Проблемы с IPSEC IKEv2
-
Добрый день друзья. Прошу помочь постичь дзен.
Использовал официальный мануал. Перепробовал кучу инфы. В итоге остановился на этом мануале.Прям на коленках умоляю, дайте совет куда копать. Убил уже 4 дня на это включая выходные. Безрезультатно.
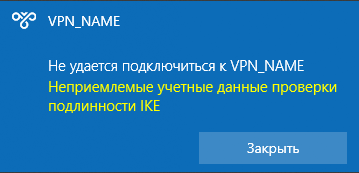
При подключении клиент выдает следующее:
Логи сервера:
Sep 2 00:10:27 charon 16[NET] <2> received packet: from IP_CLIENTA[500] to IP_SERVERA[500] (632 bytes) Sep 2 00:10:27 charon 16[ENC] <2> parsed IKE_SA_INIT request 0 [ SA KE No N(FRAG_SUP) N(NATD_S_IP) N(NATD_D_IP) V V V V ] Sep 2 00:10:27 charon 16[CFG] <2> looking for an IKEv2 config for IP_SERVERA...IP_CLIENTA Sep 2 00:10:27 charon 16[CFG] <2> candidate: IP_SERVERA...%any, prio 1052 Sep 2 00:10:27 charon 16[CFG] <2> found matching ike config: IP_SERVERA...%any with prio 1052 Sep 2 00:10:27 charon 16[IKE] <2> received MS NT5 ISAKMPOAKLEY v9 vendor ID Sep 2 00:10:27 charon 16[IKE] <2> received MS-Negotiation Discovery Capable vendor ID Sep 2 00:10:27 charon 16[IKE] <2> received Vid-Initial-Contact vendor ID Sep 2 00:10:27 charon 16[ENC] <2> received unknown vendor ID: 01:52:8b:bb:c0:06:96:12:18:49:ab:9a:1c:5b:2a:51:00:00:00:02 Sep 2 00:10:27 charon 16[IKE] <2> IP_CLIENTA is initiating an IKE_SA Sep 2 00:10:27 charon 16[IKE] <2> IKE_SA (unnamed)[2] state change: CREATED => CONNECTING Sep 2 00:10:27 charon 16[CFG] <2> selecting proposal: Sep 2 00:10:27 charon 16[CFG] <2> proposal matches Sep 2 00:10:27 charon 16[CFG] <2> received proposals: IKE:AES_CBC_256/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_2048, IKE:AES_CBC_256/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_2048, IKE:AES_CBC_256/HMAC_SHA2_384_192/PRF_HMAC_SHA2_384/MODP_2048 Sep 2 00:10:27 charon 16[CFG] <2> configured proposals: IKE:AES_CBC_256/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_2048 Sep 2 00:10:27 charon 16[CFG] <2> selected proposal: IKE:AES_CBC_256/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_2048 Sep 2 00:10:27 charon 16[IKE] <2> remote host is behind NAT Sep 2 00:10:27 charon 16[IKE] <2> sending cert request for "CN=CERT.NAME" Sep 2 00:10:27 charon 16[ENC] <2> generating IKE_SA_INIT response 0 [ SA KE No N(NATD_S_IP) N(NATD_D_IP) CERTREQ N(FRAG_SUP) N(CHDLESS_SUP) N(MULT_AUTH) ] Sep 2 00:10:27 charon 16[NET] <2> sending packet: from IP_SERVERA[500] to IP_CLIENTA[500] (481 bytes) Sep 2 00:10:27 charon 16[NET] <2> received packet: from IP_CLIENTA[4500] to IP_SERVERA[4500] (576 bytes) Sep 2 00:10:27 charon 16[ENC] <2> parsed IKE_AUTH request 1 [ EF(1/3) ] Sep 2 00:10:27 charon 16[ENC] <2> received fragment #1 of 3, waiting for complete IKE message Sep 2 00:10:27 charon 09[NET] <2> received packet: from IP_CLIENTA[4500] to IP_SERVERA[4500] (512 bytes) Sep 2 00:10:27 charon 09[ENC] <2> parsed IKE_AUTH request 1 [ EF(3/3) ] Sep 2 00:10:27 charon 09[ENC] <2> received fragment #3 of 3, waiting for complete IKE message Sep 2 00:10:27 charon 13[NET] <2> received packet: from IP_CLIENTA[4500] to IP_SERVERA[4500] (576 bytes) Sep 2 00:10:27 charon 13[ENC] <2> parsed IKE_AUTH request 1 [ EF(2/3) ] Sep 2 00:10:27 charon 13[ENC] <2> received fragment #2 of 3, reassembled fragmented IKE message (1500 bytes) Sep 2 00:10:27 charon 13[ENC] <2> parsed IKE_AUTH request 1 [ IDi CERTREQ N(MOBIKE_SUP) CPRQ(ADDR DNS NBNS SRV ADDR6 DNS6 SRV6) SA TSi TSr ] Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 