Unable to illegal DNS record from pfsense (DNS-resolver corruption)
-
I'm investigating DNS illegal entry for (using pfsense 22.05 release) on CLI
-
@asadz said in Unable to flush illegal DNS record from pfsense (DNS-resolver corruption):
I'm investigating DNS illegal entry for (using pfsense 22.05 release) on CLI .....
.....
but it re-appears shortly.unbound isn't making this up.
Someone is asking for it. Why not locating the device that asks for illegal host names and silence it ? -
@asadz said in Unable to flush illegal DNS record from pfsense (DNS-resolver corruption):
it has changed the entire mapping for local addresses
huh? You mean everything returns with that address? Use of .local as the tld is not a good choice. This is a special tld, use something different would be my one suggestion. The current recommended domain to use locally is home.arpa, or use say .lan as your tld. This is highly unlikely to ever be used in the public space.
But if if someone asks for something.local and that is returned by unbound. Either something registered that in unbound, do you have enable dhcp registration enabled? Or you set it in unbound with a host override, or its being looked up public.. What is the fqdn your doing a query for? .local is not something that would resolve public, but are you forwarding to an internal dns, or an ISP dns? etc..?
-
@johnpoz said in Unable to illegal DNS record from pfsense (DNS-resolver corruption):
@asadz said in Unable to flush illegal DNS record from pfsense (DNS-resolver corruption):
it has changed the entire mapping for local addresses
huh? You mean everything returns with that address? Use of .local as the tld is not a good choice. This is a special tld, use something different would be my one suggestion. The current recommended domain to use locally is home.arpa, or use say .lan as your tld. This is highly unlikely to ever be used in the public space.
But if if someone asks for something.local and that is returned by unbound. Either something registered that in unbound, do you have enable dhcp registration enabled? Or you set it in unbound with a host override, or its being looked up public.. What is the fqdn your doing a query for? .local is not something that would resolve public, but are you forwarding to an internal dns, or an ISP dns? etc..?
Sorry, I cannot reply as I have trouble editing my original post its blocked as spam filter, I will update complete reply above. thanks.
-
thanks , please wait let me update complete reply in my original post
-
@asadz
please use this link for read-up, while I fix this post.The thing is that in term of priority the for .local address the Domain controller does the resolution for .local address, and yes in DNS resolver we set over-ride for .local addresses and this static mapping. You can see the results of dns-reply.log in link above
-
@asadz said in Unable to illegal DNS record from pfsense (DNS-resolver corruption):
yes in DNS resolver we set over-ride for .local
Well if you point a domain override to your AD for .local - and you don't like the answer your getting your going to have to look in your AD dns on why its returning that address.
-
@johnpoz
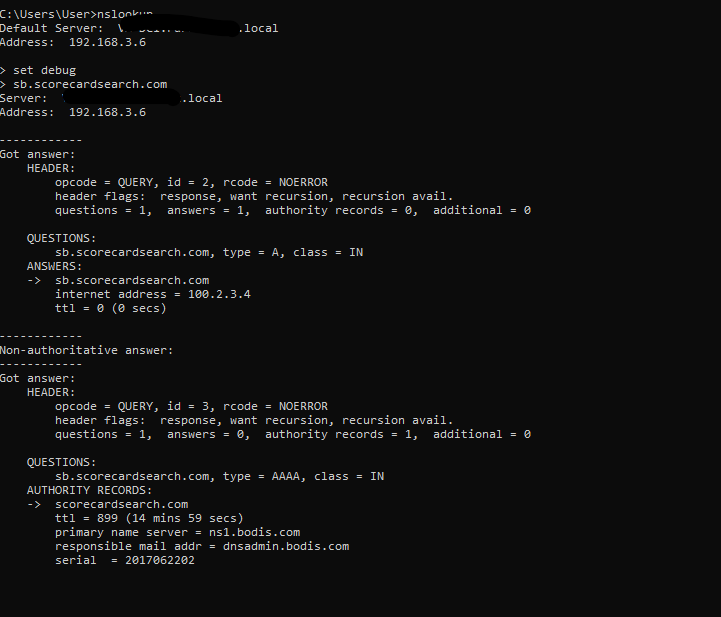
1415:40:17,reply,A,A,Unk,sb.scorecardresearch.com,192.168.3.6,100.2.3.4,USthis log entry from pfsense dns_reply.log shows the DC is requesting A record resolution for sb.scorecardresearch.com and it is however returned a wrong IP address.
