New user. Need help with firewall logs
-
Hello,
I'm a new user with basic networking knowledge. I installed an SG-3100 about an hour ago, and am slowly setting everything up for my home network. I have a question regarding my firewall logs widget that is set to filter interfaces by "All traffic (wan and lan) using only the BLOCK filter). As you can see there are a lot of random IP's being blocked on the WAN interface.
https://i.imgur.com/234gIxu.png
Is this normal behavior? The filter/widget on the homepage is set to update every five seconds and I get at least one new entry (but usually several entries). Interestingly, there is no traffic being shown on a PASS & REJECT filter I setup. All I have connected to the LAN is my computer (with a fresh install of Windows) that is connected to a Unifi Switch that is connected to the SG-3100's LAN 1 port.
I've avoided browsing the internet, yet I still see a lot of entries so the random IP's is what worries me. I'm not sure if these are port scanners, or what (despite the ports shown not being common ports). I should mention the only active firewall rules are:
- WAN is set to 'block BOGON networks' and 'block private networks'. This is the default.
- LAN is set to 'Anti lockout, 'default allow LAN to any rule', and 'default LAN ipv6 to any rule'. This is also the default, and I've actually disabled IPv6.
-
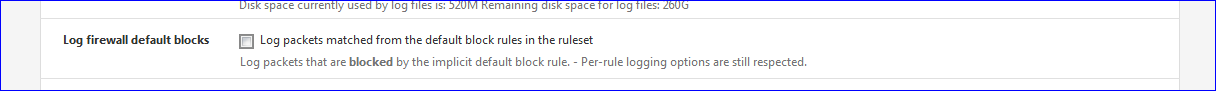
Lots of scanners out there, too many to monitor. You can reduce the log chatter in Status/System Logs/Settings/General and turn off "Log firewall default blocks".
-
Thank you for your response, provels. Sorry for such the late reply. Trying to make all of this equipment that I'm using (pfsense + UniFI) is new for me and it has been a lot more challenging than anticipated. It's a HUGE learning curve. I know some networking basics, but I obviously need to learn more.
What you suggested with turning off "log firewall default blocks" works, and that leads me to another question...
So the logged traffic on the WAN are port scanners. I eventually got around to reseting my 'firewall state table' in order to break any established connections. What I've noticed is that the same rule filter - the LOG FIREWALL DEFAULT BLOCKS - is what triggers the blocked traffic on the LAN interface as shown here: https://i.imgur.com/zBAXjCe.png
If I reset my firewall logs after ~10 minutes then I never see this blocked traffic on the LAN interface again. It only occurs immediately after reseting the firewall state table. The only firewall rules I have set on LAN is an 'anti-lockout' rule and the 'default allow lan to any' rule. I'm not inniating any of these connections myself (Windows might be - I suppose).
What is triggering this traffic to be blocked and why is it on the LAN interface?
If the firewall rule is set to allow to any, why is traffic being blocked in the first place?When I look up the IPs - they appear to be linked to Google/Microsoft/Amazon servers.
-
@lvl1k0n said in New user. Need help with firewall logs:
What is triggering this traffic to be blocked and why is it on the LAN interface?
Your firewall settings ^^
On the LAN interface, the final, hidden last rule is always a "block all".
This one logs by default, and because you can't edit it, you'll see all these logs.But ... you don't mind ^^ When you installed pfSense, a default visible - and editable - rule (probably 2 of them, the default anto-lock out rule will be there also) is created for you. As a gift. This one doesn't log.
It's a pass all rule that doesn't log. So any device on LAN can access the entire world.The WAN interface is delivered with no visible rules - but again, a default hidden rule exists - and this one logs also.
When you connect a router / firewall to the Internet, you be part of the Internet.
If you didn't know it already : on the Internet, millions of devices are "probing" about any IP possible, so also yours.How to shut down the noise ?
Remove the check on this one :
Status > System Logs > Settings :
You probably edited / removed / added rules on your LAN interface.
That's why the LAN interface also produces logs now.
It works like this : your won rules are logging > so all goes as planned.
Or : your firewall rules on LAN do not match every Internet packet so it will be parsed finally by the default rule => you'll be seeing a log for each hit (match).Do what has been said above, or modify your own rules (block devices and don't log).