0e:ac:82:60:40:56:27:97:e5:25:13:fc:2a:e1:0a:53:95:59:e4:a4 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid dd:bc:bd:86:9c:3f:07:ed:40:e3:1b:08:ef:ce:c4:d1:88:cd:3b:15 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 4a:5c:75:22:aa:46:bf:a4:08:9d:39:97:4e:bd:b4:a3:60:f7:a0:1d Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 04:15:fd:6e:d3:fb:30:cf:67:70:13:94:2f:f4:cc:18:84:f2:05:40 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 5c:b8:69:fe:8d:ef:c1:ed:66:27:ee:b2:12:0f:72:1b:b8:0a:0e:04 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 6a:47:a2:67:c9:2e:2f:19:68:8b:9b:86:61:66:95:ed:c1:2c:13:00 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 58:44:10:6d:20:05:69:23:be:1f:d5:42:ee:86:ba:96:7e:0a:84:e7 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 22:0e:70:51:35:c4:b6:a4:b0:ff:96:b6:ac:ea:06:cb:93:68:28:e9 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 01:f0:33:4c:1a:a1:d9:ee:5b:7b:a9:de:43:bc:02:7d:57:09:33:fb Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 88:4b:f5:23:8f:03:da:cf:f7:57:95:34:27:86:58:0c:46:b1:8b:fc Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 88:a9:5a:ef:c0:84:fc:13:74:41:6b:b1:63:32:c2:cf:92:59:bb:3b Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid f9:27:b6:1b:0a:37:f3:c3:1a:fa:17:ec:2d:46:17:16:12:9d:0c:0e Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 34:4f:30:2d:25:69:31:91:ea:f7:73:5c:ab:f5:86:8d:37:82:40:ec Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 3e:df:29:0c:c1:f5:cc:73:2c:eb:3d:24:e1:7e:52:da:bd:27:e2:f0 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 7c:32:d4:85:fd:89:0a:66:b5:97:ce:86:f4:d5:26:a9:21:07:e8:3e Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 64:1d:f8:d5:0e:23:31:c2:29:b2:50:cb:32:f5:6d:f5:5c:8e:00:fa Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid b3:86:36:7d:bc:e5:f8:4e:e2:8c:15:37:81:b2:1d:f5:3d:2c:15:cd Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid e1:a0:5a:95:34:75:78:a7:ff:4d:cf:32:52:5d:f2:f8:2c:1a:e1:15 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid da:ed:64:74:14:9c:14:3c:ab:dd:99:a9:bd:5b:28:4d:8b:3c:c9:d8 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 5e:8c:53:18:22:60:1d:56:71:d6:6a:a0:cc:64:a0:60:07:43:d5:a8 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 86:26:cb:1b:c5:54:b3:9f:bd:6b:ed:63:7f:b9:89:a9:80:f1:f4:8a Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid a8:e3:02:96:70:a6:8b:57:eb:ec:ef:cc:29:4e:91:74:9a:d4:92:38 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid f7:93:19:ef:df:c1:f5:20:fb:ac:85:55:2c:f2:d2:8f:5a:b9:ca:0b Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 30:a4:e6:4f:de:76:8a:fc:ed:5a:90:84:28:30:46:79:2c:29:15:70 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid c4:30:28:c5:d3:e3:08:0c:10:44:8b:2c:77:ba:24:53:97:60:bb:f9 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid a2:af:24:0a:da:e8:67:79:c8:a8:50:b3:c7:46:ee:d9:f7:1b:16:78 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 73:97:82:ea:b4:04:16:6e:25:d4:82:3c:37:db:f8:a8:12:fb:cf:26 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 69:9f:1b:7a:e9:b8:da:18:49:6c:60:8b:ce:4f:4e:aa:f9:f0:b7:aa Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 69:c4:27:db:59:69:68:18:47:e2:52:17:0a:e0:e5:7f:ab:9d:ef:0f Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid ba:42:b0:81:88:53:88:1d:86:63:bd:4c:c0:5e:08:fe:ea:6e:bb:77 