-
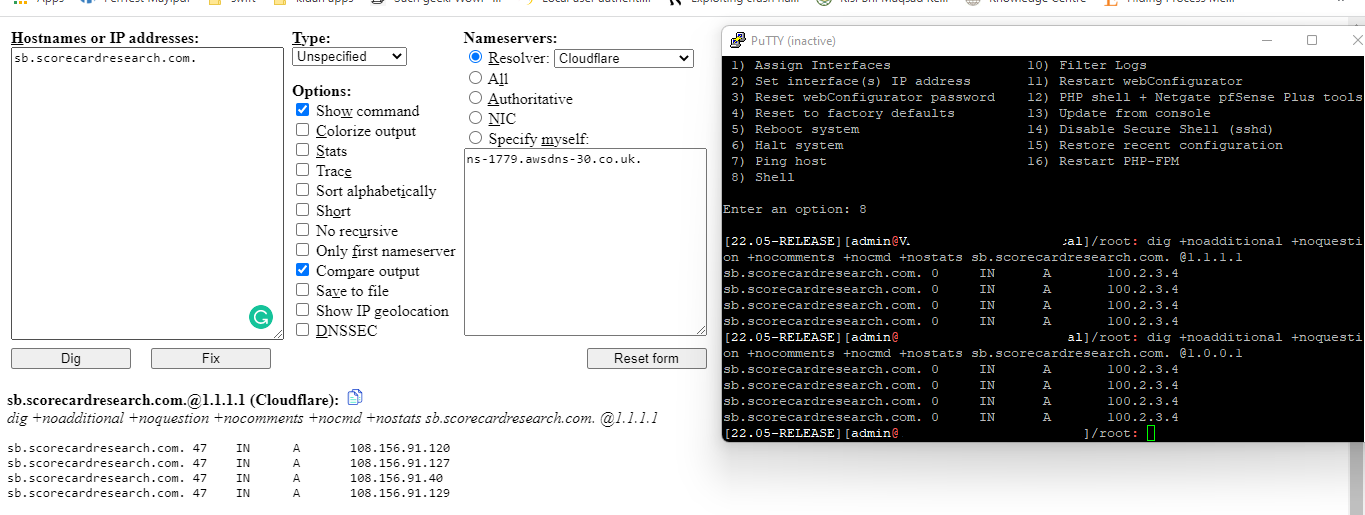
@johnpoz also i don't expect the local DC to resolve this , as its external IP address, and the local DC is only responsible for .local network host names resolution. You can see the dig command comparison as well. Pfsense is using cloudflare for name
-
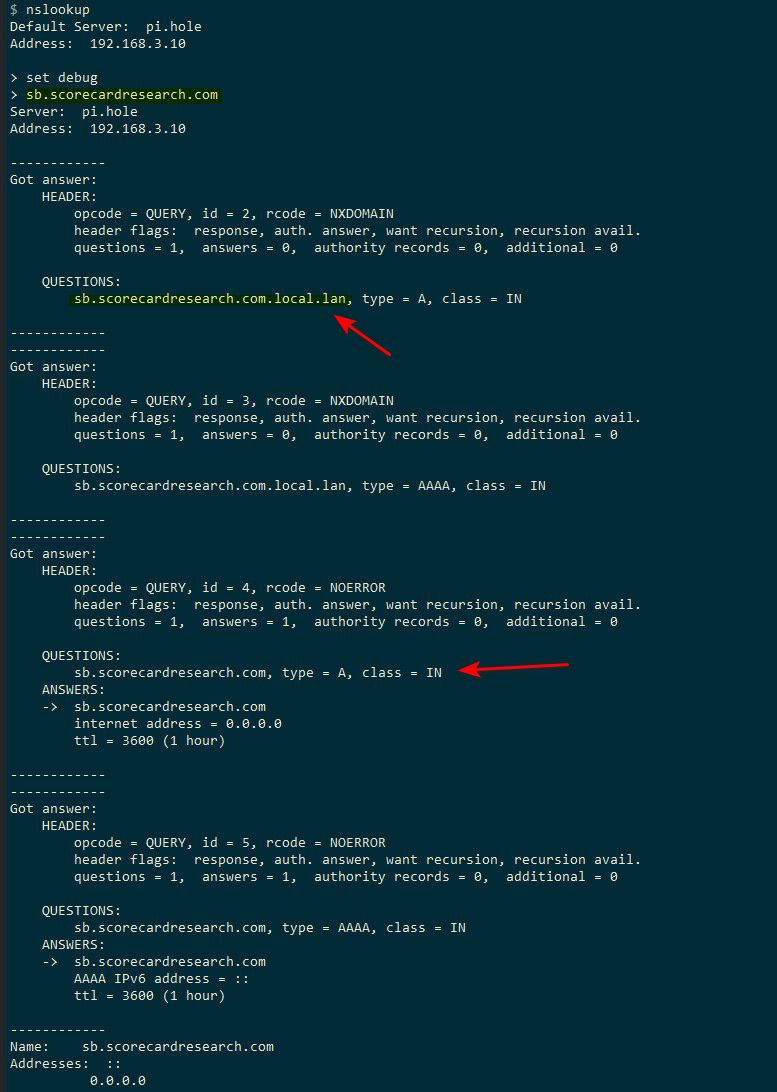
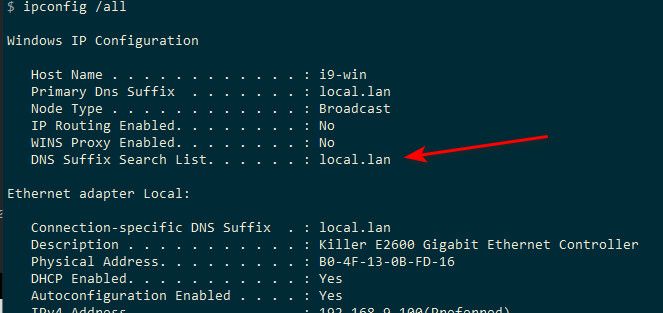
@asadz your client asked for .local per what you posted before..
Clients with search suffix setup will query your fqdn with the local tld attached.. So it would ask for say sb.scorecardresearch.com.local
