allow traffic from 4444 to 445 (smb)
-
How should I set up my pfsense firewall to allow traffic from port 4444 to port 445 so I can execute a meterpreter reverse tcp shell on a Windows 7 client. This is for learning purposes on a private virtual lab setup. So to learn how you can do it but also how you can defend against it.
I already tried to make a firewall rule source ip host with metasploit on installed to client ip (destination) with ports. But it's not working. I did install msfconsole on a Windows 11 host. The client IP is installed on vmware.
I wonder if it is a pfsense configuration mistake or a windows 11 security thing that doesn't allow it.
-
@owlbear said in allow traffic from 4444 to 445 (smb):
from port 4444 to port 445
Is that a source port of 4444 to 445, or do you want traffic that hits 4444 on an interface address on pfsense to be forwarded to 445..
If your not natting between these networks then would be a simple firewall rule with the source port set, which is not very common. But quite often when your natting you might want to send traffic that hits port X to be sent to device behind pfsense nat to be sent to port Y. This is a port forward.
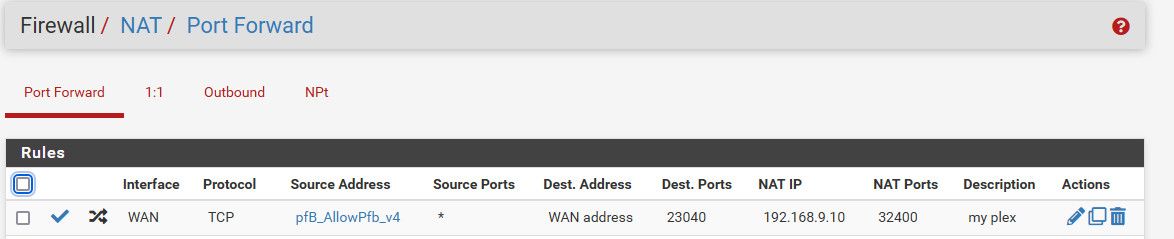
Example - here I send traffic that hits my wan on port 23040 to my plex server on 32400
I think this is what you are after because it is rare that a specific source port is used, source ports are normally some random port above 1024..
If you want to change the port that traffic is sent too, you would use a port forward. But if this is all internal and checking for some exploit not sure why you would not just send traffic to 445.. Where did this port 4444 come from?
But yes - more than likely the windows firewall would prevent access to say 445 from some non local IP..
-
The 4444 port is the standard port used by metasploit for the exploit.
In fact putting in any * would be easier I guess. It's comming from the subnet (WAN-side) before the firewall and has to get to the lan (Windows 7 SMB vulnerability) behind te firewall. -
@owlbear well if its sending traffic to your wan address to 4444 and you want that to go to some device on your lan on port 445, then you would use a port forward like I show for my plex.
you sure 4444 is listed as being the default listening port for metasploit - that wouldn't have anything to do with an exploit to some smb service on 445
-
@johnpoz Thanks for the example and your explanation of the port forward rule. I have created a similar one but indeed specifically for port 445. This time I did not do an exploit from my Windows 11 machine but from Kali Linux in the same LAN segment 192.168.0.0/24 as my windows 11 machine. This time it is quite easy to run the exploit on a machine in a different LAN segment behind the pfsense firewall. I suspect Windows 11 has built-in security.