Suricata-4.1.8 Update - Package Release Notes (for 32-bit ARM hardware appliances only)
-
Suricata-4.1.8 (32-bit ARM appliances only)
This update is specifically for 32-bit ARM hardware (Netgate SG-1000 and SG-3100)! It is available now for pfSense-2.5 DEVEL snapshot users, and it will be available in a few days for pfSense-2.4.5 RELEASE users of 32-bit ARM hardware.
Due to limitations around the use of the Rust language on legacy 32-bit ARM hardware, those platforms remain on the 4.1.x STABLE branch of the Suricata binary because that branch does not require Rust. The latest release in that branch is 4.1.8. Note that due to the absence of Rust, a number of new features introduced in versions 5.0 and later of Suricata are - and will remain - unavailable in the 4.1.x branch.
This version also removes entirely Barnyard2 support from Suricata since that port is no longer actively maintained and has a number of unpatched security vulnerabilities in its runtime-dependent shared libraries.
Installation Instructions:
It is strongly recommended that you install this new version by first removing Suricata from your firewall and then installing the update. This will help ensure the deprecated Barnyard2 package and its vulnerable shared libraries are removed. Your settings will be retained so long as you have the option to keep the existing configuration enabled on the GLOBAL SETTINGS tab of Suricata. That setting is enabled by default. You can verify it is "On" by checking the GLOBAL SETTINGS tab and then scrolling down to the General Settings section near the bottom of the page. See screenshot below.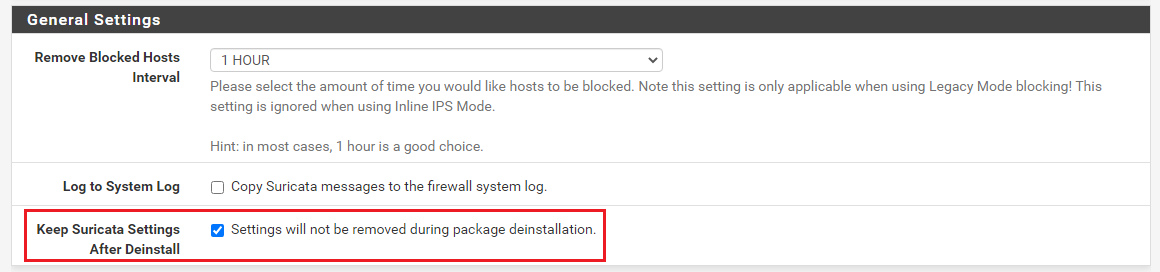
Major Functionality Changes:
- Remove all Barnyard2 support from the Suricata package. Barnyard2 is no longer actively maintained in FreeBSD ports and uses end-of-life MySQL database libraries with unpatched security vulnerabilities. Suricata upstream is also deprecating the Unified2 binary logging output option required by Barnyard2.
New Features:
- Added support for the Telegraf input.suricata plugin via a UNIX socket. See Redmine Feature Request #10421 for further details. Note that there may still issues with installing telgraf on 32-bit ARM hardware, and that without telgraf on the machine the new EVE stats logging integration cannot be used.
Bug Fixes:
-
Modify LOG MGMT cron task code to respect and use any user-specified custom File Store directory.
-
Add warning in Help Text for syslog export section on INTERFACE SETTINGS tab stating that the current FreeBSD syslog daemon will truncate exported messages to 480 bytes.
-
In
suricata_generate_yaml.php, test for both existence of file and a size greater than zero bytes before adding rules file to suricata.yaml conf file. This will prevent PHP warnings from non-existent files if user has a configured interface but zero selected rules. -
Fix lingering issues with Suricata log rotation and remove suricata_post_delete_logs() function. Send SIGHUP to Suricata when logs are rotated so it will reopen the files.
-
Change exit() to return() in GeoIP database download code so we don't possibly break out of pkg install script on a GeoIP download error and cause a failure to complete the installation of the GUI package.
-
Fix remaining occurences of the constant LOG_WARN in syslog() function calls instead of the proper LOG_WARNING constant. Redmine Issue #10751.
How To Use the New Feature
The new telgraf stats logging feature is available on the INTERFACE SETTINGS tab for each configured Suricata interface.Suricata performance stats integration with Telegraf
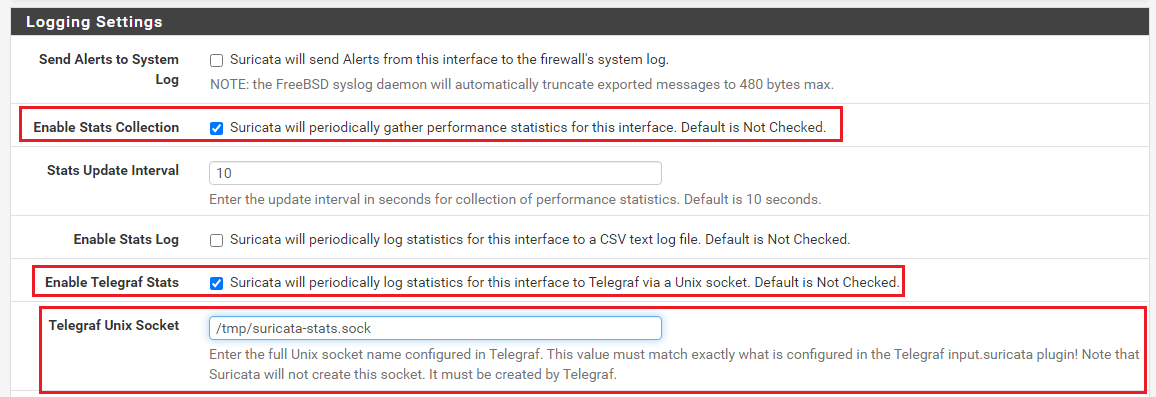
This update adds the ability for Suricata to send EVE-based performance statistics to a Telegraf instance installed on pfSense. To use this feature, you must configure the input.suricata plugin in Telegraf. Note the location and name of the UNIX socket created by Telgraf. Next, be sure the generation of performance stats is enabled in Suricata for the interface you want to monitor. When stats collection is enabled for an interface, you will see additional options appear for enabling the Telgraf integration. See the screenshot below. Note that you must provide the Telegraf-generated UNIX socket name and path to Suricata.