Which is possible your local dns returned a wildcard for that 100.1.2.3 address..
example, see set debug on nslookup and then asked for sb and you see it first asked for that fqdn with my local domain attached local.lan
-
@johnpoz The reply in my end doesn't contain any postfix or append after . Pls see ss
-
@asadz and that 192.168.3.6 is your pfsense IP?
odd that it returns a 0 ttl, unless you have unbound setup to do that (it is not default).
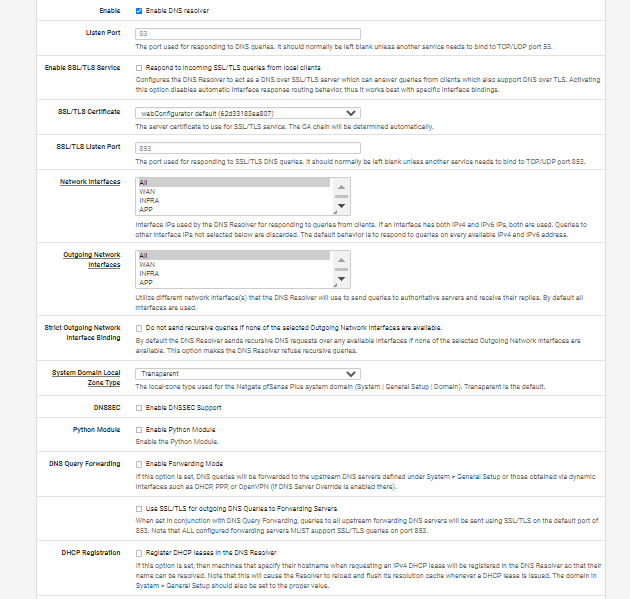
Are you forwarding in unbound? Or just that domain override - sure you didn't setup it as a host override or a full redirect?
