Connect two subnets across pfSense
-
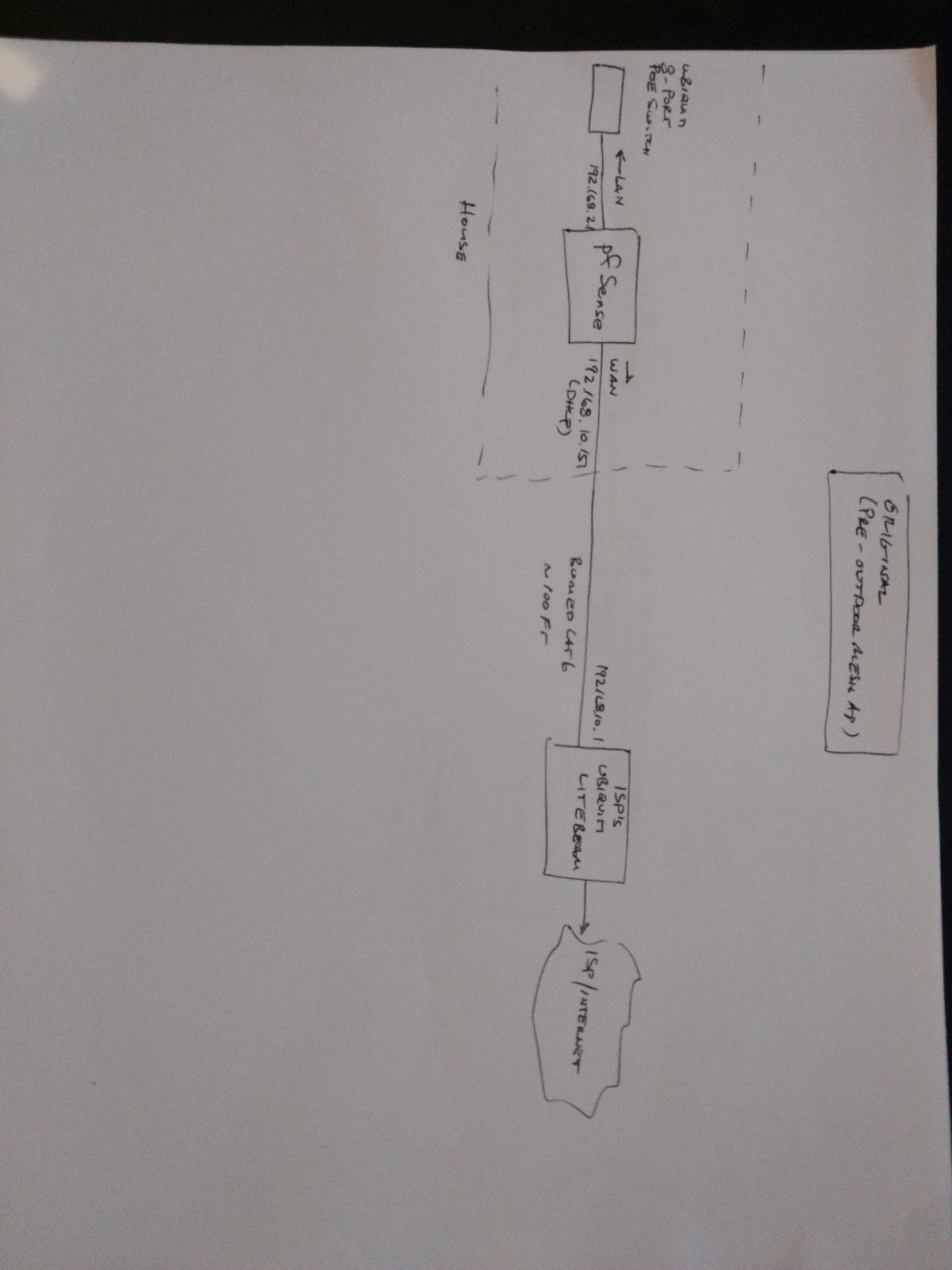
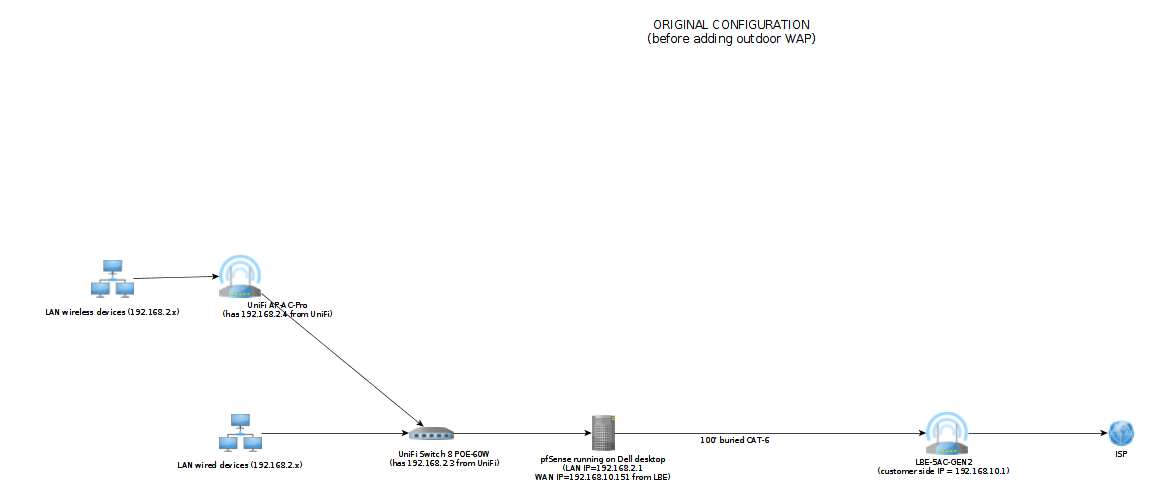
I am using pfSense 2.4.5 as a firewall and router on a computer with two NICs: LAN (192.168.2.1) and WAN (192.168.10.151). The WAN side gets its IP address from my ISP's on-site Ubiquiti LiteBeam radio (192.168.10.1). I cannot change anything on the LiteBeam. The LiteBeam is connected to pfSense via about one hundred feet of buried Ethernet cable. Everything works fine with this setup.
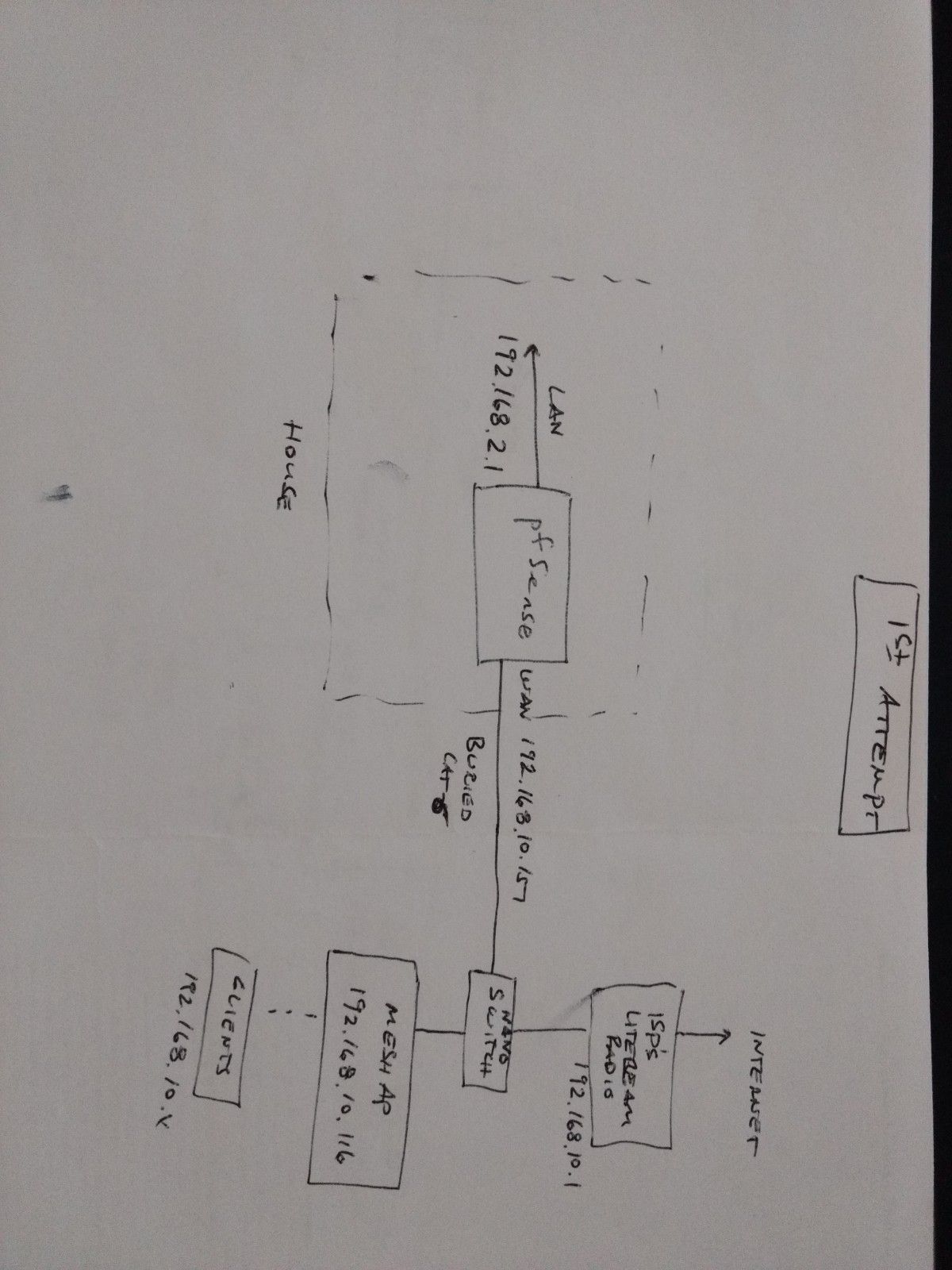
Recently I added a Ubiquiti outdoor mesh AP to begin extending WiFi across the farm. I inserted an unmanaged outdoor switch (Ubiquiti Nanoswitch) between pfSense and the LiteBeam so I could connect the mesh AP to pfSense. This means the mesh AP is part of the WAN-side subnet (192.168.10.0/24) and gets