Multiple OpenVPN mapped to different WiFi SSID (Unifi)
-
Hello all ,
My first post and new to PfSense . So far I'm very happy .
What I'm trying to achieve in my home LAB, create multiple OpenVPN connections to different countries (2) using a VPN provider, to be mapped to different Unifi SSID . Each SSID will be named with the country where the OpenVPN connection is configured . In all OPenVPN connection cases, I would like to leverage PFblocker unbound configuration .
I have a switch capable of VLAN , eventually do all using the same cable will be best solution in my LAB .
If this is possible, thanks to pointing me on the right direction .Antonio
-
Yeah you just need AP capable of doing vlan and bing bang zoom, easy peasy lemon squezy ;)
if your AP can not do vlans, then you would need different AP for each ssid.
Good price point AP would be say the unifi AC-Lite model... Retails like $80 USD
-
@johnpoz Thanks ,
I will dig in this direction . Maybe the switch can do VLAN and just the Unifi AP understand the tag .
Will search this option .
Cheers,
-
If you have unifi AP your golden.. They do valns just fine.
If you don't monitor the uplink you can set them for 8 SSID per band, all could be different vlans.. With doing that per band, so 2.4/5 you could in theory do 16 different SSID all on different vlans.
Not really good idea from performance standpoint to run that many SSIDs... But if you need many many vlans on wifi you could also do dynamic assigned vlans via radius, etc.
But if all you want/need is 2 - yeah clicky clicky!
-
@johnpoz said in Multiple OpenVPN mapped to different WiFi SSID (Unifi):
dynamic assigned vlans via radius
dynamic assigned vlans via radius is a world to discover for me :) . I know Radius on Windows server for SSL VPN appliances. For my LAB case I have to dig in since sound a bit too advanced but I like the idea .
-