What exactly do you have setup in unbound for host or domain overrides and do you have anything in custom that would do a full redirect.
if you ask unbound where it would go to look that up, what do you get?
example, here is on mine
[22.05-RELEASE][admin@sg4860.local.lan]/root: unbound-control -c /var/unbound/unbound.conf lookup sb.scorecardsearch.com The following name servers are used for lookup of sb.scorecardsearch.com. ;rrset 3240 2 0 8 3 scorecardsearch.com. 3240 IN NS ns2.bodis.com. scorecardsearch.com. 3240 IN NS ns1.bodis.com. ;rrset 3270 1 0 8 3 ns1.bodis.com. 3270 IN A 185.85.196.36 ;rrset 3287 1 0 8 3 ns2.bodis.com. 3287 IN A 199.59.243.150 Delegation with 2 names, of which 2 can be examined to query further addresses. It provides 2 IP addresses. 199.59.243.150 not in infra cache. 185.85.196.36 rto 301 msec, ttl 540, ping 1 var 75 rtt 301, tA 0, tAAAA 0, tother 0, EDNS 0 probed. [22.05-RELEASE][admin@sg4860.local.lan]/root: -
You are very helpful i for once saw a glimmer of hope. See the output plus config
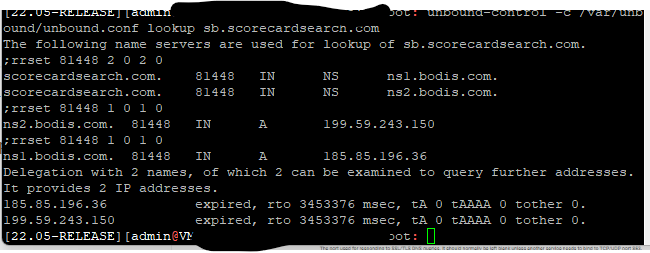
does this mean its cache gone bad or some static entry somewhere which is returned every time
-
@johnpoz
unbound-control -c /var/unbound/unbound.conf flush sb.scorecardsearch.com. but it return back.Also i'm unable to ping or tracert to 100.2.3.4, perhaps due to ttl 0?
-
@asadz well that shows unbound would ask the authoritative NS for that domain.
I don't see how you could be getting back a 100.x address from them?
What do you have setup for host or domain overrides? Do you have anything in the custom options box of unbound?
-
@johnpoz said in Unable to illegal DNS record from pfsense (DNS-resolver corruption):
@asadz well that shows unbound would ask the authoritative NS for that domain.
I don't see how you could be getting back a 100.x address from them?
What do you have setup for host or domain overrides? Do you have anything in the custom options box of unbound?
No I checked there is nothing under custom rest of setting I showed as ss. One off thing that happened during pfblockerng force reload , which was performed right at the time of Cron job was seconds away from execution and it gave me some fatal error which was later was fixed by restart of pfsense.
You can Dec 14 log dns reply.log before there was no log entry for this. Also when I ping via up address for e.g
Abc.HQ.local 192.168.8.9
I get the correct address even when I do
Ping - aBut nslookup abc.HQ.local brings 100.2.3.4
Also when I do wireshark I see A query record returned by DC for 100.2.3.4 and not by pfsense. I flush cache at DC but no change, also rebooted DC as well
-
@johnpoz said in Unable to illegal DNS record from pfsense (DNS-resolver corruption):
@asadz well that shows unbound would ask the authoritative NS for that domain.
