Multiple OpenVPN mapped to different WiFi SSID (Unifi)
-
@johnpoz do you have AP only ? in my case yes .
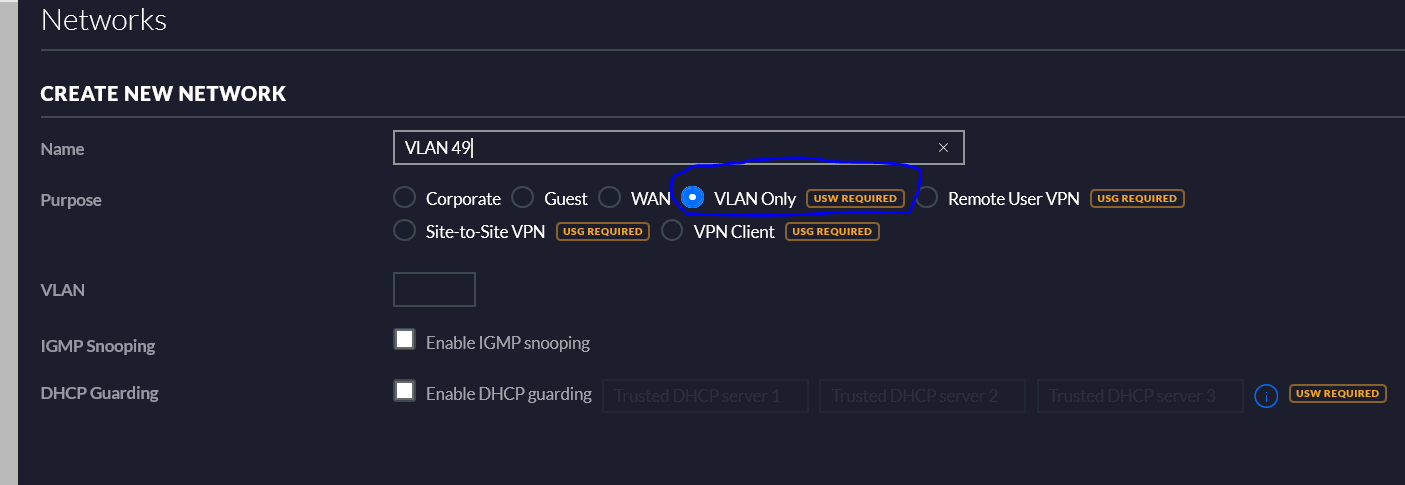
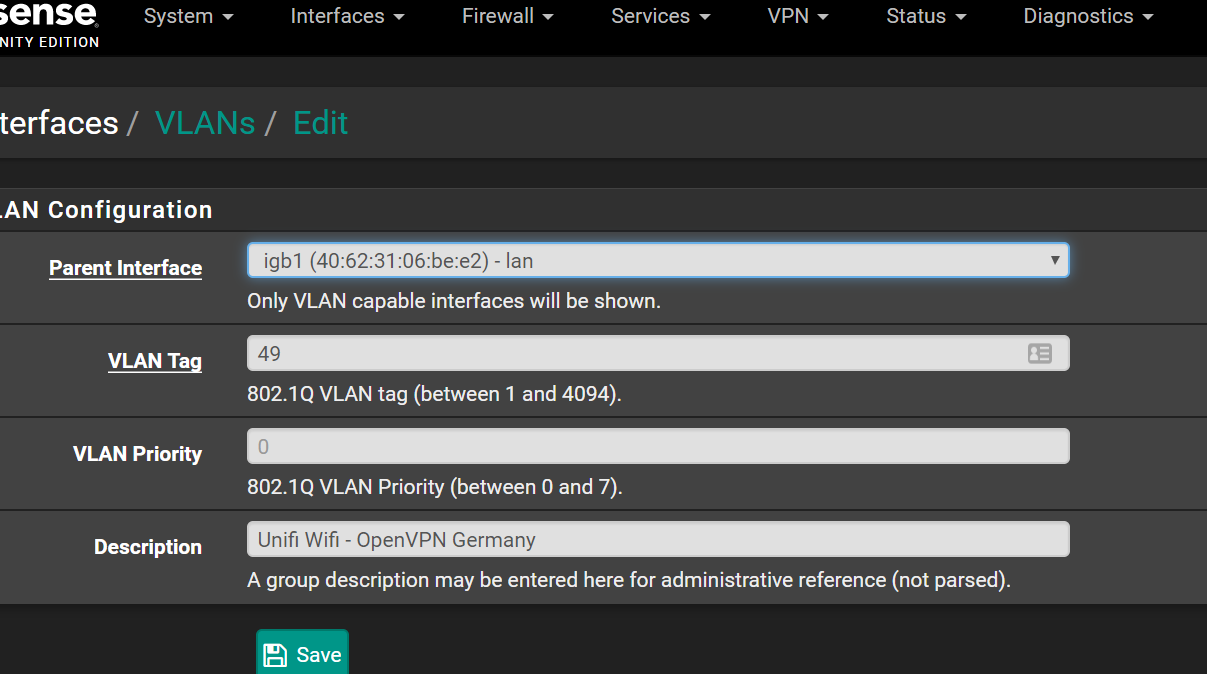
I have created a new SSID , tagged on the Pfsense VLAN .
