Pfsense only OpenVPN Server with only single interface WAN
-
Hello,
All client can ping 10.142.0.x but FAIL from other side ….
When ping from 10.142.0.4 (Windows 2016) to any pfsense client it's fail :-(
If i'm log in pfsense server GUI 10.142.0.7 and test ping to 10.10.5.249 it's only work with OPENVPN interface if I choose WAN it's fail….
See images in this link for more informations …..
https://cloud.ordivert.net/index.php/s/ubEciIGkjNlz3lB
Where add static route in pfsense server or directly in google cloud interface ???
Because my Windows 2016 server VM on google (10.142.0.4) ogtain DHCP automatic and use 10.142.0.1 for Gateway. Can add route directly in my Windows 2016 ? do you have demo route for me ?
Thx!
-
@n1tr0666 said in Pfsense only OpenVPN Server with only single interface WAN:
If i'm log in pfsense server GUI 10.142.0.7 and test ping to 10.10.5.249 it's only work with OPENVPN interface if I choose WAN it's fail….
Seems that the client is missing the route to your google cloud network.
-
What do you means ?
-
On the client you have to set the route to the 10.142.xx.xx/20 network.
In pfSense GUI enter the network into the "Remote network/s" box. -
on the client ?
client can ping google cloud VM
but
google cloud VM cannot ping client
-
Again the question:
All 6 site-to-site clients are connected to a single server? If yes, have you added CSO? -
Yes all 6 pfsense client is connected to same pfsense server (10.142.0.7)
CSO ?
-
You find it in the GUI: VPN > OpenVPN > Client specific overrides
It's necessary to tell the server into which tunnel the packets have to be routed.CSO only work in conjunction with TLS Auth (a unique certificate for each client).
-
Yes ! already setup it !!!!
My error it's maybe that my Windows 2016 server 10.142.0.4 have Gateway 10.142.0.1 but my pfsense server is 10.142.0.7
In my Windows 2016 … if add static route like the server ignore this rules ….
route add 10.10.5.0 mask 255.255.255.0 10.142.0.7
and cannot find option in google cloud for it and if i'm configure static ip on my google cloud VM (Windows server) I cannot reach vm after, only work in DHCP.
-
server1.conf.txt Even though this post is 2 years old, I thought should reply to it as is still relevant today and helped me fix the same problem I had in 2020.
As like the original post, I too couldn't access any local network resources while my pfSense is set up in a local XCP-ng VM using only one WAN port. I was able to access the internet and local pfSense IP but couldn't ping any other LAN IP/resources. Oddly, the local Xen Orchestra website loaded without any images, only the login page with just text but couldn't access all the other local resources, NAS, Plex server, local servers, etc.
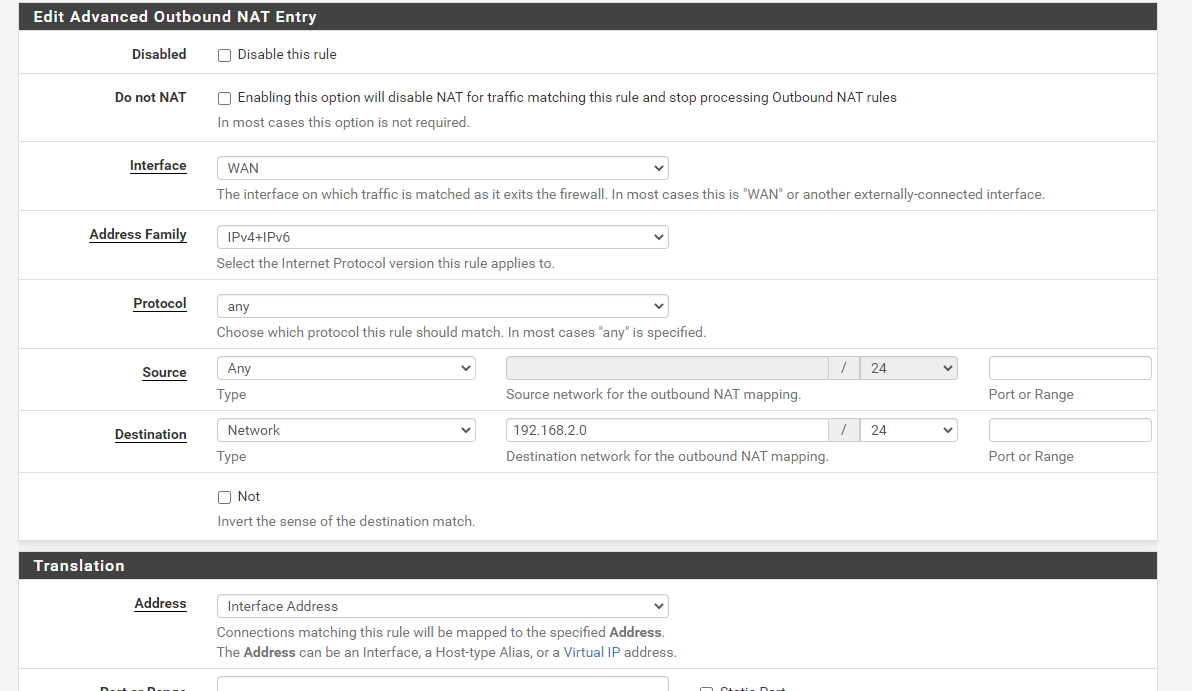
Thanks to viragomann advice on setting up the Firewall NAT Outbound rule, everything works. I was able to access all LAN resources from my work!!
My router IP is 192.168.2.1 so I setup the NAT Outbound rule as followed:
Interface: WAN
Source: Any
Destination: Network 192.168.2.0/24
I haven't set up the Dynamic DNS through pfSense as it was set up through my home router.
ALSO, DON'T FORGET TO SET UP PORT FORWARDING to port 1194 through the home router, otherwise, you won't be able to access the VPN server.
I followed this instruction to set up the VM:
https://xcp-ng.org/blog/2019/08/20/how-to-install-pfsense-in-a-vm/I followed this video to set up pfSense on local XCP-ng VM:
https://www.youtube.com/watch?v=fsdm5uc_LsUI followed these videos to set up the OpenVPN on pfSense:
https://www.youtube.com/watch?v=dBOQnApxzzQ
https://www.youtube.com/watch?v=PgielyUFGeQ[0_1602430059510_server1.conf](Uploading 100%)
-
M manfredoberd referenced this topic on