Yeah it works if your current on your AP and controller... I got it working via PSK ssid even, and then assigned vlan based on mac.. Using the freerad in pfsense.. While it could be useful.. I was thinking cutting down my SSID to only 1, and then having my iot devices assigned to their particular vlans based on their mac address..
And I still might go that route at some point.. I validated it "could" be done - but then never had the drive to actually implement it across the board ;)
There is something said to KISS, and since only currently have need of 4 different wireless networks.. Just doing it the old fashion way ;)
-
@johnpoz Hhhhee I like how you think. I'm also trying to to make it rationale and use as less as possible wired and simplify topology .
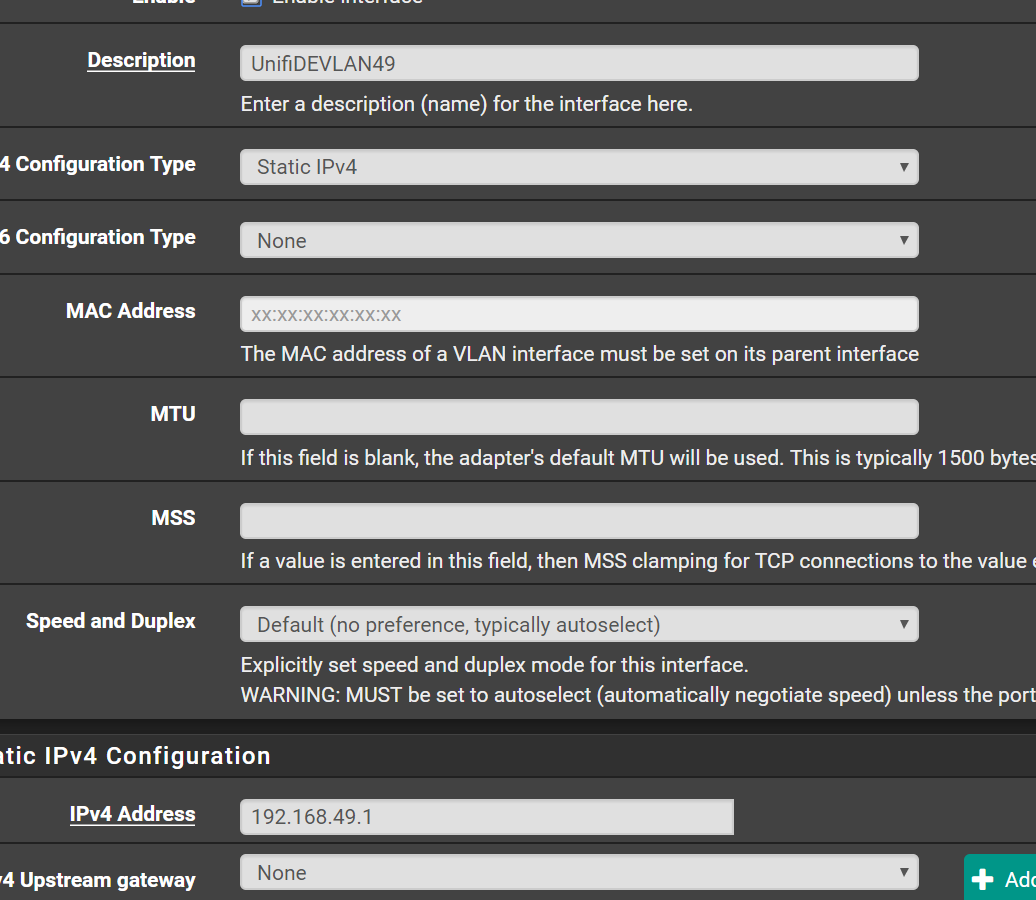
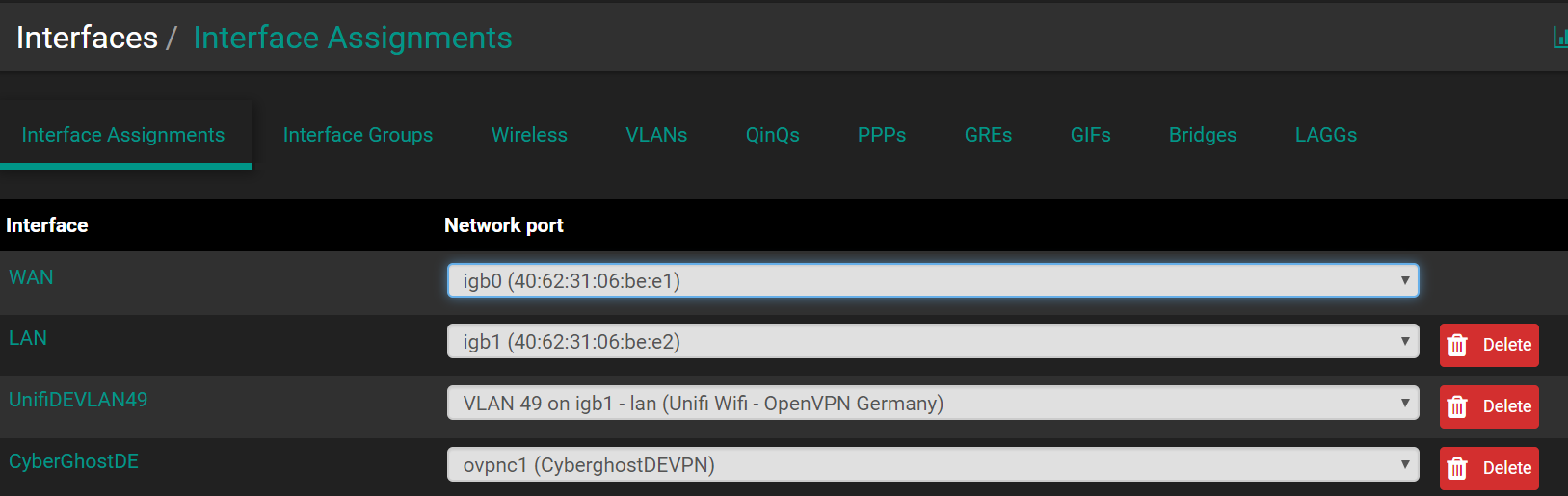
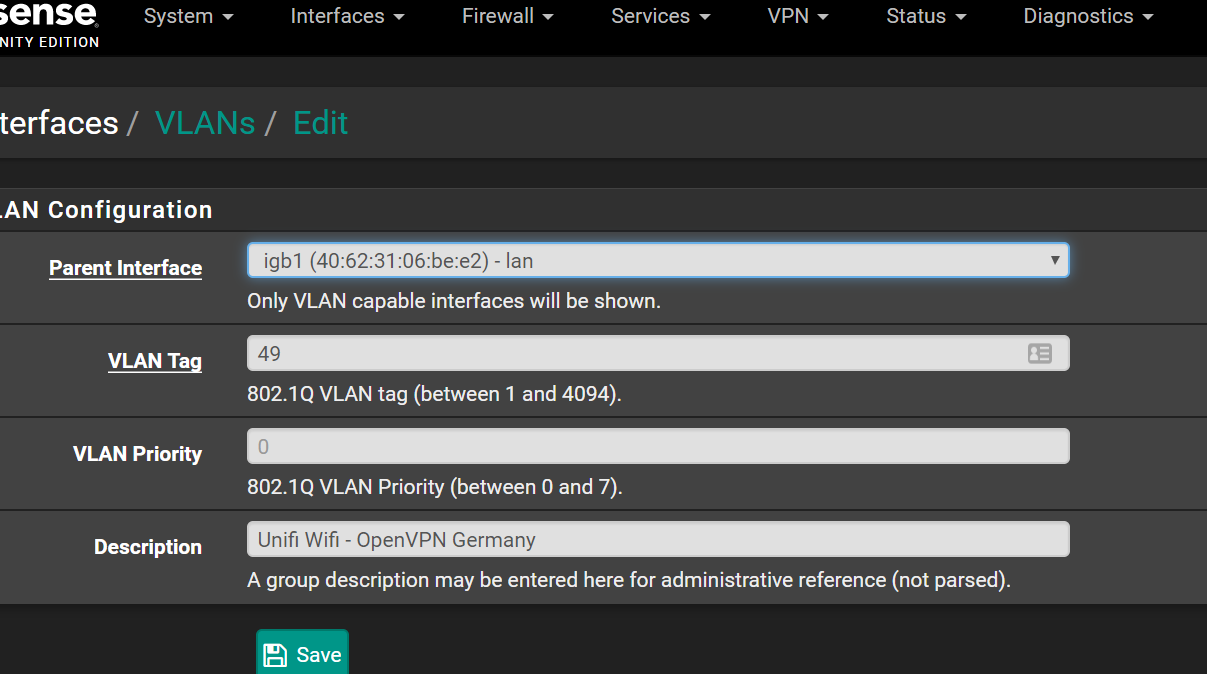
I'm now setting up now Open VPN. Vlan already created and mapped to my LAN NIC igb1 . Let'see. .
-
Ok got the tunnel up . Cyberghost VPN is pain to setup and no really docs about it.
