Multiple OpenVPN mapped to different WiFi SSID (Unifi)
-
If your going to forward through a tunnel... Why would you want that to go through another tunnel? I don't get the point other than you want it ever freaking slower?
-
@Antonio76 I have a similar situation, with different VPNs to different countries on different VLANs. The way that Unbound works is that it will send queries out to all the outgoing interfaces, and the way I understand it, it will use the first reply.
This is an issue if you want to go to multiple countries. If I am on my local network, I want replies from local DNS servers, and if I'm on my VPN to the US I want replies from DNS in the US. If you have a single unbound resolver. the server farther away will never win (my VPN to the US has about 250 ms ping time from here).
What you want is queries from a particular VLAN to only be sent out via that VLAN's gateway (i.e. routed over that VPN) but as near as I can tell you can't do that with a single instance of unbound. My solution was to run a separate DNS server (in a VM in my case) on each VLAN to ensure that queries are only sent through the proper gateway. You can also run multiple DNS servers on pfsense if you enable both the forwarder (dnsmasq) and resolver (unbound). You could also install bind to get a third. You would need to run each on a separate port of course.
I've never played with bind, but it's possible that with the multiple views you might be able to route it correctly with a single server. I just don't have any experience with it.
-
If your wanting a client to use dns from vpn X... Then have the client ASK for dns he is doing down the tunnel.. Not sure how you expect unbound to know which interface to use for which client.
Set your dns on the CLIENT!! Simple via dhcp or actually set it on the client.
Or you could set it up with views on unbound.. Its had view support for awhile, then yes specific forwarders for each view.. But your not going to be able to do that in the qui, and just way simpler to set the dns on the client. I have some threads about here setting up views.. Simple enough to do.. If that the route you want to go - but why?? Just set it on the client.. And let your unbound resolve for your normal clients that are actually using your wan.
This is specific SSID for clients to use vpn X, then on your dhcp server for this vlan - just hand out the any dns you want your clients to ask.. Not Pfsense IP, and that query will go down the vpn tunnel.
-
@johnpoz I think you misunderstood what I said, but if there's a simpler way to do it I'm willing to learn.
I have three subnets - 192.168.2.0/24 is my local ISP, 192.168.3.0/24 is a VPN to a VPS I have in the US, and 192.168.4.0/24 is a VPN to my parents' house, also in the US.
I set up three separate VMs running unbound, one on each of those subnets - 192.168.2.5, 192.168.3.5, 192.168.4.5. Clients on 192.168.2.0/24 get 192.168.2.5 from DHCP for instance.
My local one is set up as a recursive resolver, while my VPS-VPN one goes to Cloudflare (otherwise multiple queries at 250 ms each to recurse) and the one for my parents' queries their pfsense box's unbound on the other end.
This way I ensure that DNS queries on my VPN network only go through the VPN gateway.
Is there a way to do all that using just unbound in my pfsense instead? And also using pfBlockerNG? (I currently also have PiHole running on each VM)
-
@johnpoz your point make sense . I just forced the client to use PFsense as only dns . A FW rule is preventing to look up different DNS .
I set up my Pfsense to do not override DNS settings too on a client side . Sure I can revert but what is the point security wise ?
BTW I have investigated the DHCP part but got not internet if enabled explictly in the DHCP server . -
@mcarson75 Indeed I have installed BIND yesterday. Now I'm going to play around it .
Local DNS should is faster than VPN provider latency wise . I could dockerize a DNS server but goal is to let Pfsense handle this without mantaininng multiple componets. Actually I can dockerize a Pi-Hole too . Done already in past and works fine -
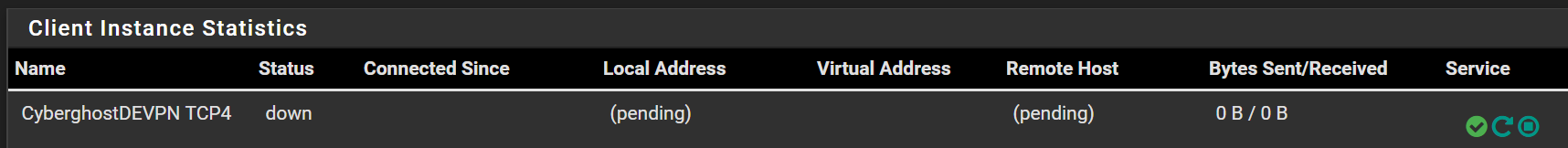
@mcarson75 no joy enabling BIND on the VLAN . OpenVPN won't start
-
Again unbound can do this for you via views, and sure bind can do it - and while bind package has as a views section.. Your still going to have to do the config by hand..