an IP address via DHCP from the LiteBeam. However, I manually change its gateway and DNS IP to 192.168.10.151 so its traffic goes through pfSense and it can be managed with UniFi.
This works but is not ideal because each device connected to the mesh AP must be given new port forwarding and firewall rules to access the computers on LAN side. Is there a way to reconfigure this network so that the clients of the mesh AP are part of the LAN?
-I don't think bridging via a transparent firewall is an option because I don't have extra network interfaces.
-I don't want to bury a new Ethernet cable from the mesh AP to my LAN switch.
-I don't think a point-to-site VPN is an option because eventually there will be clients of the mesh AP that can't run a VPN client such as Arduino microcontrollers. Maybe there's a way to set up a site-to-site VPN? I really don't know much about L2TP.The only other option I can think of is to add a second mesh AP at the house that is wired to the LAN switch and connects to the original outdoor mesh AP via WiFi. I'm not worried about reduced network bandwidth for the mesh AP clients so maybe this is the best option even though I'd rather not buy more hardware.
Happy 4th of July and thanks for any ideas.
-
@pyrocumulus said in Connect two subnets across pfSense:
. I inserted an unmanaged outdoor switch (Ubiquiti Nanoswitch) between pfSense and the LiteBeam so I could connect the mesh AP to pfSense. This means the mesh AP is part of the WAN-side subnet (192.168.10.0/24) and gets an IP address via DHCP from the LiteBeam. However, I manually change its gateway and DNS IP to 192.168.10.151 so its traffic goes through pfSense and it can be managed with UniFi.