Now if I want to create in Unifi a new network (VLAN only), different from LAN , require an Unifi switch .
On the Pfsense VLAN, the firewall rule is pretty straight forward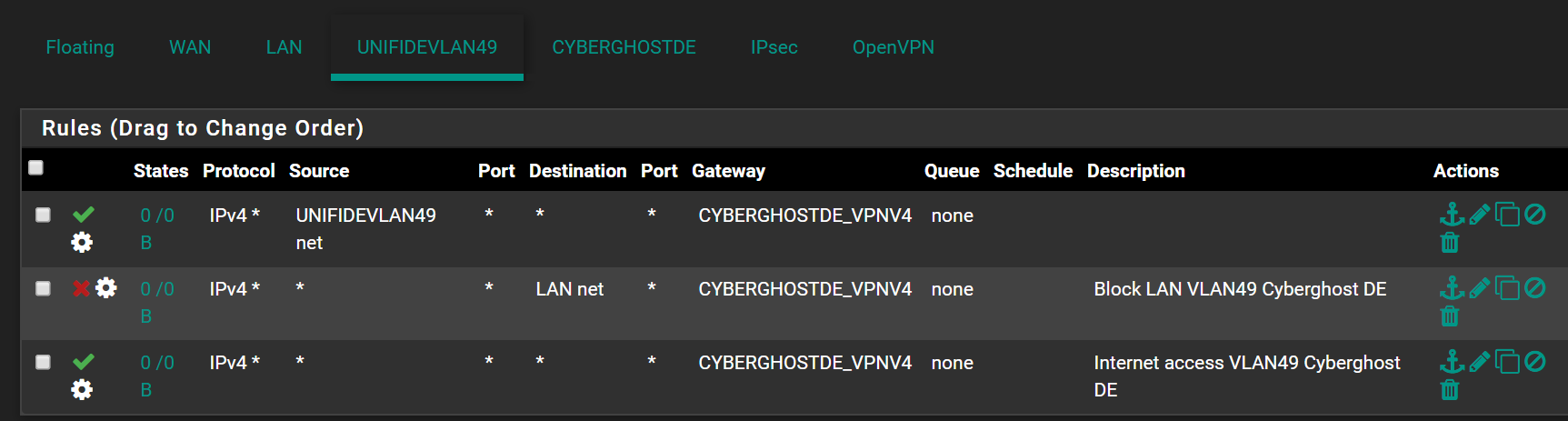
-
dude you do not need to do that... You only need to do that if you have a switch..
Let me log in and will post screenshot.
