Remote Access / TLS + User Auth - Connection up but no LAN
-
Hi
I read about the pre-shared key mode which will be disabled. Since i'm building everything new I also changed this weekend the VPN mode. So now I want to use Rmote Access / SSL/TLS + User Auth mode. This works fine the connection is established.
Side 1: Server (pfsense)
Side 2: Client (pfsense)
What is working:
I can open via the tunnel 10.0.5.1 the clients Pfsense and do a login.
I can ping from the tunnel network to the server pfsense and probably also open the webinterface.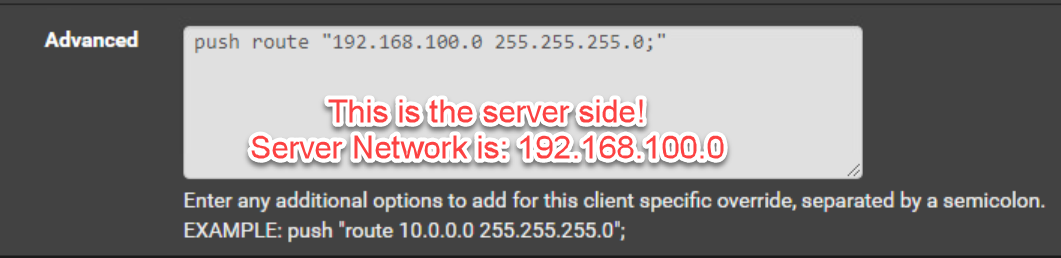
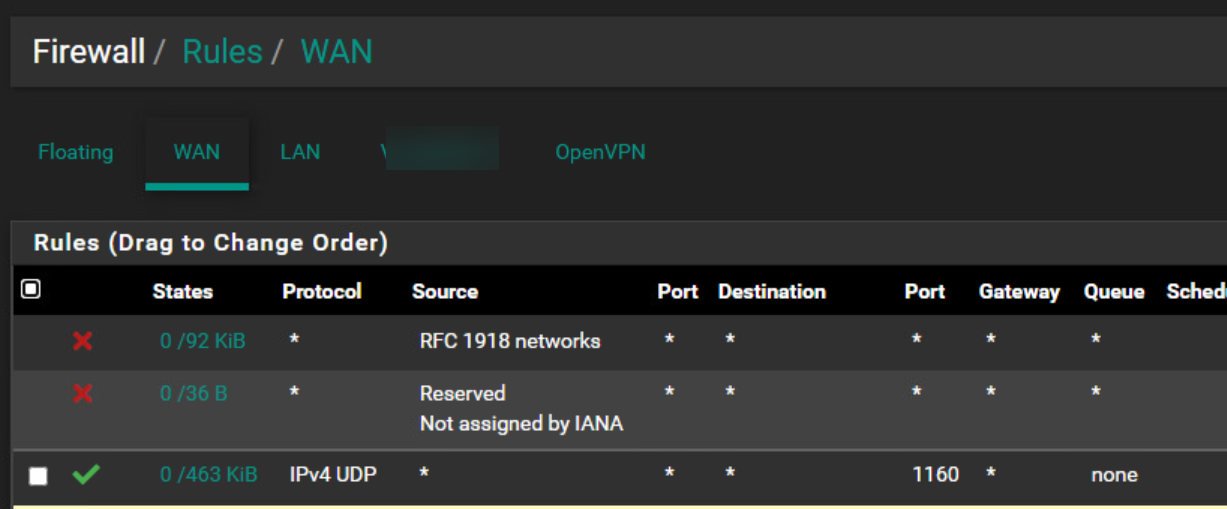
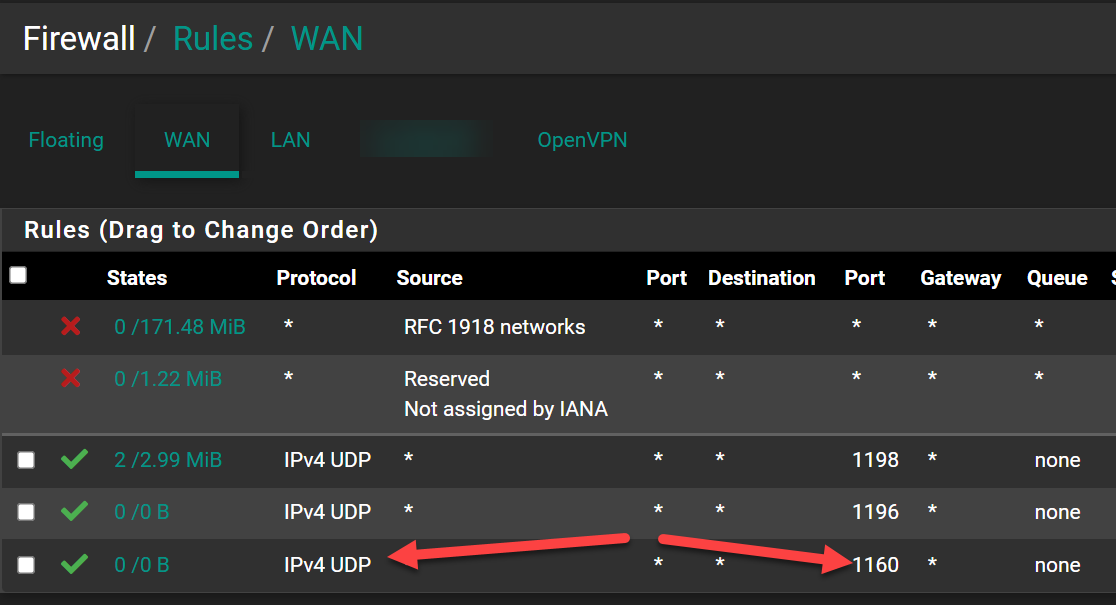
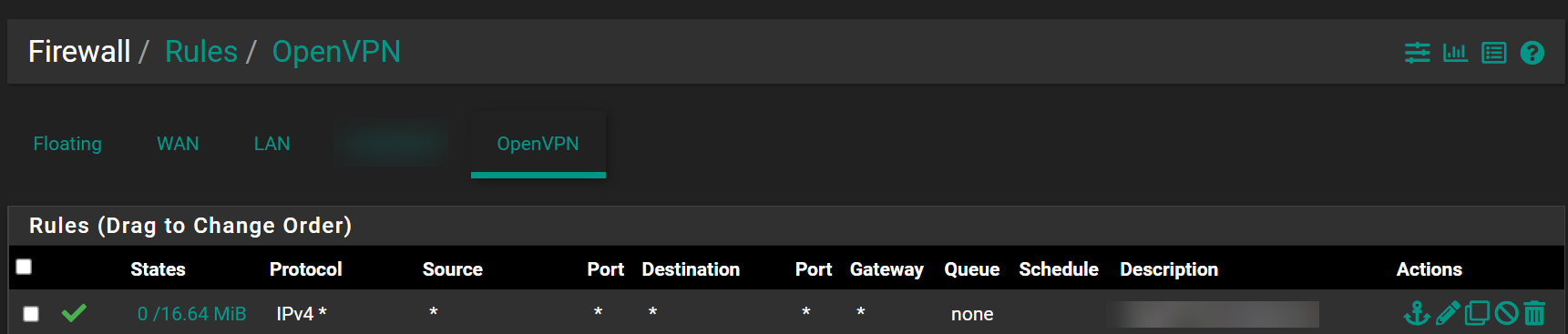
I set up also the rules and I think they look good:
Server side:
Client side:
I think it has something to do with:
https://docs.netgate.com/pfsense/en/latest/troubleshooting/openvpn-iroute.html#troubleshooting-openvpn-iroute
At the moment I don't know what I can try to fix I have tried a lot.Goal:
Acces from the server side the client's lan and also the client can connect to the server lan. -
If you're using a /24 , and not a /30 for the site-to-site (S2S) connect net.
I think you have to do a Client specific override (CSO)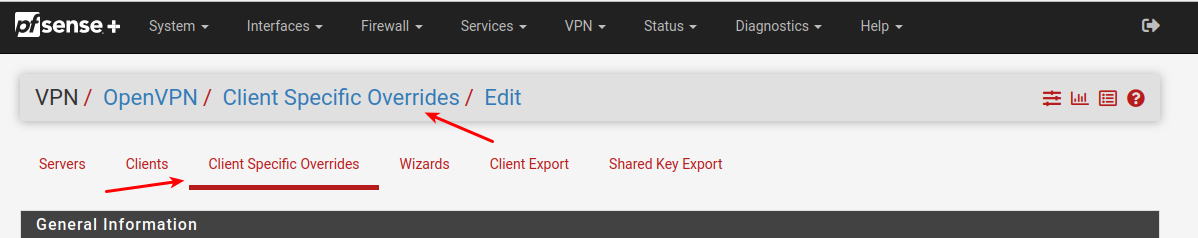
You have to match the Certificate name (CA name) , and you can then specify remote & local networks , on the CSO page.
I'm using /30 connect nets on my S2S connections , so i can specify them directly under the server or client.
Hence not much experience w. CSO & routes.
/Bingo
-
@hispeed said in Remote Access / TLS + User Auth - Connection up but no LAN:
I read about the pre-shared key mode which will be disabled. Since i'm building everything new I also changed this weekend the VPN mode. So now I want to use Rmote Access / SSL/TLS + User Auth mode.
Why? There is also Peer to Peer (SSL/TLS) Mode. Btw. I would like to know what the best settings are for max performance and good security. Here is mentioned that DCO is coming for AES-256-GCM first but "/30 tunnel" isn't preferable any more? So how should a Server2Server exactly look like, with routing on both sides, I wonder.
-
For clarity i'm including the /30 section from the URL you linked to.
Using a /30 tunnel network for peer-to-peer tunnels (one server with one client) can be potentially problematic with DCO. There are problems with the code for this mode in OpenVPN which can lead to instability. Also the client must be using at least OpenVPN 2.5.0 which is present on pfSense Plus software version 21.02 and later or pfSense CE software version 2.5.0 and later. These restrictions do not apply to client/server mode (one server capable of handling multiple clients).
Luckily my boxes aren't CPU constrained , so i would prob. not enable DCO on S2S connections.
I wonder if this is going to be fixed in later OpenVPN revisions , or if P2P (/30) connections are going to be phased out ...
It doesn't make sense to me to phase them out ...
Edit1:
Yuuckkk !!!From here:
https://community.openvpn.net/openvpn/wiki/DataChannelOffload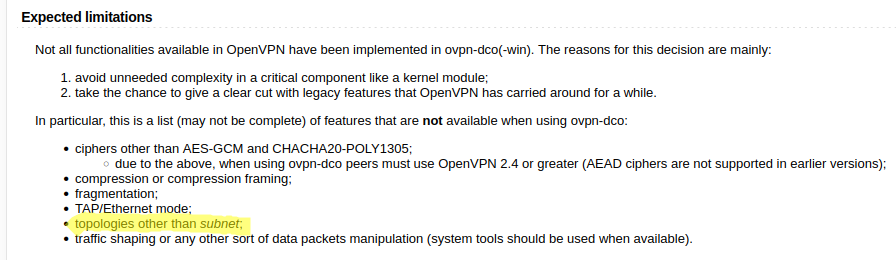
Seems like it's a DCO design/implementation decision

Edit2:
Well the two main disadvantages with the old Non-DCO wayThere are two main disadvantages with this approach:
data packets enter and leave the kernel twice;
all client traffic is handled by the single-threaded OpenVPN process.At least #2 doesn't hit a /30 P2P that hard , or at all.
Since my /30 servers are separate processes , i suspect they will spread out over available cores , and "be multi cored".Looking at it that way, it makes sense to concentrate the effort on "subnet" where multiple connections is/were bound to a single thread.
So i'll just do Non-DCO on my P2P connections , and DCO on my multi client "Road warrior" servers that are /24 anyway.
But no DCO for me, until the "versions" has been officially released by OpenVPN.
Remember if enabling DCO:
due to the above, when using ovpn-dco peers must use OpenVPN 2.4 or greater (AEAD ciphers are not supported in earlier versions);Netgate even mentions something about 2.5.0 clients, don't know if that was just for the /30 "Topology"
So no ancient clients ....
/Bingo
-
@bingo600 I switched my connection to a cheap VPS to wireguard because it is heavily cpu constrained.