This works but is not idealhi,
it definitely does not work(!) and you are well saying that this is not ideal
in this "lineup", both pfSense and AP upstream are LiteBeam, so AP is not protected by pfSense
the AP must be placed after pfSense on either a separate interface (which is not present now) or a VLAN, which can be part of the LAN's physical interface
if you buy a cheap Intel multi-port NIC and you can expand your pfSense box, the solution is easier
if you do not have the option to lay more cables, so your options are limited
like:
https://www.ui.com/airmax/nanostationm/
https://www.tp-link.com/us/home-networking/powerline/
(I do not recommend this so much)@pyrocumulus "I manually change its gateway and DNS IP to 192.168.10.151 so its traffic goes through pfSense "
(the pfSense WAN and the AP are on the same subnet)this is confusing, why do you need to specify the GW and DNS IP for / to the dual-NATed pfSense WAN IP?
-
@DaddyGo Thanks for the reply. I agree, my current set up is definitely not ideal and I'd like to get the mesh AP behind pfSense. It does work, however, as long as the firewall has the correct rules to allow each client to access the LAN.
I could move pfSense to an appliance which could be located outside but that's more money than I want to spend and it probably shouldn't be sitting outside anyway. I'm sure a NanoStation would work as well but it would be nice to take advantage of the wired Ethernet connection if I can.
What if I swap the unmanaged NanoSwitch for a managed EdgeRouter? Could I then use VLANs to connect the two subnets?
As for specifying the GW and DNS IP for the mesh AP: I need to do this in order for the mesh AP to show up in UniFi which is hosted from within the LAN. Otherwise it is stuck using the LiteBeam as its gateway because the LiteBeam is running a DHCP server. I suppose changing the DNS server doesn't matter.
-
@pyrocumulus said in Connect two subnets across pfSense:
What if I swap the unmanaged NanoSwitch for a managed EdgeRouter? Could I then use VLANs to connect the two subnets?
of course

routing between VLANs may work
-inter VLAN routing- static route
-etc.
- static route
-
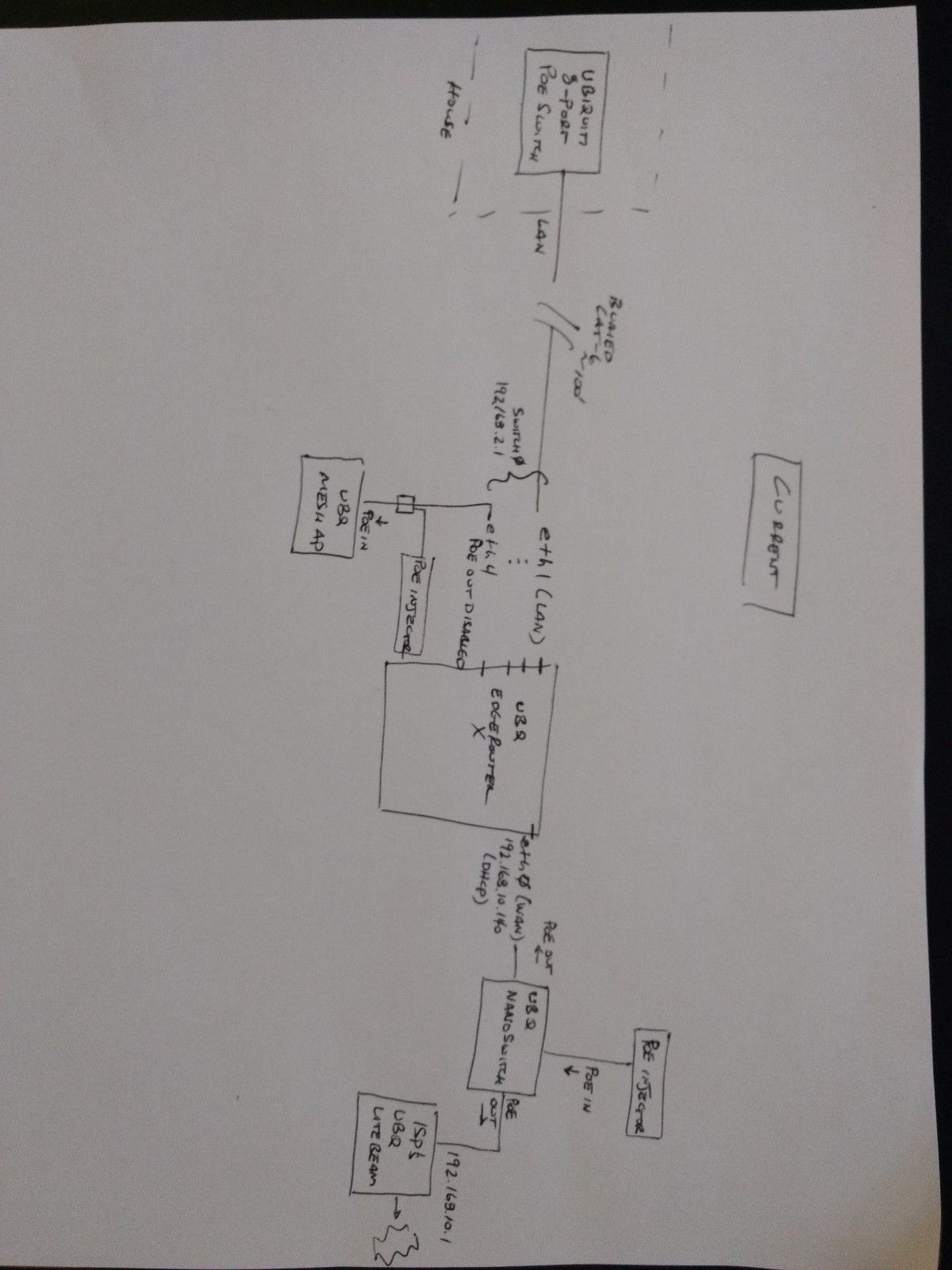
I ended up replacing the pfSense firewall/router in the house with a Ubiquiti EdgeRouter X that sits in a barn near the LiteBeam radio. Now the mesh AP can be protected behind the EdgeRouter as part of the LAN and there is no need for VLANs. I definitely miss the pfSense software but the EdgeRouter is a lot cheaper than a Netgate SG-1100. Maybe someday...
-
@pyrocumulus said in Connect two subnets across pfSense:
EdgeRouter is a lot cheaper than a Netgate SG-1100. Maybe someday...
this is indeed true, but EdgeRouterX is not a firewall either, ergo you have no protection from the confusing world

BTW-.
I use the $ 35 EdgeRouterX for PPPoE tests only because it's well configurable, nothing else... -
From the EdgeRouter documentation: "The EdgeRouter uses a stateful firewall, which means the router firewall rules can match on different connection states."
I realize pfSense provides more flexibility but if my EdgeRouter firewall is basically just doing a default deny/drop on the WAN inbound interface, it is providing equivalent protection, right? Just curious.
-
Why would you need to use an edgerouter? Just put in a managed switch?
Why can you not just connect this AP to network behind pfsense? A vlan for example? Or even just your normal lan?
Without a map/drawing of were this equipment is, etc. not sure why you didn't just connect this outside AP to your internal network. But if you used a managed switch you could then put that AP on a vlan that you connect behind pfsense.. Via another switch..
Could you provide a sketch/drawing of exactly how you have this currently connected?
-
@pyrocumulus said in Connect two subnets across pfSense:
it is providing equivalent protection, right? Just curious.
By no means and is it comparable...unfortunately
every penny category SOHO router includes something basic firewall, well there is one in EdgeRouterX
this is not real NGFW
so I don't have good news ...
https://securityboulevard.com/2019/06/next-generation-firewall-ngfw-vs-traditional-firewall/
-
I would think the flex switch would work, its poe and managed and is rated for outside.. I was not aware the edge router was routed for placement outside?
I think a drawing of how your wan comes in, and how you connected this outside AP.. Will allow us to discuss possible ways to bring this AP network into network that is behind pfsense, for least amount of money and installation.
-
@johnpoz said in Connect two subnets across pfSense:
Why would you need to use an edgerouter? Just put in a managed switch?
Mainly because it's cheap! And also because I was unaware of the Switch Flex- I definitely don't claim to know what I'm doing. The Edge Router X is about half the cost of the Switch Flex. You are right that the Edge Router is not rated for outdoor use but I've got it inside a plastic enclosure for dust protection. A managed switch would have been ideal.
Why can you not just connect this AP to network behind pfsense? A vlan for example? Or even just your normal lan?
