Newbie: traffic shaping with DSCP (Zoom)
-
Hi. I'm using pfsense 2.4.5-RELEASE-p1, with one wan, one lan on a home 100/40 connection. This is day 3.
I want to know how to traffic shape zoom to give audio traffic priority.
Zoom can set DSCP flags, it defaults to making audio traffic with 56 which is CS7 for pfsense, according to https://docs.netgate.com/pfsense/en/latest/trafficshaper/diffserv.htmlFirst dumb question: is there any harm in trying to traffic shape this on both the WAN and LAN?
I've run the traffic shaping wizard and ended up with a few queues.
Under Firewall Rules I can access an Advanced section which appears to let me match the DSCP class.
The rest of the settings are a mystery to me.I have a rule on the LAN interface.
It is a "pass" rule.
I've made it for protocol "any" and IPV4 & V6.
Source: Any, Destination: Any
(Zoom documentation has a long list of IP addresses for firewall configuration, I hope 'any' is ok).I haven't touched the TCP flags; every box is unticked.
I ticked Allow IP Options because maybe multicast is involved.
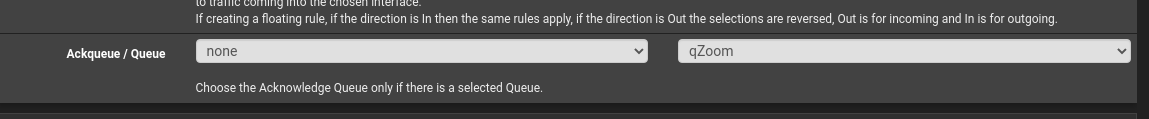
In the queues, I choose qAck and qOthersHighI have ticked 'Log Packets that are handled by this rule'
Another dumb question: where is this log? The console has an option 10 Filter Logs, but it doesn't help me.
The docs say that I can run from console shell
pftop -s1 -v queuethe qOtherHigh q shows nothing, I start a Zoom test meeting, and it shows a good amount of traffic, and it returns to no activity when I stop the test meeting. When I mute the microphone, the amount of traffic reduces a lot, but not to zero (only audio is in cs7, video is lower and should not be matched by my rule, so this is further evidence that it is matching the correct packets).
So it seems to be working. But is it a sensible rule? Should I have a WAN rule too? Which log file is it?
-
Hello @timatgca,
