OpenVPN connectivity to ExpressVPN in v 2.5.2
-
I have followed the instructions provided by ExpressVPN to setup ExpressVPN on pfSense, however the instructions are for pfSense 2.4.5. I have recently started using pfSense 2.5.2 on a Protectli appliance. Having followed the setup instructions, and checking status of OpenVPN, I get an "Unable to contact deamon" message related to the Remote Host. Anyone been able to get ExpressVPN working on v 2.5.2?
-
@maxpro
There might be something wrong in your OpenVPN configuration.
What shows the Status > System Logs > OpenVPN Log? -
@viragomann
This is what I have...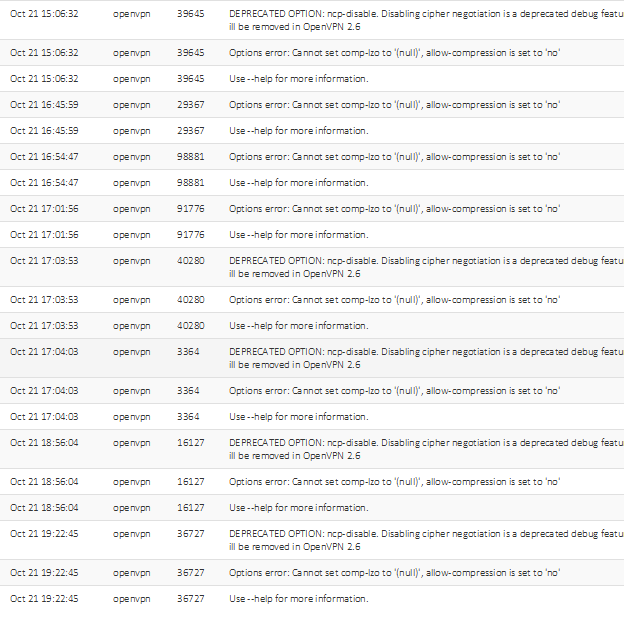
-
@maxpro
So presumably something wrong with the compression setting.
Did you configure the client in the GUI or did you import the ovpn file? You should use the GUI to set it up. -
@viragomann I followed the instructions provided by ExpressVPN for setting up on psSense which takes you through the settings via the GUI I believe. But you have to provide the client , TLS certificates and password, etc from Express VPN
-
@maxpro said in OpenVPN connectivity to ExpressVPN in v 2.5.2:
I followed the instructions provided by ExpressVPN for setting up on psSense
OMG. Try remove the custom options. All, there might be no need for any.
-
@viragomann Interesting discovery. From the step-up guide from ExpressVPN, compression should be set to "Adaptive LZO Compression [Legacy, comp-izo adaptive]" However, from the GUI, I can't find anywhere to make this selection in 2.5.2. However, in the OpenVPN wizard, there is a selection for compression where I can make this change. However, in the wizard, I must input the Tunnel Network. Given I am new to this, I do not know what this is vs the Local Network, both of which I would need to input in the wizard.
-
@maxpro
I'm not using 2.5.2 yet, but in 2.4.5 the wizard is for setting up a server instance only, not a client. So it cannot be used here.On the ExpressVPN client the Tunnel Network and Local and Remote Networks should leave blank.
-
@maxpro said in OpenVPN connectivity to ExpressVPN in v 2.5.2:
I have followed the instructions provided by ExpressVPN to setup ExpressVPN on pfSens
With pfSense 2.5.2 you use OpenVPN 2.5.x :
[2.5.2-RELEASE][admin@pfsense.mypfsense.net]/root: openvpn --version OpenVPN 2.5.2 amd64-portbld-freebsd12.2 [SSL (OpenSSL)] [LZO] [LZ4] [MH/RECVDA] [AEAD] built on Jun 24 2021 library versions: OpenSSL 1.1.1k-freebsd 25 Mar 2021, LZO 2.10 Originally developed by James Yonan Copyright (C) 2002-2018 OpenVPN Inc <sales@openvpn.net> ....or, the "pfSense to ExpressVPN" guide you followed is based on .... NOT openVPN 2.5.2 but some older 2.4.x version.
When versions change, the rules (might) change. In this case, they actually did.
Another issue : the errors : whenever a process starts and it spits out logs line with the word 'error' in it, you redo the set up. Up until there are no more errors logged.
Basically, to make pfSense (OpenVPN client 2.5.2) connect to xprssVPN (do we know what version of OpenVPN they use - an older 2.4.x or a newer version ?) I had to fall back to he official OpenVPN special "RTFM" instructions - especially the "what did we change / you didn't know this".
@viragomann said in OpenVPN connectivity to ExpressVPN in v 2.5.2:
Try remove the custom options.
Very true.
