webGUI & Certificate
-
I created the CA and Server Certificate and imported but browser always say me invalid certificate.
I'm trying to config squid too (https splice whitelist, bump otherwise) and when i type pfsense ip browser give me this error:
ERROR
The requested URL could not be retrieved
The following error was encountered while trying to retrieve the URL: https://192.xxx.xxx.xxx/*Failed to establish a secure connection to 192.xxx.xxx.xxx
The system returned:
(92) Protocol error (TLS code: X509_V_ERR_SELF_SIGNED_CERT_IN_CHAIN)
Self-signed SSL Certificate in chain: /CN='CA NAME' CA/O=home/OU=homeThis proxy and the remote host failed to negotiate a mutually acceptable security settings for handling your request. It is possible that the remote host does not support secure connections, or the proxy is not satisfied with the host security credentials.
Your cache administrator is admin@localhost.
-
@falassion said in webGUI & Certificate:
I created the CA and Server Certificate and imported but browser always say me invalid certificate.
Because :
@falassion said in webGUI & Certificate:
Self-signed SSL Certificate in chain:
so, what about creating a certificate that your browser trusts ? That what's the pfSense acme.sh package is all about.
or, inform your browser that it should trusted your self made made certificate - see the browser's doc how to do so. -
I already imported certificate in browser trusted certificate but still give me this error. I will install Acme package
-
@falassion said in webGUI & Certificate:
I will install Acme package
ACME obtains trusted certificates from Letsencrypt.
You have to have a domain name, something like your-domain.tld.
Check that the registrar where you got your " your-domain.tld" from has the possibility to support a method that acme.sh uses to obtain the certificate. -
@falassion said in webGUI & Certificate:
This proxy and the remote host failed to negotiate
So your trying to access pfsense gui via a proxy?
Your going to have to provide a bit more info if you want help.. Creating a CA and then a cert using for your webgui is pretty clickity clickity.. But without some details of what your actually doing, what browser? Details of your cert nobody is going to be able to help you find what your doing wrong.
That looks like sslbump error.. How about you get a cert working with just the gui, before you try using sslbump with your proxy to do mitm..
For you to use IP with webgui and cert, you would have to put the SAN in the cert for the IP your going to use..
-
Yeah, just checked again. I'm using the same 'known, old and mature' browser. It still offers the possibly to trust your own CA and certificates.
A simple Google-it-up lead me to the answer. Works well.
Ok, takes 3 or 4 clicks now, not one. -
Hi, thanks all.
I think proxy error is related to the certificate problem. Every browser in the lan I use to connect to pfsense give me certificate alert/error. After forcing it I can log in.
I’m sorry but I’m newbie in pfsense and certificate’s logic and function and I’m trying to learn.
I believed that with a certificate imported and manually trusted from the browser it would no longer give me any error.
What do you need for help me ?
-
Again - turn off your proxy... Get your cert working with just pfsense and direct access to the gui. Not trying to use a proxy..
I must of gone over this 3 or 4 times already.. Here is somewhat recent post with explicit walk thru of how to setup ca and cert your browser trusts
https://forum.netgate.com/post/831783
Only change since then is browsers don't like certs that long any more.. Set it for like 1 year for length vs 10 years.. Or browsers might balk at it..
-
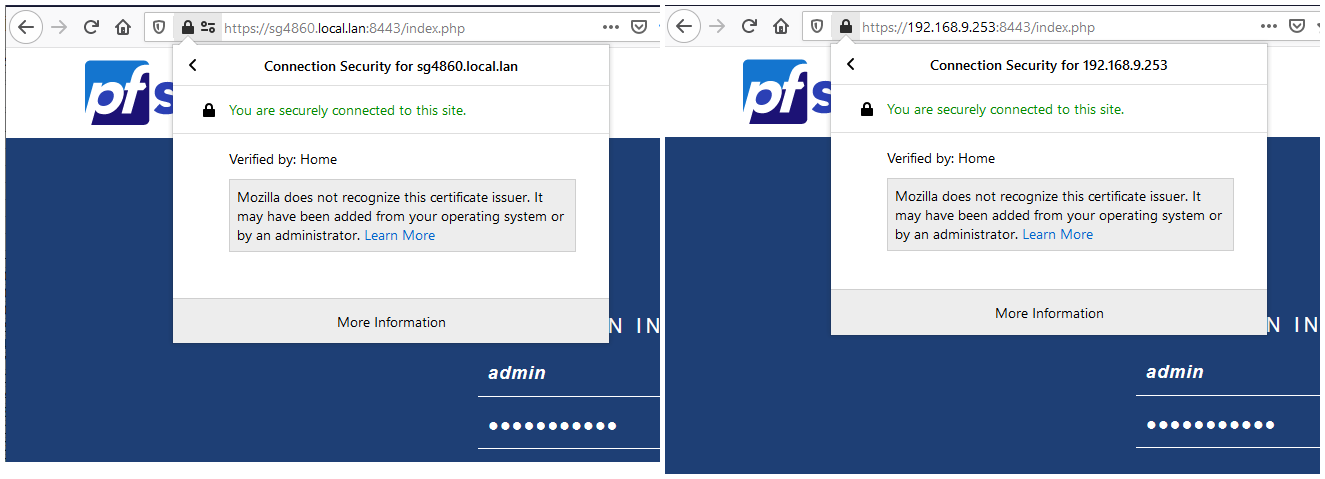
Ok I followed your suggestions and now with the IP the certificate work!
I don't know how set up your settings name.local.lan, have you some guide to read? I haven't found any guides
If i try to connect via Proxy error remain ...
-
@falassion Use whatever domain you want.. I use local.lan, you could use something.tld