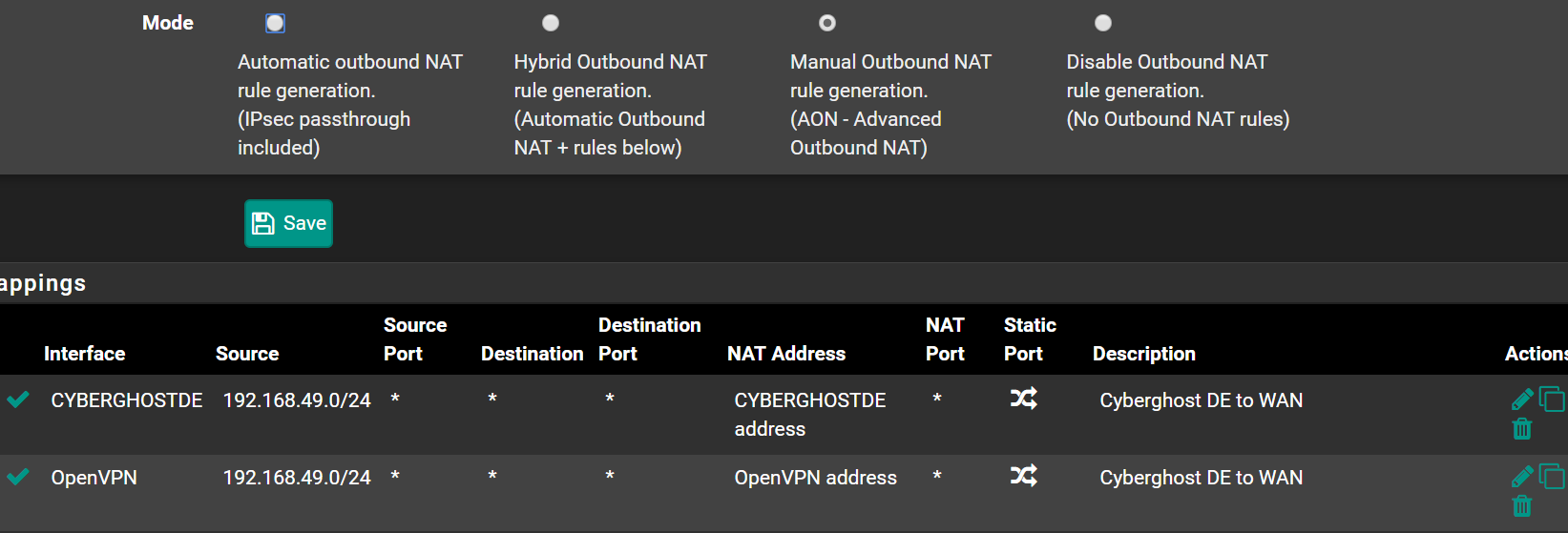
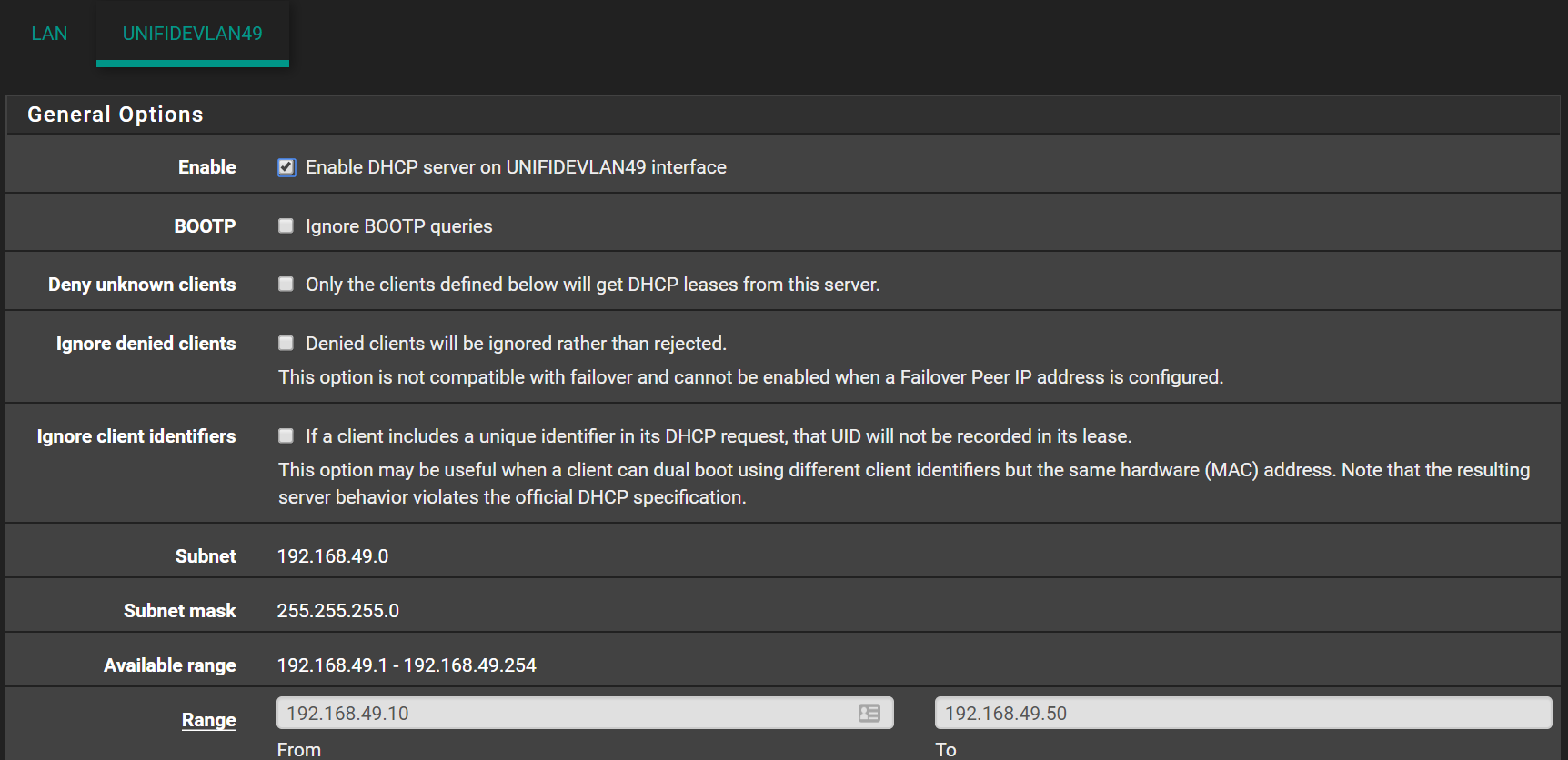
VLAN created, dhcp , subnet and range added to this VLAN , VLAN tagged in Unifi . NAT rule created to allow from this VLAN to WAN
No IP offered on this new VLAN . Maybe because I have created on Unifi a rule that block LAN traffic (Internet only like a guest) . I will further troubleshoot . Also becasue when this tunnel is up , normal LAN has no internet.
I only have a question about the GW to be assigned to this VLAN. In Pfsense I got this option uncheked. Not sure if in this case should be checked .
Use non-local GW: This will allow use of a gateway outside of this interface's subnet. This is usually indicative of a configuration error, but is required for some scenarios. -
When creating new "lan" side networks there would be no gateway assigned.. You just give the interface an IP.. say 192.168.2.1/24 if your lan is 192.168.1 for example.
You can route your different networks or even just specific devices out a vpn connection via policy routing - ie select the vpn as gateway in your firewall rule.
You almost never want to pull routes from some vpn service - they like you send everything through them... Which normally you would want to policy route.
