PFSense 2.6.0 VPN IPsec behind NAT Firewall issues
-
I have working to setup an IPSec tunnel VPN between 2 sites using a brand spanking new installation of version 2.6.0 CE w/FreeBSD 12.3 Stable (Latest version on ISO) under VmWare 7. As far as the installation goes, I'm confident it is A-1. The goal is to create this tunnel behind a pair of Fortinet firewall (FG200e at one site, FG100e at the other one. Both running 6.4.9. Both are directly connected to the Internet with a SINGLE public IP addy).
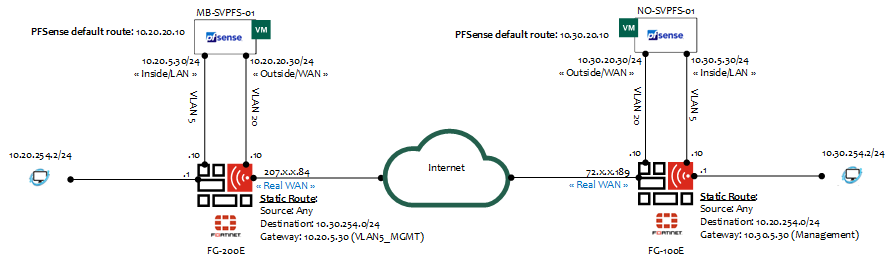
Here's a schematic of the setup:
Some other details:
I have full control of the FW's, workstations and PFSense's (Obviously, VmWare too!). The ultimate objective is to insure connectivity between the workstations sitting on both sites (10.20.254.2 <-> 10.30.254.2).
Here are the issues/challenges I'm facing:
- We already have an IPSec tunnel VPN between the sites using Fortinet's "recipe". I can "switch" from traditional UDP 500 to NAT-T UDP 4500 (Or even something else completely). This tunnel is working and carrying traffic BUT the performance is poor considering we have a 1 Gbps link at both sites. (I have been involved with their support team for more than 5 weeks to no avail: 1 direction is 500Mbps and the other 180Mbps). In lab, the pretend they were able to attain more the 700Mbps in both directions with our config. They just can't make OUR setup work properly (This is Fortinet support for me, in a nutshell)
Sorry, this is very contextual, but this should answer some questions about the relevance of setting up an IPSec tunnel behind devices that SHOULD do the job themselves.
- I have rigorously followed the "cookbook" but I have a feeling I'm missing something. In order to "link" the PFSense outside/wan to the real outside/wan (Of the FW), I'm using a Fortigate's VIP (Virtual IP), which is, in reality, a port-based static NAT (External IP Public addy mapped to PFSense's WAN interface with UDP forwarding). This is how it is defined:
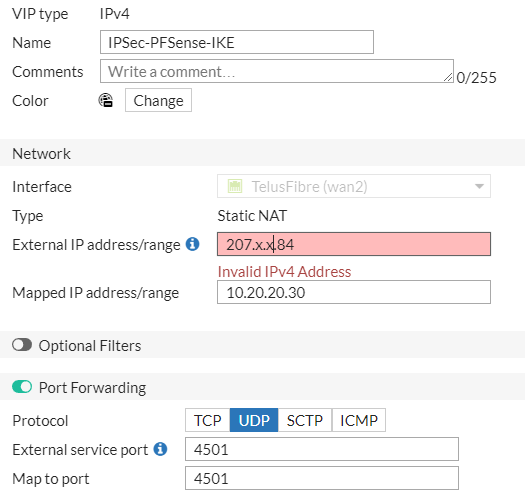
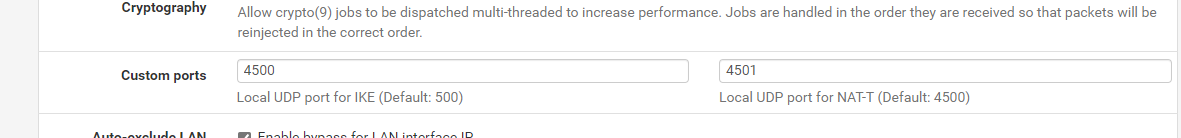
- I have configured the FG firewalls to use traditional (UDP 500). So I configured PFSense to use NAT-T (UDP 4500) to no avail. I did the opposite but no dice.