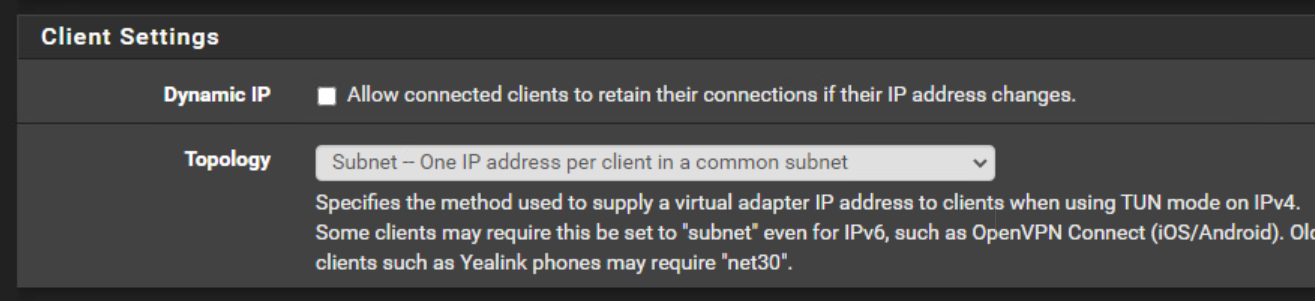
I also wonder with OpenVPN, you can set the "IPv4 Tunnel Network" to a /30, but also there is the option "Client Settings - Topology" where you can set subnet. Does this make sense? I don't know but would like to see a performant OpenVPN anyway. -
@bob-dig said in Remote Access / TLS + User Auth - Connection up but no LAN:
@bingo600
I also wonder with OpenVPN, you can set the "IPv4 Tunnel Network" to a /30, but also there is the option "Client Settings - Topology" where you can set subnet. Does this make sense? I don't know but would like to see a performant OpenVPN anyway.I think the first "IPv4 Tunnel Network" , sets the IP-Connect net , used for server & client(s).
The 2'nd : "Client Settings - Topology" /30
Specifies the "Topology" ... Aka. The way the first net is used.
And a /30 is "hardcoded" to give first ip to the server , and the 2'nd to the client.So in a "bit" cryptic way, they both make sense.
Ps: Read my Edit's in the previous post.
/Bingo
-
@bingo600 and the others
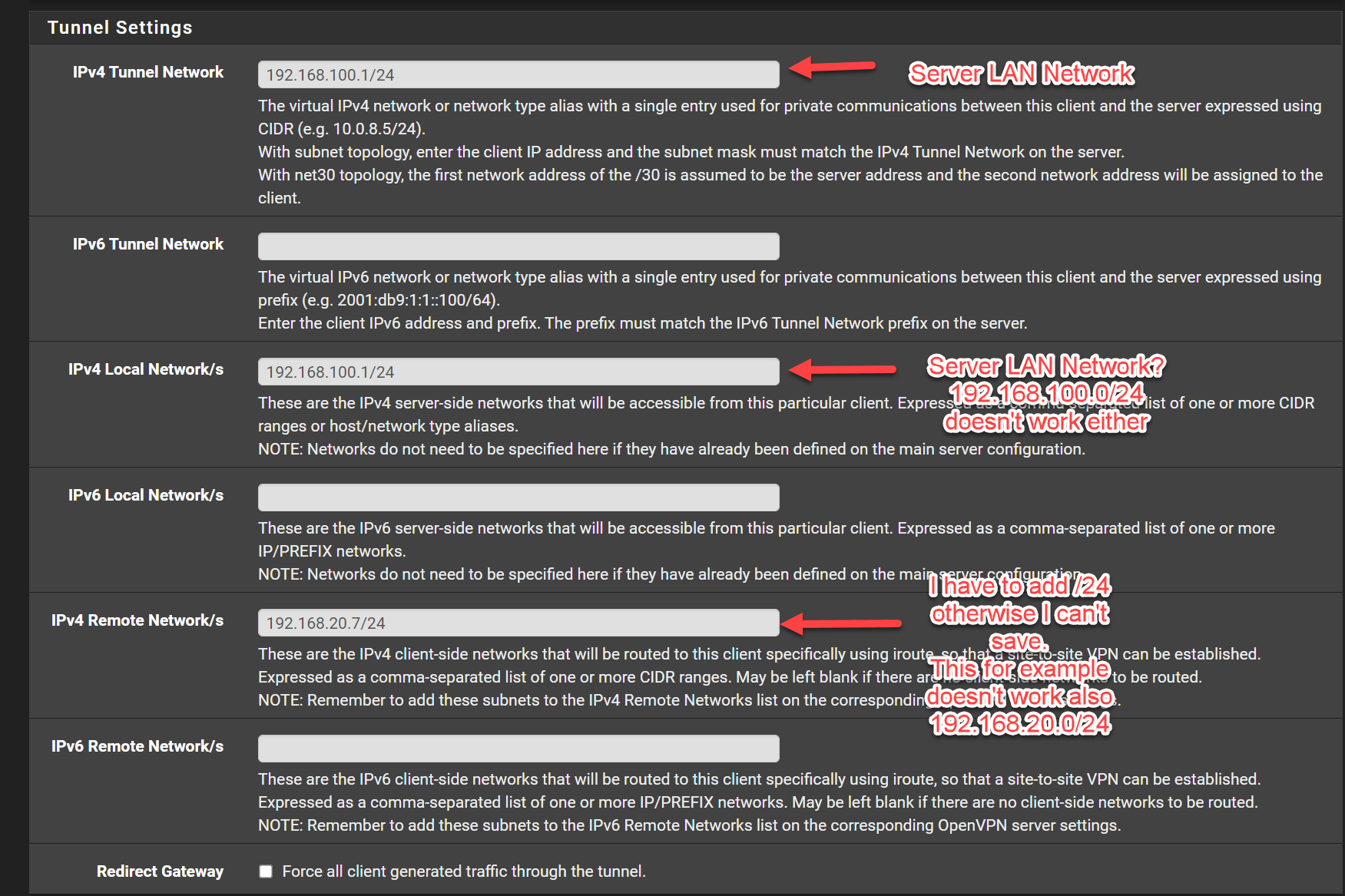
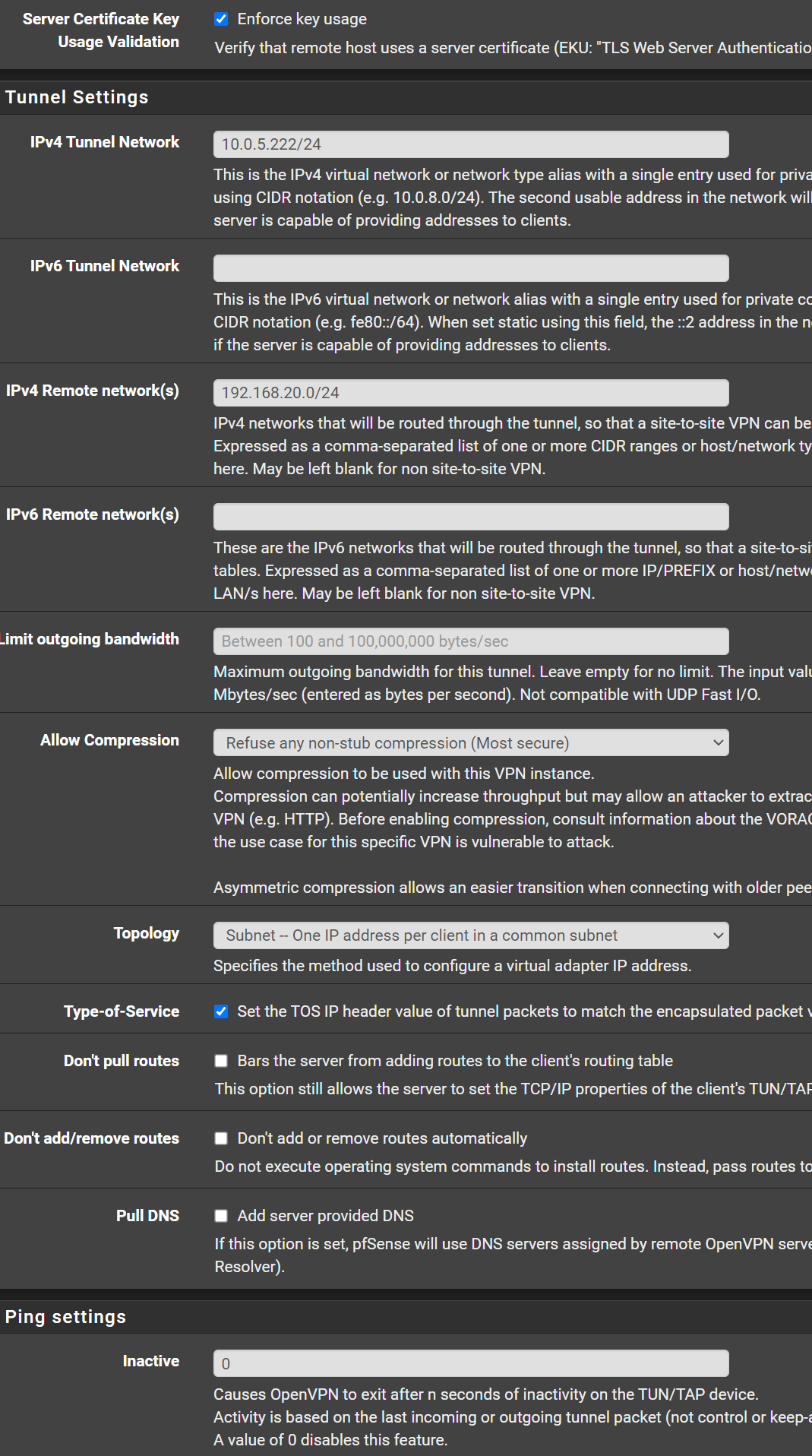
I have on the server side:
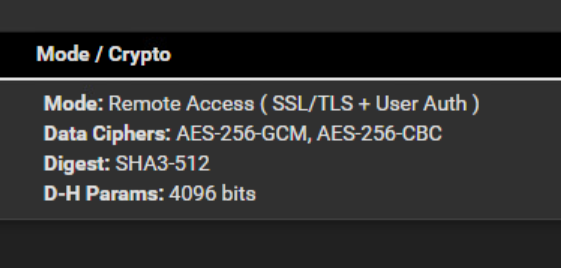
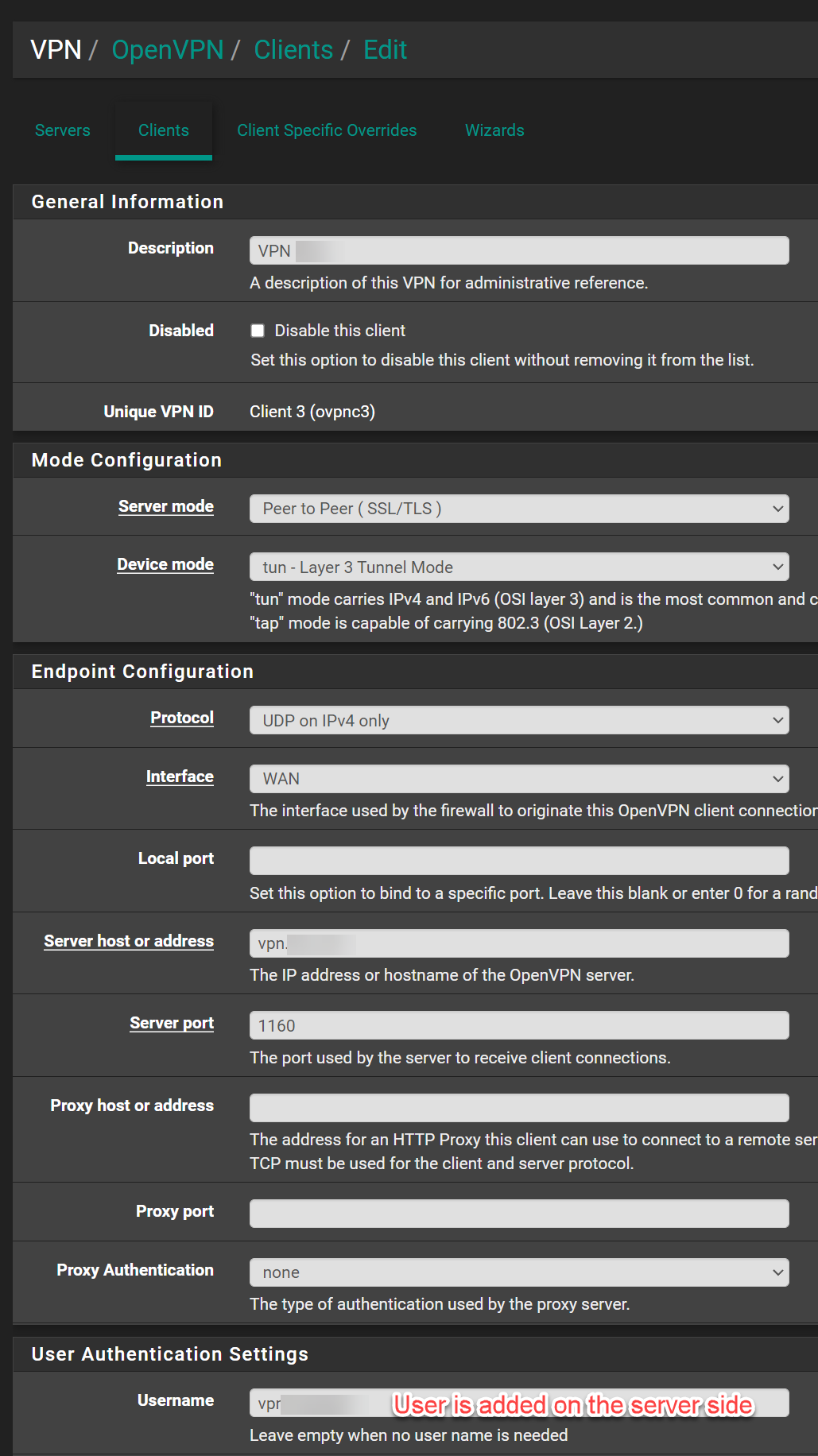
Client side:
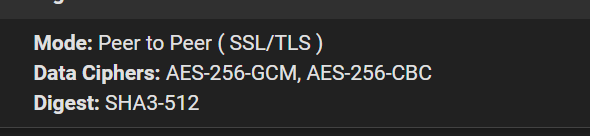
Because of the mode i'm not sure if this can work?