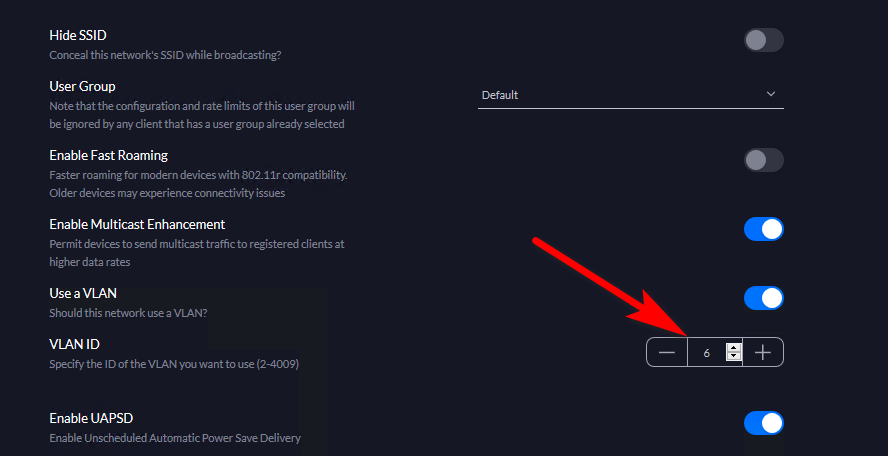
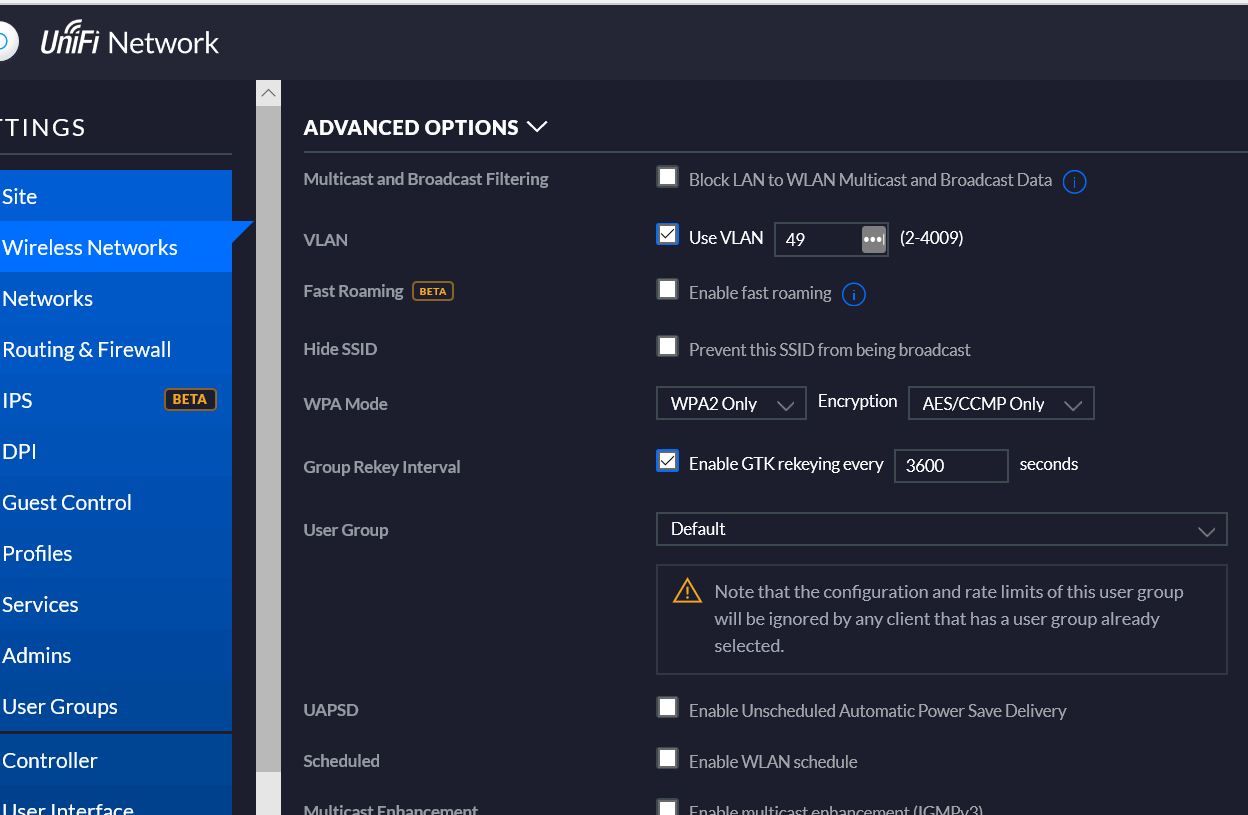
You set the vlan ID on your wifi network
That network tab on the controller has nothing to do with it.
