[SOLVED-Not Possible] NAT Outbound rules with SNAT WAN Address
-
EDIT: With a SNAT network (when WAN ip address is different from the external IP) using Automatic Outbound Rules isn't possible
Dear forum members,
my pfsense (2.4.4-p3) is behind a nated network like this :
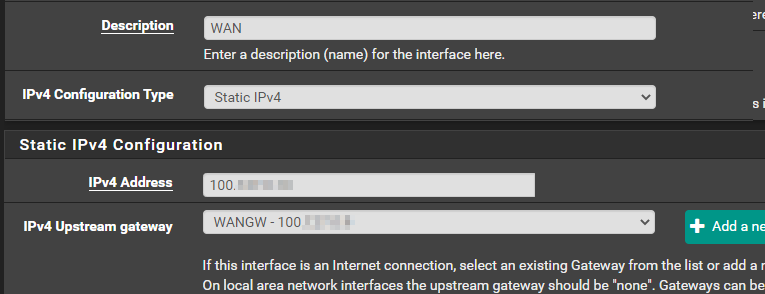
WAN address: 100.0.0.10 (GW: 100.0.0.9)
Public IP: 45.0.0.1Therefor, I can't reach outside with the NAT Outbound "automatic" rules, because by default, the 'NAT Address' is set to 'WAN address', and not my NATed 'Public IP'.
Is there a way to use the Automatic Outbound rules and stating somewhere that the NAT address should be my public IP instead of my "real" WAN address ?
Regards,
Nono
-
Hi,
There is little information, but ...
Will you allow me a stupid question?
are you really using these IP ranges or is this just an example?These are not free-to-use IP ranges, since:
https://www.speedguide.net/ip/100.0.0.1
https://www.speedguide.net/ip/45.0.0.1The proposal is the RFC1918 range:
https://en.wikipedia.org/wiki/Private_networkand at the very end I would like to mention the new version of pfSense: 2.4.5 -p1
https://forum.netgate.com/topic/154337/pfsense-2-4-5-release-p1-now-available -
Hi @DaddyGo :
It's NOT the real IP. I just "simplified" them (and not disclose the real one).I just upgraded to 2.4.5-p1 following my initial post.
-
Hi Nono,
"my pfsense (2.4.4-p3) is behind a nated network"
and then there is no need to change the IPs, because they are not the real public IPs
am I correct? (but also RFC?)if you've done the upgrade, please come back and provide more specific information so we can see better as you're struggling....
tell me if I misunderstand you, these days it often happens to me

-
@DaddyGo not sure what's information you need ?
The configuration is the same as my other topic (solved) here :
https://forum.netgate.com/topic/150333/solved-dns-forwarding-behind-s-nated-network
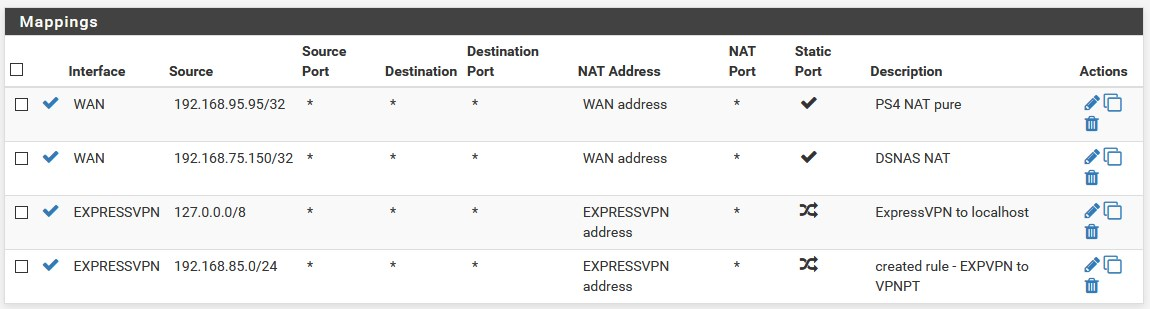
Also, my current configuration work. I just have to use manual outbound rule & change the NAT AddressMy question is simply :
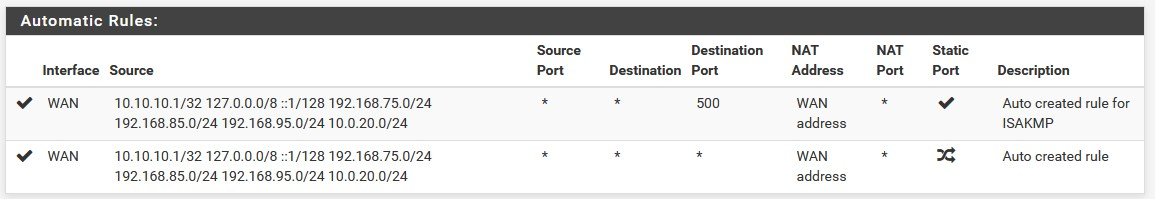
By default, the Automatic Outbound Rules set (all) the "NAT Address" as the "WAN Address".