-
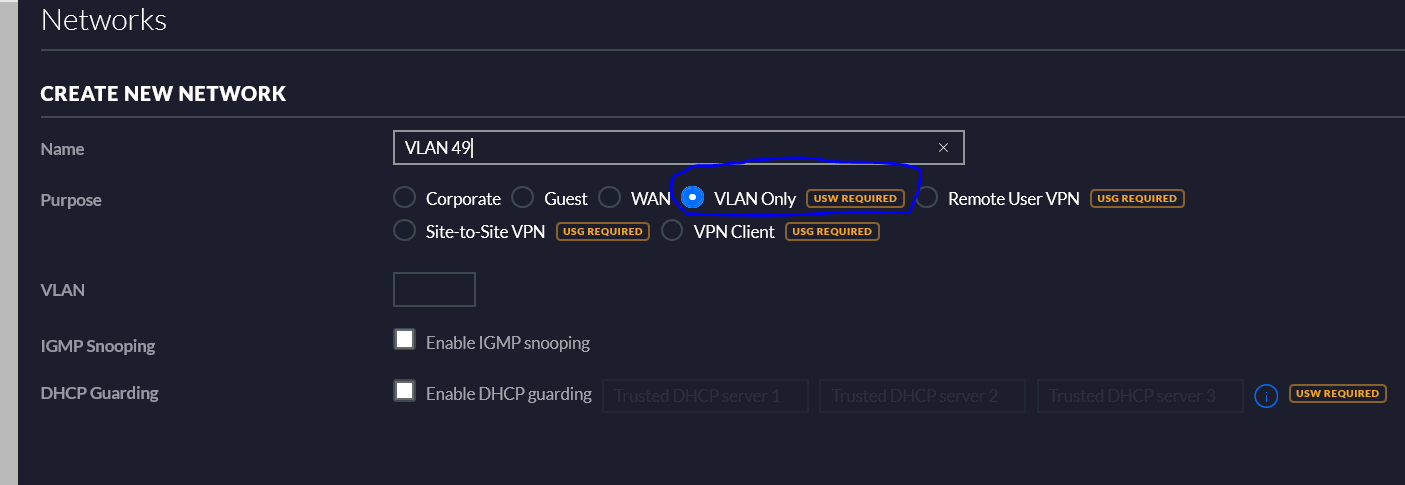
That's a bit nasty on Unifi side . Each time they upgrade the controller , they remove features . Such as VLAN only network, now is mandatory an Unifi switch .
As result the DHCP on the new Pfsense VLAN can't hand over an IP to the new SSID , therefore I got a bogus IP assigned by Unifi .
Will still try to find solutions , otherwise I will use an old DDWRT AP to test -
What? Dude I run unifi AP I have vlans tagged and untagged... Not sure what your talking about? I am running 5.11.26 on controller and 4.0.43 firmware...