-
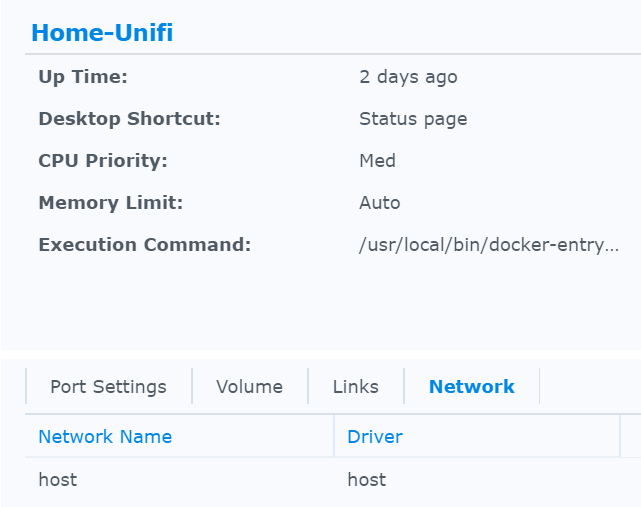
@johnpoz I guess I got your point. And indeed this is how I have configured it that struggles to work . I'm running a Docker version of the controller (does not really matter, is bridged to LAN)
-
If your client is not getting an IP from that vlan ID... Then you have a problem on your switch, or your vlan setup on pfsense or your not running dhcp...
All there is to do is set the vlan ID on your wireless network, and tag that to the AP..
-
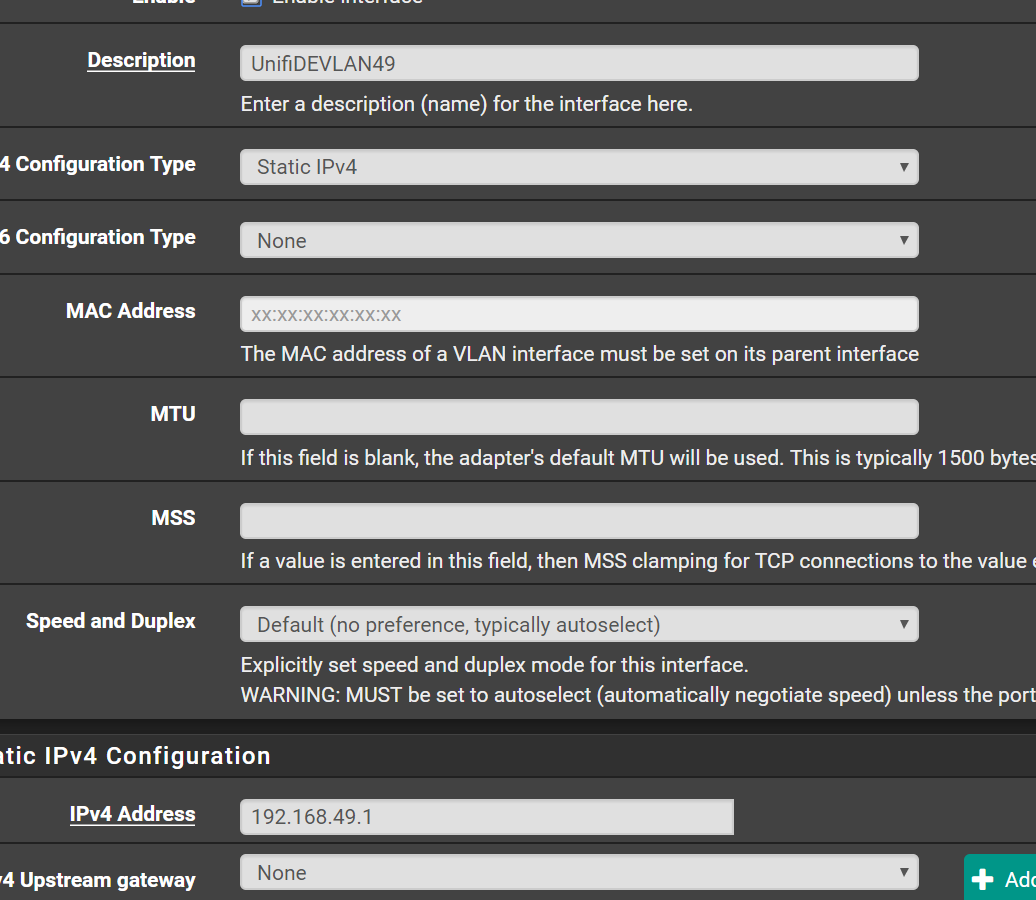
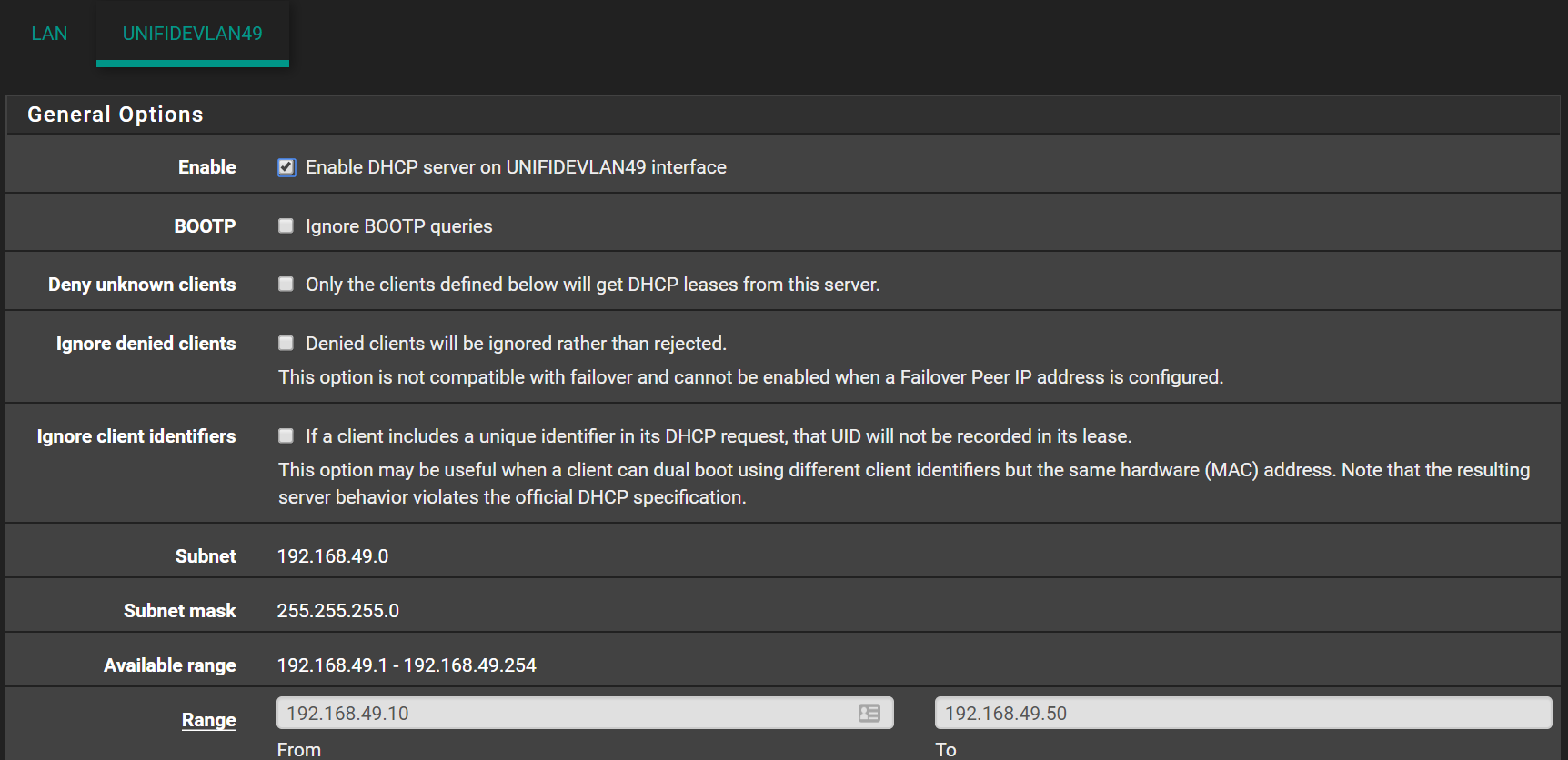