The reason I didn't want to connect the new AP behind pfSense (which is running on an old desktop in my basement) is because of the physical location. I wanted to extend WiFi further out across the farmstead from the house and the best location is at the end of the buried ethernet cable by my ISP's Litebeam. Alternatively, I could have moved the pfSense desktop outside to the other end of the cable but that seemed extra risky, plus it was on a UPS.
I attached pictures of three crude sketches. Sorry for the hand-drawn pictures; obviously I'm not a network engineer. But maybe they will help explain my setup.
-The one labeled "Original" shows how the network was set up before I decided to add the outdoor AP and it worked fine.
-The one labeled "1st Attempt" shows how it was set up before the Edge Router. It worked but clients of the new AP were not behind pfSense and were on the wrong subnet and couldn't easily access the LAN.
-The picture labeled "Current" shows the setup as it is working now. It's extra convoluted due to the limited PoE options of the Ubiquiti hardware as well as by the limits of the PoE injectors that I happened to have on hand. I had to run A/C power out to this location and my wife is getting tired of this project so it's probably not going to change any time soon.@DaddyGo Thanks for the information on the differences between firewalls. I don't think I need DPI for a simple 'default deny' firewall but I was running Snort on pfSense so unfortunately that's gone now. Mainly what I miss about pfSense vs. the EdgeRouter is all of its extra monitoring and reporting options. I also had pfSense set up as an OpenVPN client via ProtonVPN to cover my entire LAN. I haven't figured that out yet with EdgeOS.
Thanks for the help.
Dave!
-
Well that is start.. But that is not showing us the important parts.. How exactly did you break and make these new connections?
When you stated a underground cable.. How did you connect into the line.. From the backend of the litebeam? Which is still 100ft away?
Where did you place this new mesh AP? right next to the litebeam?
Looks to me you just put yourself behind the router outside, and its edge router vs pfsense now.. You don't show your pfsense in current drawing, or what IP space using behind it? Before you were using 192.168.2 behind pfsense, now your using that as you wan to pfsense? What did you change your pfsense lan network too?
You could for sure put pfsense behind a double nat, and this could work pretty easy with just correct routing and a transit network that your outside AP sits on..
-
@johnpoz said in Connect two subnets across pfSense:
How exactly did you break and make these new connections?
I disconnected the desktop running pfSense from the network so now the buried cable connects straight into the 8-port switch in the house. Previously the cable went from the pfSense WAN interface and powered the LiteBeam with a PoE injector. (Another reason I am missing pfSense: no reboots in almost 365 days and counting)
When you stated a underground cable.. How did you connect into the line.. From the backend of the litebeam? Which is still 100ft away?
Yes, the LiteBeam is still about 100' from the house. It can only be powered by PoE which worked fine with the original configuration but now I have to keep the NanoSwitch in there to serve as a PoE injector/splitter to power both the EdgeRouter X and the LiteBeam.
Where did you place this new mesh AP? right next to the litebeam?
Correct. Here is a picture.

Looks to me you just put yourself behind the router outside, and its edge router vs pfsense now..
Correct. pfSense is currently disconnected from the network. If there was a $50 pfSense appliance I would have moved it outside and used that instead of the EdgeRouter X.
You don't show your pfsense in current drawing, or what IP space using behind it? Before you were using 192.168.2 behind pfsense, now your using that as you wan to pfsense? What did you change your pfsense lan network too?