I'm interested in this topic. My zoom meetings are having some sound issues due to a DSCP marking that is activated by my company (https://support.zoom.us/hc/en-us/articles/207368756-QoS-DSCP-Marking).
@timatgca, let me know if you implement correctly DSCP on pfSense. If so what are the options to get them configured.
Thank you
-
@luiscachog
Hi, I'm not using my rules anymore because my home network is never saturated to the point where it could make any difference. Traffic shaping only helps prioritise traffic when there is not enough capacity. So the DSCP marking can't be causing the problems: if you don't have any rules, the DSCP marking is ignored. Possibly, if you are running out of bandwith due to competing use of your connection, activating the rules will help.I think the rule I set up was working so I hope my initial post helps.
-
Hi, I believe I do not have any rules in place.
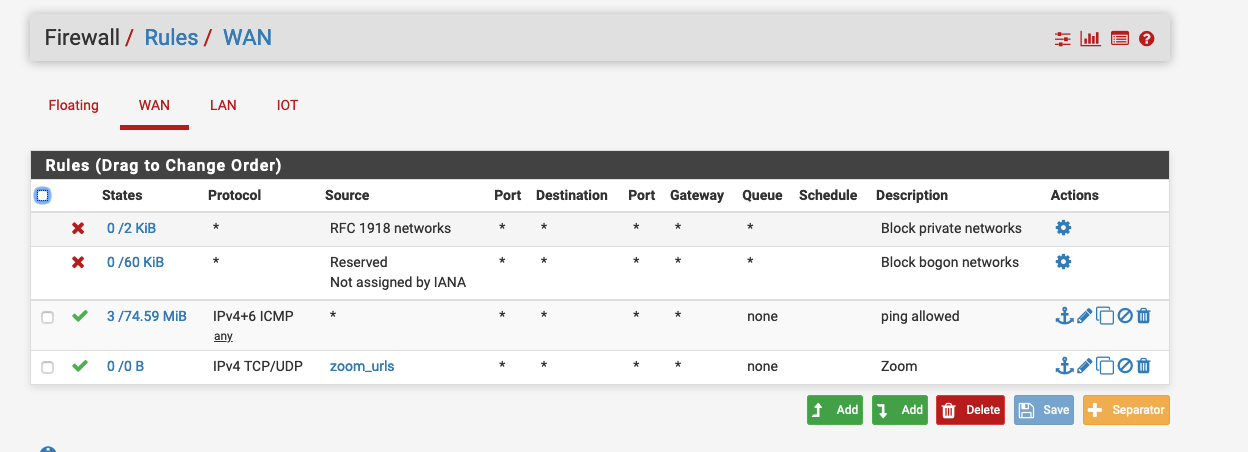
WAN:
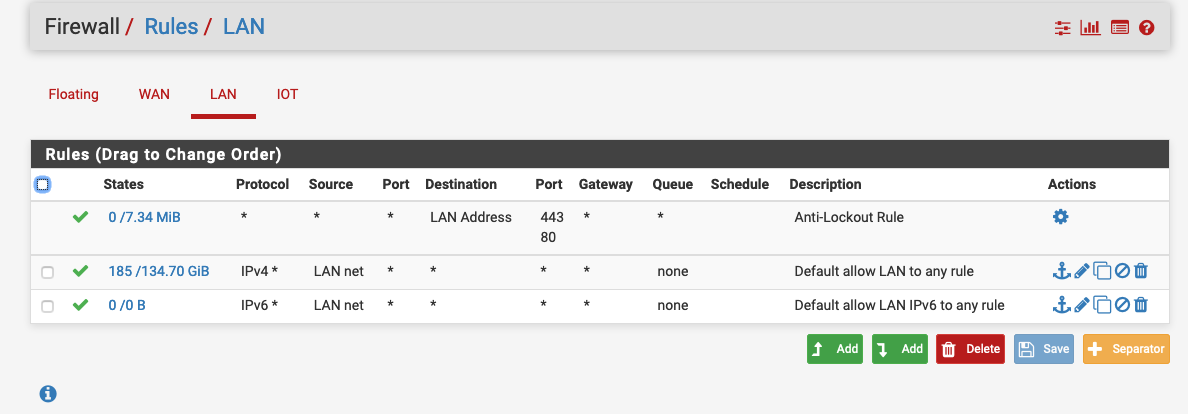
LAN:
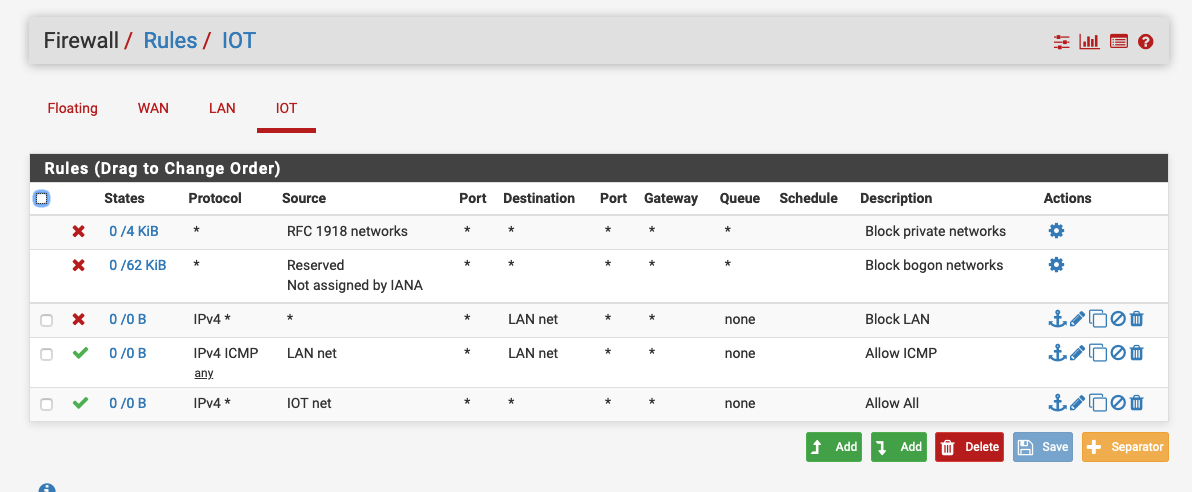
IOT:
I'm using:
- ISP Service: ATT Gigapower
- ATT Gateway: AT&T Pace 5268ac
- pfSense Box: Protectli FW4A
- Wireless Accesspoint: Ruckus R510
- Core Switch: Ruckus ICX 7150 12 ports
- DNS Server: Pi-hole on a Raspberry pi
I'm connected as:
Internet <---> ISP Service <---> ATT Gateway <---> pfSense Box <---> Core Switch <---> DNS Server <--> Wireless Accespoints <---> Laptop (MacBook pro, Lenovo T495 - Ubuntu)- The ATT Gateway is configured as Bridge
Do you think that you can help me?
-
@luiscachog Can you elaborate what you have under rules for zoom_urls?
-
Hello @rjamesm,
zoom_urls is a list of IPs that you can find on https://assets.zoom.us/docs/ipranges/Zoom.txt
I permitted the traffic from those IPs from Zoom.
-
@luiscachog Yes I got that list too but what did you choose when setting the list URL IP or IP Table? Also did you added all the ips listed thats a lot to add too. The reason I ask is because I fired up some zoom meetings and don't see the traffic through those queue.