Client Ovverrides Server
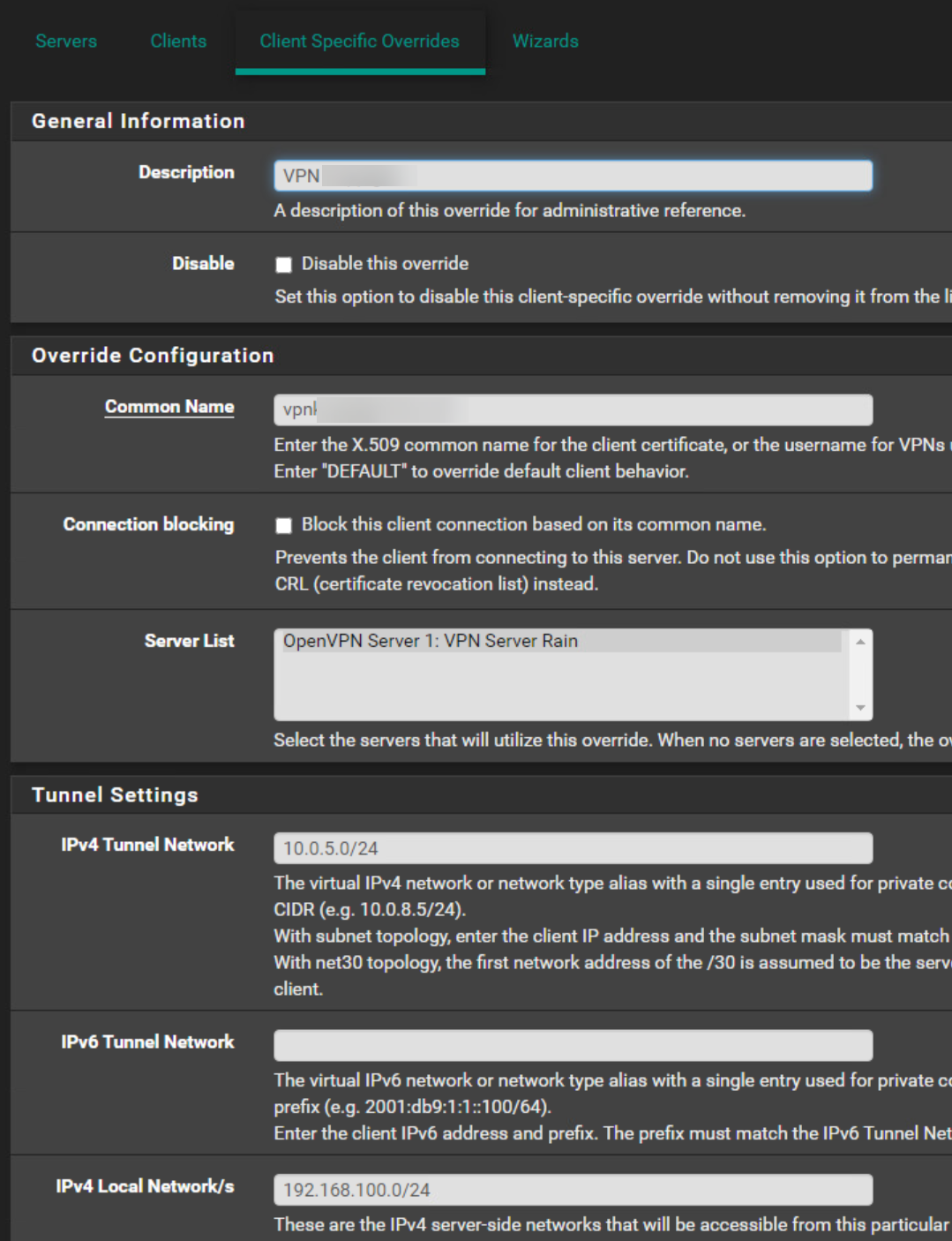
I have added it also on the client side.
-
@hispeed
That seems a bit strange. To use SSL+TLS+Userauth on Server side , and not the same on client side (only SSL + TLS)Is this the client a Person logging in or a PC (like another pfSense) ?
Userauth would not be feasible if it's not a person logging in.If it's a S2S connection made by 2 PC's , i'd just use SSL/TLS.
/Bingo
-
@hispeed
Also in the CSO you must not use a /24 tunnel.
How to set the tunnel, depends on the server topology. If it uses a /30 set also a /30 subnet in the CSO. If the server uses subnet topology set a single IP out of the tunnel.Also the "push route" in the advanced settings is superfluous. This is already done by the "Local Networks" field.
-
The client is also a Pfsense so both are Pfsense (+ version).
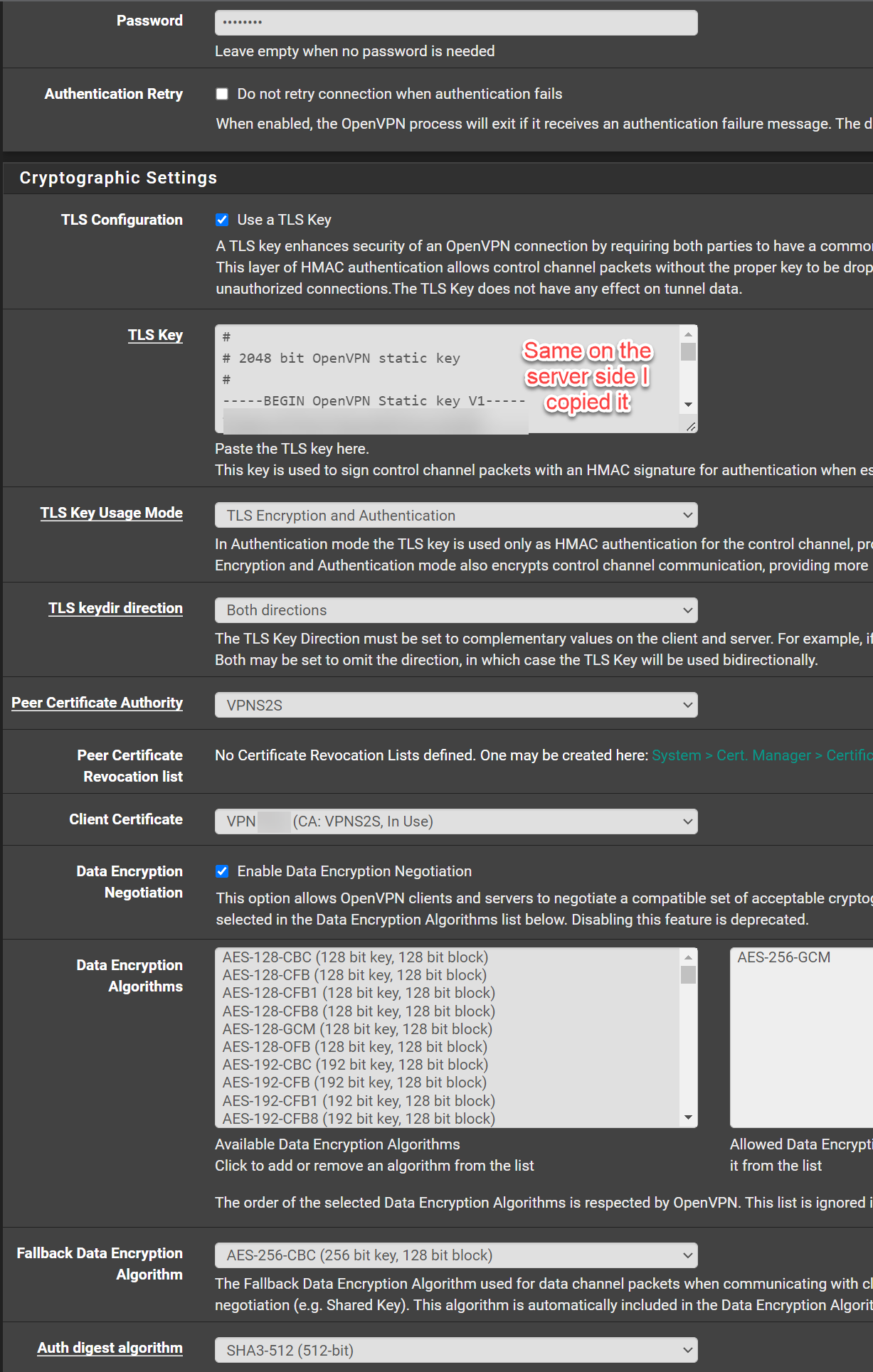
Ok I haven't changed that yet concerning the mode because I would like to have 2 security steps (TLS Key + Username Password).@viragomann
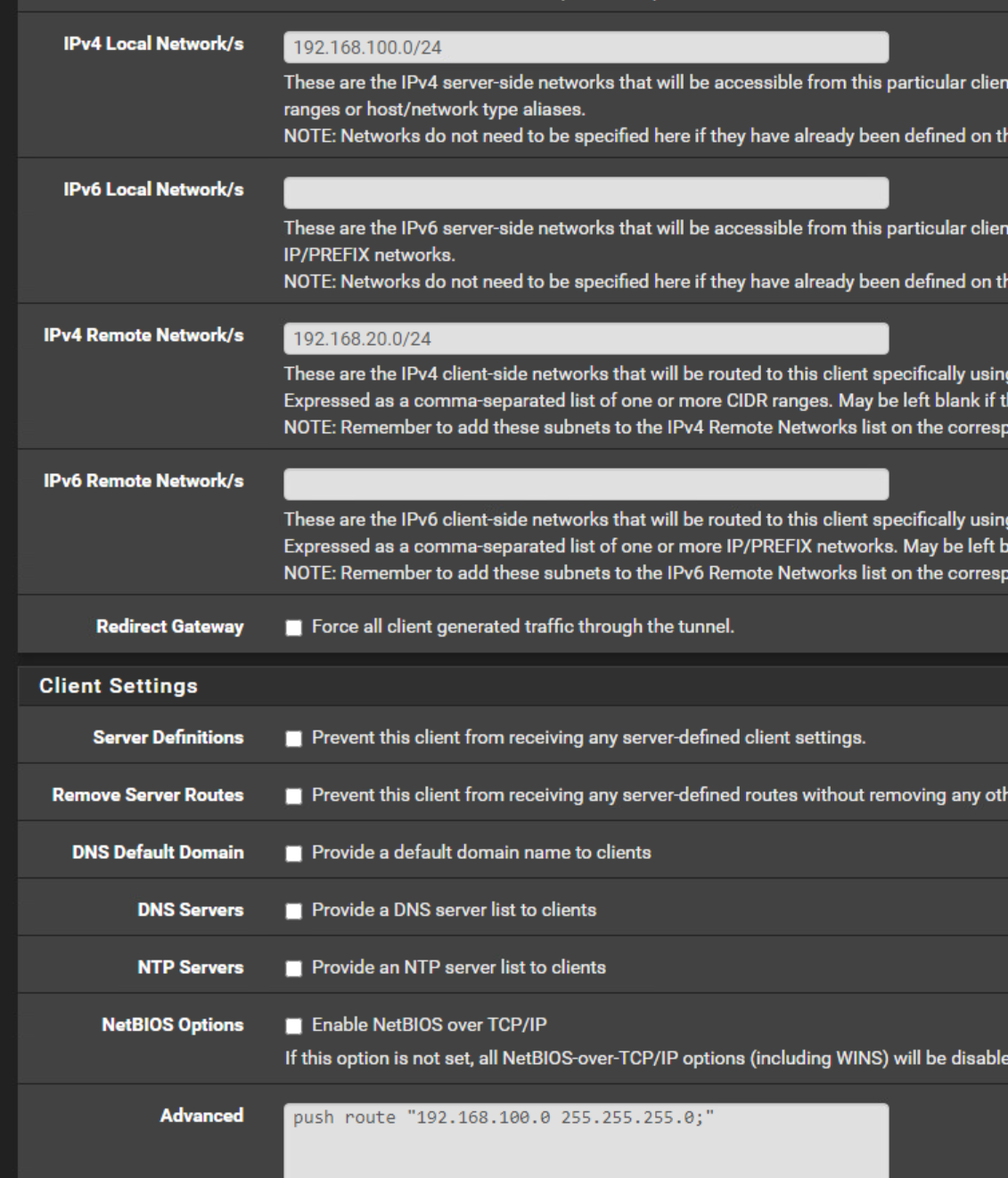
Ok I removed the push route.Server:
So I use at the moment subnet.