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 87:db:d4:5f:b0:92:8d:4e:1d:f8:15:67:e7:f2:ab:af:d6:2b:67:75 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 6e:58:4e:33:75:bd:57:f6:d5:42:1b:16:01:c2:d8:c0:f5:3a:9f:6e Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 4a:81:0c:de:f0:c0:90:0f:19:06:42:31:35:a2:a2:8d:d3:44:fd:08 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid d5:2e:13:c1:ab:e3:49:da:e8:b4:95:94:ef:7c:38:43:60:64:66:bd Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 6c:ca:bd:7d:b4:7e:94:a5:75:99:01:b6:a7:df:d4:5d:1c:09:1c:cc Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid ab:30:d3:af:4b:d8:f1:6b:58:69:ee:45:69:29:da:84:b8:73:94:88 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 42:32:b6:16:fa:04:fd:fe:5d:4b:7a:c3:fd:f7:4c:40:1d:5a:43:af Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid a5:06:8a:78:cf:84:bd:74:32:dd:58:f9:65:eb:3a:55:e7:c7:80:dc Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid e2:7f:7b:d8:77:d5:df:9e:0a:3f:9e:b4:cb:0e:2e:a9:ef:db:69:77 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 6d:aa:9b:09:87:c4:d0:d4:22:ed:40:07:37:4d:19:f1:91:ff:de:d3 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 83:31:7e:62:85:42:53:d6:d7:78:31:90:ec:91:90:56:e9:91:b9:e3 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 3b:37:c0:c5:47:3d:fc:5b:9a:0d:01:5b:12:3b:53:cc:ad:b7:54:66 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 3e:22:d4:2c:1f:02:44:b8:04:10:65:61:7c:c7:6b:ae:da:87:29:9c Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid b1:81:08:1a:19:a4:c0:94:1f:fa:e8:95:28:c1:24:c9:9b:34:ac:c7 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 21:0f:2c:89:f7:c4:cd:5d:1b:82:5e:38:d6:c6:59:3b:a6:93:75:ae Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 23:4b:71:25:56:13:e1:30:dd:e3:42:69:c9:cc:30:d4:6f:08:41:e0 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid bb:c2:3e:29:0b:b3:28:77:1d:ad:3e:a2:4d:bd:f4:23:bd:06:b0:3d Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid c8:95:13:68:01:97:28:0a:2c:55:c3:fc:d3:90:f5:3a:05:3b:c9:fb Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid ee:e5:9f:1e:2a:a5:44:c3:cb:25:43:a6:9a:5b:d4:6a:25:bc:bb:8e Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 17:4a:b8:2b:5f:fb:05:67:75:27:ad:49:5a:4a:5d:c4:22:cc:ea:4e Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 68:33:0e:61:35:85:21:59:29:83:a3:c8:d2:d2:e1:40:6e:7a:b3:c1 Sep 2 00:10:27 charon 13[IKE] <2> received cert request for unknown ca with keyid 4f:9c:7d:21:79:9c:ad:0e:d8:b9:0c:57:9f:1a:02:99:e7:90:f3:87 Sep 2 00:10:27 charon 13[IKE] <2> received 52 cert requests for an unknown ca Sep 2 00:10:27 charon 13[CFG] <2> looking for peer configs matching IP_SERVERA[%any]...IP_CLIENTA[192.168.100.2] Sep 2 00:10:27 charon 13[CFG] <2> candidate "con-mobile", match: 1/1/1052 (me/other/ike) Sep 2 00:10:27 charon 13[CFG] <con-mobile|2> selected peer config 'con-mobile' Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> initiating EAP_IDENTITY method (id 0x00) Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> processing INTERNAL_IP4_ADDRESS attribute Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> processing INTERNAL_IP4_DNS attribute Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> processing INTERNAL_IP4_NBNS attribute Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> processing INTERNAL_IP4_SERVER attribute Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> processing