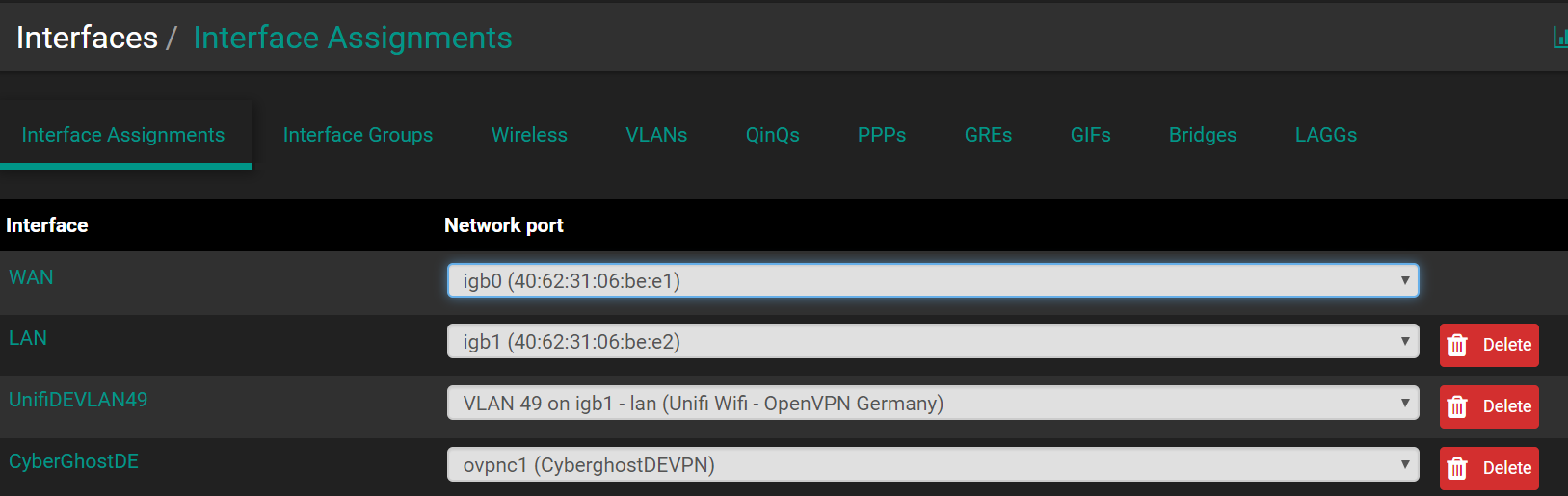
@johnpoz There is no switch in between . Unifi AP straight forward in Pfsense LAN igb1 . DHCP server is running on that VLAN
-
So how exactly are you provisioning the AP? Its IP is also on vlan 49?
The AP talks to the controller normally via untagged... Where is your controller if you have the AP directly connected to your pfsense?
-
@johnpoz nope. AP is on the default LAN /24 . Works fine in that LAN.
-
And where is your controller? If you have the AP directly connected to your lan interface on pfsense? With no switch?
Draw up how you have everything connected...
-
@johnpoz Controller is running on Docker on a bridged LAN . Same main LAN subnet 192.168.1.0/24 . Just on it's own port 8443.
WAIT : I just remeber that I got a Tomato as bridge in between . Let me create a VLAN 49 there on the br0
-
Try a packet capture on VLAN49.
-
Well yeah is that bridge you setup going to pass the tags? Or anything... How do you have this all connected... Why would you be bridging on your tomato box?? And does it even support vlan tags... Dude get a SWITCH!!!
How do you have a "lab" and not have a switch that does vlan tags?