Client:
Maybe I have something else wrong in my configuration?
-
@hispeed said in Remote Access / TLS + User Auth - Connection up but no LAN:
Client:
This looks rather like the client specific override page. However, it's the right place to do your settings.
But you have something to correct:In IPv4 Tunnel Network you have to state the clients virtual IP. This must be part of the servers tunnel network, when using subnet topology, as mentioned.
So since your server is 10.0.5.0/24, enter here "10.0.5.222/24".IPv4 Local / Remote Networks must be network addresses! Yours are IPs, but not networks.
So into the IPv4 Local Network/s box enter "192.168.100.0/24",
and into IPv4 Remote Network/s (clients side LAN) enter "192.168.20.0/24", if that's the proper network, you didn't mention. -
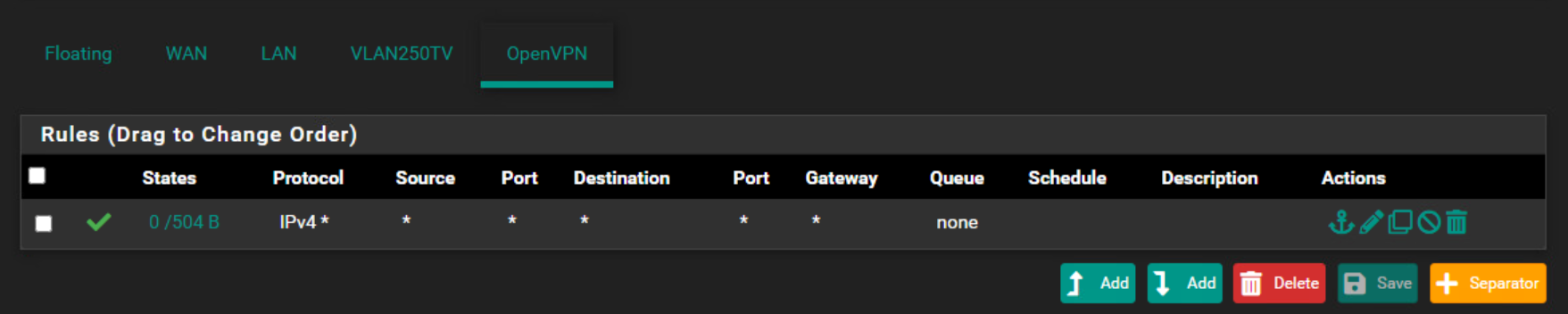
@hispeed What rules do you have on the OpenVPN interface?
-
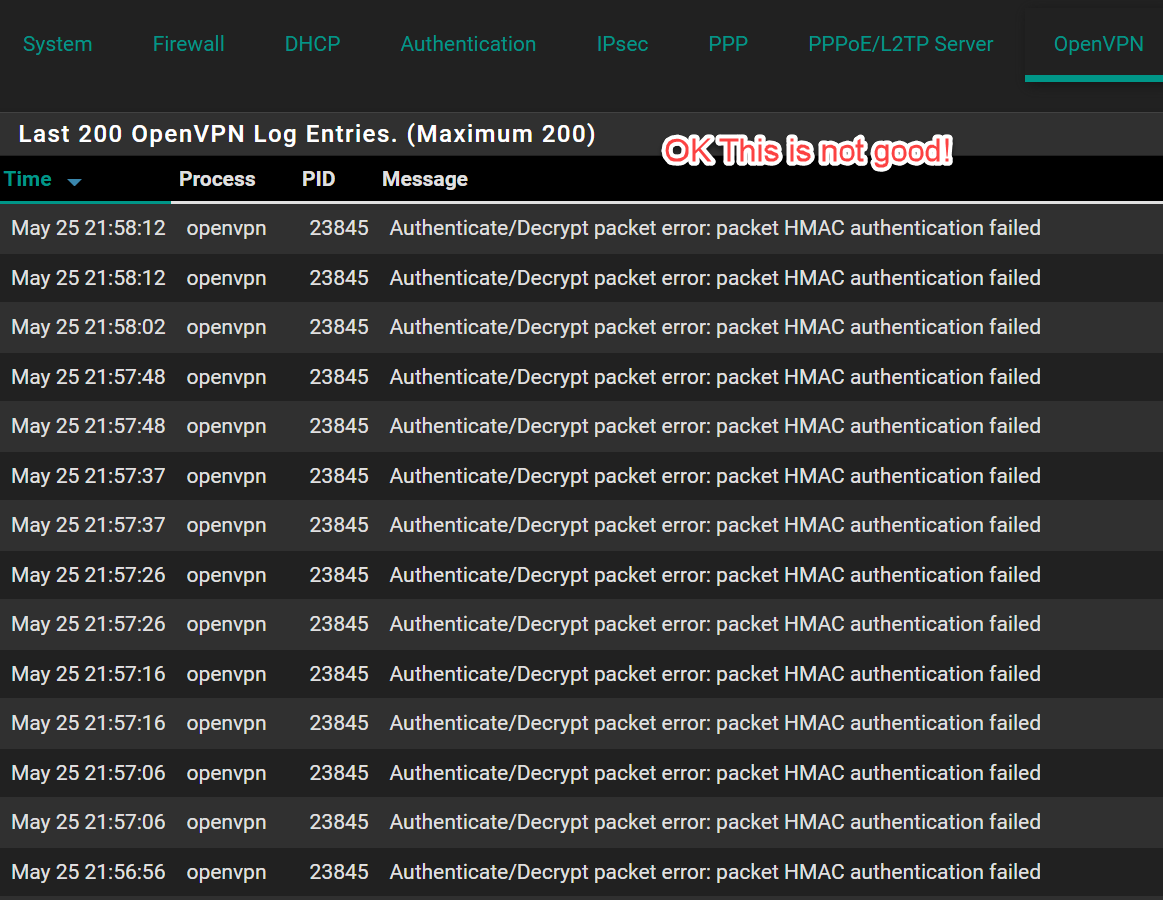
I set up your settings, tunnel is up but still i can't reacht the remote network.
On both side I have this rule as the first rule.
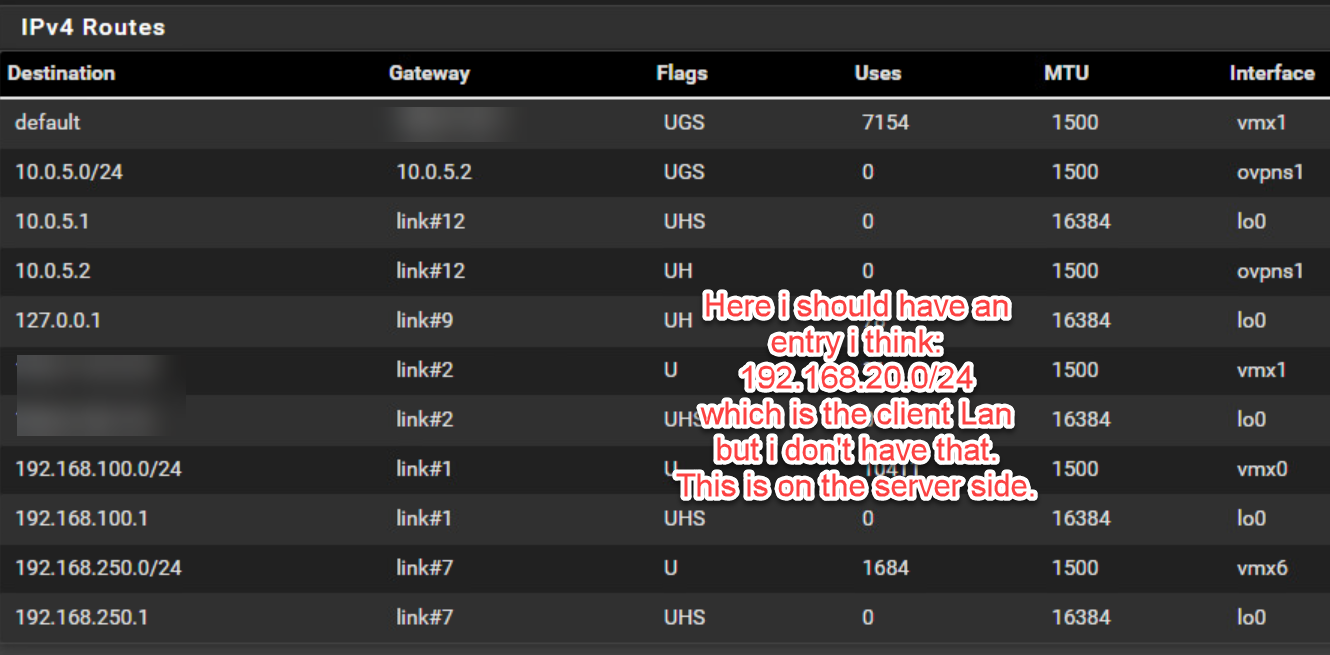
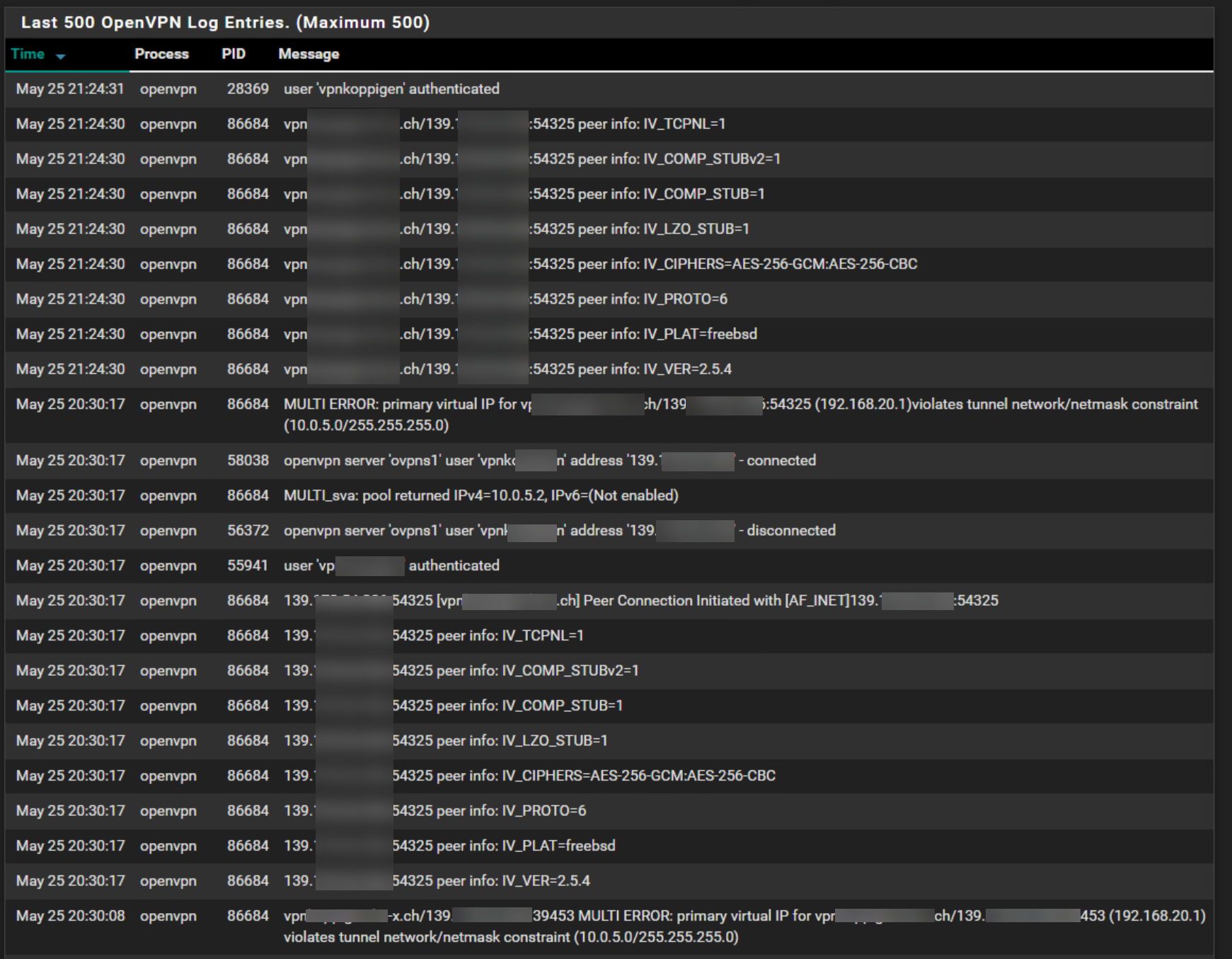
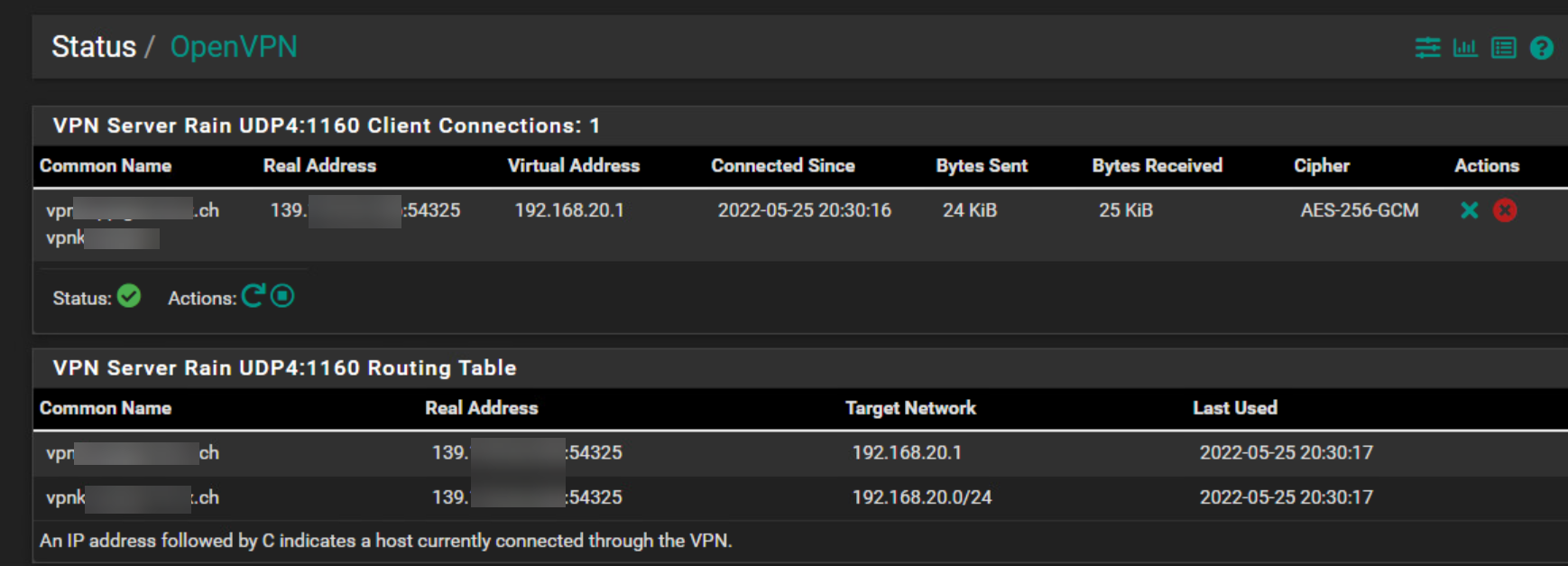
I'm pretty sure this is because I don't see the IPv4 Routes entries in Diagnostic Routes belonging to the remote network from the client when I look on the server side.
