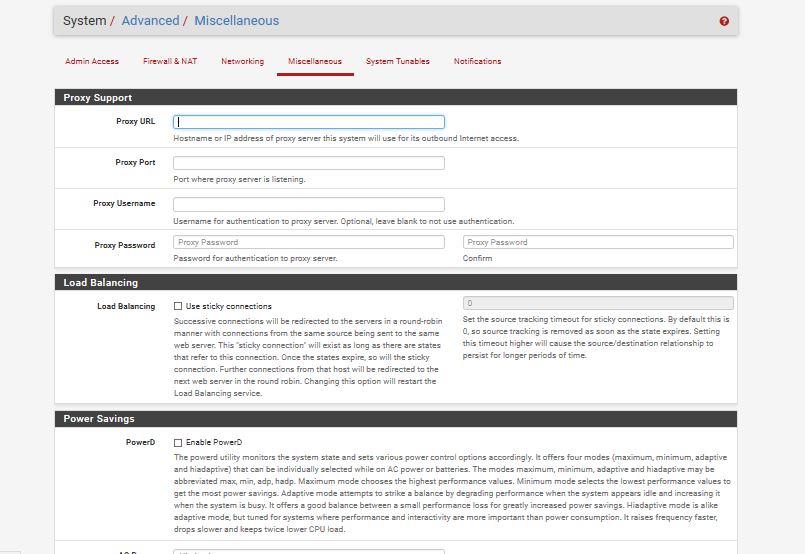
What do you have set for this:
System > Advanced, Miscellaneous, Skip rules when gateway is down
Look. This stuff is extremely complicated. You really have to know exactly what you are doing to pull this kind of policy routing off. You have multiple OpenVPN clients and you want certain LAN hosts to behave one way and certain LAN hosts to behave another.
The NO_WAN_EGRESS rules I sent will not do ANYTHING to connections that do not originate from that source host.
You are refusing my suggestion of starting over from the beginning.
You are policy routing everything from LAN to the OpenVPN gateway. is gateway monitoring enabled there? Does the system even recognize the OpenVPN is down? If not, it will continue to send the traffic out the OpenVPN.
"100 percent loss" is not a trouble description. I understand you are frustrated. More details might be necessary.
-
and sorry if the screen shots are irrevelent to the settings
as i been told i have to post screen shots of the settings i do.. as you guys arent willing to watch videos... and i got blasted last year for not posting screen shots of what i was doing..was only trying to show you the settings i set... didnt mean to make it irrvelent.. to me they were relevent as its the stuff you told me to set..
sorry about that -
It would help if you followed my instructions exactly.
Derelict about 19 hours ago
Make a rule for that specific source host above the NORDVPN rules.
Make it just like the other rule, but with a source of that host address instead of LAN net, policy routing to NORDVPN.
Add the following advanced option:
Tag: NO_WAN_EGRESS
Make a floating rule in Firewall > Rules, Floating
Action: Reject
Quick: Checked
Interface: WAN
Direction: Out
Source: Any
Destination: AnyDisplay Advanced
Tagged: NO_WAN_EGRESS
TAG on LAN
TAGGED on WANThe former SETS the tag
The latter MATCHES the tag previously set by the LAN rules. -
i get that t he No Wan Egree rule only to that
but ill make a video and prove your wrong its not doing that.. its doing it on its own cuz your not believing me..
and i didnt refuse of starting over.. i told you ok in the one reply i said i didnt wanna cuz thats alot of typing and figuring where all the settings god..
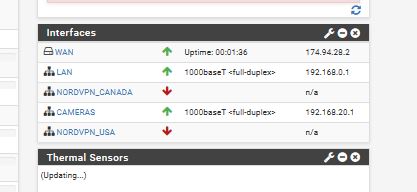
yes I got different openVPNs
so what i have is
WAN ----> Only For Game Consoles
NORDVPN USA for entire Network
NORDVPN CANADA for entire Network these 2 is when i wanna be in usa or in canada
OPENVPNSERVEr ---->> so i can Remote access my network from away from the homeand i wouldnt know if gateway monitoring enabled..
and ya the system knows when NordVPN goes down... either i get a email from my ISP my son did something bad which i told him to stop ... or my internet goes down and then im using my WAN IP address so it falls over
i only had issues because you told me i had the rules set wrong for when VPN goes down and to make sure no Internet leaking happens..
and then i find out now that the Floating rule seems to automaticlly load ...
if i disable all the rules minus that lock out rule Floating Rule No Wan Still gets loaded and 100% packet lossbut there is monitoring as there is a monitoring IP when i showed the Gateway images
but here the pics of the misc's
-
i think i found the error on floating
i put TAG NO_WAN_EGRESSnot TAGGED NO_WAN_EGRESS
guess thats the reason it automaticlly Blocks because i put NO_WAN_EGRESS under TAG
i really hate dislexia i read Tagged as Tag... ill try that
So Tag means anything on the Local Network... and TAGGED means anything going out on the internet
ill re try again thank you for being patient
-
nope didnt work
having TAG No Wan EGress for the 192.168.0.11 Under NordVPN one
and having TAGGED No Wan Eggress under Floating
just lets the 192.168.0.11 get WAN internet instead of blocked..
shouldnt the Rule be also set to TAGGED not TAG?