-
Hello @rjamesm,
It was created using
aliases, as shown on the picture:
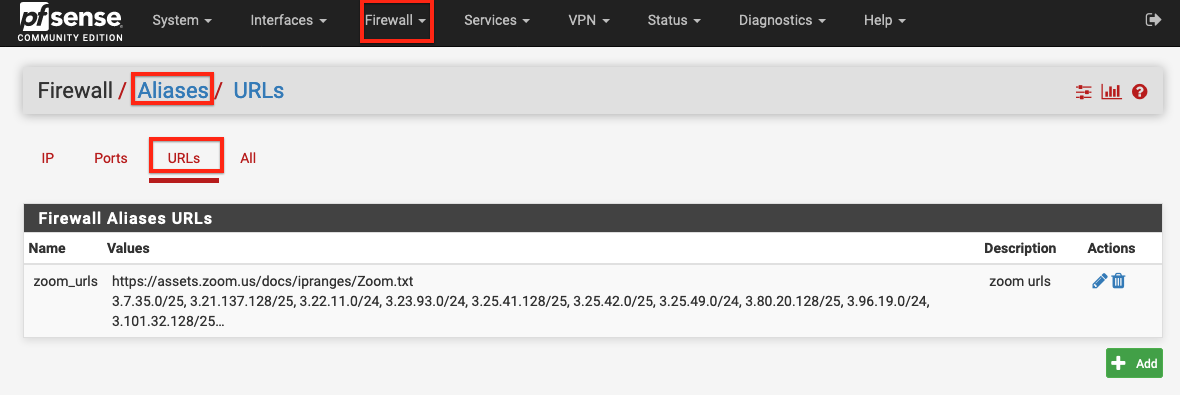
That way I only need to add that URL with the list of IPs.
Not sure how to see the traffic through a queue. Can you guide me?
Also, I'm having problems when I'm using my company zoom account because DSCP is enabled for all the company. When I use my personal account I don't have any issue.
-
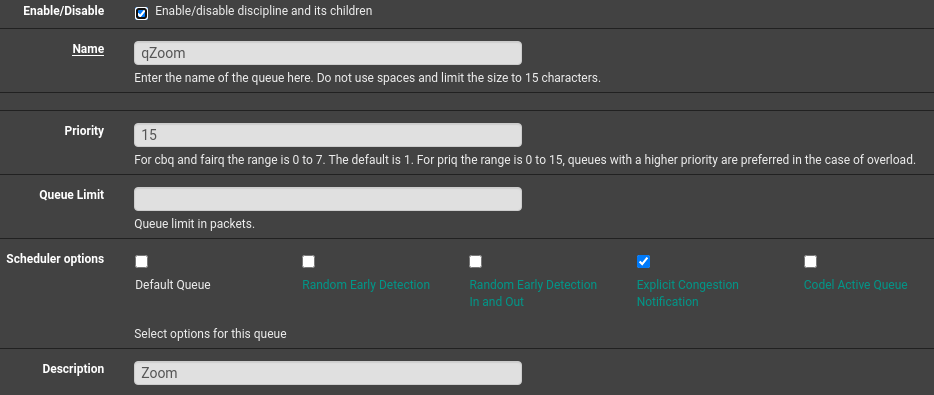
@luiscachog Hey there! Thanks for sharing your screenshot and the URL for the IP of Zoom servers, that really helped! Sure, you need to create a floating rule for Zoom URLS not on the WAN side but on Floating Rules. Then move that rule to the top or what ever order you need and create a queue for Zoom
With the queue created you will be able to see the traffic through STATUS> QUEUE
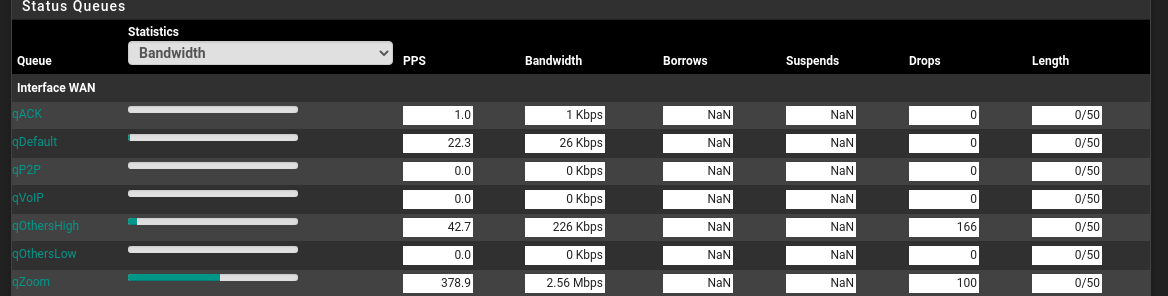
We are using traffic shaping and assigned it a high priority
I hope that helps out!
-
@luiscachog Unfortunately Zoom does not keep (https://assets.zoom.us/docs/ipranges/Zoom.txt) up to date. I have found at least 10 other IPs I had to add. Everyday there seems to be a new IP. I may see if QoS DSCP Marking can be turned on by the host.