-
@hispeed Can you post the full vpn config from both sides?
You have snippets of each and they're getting jumbled.Also, what does the openvpn logs show?
Do you have the user/pass in the clients config?
Do you have all the right cert's?Why are you opening ports on the client side?
-
Hi @Jarhead
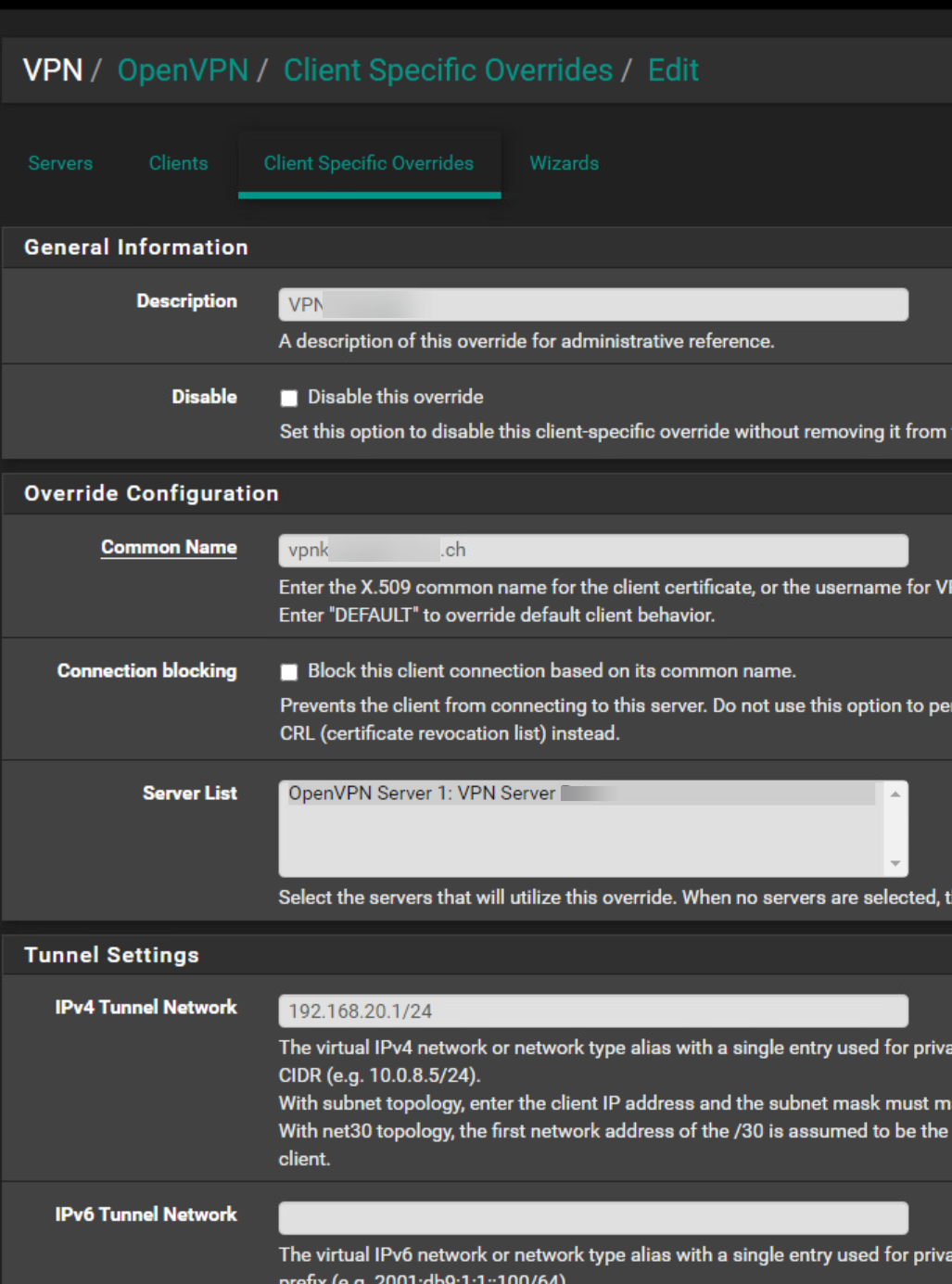
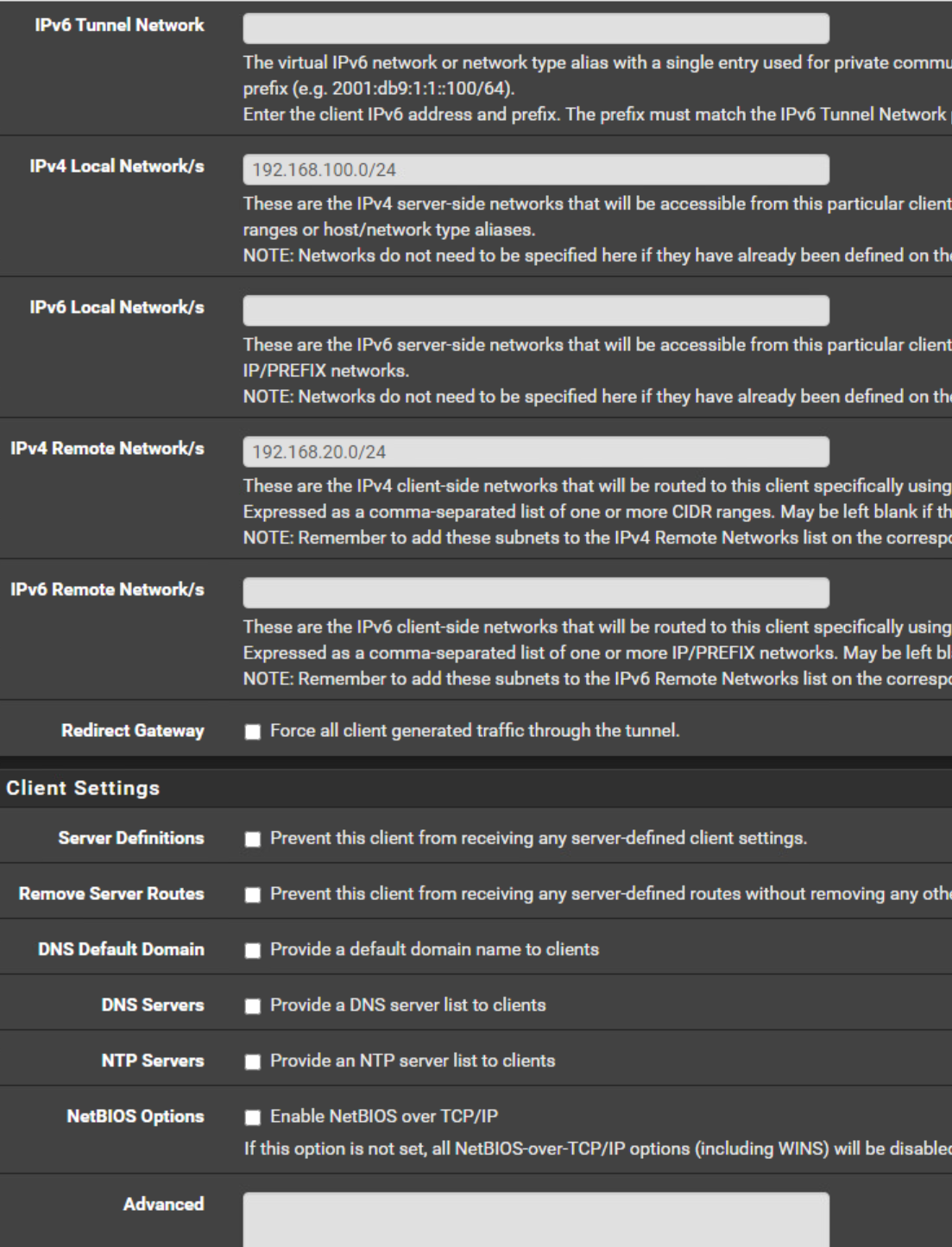
Here are the images you requested:
Server side:
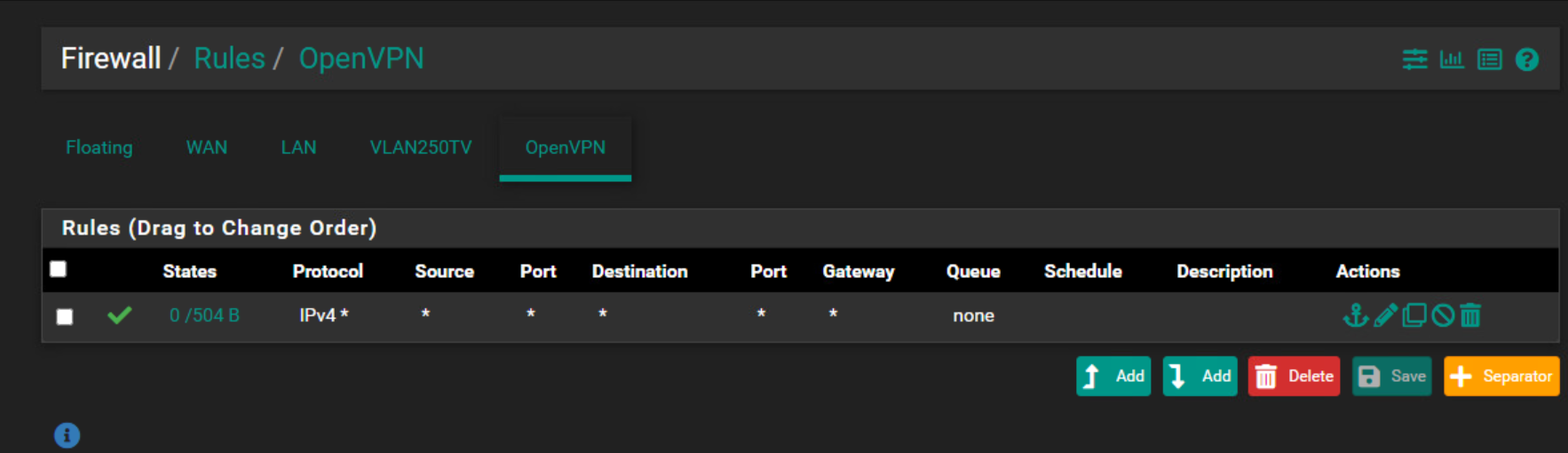
Firewall Rules OpenVPN
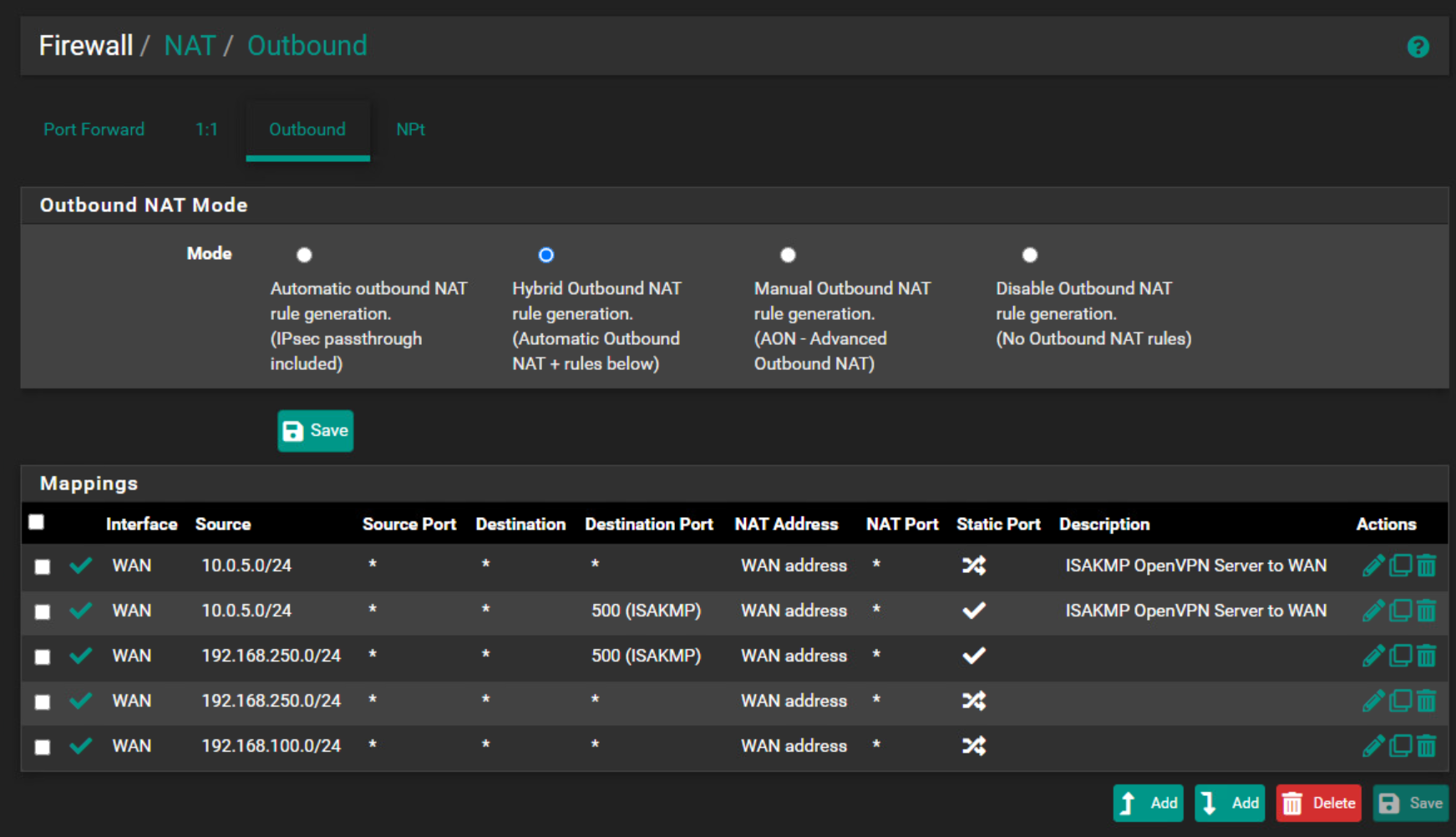
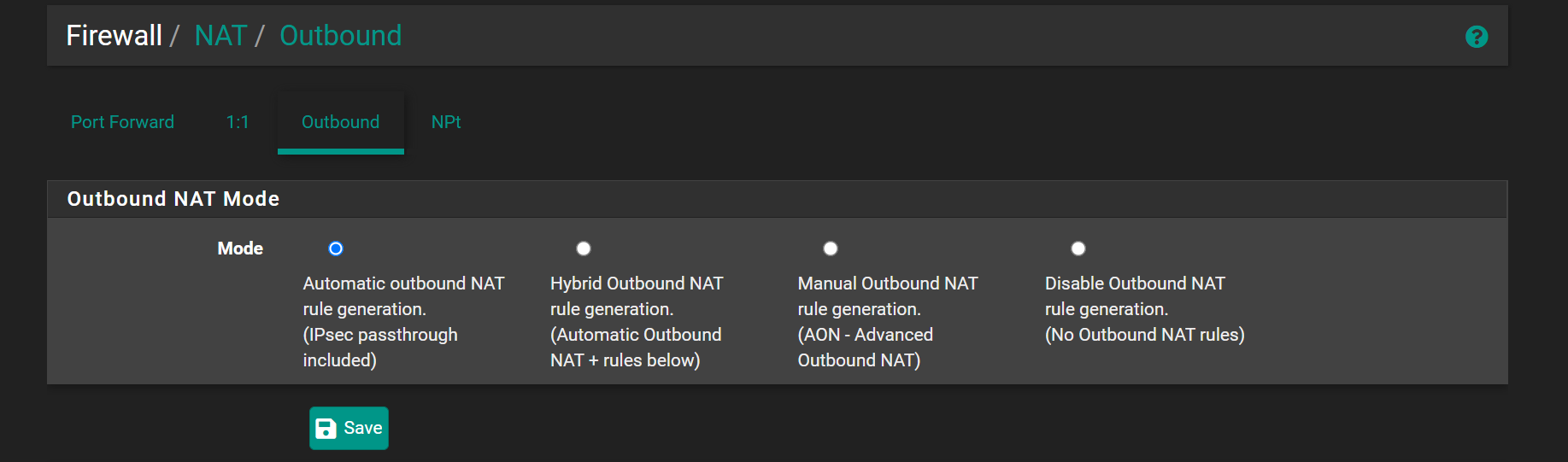
NAT Outbound
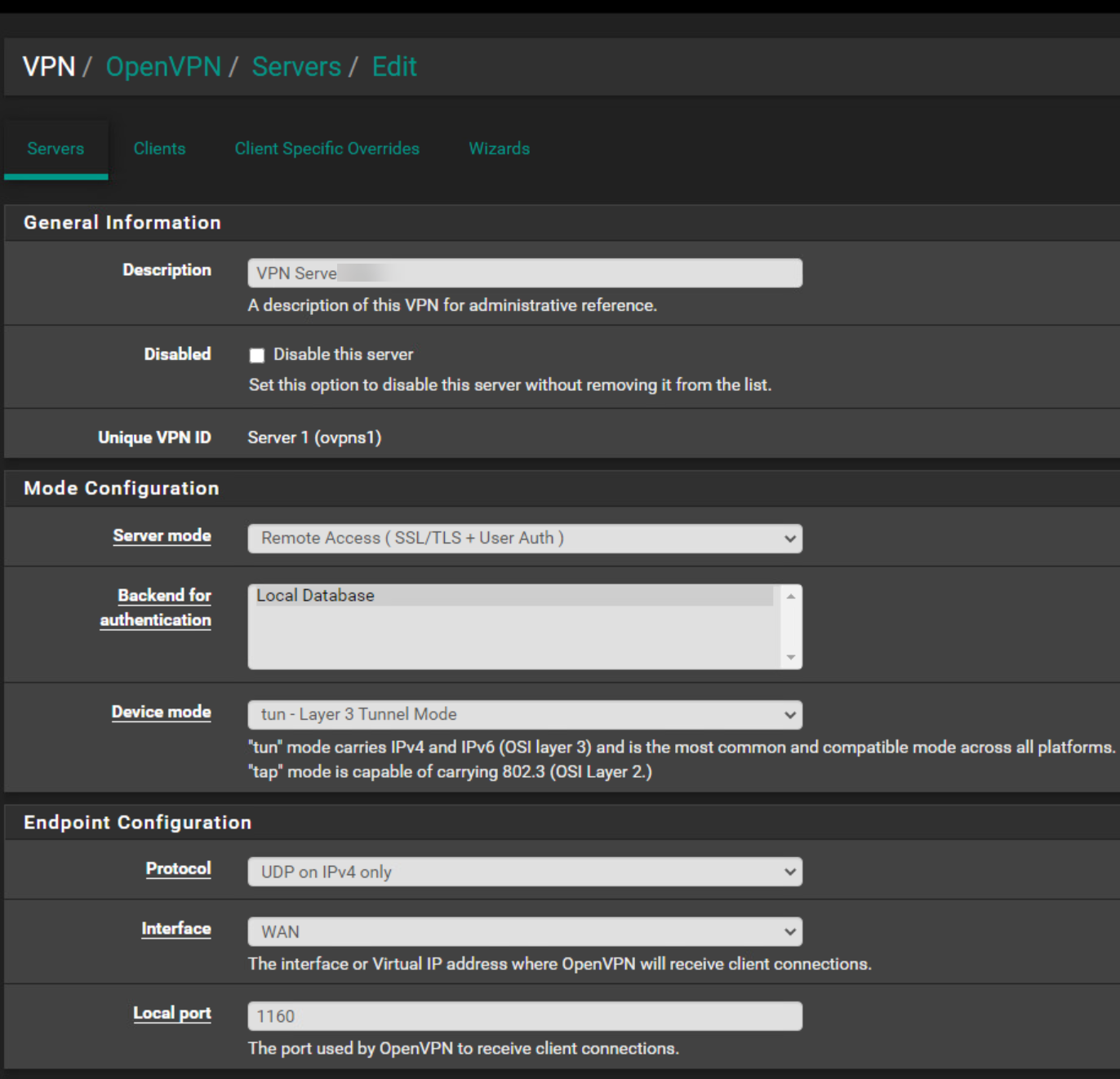