What would unifi be handing out IPs for??
You set your vlan ID as tagged on our switch connected to the AP... Set your SSID with vlan ID to match and there you go.
-
@johnpoz do you have AP only ? in my case yes .
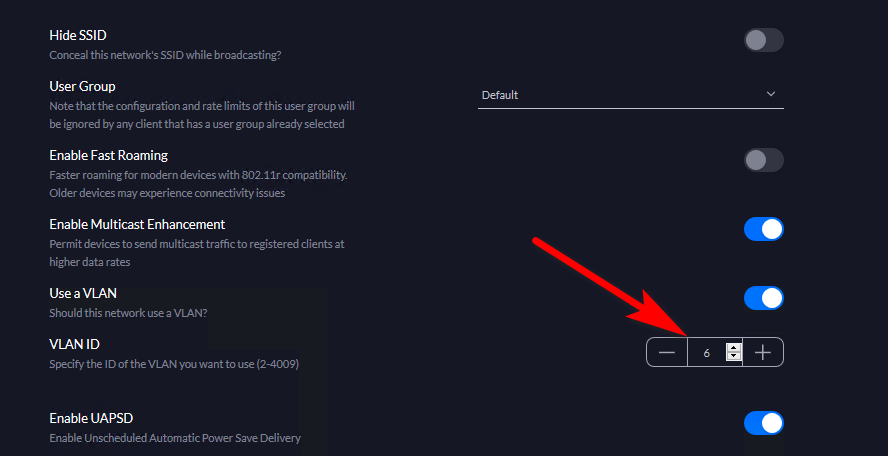
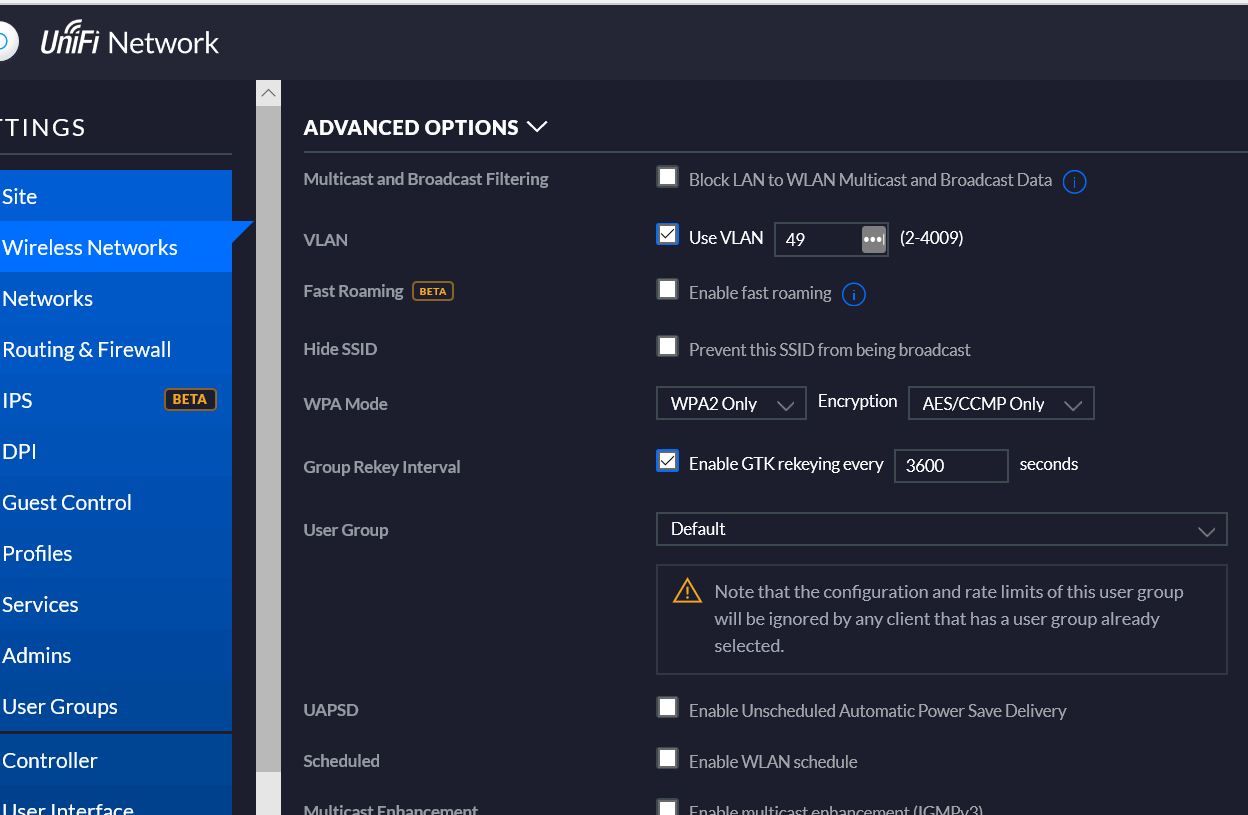
I have created a new SSID , tagged on the Pfsense VLAN .
Now if I want to create in Unifi a new network (VLAN only), different from LAN , require an Unifi switch .