After setting up the OpenVPN client, using the GUI, I compare the created openvpn client config file for "strange things" like options that are present multiple times, or even contradictory.I've added "custom options" these :
verify-x509-name Server name-prefix; remote-cert-tls server; route-delay 2; tun-mtu 1500; fragment 1300; mssfix 1450; auth-nocache;The connection logs (in reverse order) :
2021-10-22 12:39:45.217054+02:00 openvpn 7206 Initialization Sequence Completed
2021-10-22 12:39:45.216018+02:00 openvpn 7206 /sbin/route add -net 10.104.0.1 10.104.0.109 255.255.255.255
2021-10-22 12:39:45.214972+02:00 openvpn 7206 /sbin/route add -net 128.0.0.0 10.104.0.109 128.0.0.0
2021-10-22 12:39:45.213933+02:00 openvpn 7206 /sbin/route add -net 0.0.0.0 10.104.0.109 128.0.0.0
2021-10-22 12:39:45.212679+02:00 openvpn 7206 /sbin/route add -net 45.91.22.2 192.168.10.1 255.255.255.255
2021-10-22 12:39:43.054623+02:00 openvpn 7206 /usr/local/sbin/ovpn-linkup ovpnc2 1500 1629 10.104.0.110 10.104.0.109 init
2021-10-22 12:39:43.049492+02:00 openvpn 7206 /sbin/ifconfig ovpnc2 10.104.0.110 10.104.0.109 mtu 1500 netmask 255.255.255.255 up
2021-10-22 12:39:43.049346+02:00 openvpn 7206 TUN/TAP device /dev/tun2 opened
2021-10-22 12:39:43.049090+02:00 openvpn 7206 TUN/TAP device ovpnc2 exists previously, keep at program end
2021-10-22 12:39:43.049058+02:00 openvpn 7206 ROUTE_GATEWAY 192.168.10.1/255.255.255.0 IFACE=em0 HWADDR=00:15:17:77:d1:19
2021-10-22 12:39:43.048918+02:00 openvpn 7206 Incoming Data Channel: Using 512 bit message hash 'SHA512' for HMAC authentication
2021-10-22 12:39:43.048897+02:00 openvpn 7206 Incoming Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
2021-10-22 12:39:43.048886+02:00 openvpn 7206 Outgoing Data Channel: Using 512 bit message hash 'SHA512' for HMAC authentication
2021-10-22 12:39:43.048871+02:00 openvpn 7206 Outgoing Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
2021-10-22 12:39:43.048775+02:00 openvpn 7206 Using peer cipher 'AES-256-CBC'
2021-10-22 12:39:43.048766+02:00 openvpn 7206 OPTIONS IMPORT: adjusting link_mtu to 1629
2021-10-22 12:39:43.048758+02:00 openvpn 7206 OPTIONS IMPORT: peer-id set
2021-10-22 12:39:43.048750+02:00 openvpn 7206 OPTIONS IMPORT: --ip-win32 and/or --dhcp-option options modified
2021-10-22 12:39:43.048742+02:00 openvpn 7206 OPTIONS IMPORT: route options modified
2021-10-22 12:39:43.048734+02:00 openvpn 7206 OPTIONS IMPORT: --ifconfig/up options modified
2021-10-22 12:39:43.048723+02:00 openvpn 7206 OPTIONS IMPORT: compression parms modified
2021-10-22 12:39:43.048712+02:00 openvpn 7206 OPTIONS IMPORT: timers and/or timeouts modified
2021-10-22 12:39:43.048619+02:00 openvpn 7206 PUSH: Received control message: 'PUSH_REPLY,redirect-gateway def1,dhcp-option DNS 10.104.0.1,comp-lzo no,route 10.104.0.1,topology net30,ping 10,ping-restart 60,ifconfig 10.104.0.110 10.104.0.109,peer-id 71'
2021-10-22 12:39:42.923540+02:00 openvpn 7206 SENT CONTROL [Server-2776-4a]: 'PUSH_REQUEST' (status=1)
2021-10-22 12:39:41.762346+02:00 openvpn 7206 [Server-2776-4a] Peer Connection Initiated with [AF_INET]45.91.22.2:1195
2021-10-22 12:39:41.760188+02:00 openvpn 7206 Control Channel: TLSv1.3, cipher TLSv1.3 TLS_AES_256_GCM_SHA384, peer certificate: 2048 bit RSA, signature: RSA-SHA256
2021-10-22 12:39:41.723001+02:00 openvpn 7206 VERIFY OK: depth=0, C=VG, ST=BVI, O=ExpressVPN, OU=ExpressVPN, CN=Server-2776-4a, emailAddress=support@expressvpn.com
2021-10-22 12:39:41.722944+02:00 openvpn 7206 VERIFY X509NAME OK: C=VG, ST=BVI, O=ExpressVPN, OU=ExpressVPN, CN=Server-2776-4a, emailAddress=support@expressvpn.com