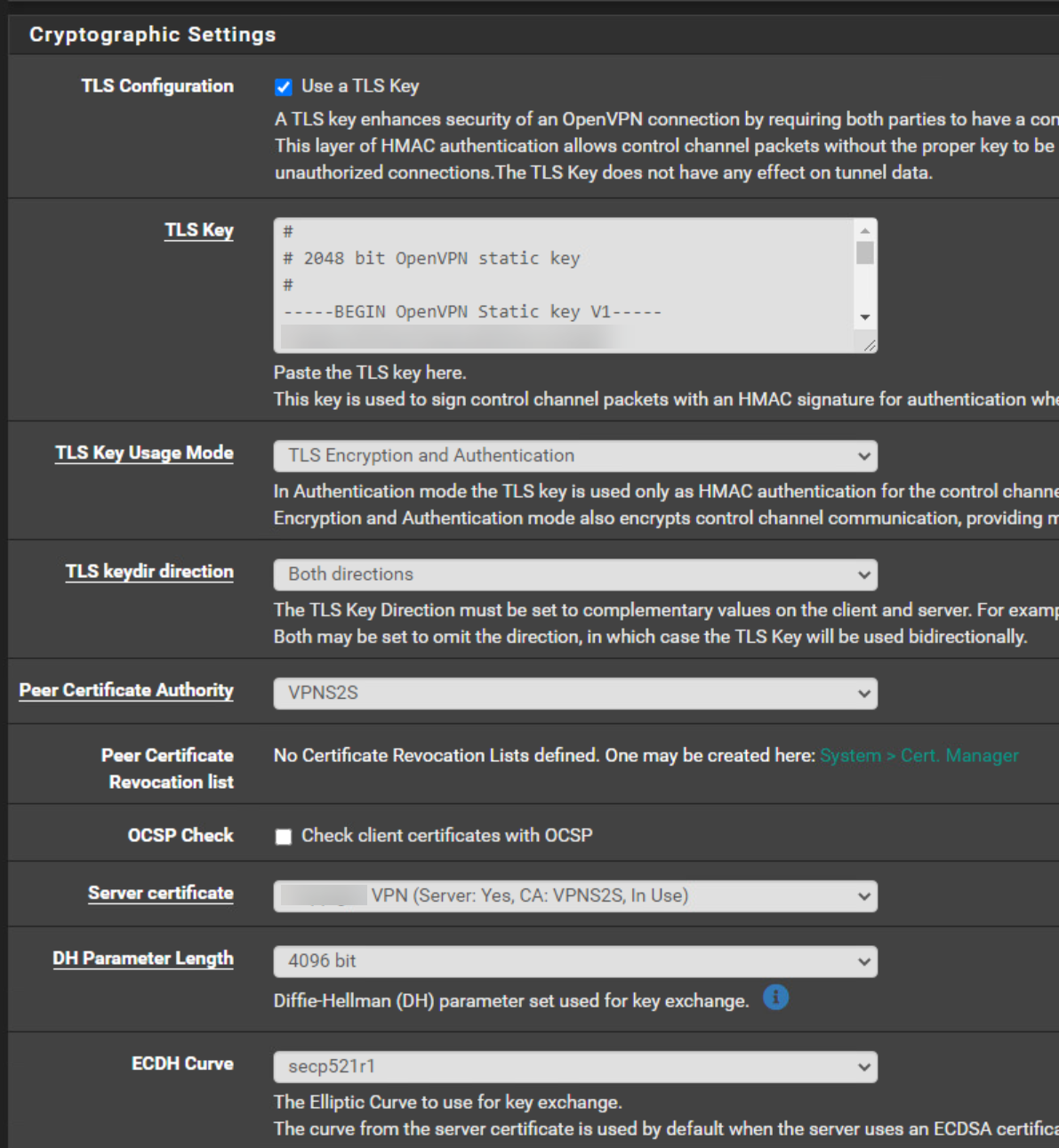
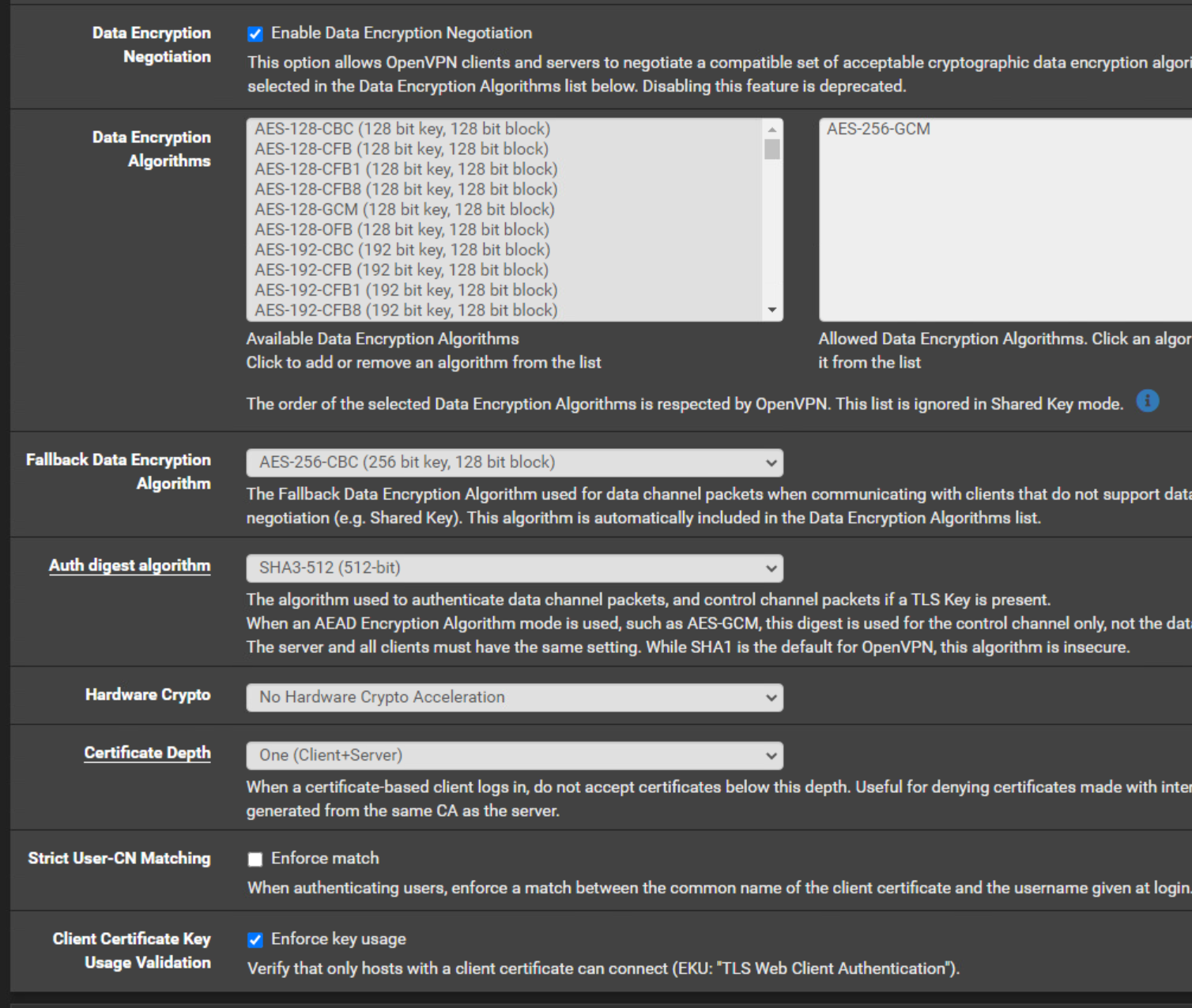
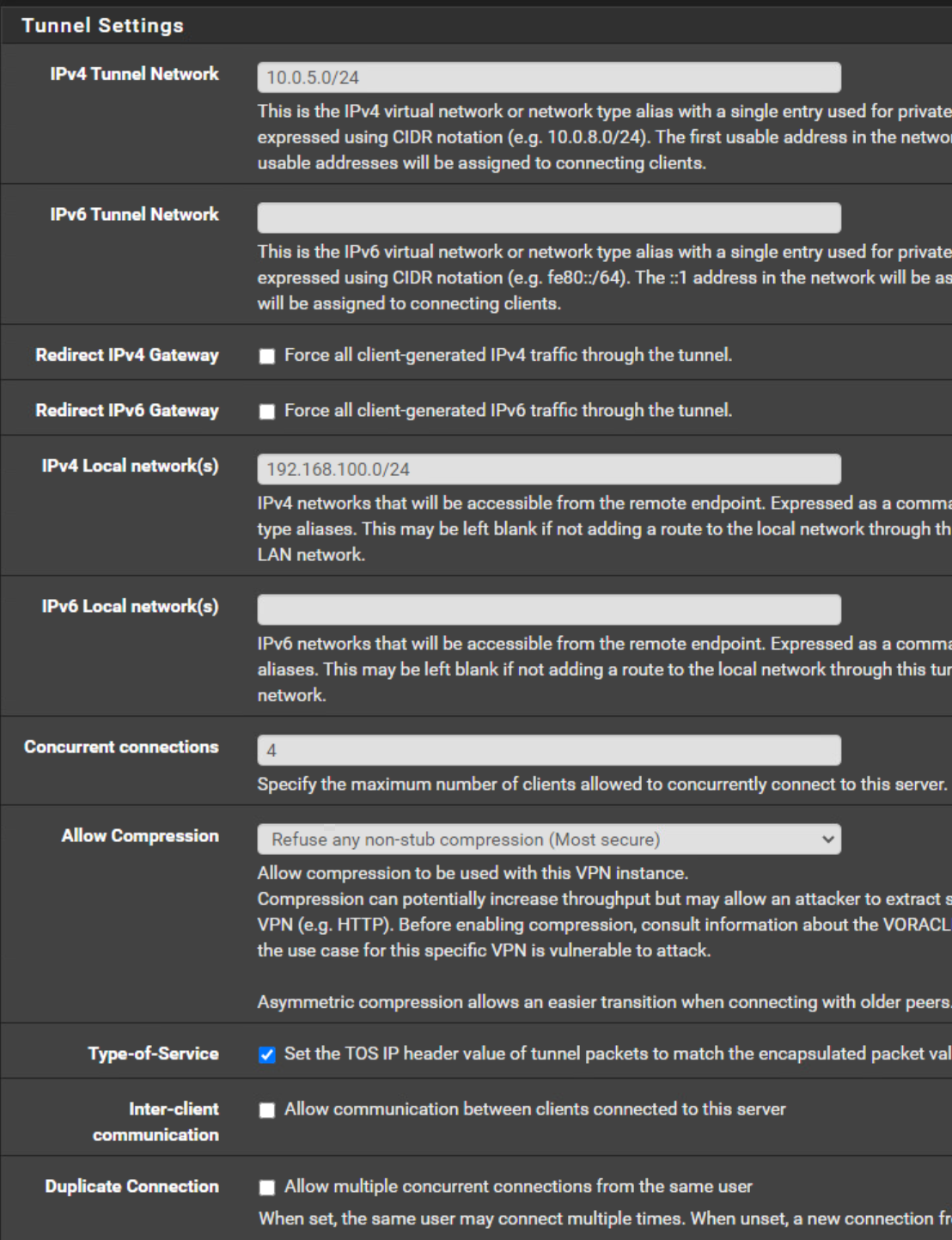
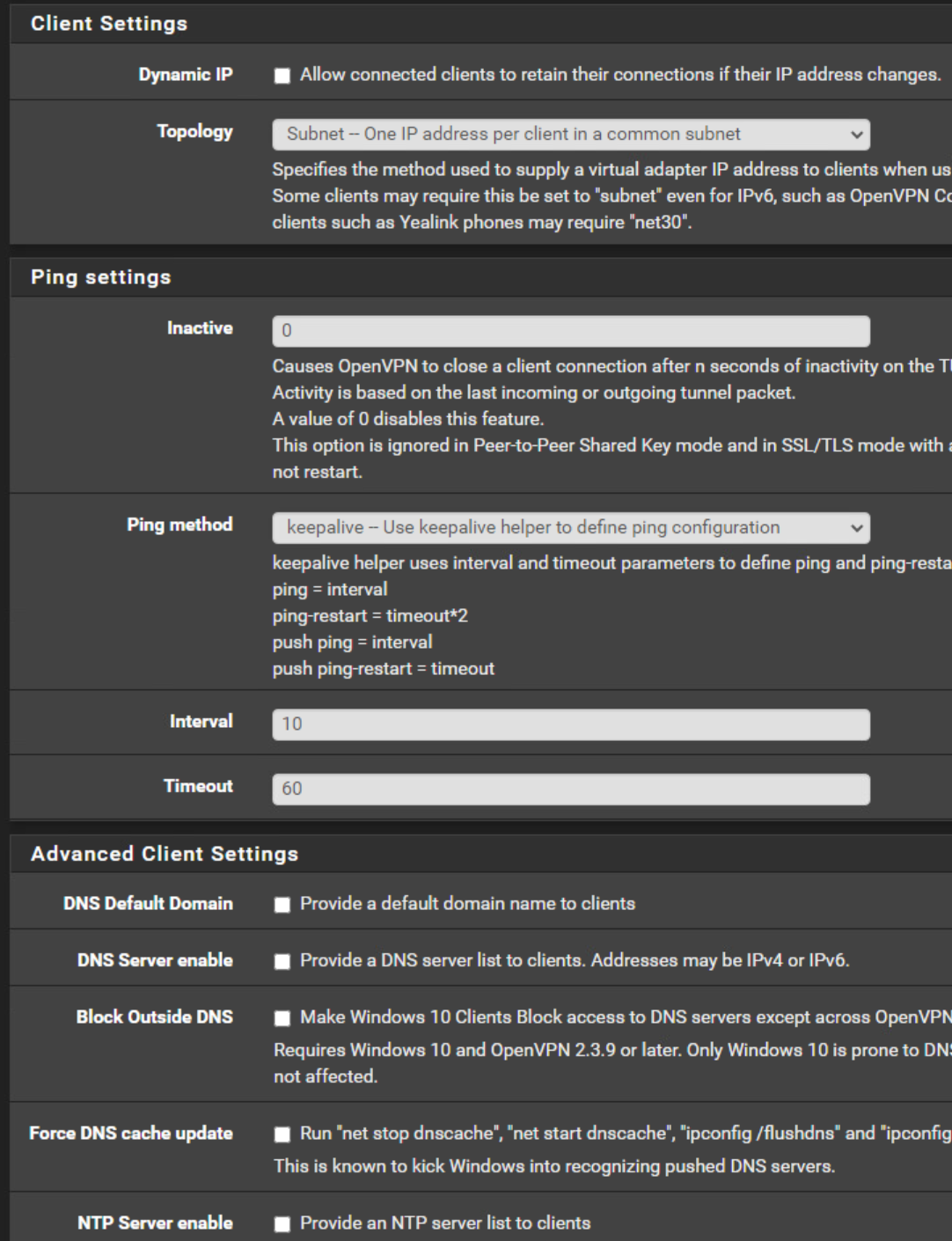
OpenVPN Server Configuration
OpenVPN Server Client Specific Overrides
Server-Side Log:
OpenVPN Log
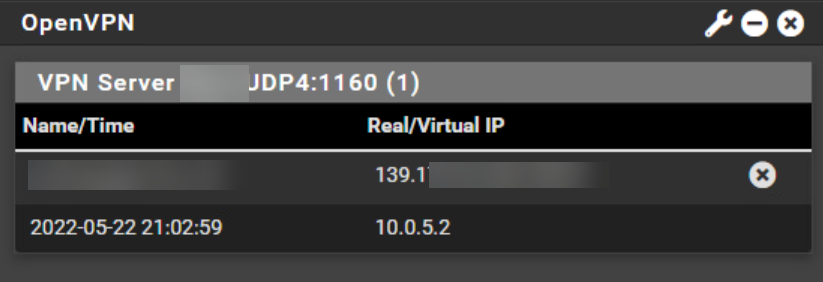
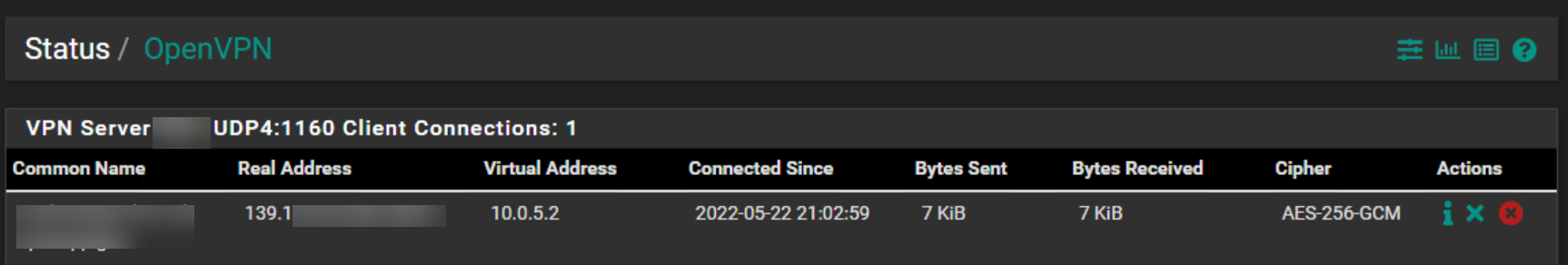
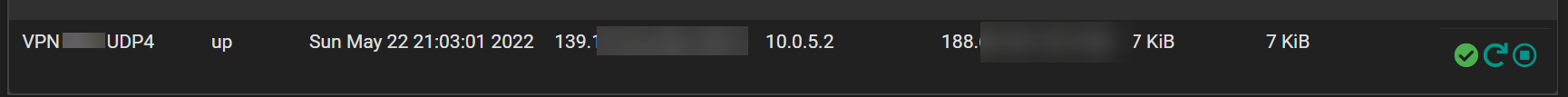
OpenVPN Status:
Answers for your questions:
Do you have the user/pass in the clients config?
Yes I will post in a second post the client config.Do you have all the right cert's?