I don't see how you could be getting back a 100.x address from them?
What do you have setup for host or domain overrides? Do you have anything in the custom options box of unbound?
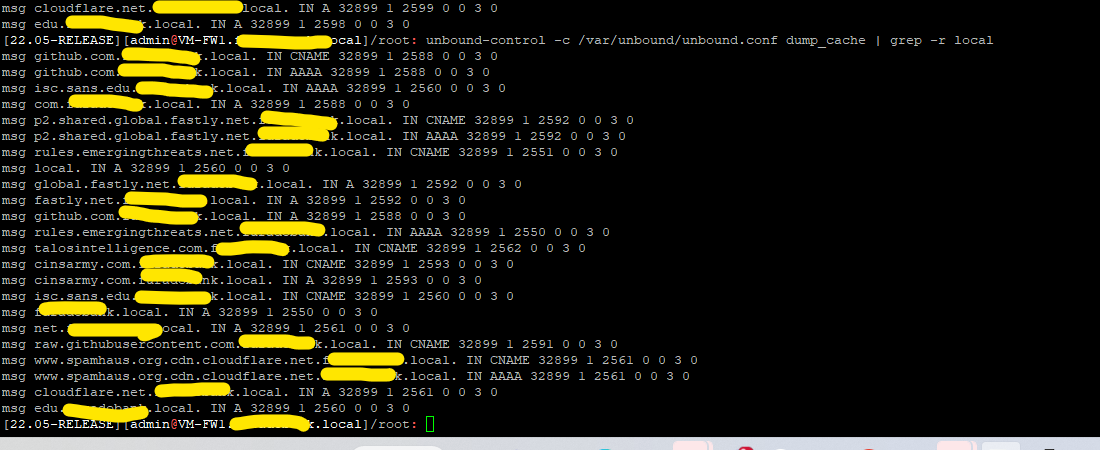
Following your advice I check .local resolution as you suggested, I see strange entry the yellow is the domain that is owned by me, but I see .local appended queries going to all places e.g github,isc etc.
Does it look like poisoning, how can I remove these entries?
-
Also, i found
Services> SnortPass> ListEditpasslist included this IP address, although the list was not attached to any snort interface.
-
@asadz again that is common practice for pretty much any client.. It will append the search suffix..
Again a single level domain (sld) like .local is not a good idea, especially with .local because of its special use. MS did change their stance on these quite some time ago.
"Existing products may continue to function with SLDs, but SLDs aren't a recommended configuration for future deployments and may not work with some products or versions."
Its a been quite some time since I have had to deal with MS world and dns issues like this. But it is also best that if your a MS shop to have your clients get their dhcp and dns from your AD.. Clients should point directly to your AD for dns, and then MS dns can forward to pfsense to let it resolve stuff that is not in your namespace.
You can look to how to alter the suffix search, and or another problem that can come up is the devolution of the domain as well.
My advice would be to point your clients to AD DNS, and move away from the .local sld. Use something like yourname.home.arpa. This is the new tld that is recommended for local domain use.
-
@johnpoz Thank you for your education, I will take this mater related to .local sld internally with the IT team.
But, we are using DC as DNS server it has SOA records, along with forward and reverse lookup zones configured up.
I'm not still not sure, about following:-
- why my internal hostnames are resolved to 100.2.3.4 address, where this DNS response comes from, why can't I change to point to correct IP address?
- Why ttl is set as 0 for sb.scorecardsearch.com, I read if the value is artificially set (due to some error) then the upstream cache server would reject for new DNS TTL response.
- Also the resolution for the address, has changed the DNS mapping for internal hosts
e.g abc.bank.local -> sb.scorecodesearch.com
dns.bank.local -> sb.scorecodesearch.com :100.2.3.4
even incorrect why this DNS A record response change internal mapping of host on network?
Thank you for help