Application and Server Communcation Between Two Pfsense Firewalls
-
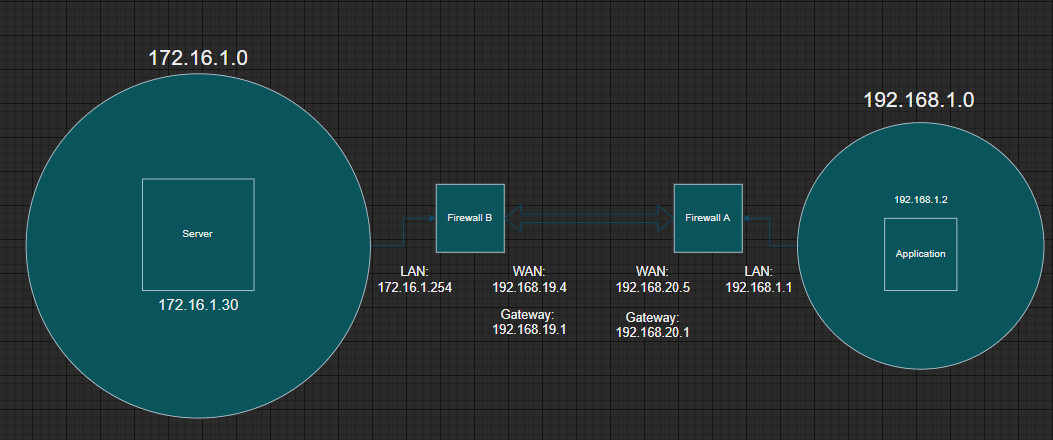
I have a test scenario where I have an application elastic-agent (behind Pfsense Firewall A) that needs to send communication over 8220 and 9200 to my server elasticsearch (behind Pfsense Firewall B). So the communication between A and B needs to pass through these firewalls, so they are at different subnets, I want to know if is it possible communicate to each other? How I can create these rules? The application elastic-agent (behind Pfsense Firewall A) need to send information to 172.16.1.30:9200 and 172.16.1.30:8220, which is on the other network. How will my subnet see the other? Please anyone can help me?
Sorry, if is not the correct topic area. -
1:
Why is your WAN on two different "net's" ??
192.168.19.x and 192.168.20.x
In order for that to work you would need a /21 WAN subnet mask (255.255.248.0) on both firewalls.2:
Your default gateway should point to the "Opposite" node
So on FWA def-gw-should be the IP of FWB (192.168.19.4) , and vice versa FWB should point to (192.168.20.5)Edit:
You have WAN as the communications interface , so there will be NAT/PAT involved.
You would have to "Expose/PortTranslate" the Server on FWB to the "Outside" , and on FWB allow inbound traffic traffic from FWA's WAN IP , to the exposed Server NAT IP.This is not a beginners task ...
Edit2:
I would probably make an OpenVPN Lan-to-Lan tunnel instead./Bingo
-
Hi @bingo600, thanks very much for the answers.
@bingo600 said in Application and Server Communcation Between Two Pfsense Firewalls:
1:
Why is your WAN on two different "net's" ??
192.168.19.x and 192.168.20.x
In order for that to work you would need a /21 WAN subnet mask (255.255.248.0) on both firewalls.I will verify and check this. The network of the WAN nets interfaces needs to be /21 right?
@bingo600 said in Application and Server Communcation Between Two Pfsense Firewalls:
2:
Your default gateway should point to the "Opposite" node
So on FWA def-gw-should be the IP of FWB (192.168.19.4) , and vice versa FWB should point to (192.168.20.5)Did you say that because of the opposite sides of the letters? I didn't quite understand.
@bingo600 said in Application and Server Communcation Between Two Pfsense Firewalls:
Edit:
You have WAN as the communications interface , so there will be NAT/PAT involved.
You would have to "Expose/PortTranslate" the Server on FWB to the "Outside" , and on FWB allow inbound traffic traffic from FWA's WAN IP , to the exposed Server NAT IP.I did the following, at FWA I expose the 9200 and 8220 ports and at FWB I use a NAT to redirect to the server 172.16.1.30, "Its works", I can get some information, but it is not working properly. I am missing some information, the server can't reach the application, but the application can reach the server, but some information is missing. Do I have to do the inverse NAT (at FWB expose ports 9200 and 8220 and at FWA create a NAT rule to redirect to my application)? is it correct?
Edit:
This only works because I have a configuration at elastic-agent that I say to reach the WAN interface of the firewall B, is the unique way for receive information from the elastic-agent, but I think is more correctly maintain to reach the elasticsearch at 172.16.1.30, but if I do this, I can't get anything. I don't know if this are right.Thanks again.
-
@lastday said in Application and Server Communcation Between Two Pfsense Firewalls:
2:
Your default gateway should point to the "Opposite" node
So on FWA def-gw-should be the IP of FWB (192.168.19.4) , and vice versa FWB should point to (192.168.20.5)Did you say that because of the opposite sides of the letters? I didn't quite understand.
Well since you are using NAT on the WAN , and have Natted the server to the outside of FWB. And you will use a /21 Wan subnet mask , default gateway will not be needed in the communiction.
Edit:
This only works because I have a configuration at elastic-agent that I say to reach the WAN interface of the firewall B, is the unique way for receive information from the elastic-agent, but I think is more correctly maintain to reach the elasticsearch at 172.16.1.30, but if I do this, I can't get anything. I don't know if this are right.
Thanks again.The current setup will only allow communications to be initiated from the Agent to the Server. Once initiated , the server is allowed to answer.
-
@bingo600 said in Application and Server Communcation Between Two Pfsense Firewalls:
The current setup will only allow communications to be initiated from the Agent to the Server. Once initiated , the server is allowed to answer.
So, I don't need to do inverse NAT, correct? So there is any problem with my elastic-agent. Thanks!