2 pfSense with gateway on the second
-
I have the following settings:
2 pfSense, connected via a routed IPsec tunnel (VTI)Configuration of the pfSense 1:
one Interface LAN1 with subnet 192.168.2.0/24Gateway at pfSense 2
I now want to tunnel the whole traffic to the second one through the IPsec tunnel.
Whichs works, when i define one rule at the pfSense 1 to use the IPsec tunnel (pfSense 2) as a gateway.Because of the static route on pfSense 2 a NAT rule is created automatically, which works fine.
Clients in the LAN1 net can ping things at the internet and browse some sites.
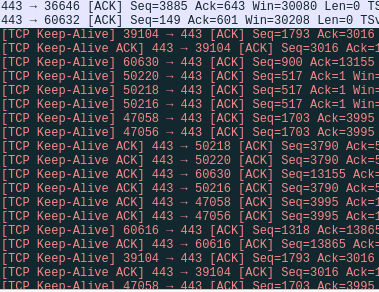
Somehow it is not very stable and some ACK packets are rejected
Why are those rejected? Also creating a rule does not work.Here is a log entry on the second pfSense (the Gateway):

Why are those packets blocked? Is there something wrone with my routing and the pfsense is dropping packets?
Does somebody other know a better solution or an answer to solve my problem?
Thank you
-
You have asymmetric routing going on. Read through this: https://docs.netgate.com/pfsense/en/latest/firewall/troubleshooting-blocked-log-entries-due-to-asymmetric-routing.html
-
@jimp
I do not know, where an asymectric route shoud happen.
"Bypass firewall rules for traffic on the same interface" doesn't fix my problem, also the outgoing floating rule with the "sloppy state" does not work.Do i understand something wrong?
I only have two rules, on the pfSense 1 at interface LAN1 to use the ipsec tunnel as a gateway, and on pfSense 2 one rule to allow traffic fron 192.168.2.0/24 to any at the ipsec interface.
-
Ah, I misread what you had. I thought you had two pfSense routers at the same location doing a tunnel to a remote site.
In your case, the log you see is probably not a problem. It's most likely an out-of-state/OOW response from a web server being blocked from going back across the tunnel. (Server sent another packet after pfSense removed the state, more or less). That is common with web server traffic.
https://docs.netgate.com/pfsense/en/latest/firewall/troubleshooting-blocked-log-entries-for-legitimate-connection-packets.html
-
@jimp
Simple webpages are working well. But wen i try to use more complex sites like speedtest.net it doesn't work. Maybe there is something other wrong with the rules.Am i missing something? When i test it with speedtest.net it shows the ip address of the second pfSense, which is the gateway. Sometimes connection times out.
What else could be wrong in my configuration? Those blocked packeges at the firewall are too much. I only have one client using one webpage.
-
Could be that you need to setup MSS clamping for the VPNs (IPsec advanced tab), or set the MTU lower on the IPsec VTI interfaces
-
@jimp
the tunnel works fine for other purposes, but i will try to change the mtu.if there is a problem with the mtu, shoundn't wireshark get icmp messages?
I only get many, many TCP Keep-Alive messages.
-
This post is deleted! -
Since the update to pfSense 2.4.5 some webpages through other tunnels also do not work.
Thats is now a differen tunnel. Some http requests do work, some do not. I can see packet go to the tunnel but do not arrave on the other point.
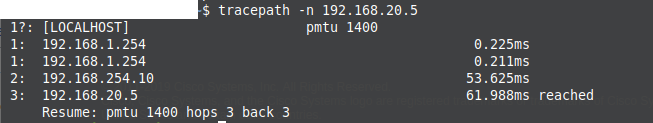
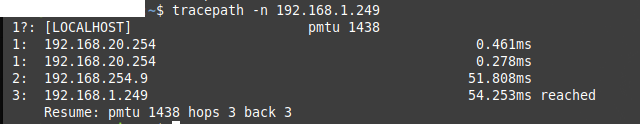
There is a tracepath in both directions:
This is now an other situation. If i, for example, want to view a webinterface of a switch it does not work.
What mtu and mss settings do i have to set? Do i have to add or remove some bytes to those values?
Thank you
-
Regarding the first problem, setting the mtu and the mss really solved my problem. Thank you.
I just set the MTU to 1400 and the MSS to 1360. How can i easily find out the highest i can get?