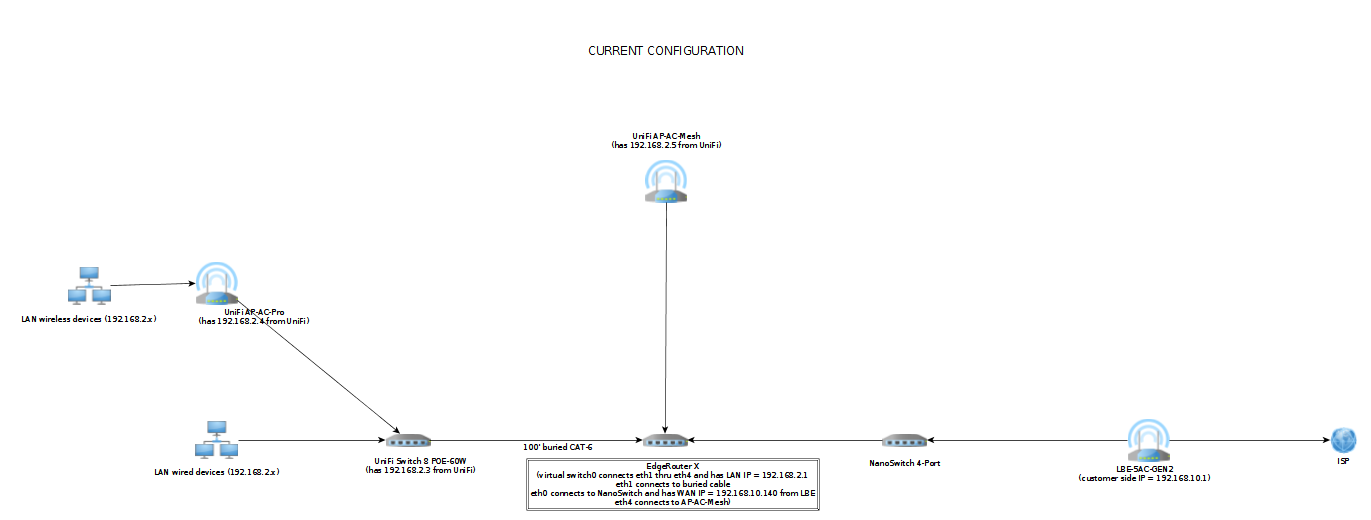
The LAN subnet is still 192.168.2.x but currently pfSense is not part of the configuration. The EdgeRouter is configured as the LAN's gateway (192.168.2.1).
You could for sure put pfsense behind a double nat, and this could work pretty easy with just correct routing and a transit network that your outside AP sits on..
I would be interested in continuing to run pfSense from behind the EdgeRouter as long as clients of the outdoor AP could still directly access the LAN, but someone would have to explain to me how to configure double natting. I would also be interested in running it on a bare bones/more efficient SBC; my old Dell Optiplex is consuming about 50W even just idling.
Here are a couple of better network diagrams. You'll notice that the NanoSwitch isn't really doing anything other than providing PoE power to both the EdgeRouter X and the LiteBeam.
-
@pyrocumulus said in Connect two subnets across pfSense:
I would be interested in continuing to run pfSense from behind the EdgeRouter as long as clients of the outdoor AP could still directly access the LAN
Yeah you just need to create a transit network..
Here is a logical drawing..
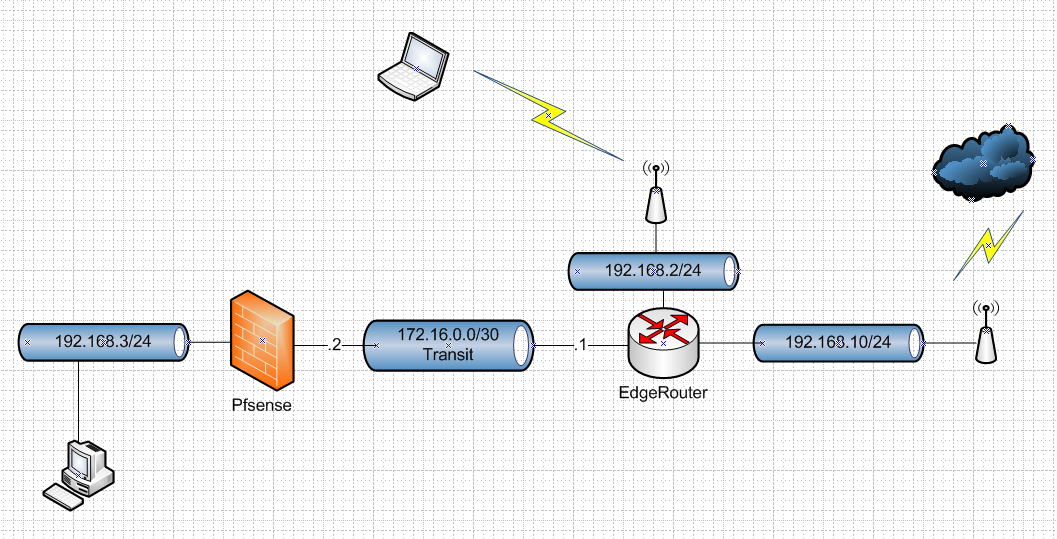
In such a setup you would really just disable nat on pfsense. And let your edgerouter do natting to the internet. You would just need to create a route on edgerouter to get to your 192.168.3 network your edgerouter.