-
@johnpoz I got a switch . I have to connect it . Mostly is all virtual but I will get this switch up and test again .
-
This is pretty simple/basic stuff here... You tag the vlan, that is what is on the wifi ssid with that tag.. Been using these AP since 2014 ;) I just had to look that up for another thread... Got an old square uap-ac back then.. tagging ssid worked the same as it does now..
If its not working your loosing your tag somewhere, didn't set it up, etc. etc.
-
@johnpoz Indeed . upgrading this netgear firmware(with PoE) and I will put it in the game .
Forgot I had this tomato device in bridge plugged somewhere . Sorry about. -
@johnpoz all is working as intended. Again thanks for the help .
Last thing to solve is within the OpenVPN connection , is how to use my Pfsense / Pfblocker as DNS in the tunnel . Not sure where to look in this regard .
After that , I can export this config and us it in private LAN .Thanks again
-
You want unbound to use your vpn connection for it lookups?
-
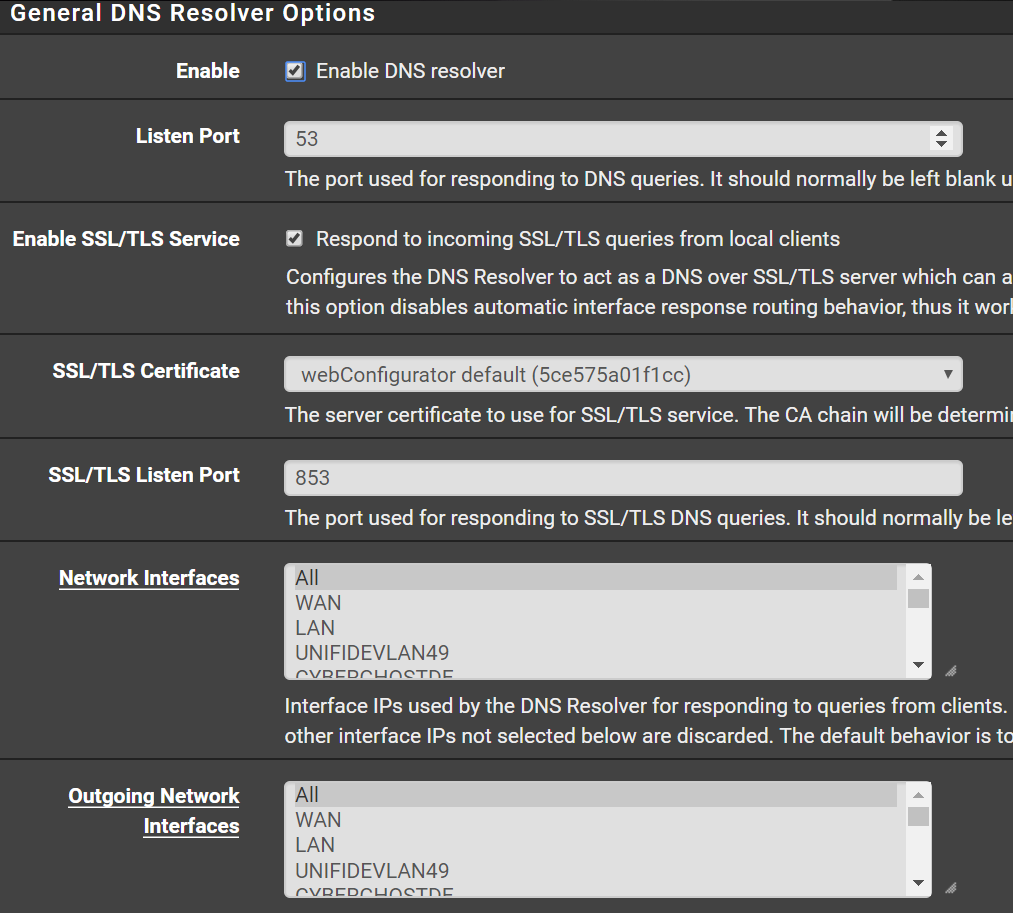
@johnpoz correct. I'm playing with settings and rule but seems that I got no luck . In DNS resolver (over TLS) , all the network are selected and outgoing network interfaces are selected. No VPN providers DNS are set in the general config . I do not allow clients to override Pfsense DNS default DNS via FW rule
-
Should be pretty much this :/
-
If your going to forward through a tunnel... Why would you want that to go through another tunnel? I don't get the point other than you want it ever freaking slower?
