Hosting nextcloud behind 1 WAN
-
Hello,
I am having difficulty configuring my sg-2100 NAT for my opt vlan that hosts my nextcloud server and acts as a dmz. I have the opt configured, I need to configure:
SERVER (OPT1) <-> WAN <->Nameserver/DNSSince I only have 1 WAN, I assume that I must use haproxy. This should also increase security somewhat from what I have read. Any assistance would be appreciated as I am stumped.
-
Don't you just make a NAT rule to the http or https port...? I'd put your firewall on an alternative port like 8081 so you can manage your firewall like https://ip:8081 (or some other port) and then simply NAT your nextcloud to http and https > vlan IP.
Should work no...?
-
@wolfsden3 I do server side setup, dove into this without realizing how complex the config is. There's so many choices and conflicting answers that I am beyond confused. Currently the wan takes me to the pfsense page, my thoughts were using haproxy to both mask and separate the pfsense dchp server and the nextcloud server
-
I wouldn't because, in my view, that complicates things.
You have two services that need http and https. You have to pic one for each port.
In a virtual server setup you can serve http and https depending on the host name request.
1 server > 2 websites
Unfortunately you have...
2 servers > 2 websites (your firewall http and your nextcloud http)
This is why you need to (again, in my view):
1 - Go to: system > advanced > change your port to something else, like me. I serve it on port 10000
- Note: You will want to first make a firewall rule to allow port 10000 on your WAN. Firewall > Rules > Floating allow any to 10000 TCP

Here's the advanced web port change.
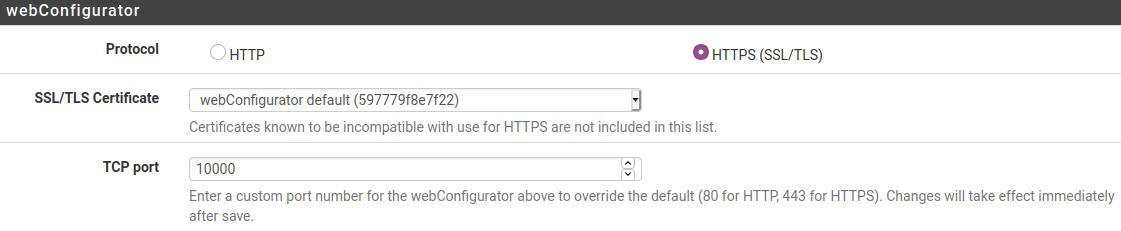
Once you change your web port on your firewall from http port 80 /https port 443 > you've free'd those up to be used on something else. Now you're doing http/https on port 10000 :-)
Now you can make a NAT rule:
firewall > nat > that says, anything from your WAN on http port 80 and https port 443 > go to your private IP 192.168.1.whatever (or whatever private IP's you're using).
Hope that helps.
That's how we've done these things in the past. Not using standard ports on your firewall for web management helps cut down on the BS even though they'll find you eventually. 10000 is a common port used in web servers as is 8080, and many others.
Alternatively, you could host your nextcloud on an alternative port too like 4434 or something and NAT 4434 > 443 on your private LAN side too. That would maintain the firewall defaults BUT we've found when publishing your owncloud URL that people will often hit the firewall interface not knowing they need to type in https://ip_address_here:4434
...so it can get confusing.Always take a backup of your firewall before making and testing these changes :)