Order of VPN clients determines if they work
-
Can someone comment on an issue that I am having regarding the use of a VPN. I can set up a number of openvpn clients for pfsense (using pfsense 2.5) . If I disable the 1st vpn client, the status--> openvpn shows that it is up but if I try to get outside my LAN I can't. Please see the picture below
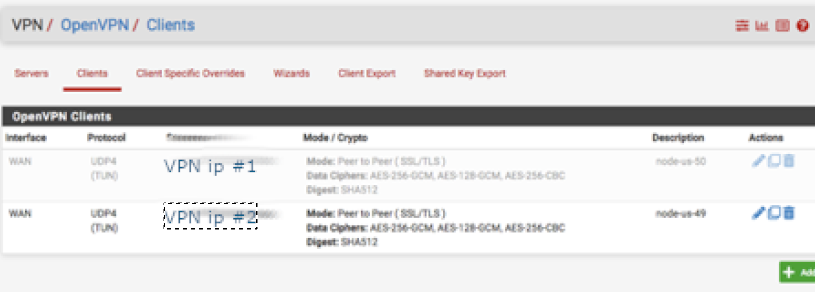
But if I list the rules in opposite order, with the enabled one first, I can get access outside the LAN. Is there something else going on that I am missing ?
I need to do this because every now and then the VPN goes down or the site I am trying to reach (like netflix or bbc ) decides it does not like the vpn. So being able to turn on a vpn easily would be very helpful. Thanks in advance... parry
-
@parry Is there anyone who can help answer this question please ?
Thanks -
@parry Show your rules then. Picture of your OVPN clients will not help here.
-
@bob-dig Thanks for the response
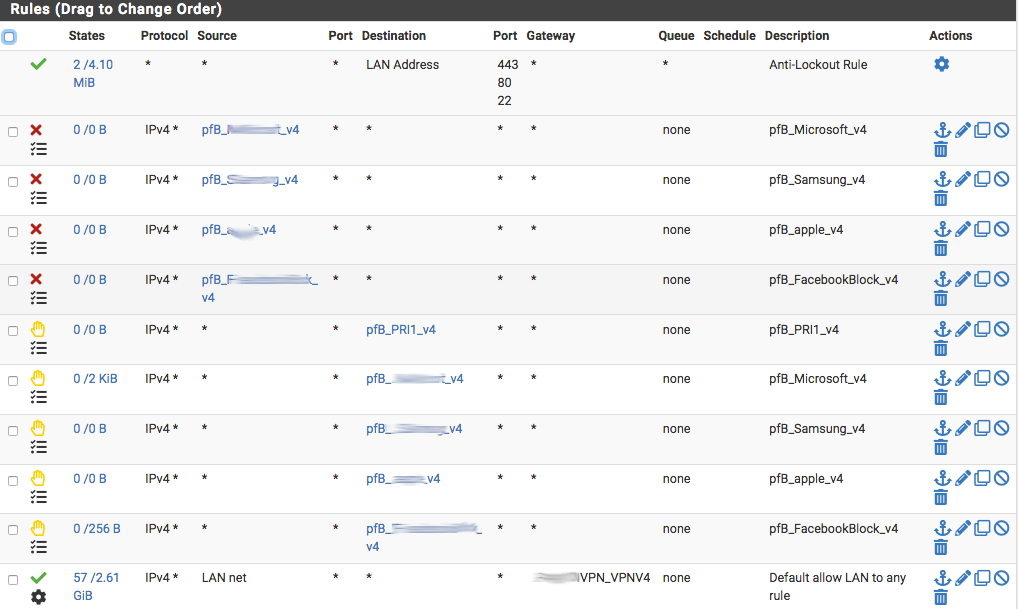
Here's my LAN
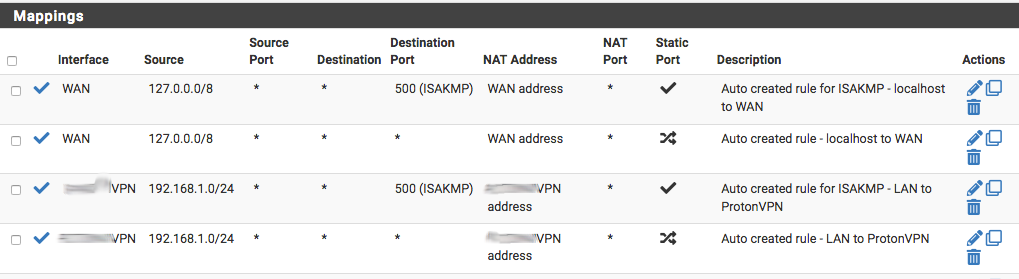
Here's the WAN Outbound
The VPN client has all the same settings except the VPN ip address.
If I place the active VPN client ahead of the disabled one, no problem, but if I place the disabled client ahead of the enabled one, I can't get out of my LAN. Is there anything else I need to post ?
Thank you again
Cheers, parry -
@parry What you want is to create a gatewaygroup with the OpenVPN clients, I guess. But before that you have to create Outbound NAT Rules vor every OpenVPN client. And before that assign every client its own interface.
What you have done so far doesn't look right to begin with.
It is also arguable that you block and reject the same IPv4 list on LAN.
-
@bob-dig Hmm, I dont really understand your answer Bob, ,probably because I am missing something . There is 1 gateway using the VPN ip address - that is created as an interface (I create the name, but the system assigns it ovpnc2 as a name). The ip address is assigned in the openvpn client The gateway name does not change, the outbound NAT rules don't change because the gateway is a name - and all I am changing is the ip address of the remote vpn. Everything else is the same. I suspect it is because the firewall is looking at the clients and sees the 1st one as disabled and does not look at any subsequent ones. However, if I check the status of the vpn it is up. even when the 1st client is disabled and I cant out of the LAN.
The reason I am doing this is to determine the functionality and performance of these different VPN addresses. I dont want to go through the pain of creating a new client from scratch so I just copy one client and update the ip address. If I could easily change their order I would but the clients panel does not allow this. Thanks for bothering to respond.
-
@parry Each client needs its own interface and outbound NAT, etc.
If you do it your way, you will have to live with the consequences. -
@bob-dig But Bob, what I do is simple. I change the IP address that's all. Everything else stays the same. The components of the system are (1) An interface that gets a name and that name does not change (2) A client that gets an ip address that accesses the VPN and uses the aforenamed interface The certificates, the CA are the same. If I just change the IP address for the single client, it works. But if I duplicate the client disable the first one in the list and keep the same ip address (I am just duplicating the client simply for a test) - I can't get out of my LAN. What am I missing ? When you say "live with the consequences" could you explain why these consequences arise ? If I were a betting person, I would say pfsense sees the 1st disabled client and stops there. It does not look for another client. I get if say I were using NordVPN and ExpressVPN (the latter only supports pfsense 2.4) for various purposes I would need to do this but Im using the same VPN provider. I bet I am missing something. As always, thanks.