As far as I know i'm pretty sure I have checked it and if they wouldn't be correct the connection is not working.Why are you opening ports on the client side?
Which ports do you mean? I don't know I didn't open any ports as far as i know. -
@hispeed
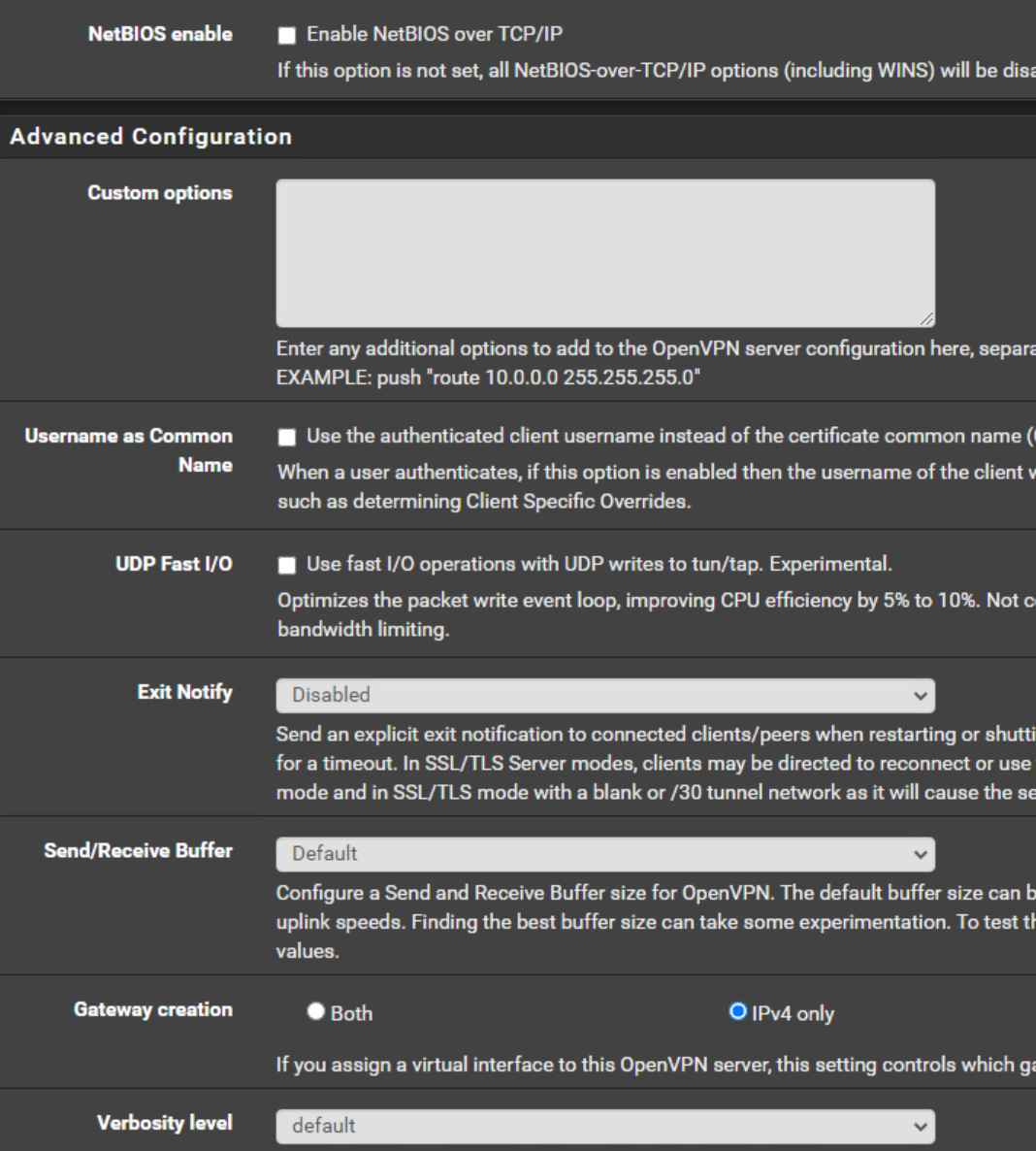
So this is not, what I told you to set up. -
I hope this works since I'm doing a double post.
This is the follow up and client side configuration. The client side is also a Pfsense, so the connection will be from Pfsense to Pfsense.Client Side
Firewall Rules OpenVpn
NAT Outbound:
OpenVPN Configuration:
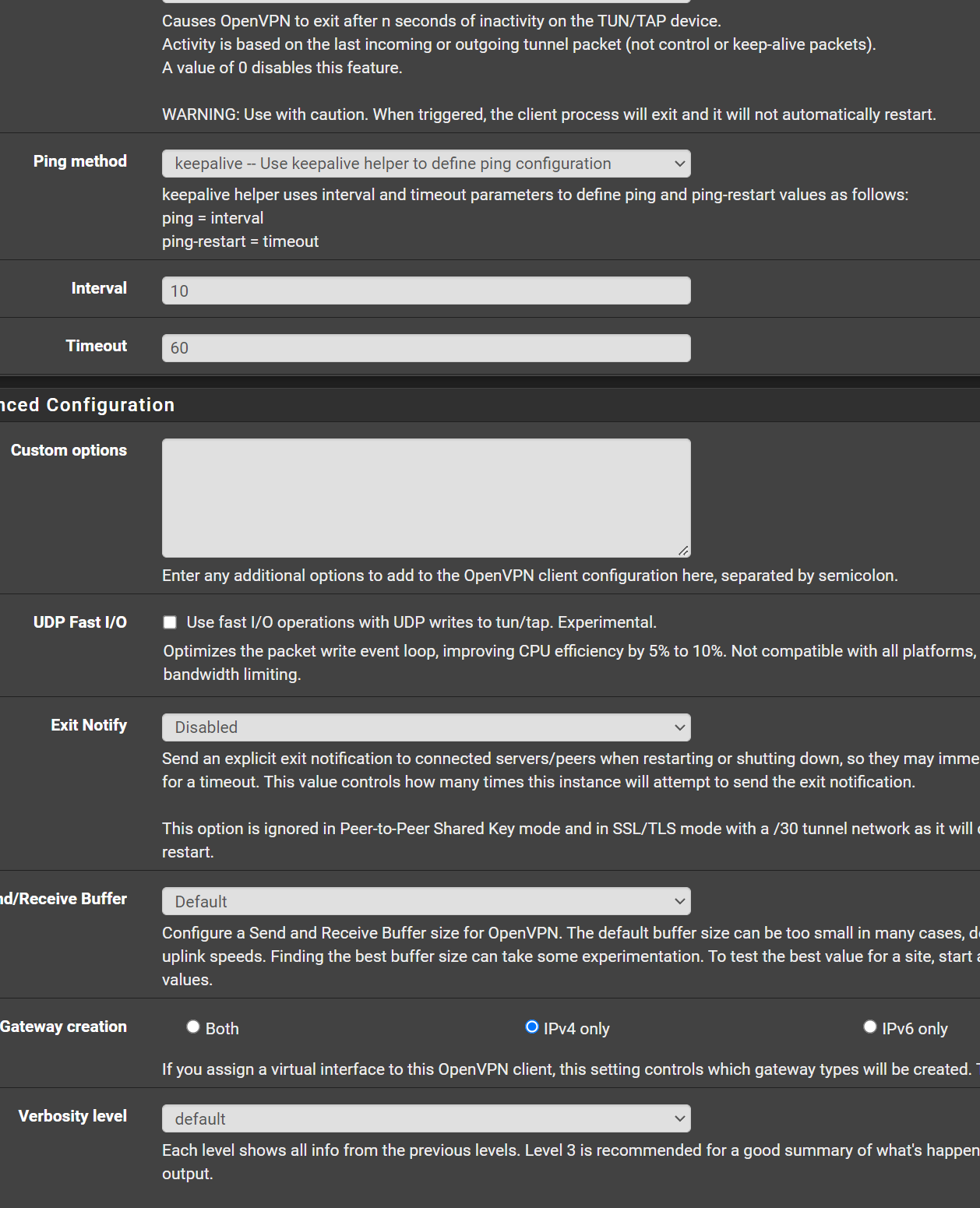
Client Log OpenVPN:
Any help is welcome.
-
@hispeed Get rid of the client specific override.
The tunnel networks have to be the same. Copy the subnet from the server to the client. 10.0.5.0/24
-
@hispeed
You're messing up the settings, again and again.Configure the CSO as I suggested above, please. The tunnel network is wrong again.
In the client settings you must not state a tunnel IP. You can leave it blank or enter the tunnel network equal to the server settings.
And the Remote Network is wrong! This is your local network. In the Remote Networks box enter the server sides network! -
@hispeed Forgot, in one of your pics you showed port 1160 open on the client side