2021-10-22 12:39:41.722897+02:00 openvpn 7206 VERIFY EKU OK
2021-10-22 12:39:41.722849+02:00 openvpn 7206 ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Server Authentication
2021-10-22 12:39:41.722798+02:00 openvpn 7206 Validating certificate extended key usage
2021-10-22 12:39:41.722746+02:00 openvpn 7206 VERIFY KU OK
2021-10-22 12:39:41.722222+02:00 openvpn 7206 VERIFY OK: depth=1, C=VG, ST=BVI, O=ExpressVPN, OU=ExpressVPN, CN=ExpressVPN CA, emailAddress=support@expressvpn.com
2021-10-22 12:39:41.722066+02:00 openvpn 7206 VERIFY WARNING: depth=1, unable to get certificate CRL: C=VG, ST=BVI, O=ExpressVPN, OU=ExpressVPN, CN=ExpressVPN CA, emailAddress=support@expressvpn.com
2021-10-22 12:39:41.721949+02:00 openvpn 7206 VERIFY WARNING: depth=0, unable to get certificate CRL: C=VG, ST=BVI, O=ExpressVPN, OU=ExpressVPN, CN=Server-2776-4a, emailAddress=support@expressvpn.com
2021-10-22 12:39:41.696122+02:00 openvpn 7206 TLS: Initial packet from [AF_INET]45.91.22.2:1195, sid=294829c6 d3609128
2021-10-22 12:39:41.674603+02:00 openvpn 7206 UDPv4 link remote: [AF_INET]45.91.22.2:1195
2021-10-22 12:39:41.674592+02:00 openvpn 7206 UDPv4 link local (bound): [AF_INET]192.168.10.3:0
2021-10-22 12:39:41.674575+02:00 openvpn 7206 Socket Buffers: R=[42080->524288] S=[57344->524288]
2021-10-22 12:39:41.674550+02:00 openvpn 7206 TCP/UDP: Preserving recently used remote address: [AF_INET]45.91.22.2:1195
2021-10-22 12:39:41.674252+02:00 openvpn 7206 Incoming Control Channel Authentication: Using 512 bit message hash 'SHA512' for HMAC authentication
2021-10-22 12:39:41.674161+02:00 openvpn 7206 Outgoing Control Channel Authentication: Using 512 bit message hash 'SHA512' for HMAC authentication
2021-10-22 12:39:41.673905+02:00 openvpn 7206 WARNING: experimental option --capath /var/etc/openvpn/client2/ca
2021-10-22 12:39:41.672766+02:00 openvpn 7206 NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
2021-10-22 12:39:41.672665+02:00 openvpn 7206 MANAGEMENT: unix domain socket listening on /var/etc/openvpn/client2/sock
2021-10-22 12:39:41.671745+02:00 openvpn 7156 library versions: OpenSSL 1.1.1k-freebsd 25 Mar 2021, LZO 2.10
2021-10-22 12:39:41.671733+02:00 openvpn 7156 OpenVPN 2.5.2 amd64-portbld-freebsd12.2 [SSL (OpenSSL)] [LZO] [LZ4] [MH/RECVDA] [AEAD] built on Jun 24 2021Now the connection is up.
This doesn't mean traffic flows trough the newly created WAN OpenVPN client interface, which goes to "XprssVN". Some gateway settings have to be changed and/or policy routing firewall rules have to be added.
I have to say : I never use the xprssVPN with pfSense.
But it connects :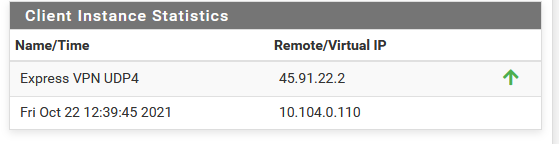
About :
route-delay 2; tun-mtu 1500; fragment 1300; mssfix 1450;These seem to work, Can't tell right now where I got them from.
Most probably from a "documentation session" (this was called "learning" back then) using my favourite web search engine. -
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
hi , I have the same error on compression using 2.5.2, how did you solve this problem?
-
@jly2680
Same problem ?
Then you should be able to find the answer here.Btw : you're late. 2.5.2 is past now, so is OpenVPN 2.5.2. It's pfSense 2.6.0 now, and OpenVPN 2.5.4.
But, be happy, the issue stays the same. Depending your setup you use, some adjustments have to be made.
As always, as everything, this needs the old way of finding solutions : look at the logs. Make the errors go away. Do what needs to be done.