On the Pfsense VLAN, the firewall rule is pretty straight forward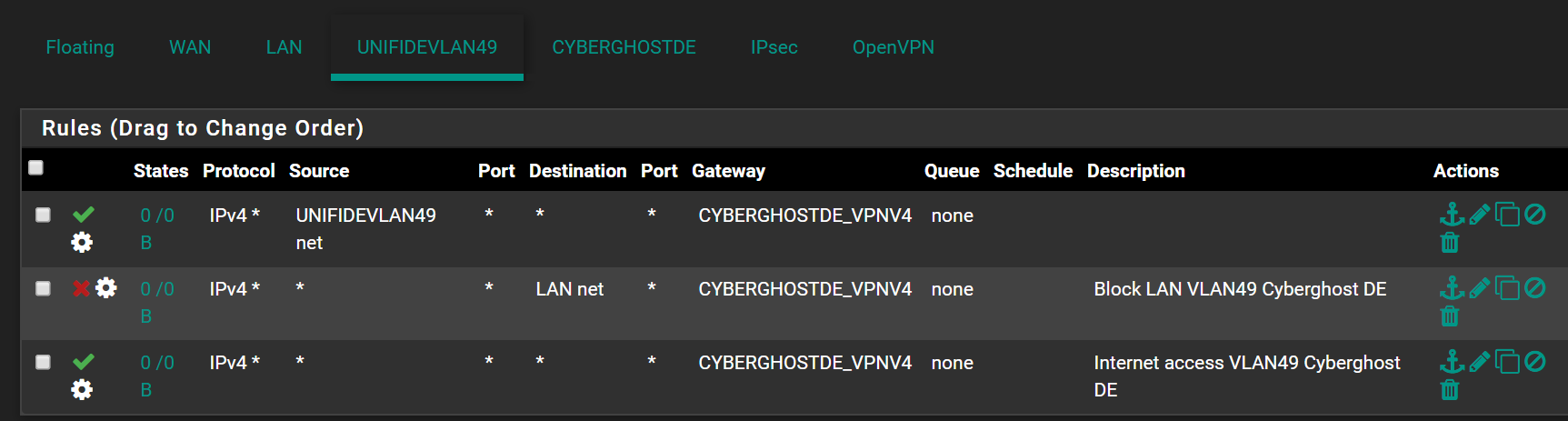
-
dude you do not need to do that... You only need to do that if you have a switch..
Let me log in and will post screenshot.
You set the vlan ID on your wifi network
That network tab on the controller has nothing to do with it.
-
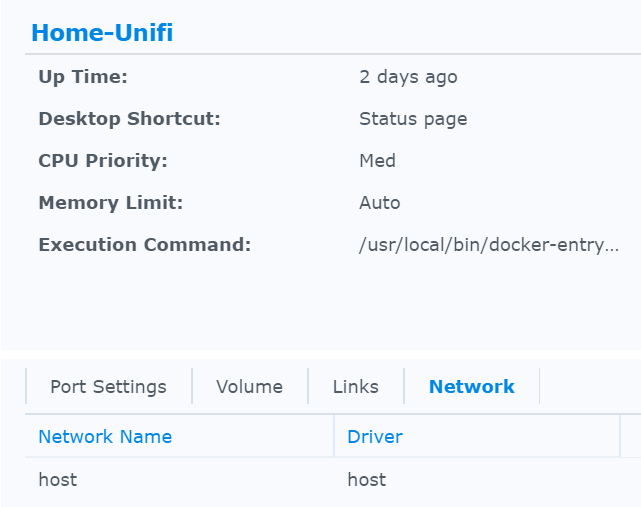
@johnpoz I guess I got your point. And indeed this is how I have configured it that struggles to work . I'm running a Docker version of the controller (does not really matter, is bridged to LAN)
-
If your client is not getting an IP from that vlan ID... Then you have a problem on your switch, or your vlan setup on pfsense or your not running dhcp...
All there is to do is set the vlan ID on your wireless network, and tag that to the AP..
-
@johnpoz There is no switch in between . Unifi AP straight forward in Pfsense LAN igb1 . DHCP server is running on that VLAN
-
So how exactly are you provisioning the AP? Its IP is also on vlan 49?
The AP talks to the controller normally via untagged... Where is your controller if you have the AP directly connected to your pfsense?
-
@johnpoz nope. AP is on the default LAN /24 . Works fine in that LAN.
-
And where is your controller? If you have the AP directly connected to your lan interface on pfsense? With no switch?
Draw up how you have everything connected...
-
@johnpoz Controller is running on Docker on a bridged LAN . Same main LAN subnet 192.168.1.0/24 . Just on it's own port 8443.
WAIT : I just remeber that I got a Tomato as bridge in between . Let me create a VLAN 49 there on the br0