How many clients are you going to have on this special ssid vlan? You do understand clients normally cache their own dns.. Are the clients on this vlan iot type devices that do not have a local cache of their own..
My take is you want these special vpn ssids so you can circumvent specific geo restrictions.. Keep in mind that both unbound and bind are going to be using a common cache..
So you have client look up host.domain.tld from country A, now when you have client ask pfsense for host.domain.tld but you want the answer to be the IP for country B - its just going to get the cache from country A, etc. etc..
Your going to be better off just letting the clients ask some public dns via your vpn connection... Your doing a lot of extra work for what a couple of ms of query time for what exactly... I don't think these clients you have on this country based vpns are going to be doing a lot of "user" internet browsing where cache helps, etc.
-
Is not a Ms gain, is the DNSBL feature that I need . I can sacrifice time for resolve but keep the privacy and security is what concern me the most .
About the shared cache you are right
About DHCP:
Local DNS flush is not the issue . SSID displayed as connect, no internet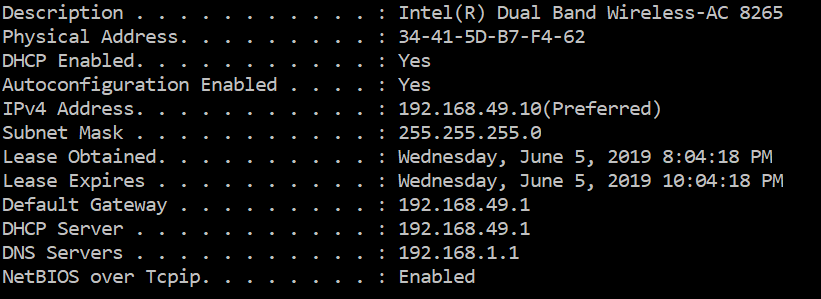
-
@Antonio76 It looks like you are blocking LAN in your firewall rules, but your DNS server is on your LAN. You should push 192.168.49.1 as your DNS server instead of 192.168.1.1. It should be running on all interfaces.
Alternatively you could add a firewall rule to allow access on port 53 only to 192.168.1.1.
-
@mcarson75 got it fixed via DNS forwarder (enabled) on that VLAN 49 . (I had it disabled)
Still debugging because beside click and click , I need to understand the Pfsense logic behind
-
@Antonio76 said in Multiple OpenVPN mapped to different WiFi SSID (Unifi):
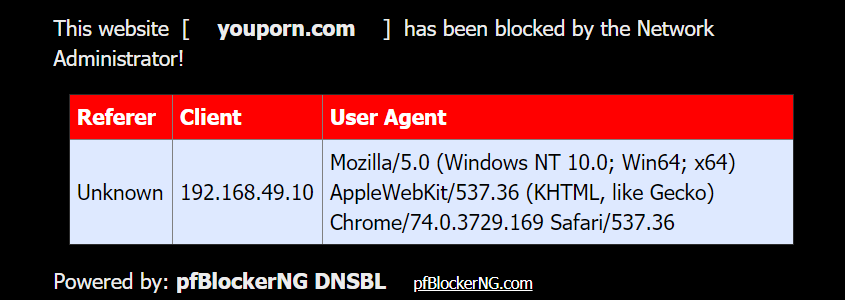
is the DNSBL feature that I need
And why are you going to youporn.com? I would assume you would only go there if you wanted too.. Do you have teenage boys or something your trying to filter?
-
My take is you want these special vpn ssids so you can circumvent specific geo restrictions.