The PFSense FW's have the IPSec rule configured.
This is what I'm getting on both sites IF I'm forcing NAT-T with IKE UDP port 4500 and NAT-T UDP 4501.
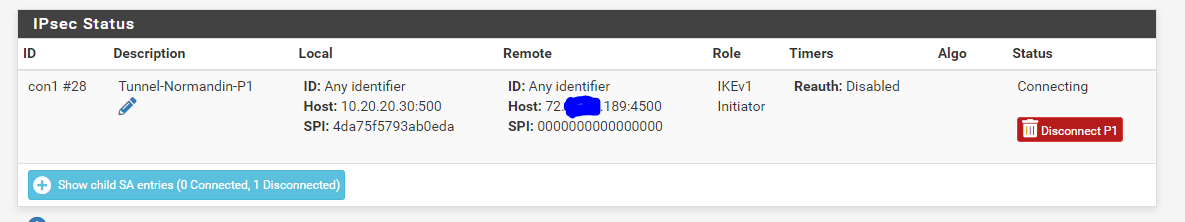
I don't get why the "local" (Outside/WAN of the PFSense) is still using UDP 500. Of course, if the traffic hits the outside interface of the firewall (Towards Internet), it will NAT UDP 500 and It will fail. What is the purpose of configuring the remote IKE/NAT-T or local ones with specific ports if PFSense is not using them? Proof:
Any answer/guidance/help/comment are welcomed.
-
@evilchuck if you have two FGs, why are you trying to put pfSense behind them to perform IPSEC?!
Makes tunnels using FGs.. -
@topogigio Simple. This design was intended to prove (Or disprove) a possible configuration issue on the Fortinet Firewalls in regards to performance. We have a 1Gbps Internet link at both sites and the maximum performance observed was around 300Mbps (Among hundreds of tests performed)... We finally got the "maintenance window" to bypass the Fortinet FWs and ended up with the same issue... Shame... This story does not have an happy ending: after a lot more tests with partners and all, we were able to establish that the ISP "feeding" ours does in fact throttles the IPSec protocol. So, I'm able to transfer stuff in the "clear" (FTP or else) at over 940Mbps between our sites but only at 300Mbps if we use IPSec. The sad part: there's NOTHING we can do about it and it seems our ISP is also stuck with this non-sense. The culprit: Bell Canada... So, in future endeavours with them, make sure you ask and most importantly, have it written in a contract that they will not "throttle" ANY traffic on your link(s) with them.
-
@evilchuck Interesting!
But was this admitted by Bell at the end?I always provide connections only with "net neutrality" contracts, so I hope I will not have this kind of problem.
Clearly was the tests performed with only "any to any" FG rules without any kind of inspection I think, right? I ask this because 300 Mbs basically is the throughput of the 100E firewall engine..
-
@topogigio In terms of Bell admitting to anything, good luck with that! It's not like Bell is connected to us directly, our ISP is. They (Bell) will not admit to them... Imagine us. Our location REALLY limits the choice of providers; we're lucky enough that they can provide service @ 1Gbps. The tunnel @ 300Mbps is fine with day-to-day operations, but backups between sites are handled differently (Which was the big headache) as we encrypt the stuff with Veeam and carry it with our QNAPs HBS3 sync functions (With SSL encryption on) out of the IPSec tunnel (Thus at high speed).
In terms of the expectations for the 100E, it is way over 300Mbps for IPSec; granted it's not 4Gbps or something with very small packets (In reference to the specs), but it's over 300. We were able to go as high as 740Mbps with a non-throttling ISP...