But in my case, the WAN Address is not the Public IP, so I have to edit them manually.
Is there a way to set that the "Automatic OUtbound Rules" should use my alias "External IP" as NAT address instead of using the "WAN address" setup on the WAN Interface configuration ? -
BTW, I don't read old posts from others...
unless, I am specifically interested in the themeis included in the name - "Automatic Outbound Rules", it works from what you have already configured once, by default with the appropriate rules and interfaces
You can configure Manual / Advanced Outbound NAT Settings the way you want, of course following the principles
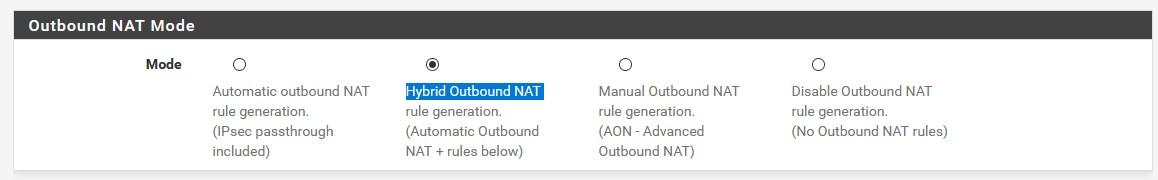
such as Hybrid Outbound NAT, you can configure this, but you can't configur the ones created automatically
by the way, everything is described here:
https://docs.netgate.com/pfsense/en/latest/nat/index.html -
the fact is :
"Automatic Outbound Rules" does NOT work in my case.
I HAVE to use "Manual Outbound NAT", and edit all the rules, to change the "NAT Address" manually, to my public IP, like this :
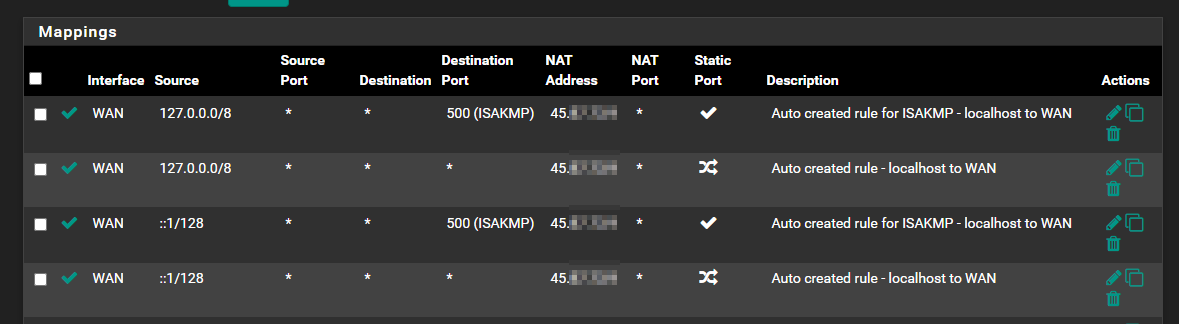
My understanding is, the Automatic Outbound Rules is taking the 'ip address" that I set on the interface configuration, which, on my case, isn't the same as the NAT address:
Is this possible, or not ?
-
@Nono_ said in NAT Outbound rules with SNAT WAN Address:
My understanding is, the Automatic Outbound Rules is taking the 'ip address" that I set on the interface configuration, which, on my case, isn't the same as the NAT address:
You understand exactly!
but pls. don't use these IP addresses!
RFC1918 is a standard and all manufacturers respect the internal (private) address range
because of this, many tools, devices will not understand what you want to achieve
you are not more secure, if you use another dedicated address space internallythis is especially true if you want to access your system from the outside
-
@DaddyGo thanks for the confirmation.
But again, those aren't the real IP (and anyway, forced by my provider), so nothing I can do here.