-
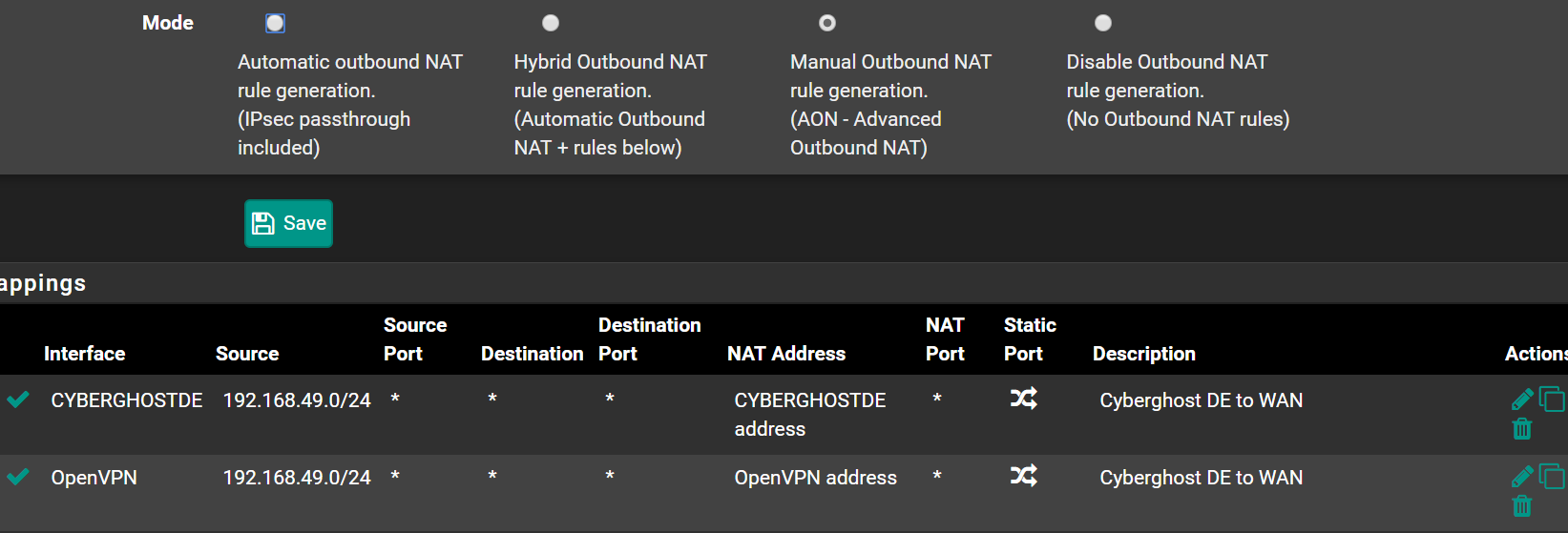
@Antonio76 I have a similar situation, with different VPNs to different countries on different VLANs. The way that Unbound works is that it will send queries out to all the outgoing interfaces, and the way I understand it, it will use the first reply.
This is an issue if you want to go to multiple countries. If I am on my local network, I want replies from local DNS servers, and if I'm on my VPN to the US I want replies from DNS in the US. If you have a single unbound resolver. the server farther away will never win (my VPN to the US has about 250 ms ping time from here).
What you want is queries from a particular VLAN to only be sent out via that VLAN's gateway (i.e. routed over that VPN) but as near as I can tell you can't do that with a single instance of unbound. My solution was to run a separate DNS server (in a VM in my case) on each VLAN to ensure that queries are only sent through the proper gateway. You can also run multiple DNS servers on pfsense if you enable both the forwarder (dnsmasq) and resolver (unbound). You could also install bind to get a third. You would need to run each on a separate port of course.
I've never played with bind, but it's possible that with the multiple views you might be able to route it correctly with a single server. I just don't have any experience with it.