Port forwarding problem
-
@johnpoz said in Port forwarding problem:
nd it has a interface in the 192.168.50 network, its sure and the F does not need a gateway to get to the 192.168.50 - which is what your showing at 192.168.50.1
The 192.168.50.1 it´s another host in the 50 network as a gw.
This doesn´t matter even when I have the 192.168.50.0 pointing to the interface.. all the related and established by directly connected network doesnt need the GW.. -
@johnpoz TheScope of forward wanted IS
10.200.40.132 (outgoing port) > 10.200.40.180(pfsense) port 999 (xn1) > forward(nat) 192.168.50.4:999 xn0
As can you see in the tcpdump the packages are not nated are come to the 192.168.50.4 as 10.200.40.132 and back by the default gw in the eth1 as you can see in the route table of the 192.168.50.4 host. -
@fakauy said in Port forwarding problem:
10.200.40.132 (outgoing port) > 10.200.40.180(pfsense) port 999 (xn1) > forward(nat) 192.168.50.4:999 xn0
Here is where you going to have a problem... Your .4 host has an interface in 10.200.40 so he will answer back via his other connection.
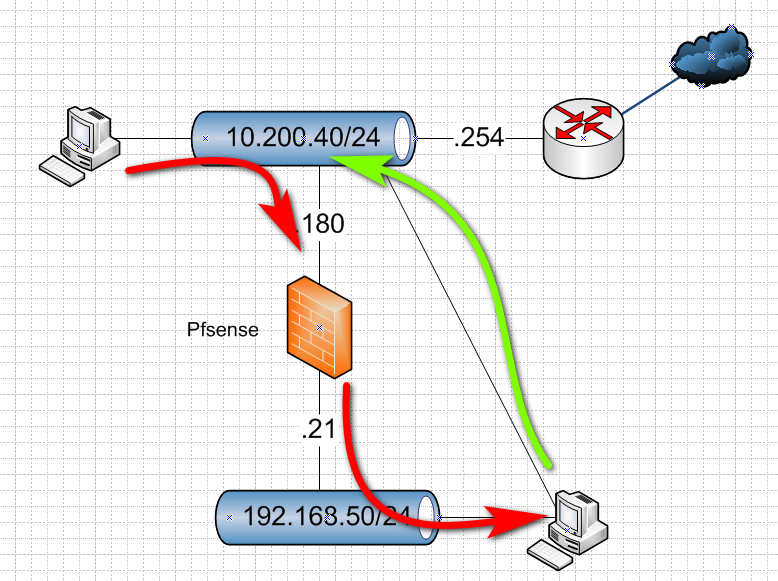
You would have to source nat it to the 192.168.50.21 address if you want .4 to send it back to pfsense...
Pfsense doesn't nat port forwards, only outbound nats..
Why would you want to hit 192.168.50.4 when you can just hit on its 10.200.40 address?
Your clients going not going to accept such an answer... because they sent it to 10.200.40.180, why would 10.200.40.x be sending me an answer, etc. etc.
-
@johnpoz said in Port forwarding problem:
Why would you want to hit 192.168.50.4 when you can just hit on its 10.200.40 address?
The 10.200.40 address its from one interface that´s need to be clear of traffic in this host (192.168.50.4)
-
@johnpoz I haved tested of remove this interface in 192.168.50.4 and didnt work.
-
Then you have to source nat..
The network makes ZERO sense.. .What exactly are you wanting to accomplish, once you multihome a device and put interfaces in networks on each side of a firewall - you basically make that firewall pointless.
-
What??? Removed what interface? The 200, then trouble shoot your port forward.. You did on pfsense WAN?
Did you change the .4 box to point to .21 as its default gateway? If not it wouldn't know how to get back to the 10.200
-
@johnpoz said in Port forwarding problem:
You did on pfsense WAN?
No only Haved tested to remove the 10.200 interface on the 192.168.50.4 and now I pointed a static route.. in this host..
Now looks:
Destination Gateway Genmask Flags Metric Ref Use Iface
10.200.40.132 192.168.50.4 255.255.255.255 UGH 0 0 0 eth0
192.168.50.0 192.168.50.1 255.255.255.0 UG 0 0 0 eth0
192.168.50.0 * 255.255.255.0 U 0 0 0 eth0
10.200.40.0 * 255.255.255.0 U 0 0 0 eth1
default 10.200.40.254 0.0.0.0 UG 0 0 0 eth1 -
@fakauy This didnt work.
-
Why and the F would you think that would work... It still has its 10.200.40.x interface..
If you want this to work while the box still has a 10.200 interface then you have to SOURCE nat it at pfsense.. Period, end of story..
Or you have to talk to it on its 10.200 interface..