INTERNAL_IP6_ADDRESS attribute Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> processing INTERNAL_IP6_DNS attribute Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> processing INTERNAL_IP6_SERVER attribute Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> peer supports MOBIKE, but disabled in config Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> authentication of 'CERT.NAME' (myself) with RSA signature successful Sep 2 00:10:27 charon 13[IKE] <con-mobile|2> sending end entity cert "CN=CERT.NAME" Sep 2 00:10:27 charon 13[ENC] <con-mobile|2> generating IKE_AUTH response 1 [ IDr CERT AUTH EAP/REQ/ID ] Sep 2 00:10:27 charon 13[ENC] <con-mobile|2> splitting IKE message (1260 bytes) into 2 fragments Sep 2 00:10:27 charon 13[ENC] <con-mobile|2> generating IKE_AUTH response 1 [ EF(1/2) ] Sep 2 00:10:27 charon 13[ENC] <con-mobile|2> generating IKE_AUTH response 1 [ EF(2/2) ] Sep 2 00:10:27 charon 13[NET] <con-mobile|2> sending packet: from IP_SERVERA[4500] to IP_CLIENTA[4500] (1248 bytes) Sep 2 00:10:27 charon 13[NET] <con-mobile|2> sending packet: from IP_SERVERA[4500] to IP_CLIENTA[4500] (80 bytes) Sep 2 00:10:31 charon 09[CFG] vici client 55 connected Sep 2 00:10:31 charon 13[CFG] vici client 55 registered for: list-sa Sep 2 00:10:31 charon 13[CFG] vici client 55 requests: list-sas Sep 2 00:10:31 charon 13[CFG] vici client 55 disconnected Sep 2 00:10:37 charon 05[CFG] vici client 56 connected Sep 2 00:10:37 charon 10[CFG] vici client 56 registered for: list-sa Sep 2 00:10:37 charon 07[CFG] vici client 56 requests: list-sas Sep 2 00:10:37 charon 07[CFG] vici client 56 disconnected Sep 2 00:10:43 charon 06[CFG] vici client 57 connected Sep 2 00:10:43 charon 14[CFG] vici client 57 registered for: list-sa Sep 2 00:10:43 charon 08[CFG] vici client 57 requests: list-sas Sep 2 00:10:43 charon 14[CFG] vici client 57 disconnected Sep 2 00:10:49 charon 13[CFG] vici client 58 connected Sep 2 00:10:49 charon 16[CFG] vici client 58 registered for: list-sa Sep 2 00:10:49 charon 16[CFG] vici client 58 requests: list-sas Sep 2 00:10:49 charon 09[CFG] vici client 58 disconnected Sep 2 00:10:55 charon 07[CFG] vici client 59 connected Sep 2 00:10:55 charon 05[CFG] vici client 59 registered for: list-sa Sep 2 00:10:55 charon 05[CFG] vici client 59 requests: list-sas Sep 2 00:10:55 charon 05[CFG] vici client 59 disconnected Sep 2 00:10:57 charon 15[JOB] <con-mobile|2> deleting half open IKE_SA with IP_CLIENTA after timeout Sep 2 00:10:57 charon 15[IKE] <con-mobile|2> IKE_SA con-mobile[2] state change: CONNECTING => DESTROYING -
Добрый.
@glifedИспользовал официальный мануал.
Этот https://docs.netgate.com/pfsense/en/latest/vpn/ipsec/configuring-an-ipsec-remote-access-mobile-vpn-using-ikev2-with-eap-mschapv2.html ?
В гугле по фразе из Вашего лога ниже пробовали?
received cert request for unknown ca with keyid
https://forum.netgate.com/topic/106374/ipsec-ikev2-eap-tls-received-cert-requests-for-unknown-ca/
Regarding the import of the certificate, I again followed every step in the tutorial and I can see the certificate authority in the certificate store.
Как можно 4 дня (если это правда, конечно) искать не глянув прежде оф. доку? Люди, человеки, вы совсем думать разучились?
-
@werter Уже просто "смотрю в книгу вижу фигу"
Сертификат ставил на Текушего пользователя а не на Локальный компьютер.
Все заработало спасибо.