Your devices on your AP would be able to access 192.168.3 you would just being routing and firewall rules.. If you need devices on this AP network and stuff behind pfsense they would not be on the same L2..
If you would just place a vlan capable switch out by the barn you could just do everything on the same L2 just behind pfsense.
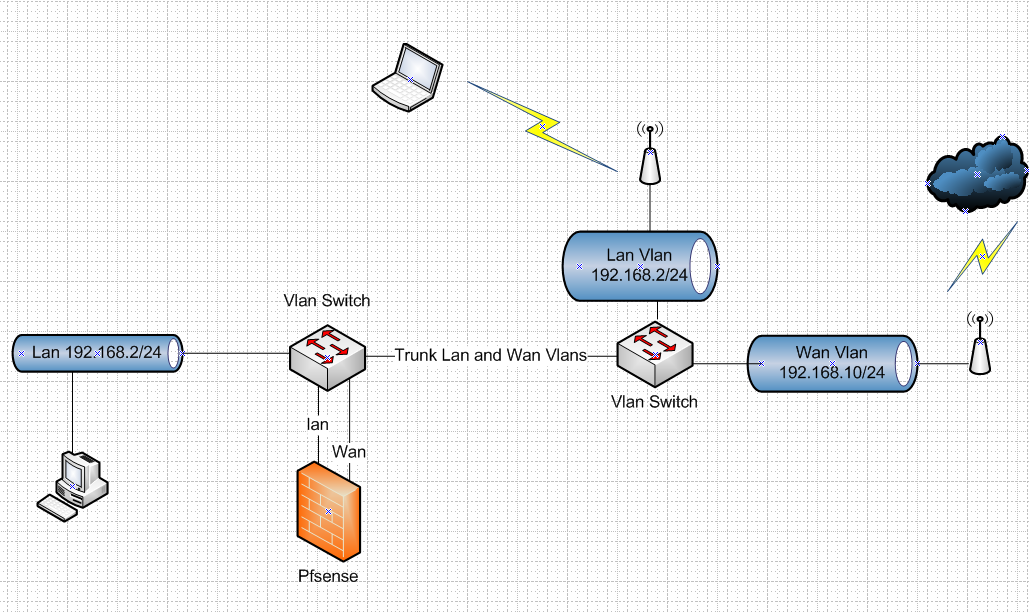
Your switch in the house is vlan capable, so you just need a switch in the barn that can do vlans. that unifi flex switch for example.
-
Couldn't the Edge Router serve as the outdoor VLAN-capable switch? The User Guide says it handles VLANs and I know it can create a virtual switch interface by switching together some of its ports.
https://dl.ubnt.com/guides/edgemax/EdgeOS_UG.pdf
-
Possible... I don't have one to play with... But sure if you could just use it as vlan capable switch then you could do that..
https://help.ui.com/hc/en-us/articles/217990978-EdgeRouter-Configure-an-EdgeRouter-as-a-Layer-2-Switch
-
@johnpoz
I'm beginning to confuse myself so I want to be sure I'm going the right direction before I screw up my network. I especially want to get the VLANs right before I re-introduce pfSense back into the configuration.Does this make sense for configuring the Edge Router X as an L2 switch with VLANs for your 2nd diagram above:
-leave switch0 connecting ports eth1 through eth4 as it currently is set up
-eth0 is connected to the LiteBeam (WAN) and continues to have the IP address it gets from the LiteBeam; untagged for VLAN10
-eth1 is connected to the ethernet cable going back to the switch in the house and serves as the trunk VLAN; untagged for VLAN10, tagged for VLAN2
-eth2 and eth3 are currently unused
-eth4 is connected to the outdoor mesh AP; untagged for VLAN2managed LAN switch in the house:
-all ports get untagged for VLAN2This was also useful:
https://help.ui.com/hc/en-us/articles/115012700967