It's not always about geo restrictions. I'm an American working in Asia. All my banks and other accounts are in the US. I just feel more secure accessing them from a US-based VPN. Perhaps it's overkill. But yeah, most of the time I am browsing internet on my VPN to the US, and I want an ad-blocker.
-
@johnpoz porn list is one of my DNSBL. Don't get me wrong for the test selection :) . but DNSBL was the goal .
Small kids, better be safe -
@mcarson75 said in Multiple OpenVPN mapped to different WiFi SSID (Unifi):
I just feel more secure accessing them from a US-based VPN.
That scenario is not what it sounds like he is wanting... He has multiple vpn connections to different countries... Sorry but that just SCREAMS circumvention...
Why do his small kids need to be surfing his allowed list through a vpn that goes to country xyz?
-
@mcarson75 correct. Blocking ADS, crypto javascript , privacy, tracking and porn for kid. Not fakenews because it actually it blocks what is left or real news ;) .
To be clear , I need access resource in other countries via DNSBL . That's the goal . No proxy PAC please . . :)
-
Why do his small kids need to be surfing his allowed list through a vpn that goes to country xyz?
You're arguing as to why you disagree with his use case. That's your opinion, but honestly I don't feel it's adding anything to the discussion about whether he can do what he wants or not.
-
@mcarson75 @johnpoz anyhow guys . i will further break this down , monitor , logging, grafana ntopng, SNMP and so on but indeed I have reached my goal in this LAB. I will reproduce at home . End goal is to leave my ISP GW as much as possible without leaks anything . Not because I have stuff to hide but because it's "dangerous" out there and often underestimated .
Pfsense is an mazing product . I will try to create an How-to post for Pfsense and Cyberhost VPN since there is near to 0 documentation about it beside this is an amazing VPN services .Thank you all for the time and help !
-
Not arguing the use case - trying to understand how freaking tight his tinfoil hat is!! To me its starting to cut off the circulation to his brain to be honest..
Keeping my kids from surfing porn has ZERO to do with forcing their traffic out a vpn to some other country than my own.. ZERO!!
You can for sure have unbound use VPN A for its queries - my point is trying to have it use vpn A for user B, and vpn C for user A or vlan X is just nuts!! For what possible reason is there to do such a thing..
Just have them all use vpn X.. If your trying to circumvent geo restrictions by using different vpns for different queries.. Your going have a shared cache.. So no going to work..
without leaks anything
This is NONSENSE word... you are "leaking" information everywhere you go, be it you use a vpn or not... Your leaking everything to the vpn.. But for some reason they are more trust worthy then your ISP??? Your leaking dns to wherever you forward.. So unless your resolving your handing over every dns query you do be it you came from a vpn or not to who is providing you dns... You understand there are more ways then what your source IP is to fingerprint you.
You are for sure leaking information to ever site you visit, etc. etc.
"leak" is just the latest buzz word to get money from the you know who... If you don't want to "leak" info - then don't get on the freaking internet ;)
edit: This topic just gets me so worked up ;)
So your worried about your ISP tracking you.. But you don't care that that your CC knows everything you buy when and where.. When you get more condoms, when you stop for a beer after work... When you drive through taco bell after the bar.. Guess you only use cash ever an all purchases?
You do understand your lic plate is read more than likely by every camera on the highway you drive be.. For sure at the toll boths.
Its more than likely your face is picked up at camera's every freaking were.. but for some reason your ok with paying company xyz $ a month so your isp doesn't know you went to pfsense.org... Just makes no freaking sense!
Oh btw your cell provider know pretty much every where your at 24 hours a day, and sells this info for profit... But again your worried about your isp knowing that you hit netflix.com
-
You can for sure have unbound use VPN A for its queries - my point is trying to have it use vpn A for user B, and vpn C for user A or vlan X is just nuts!! For what possible reason is there to do such a thing..
Just have them all use vpn X.. If your trying to circumvent geo restrictions by using different vpns for different queries.. Your going have a shared cache.. So no going to work..
I agree that if you are connecting to other locations via vpn then the only way to make dns work the way you want it to is to have separate dns servers/caches for each.