Multi-WAN OpenVPN Setup
-
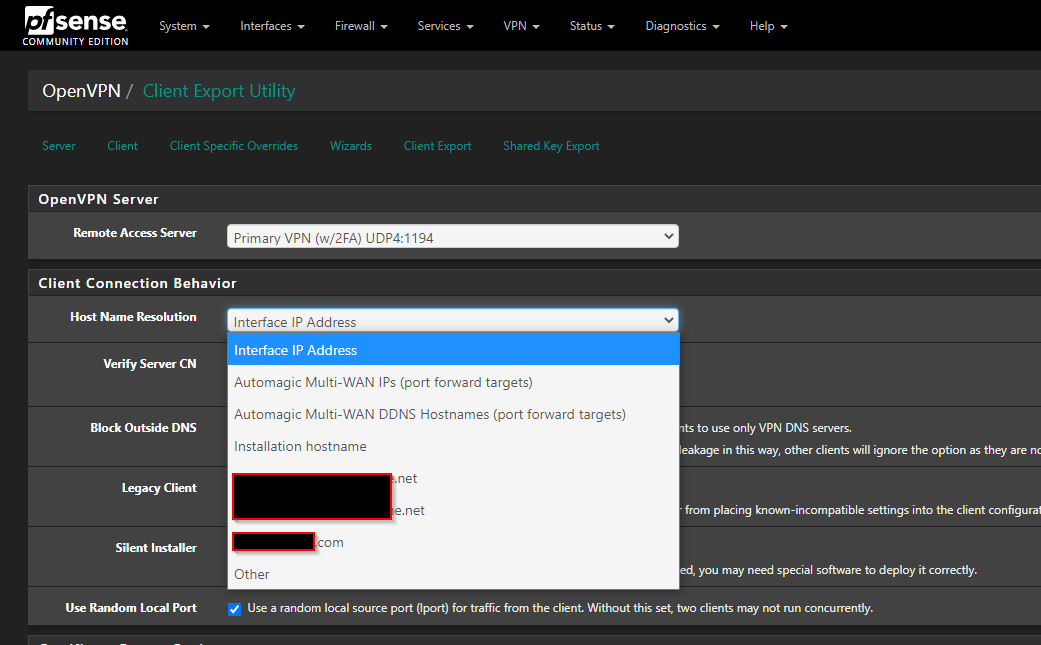
So we just recently got a 2FA system set up and I'm working on configuring a new OpenVPN server to use this. In the process I thought it would be nice to have some failover capability since we have two WAN connections now. Currently the VPN is tied to a single WAN so if that goes down so does the VPN connection. I was following the steps in this kb from netgate and was planning to use the gateway group failover method. What I'm wondering is when I do the client export which option should I choose for "Host Name Resolution" setting? For our existing VPN we were using a dynamic dns hostname which was nice when we recently changed our static IP's as I didn't have to go update all the clients. Not sure if something similar could be implemented in a multi-WAN VPN environment. Thoughts?
-
@snewby
If you've set it to listen on loopback and make the port forwards, and have DDNS setup on both WANs, you can use the automagic DDNS option. I've done it with static DNS, in that case I pick 'other', point it to vpn.company.com and add vpn2.company.com as a custom option. If you had statics and didn't care about DNS, you could use the automagic IPs option. -
@dotdash thanks for the reply. I actually wasn't planning to use the port-forward method at all but rather just a simple gateway failover group as the "interface" on the VPN server as outlined at the beginning of the kb I linked to. I was just trying to figure out if there was a way to use that method but still have DDNS hostnames.
-
@snewby
I've never tried the failover group method, but you may need to configure like I do for static DNS: select other, use foo.dyndns.org for the hostname, and add -
server bar.dyndns.org
to the custom options. (foo and bar being your DDNS hostnames for WAN1/2) -
@dotdash I wanted to follow up on this. I decided the port-forward method was the most flexible so I am going that route. I am going to be using DNS entries for the host name resolution as I feel this gives me greater flexibility down the road such as not having to update all our clients if the IP changes. What I wondering now is I watched a video that was talking about a multi-wan setup and they mentioned with the port-forwarding method you can also have openvpn running on multiple ports or at least have failover to alternative ports. This would be great for us because sometimes our users may be on a network with a restrictive firewall that blocks 1194. I know I could setup another openVPN server instance with the alternate port (i.e 443) but I wasn't sure if that was necessary or not, I'm trying to keep the set up as clean as possible. I also wasn't sure if there needs to be some configuration in the client for this failover to the alternate port to occur. Any thoughts?
-
@snewby
You can configure the OpenVPN server to listen on localhost and forward both ports to it.
However, consider that if your primary OpenVPN is on 1194 UDP, the secondary port has also be on UDP. But 443 UDP might be blocked in some public wifi as well, while 443 TCP is allowed. To use this you will have to set up an additional server, or you configure your primary connection for TCP as well. But that might result in lower throughput.Whatever protocol you use, in the client config you need an additional remote line for the secondary connection. You can add this in the client export utility in the advanced options by entering a line similar this:
remote <yourWANIP> 443 tcpIf you set up a additional server for port 443 TCP ensure that you make all settings equal to the primary apart from port and protocol.
-
@viragomann I thought maybe I could choose the "TCP/UDP" option in the port-forward rule to negate the need for two servers but I guess you're right the OpenVPN server instance itself can't listen on both TCP & UPD at the same time so you'd need two servers. Also I tested a failover with multi-wan and it worked but it seemed to be very slow to failover to the second WAN, like 3-5 minutes. Ideally the failover would happen much faster. Any thoughts on that? I have multiple remote servers specified in the client config. I am not using the remote-random option as I always want the client to connect to the primary WAN unless it is down.
-
@snewby
At failover the client has to recognize that the server does not respond anymore and then establish a new connection to the other IP. This might take some time, but should be far less then 3 minutes.Maybe a check at System > Advanced > Miscellaneous > State Killing on Gateway Failure can help.
-
@viragomann I tried disabling the port-forward rule but the connection didn't drop at all. Maybe I need to kill the states on the firewall but can't do that during production hours without disruption. I haven't actually disconnected the primary WAN either. I suppose I could try that after hours for a real test. I'm adding 2FA to our VPN connections so this is the perfect time to make the connections more robust with failover as well.