DNS FOR VPN
-
Hi,
I want to say that I don't post until I know I cannot find the answer for issues. I do search but I believe my question is not like the ones on forums I have come across.I have setup OPENVPN with a VPN Provider. It works well for the devices that I have set an alias for. I have two on that alias. I also set up some domain names to bypass the VPN and go out my regular WAN connection. For the devices behind the VPN, everything works well, no dns leak, nothing, works as it should. However, I have found that for devices that are not supposed to be behind the VPN, it shows my correct ISP address but when checking for DNS, those devices are using the VPN DNS.
I am using a port forward rule for the VPN DNS on port 53 and in there the DNS of my VPN provider is specified. Also, I have an active directory domain set up and also use PIHOLE to block ads, malware and adult websites. On PFSENSE, under DHCP, the Pihole is set up for the domain on all devices, this works well so that it block all ads. On the Pihole, under DNS, I have set the DNS IP for my domain controller. On the windows DNS server, I have set the PFSENSE router IP under the forwarders tab. Then on the PFSENSE box, setting, general, DNS servers, I have entered OpenDNS servers and google's. Under DNS resolver, network interfaces, I have my LAN and local host highlighted, under outgoing network interfaces, i have only highlighted the VPN interface. DNSSEC is checked as well as Enabled forwarding mode.
Can anybody please advise as to why the none VPN devices use the VPN DNS? I have checked lots of guides and this seems to be the only way that my VPN devices don't leak the DNS. I just wonder if there is anything I am missing or is there any drawback of having it setup this way? I feel like it can be tweaked a bit more but I don't know what else to look for.
If you need more info about my setup, please let me know. I can provide it.
Thanks! -
Under general settings, you can specify dns for different gateways
Set a dns server for wan gateway
And set a separate entry for vpn gateway -
@oxibquieh The way that I deal with this, although there may be better ways, is to create DHCP static mappings for only the hosts that I wish to bypass the VPN, and in those static mappings assign DNS servers. This is manageable as long as you don't have too many hosts that you want to bypass the VPN.
The reason why all your hosts are performing DNS via the VPN right now is that when you use the DNS resolver, by default all of the clients on your LAN are given your pfSense machine's LAN IP (e.g. 192.168.0.1) as their DNS server. And the DNS resolver, as you described, is configured to only use the VPN interface for outgoing queries.
But if you override a client's DNS server(s) in a DHCP static mapping, it will use them instead. For example, if you create a static mapping for a client to get the LAN IP 192.168.0.105, and assign it Google's DNS server 8.8.8.8, and then have other policy routing rules in place to make 192.168.0.105 bypass your VPN, then all if its DNS traffic to 8.8.8.8 will bypass the VPN as well.
-
@thenarc Thanks very much for your reply.
I only have two devices behind the VPN. All devices in my network have static mappings and I'd like to keep it that way because it's more organized. As for assigning the DNS server(s) in those static mappings, I have set the PIHOLE there as that's what blocks ads and it's doing a really good job. I'd also like to keep that for all the devices.Is there a way to change the settings for the DNS Resolver ? I followed this guide: https://www.techhelpguides.com/2017/06/12/ultimate-pfsense-openvpn-guide/
to setup the VPN but I only have one VPN connection and I am using the DNS port forward method 1 for DNS leak prevention.So i guess my only choice from your response it to remove the entry for the PIHOLE as the DNS server for the devices behind the VPN and set for example google's DNS server? I already have aliases set up for the devices behind the VPN and for domains to bypass the VPN. Any of those would required to be modified?
-
@teknikalcrysis
Thanks for your reply teknikalcrysis - so to verify this is the section you are advising, correct?
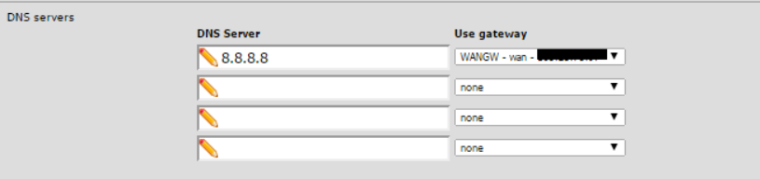
if yes, do I only need two entries one for the WAN and the other for the VPN? Does the VPN gateway need to be its own DNS address?
Do I need to modify the network interfaces and outgoing network interfaces under DNS resolver?
Thanks again, -
@oxibquieh I may be getting confused. If you assign any DNS servers within static mappings, then DNS queries from the hosts to which those static mappings belong will be made outside the context of the VPN tunnel. The only exception to that statement would be if the PIHOLE itself connects via the VPN tunnel. Your setup may be more complicated than I realize, but the core points are:
If you are using the DNS resolver, and have it configured to use only your VPN interface(s) for outbound queries, then any LAN hosts for which you have not specified DNS server(s) within static mappings are going to perform DNS queries through the VPN.
Within the context of static mappings, if you specify only "raw" DNS servers for a given mapping (e.g. Google's 8.8.8.8), then the host to which that mapping applies will perform DNS queries outside of the VPN tunnel. If you specify another LAN host as the DNS server (e.g. your PIHOLE), then whether the DNS queries occur through the VPN tunnel will depend on whether you have said LAN host that is acting as a DNS server configured to use the VPN tunnel.
I hope this hasn't just further muddied the waters :)
-
@thenarc - geez, lol, I think this has indeed muddied the waters much further...
I just tried the advice that teknikalcrysis provided and specified a DNS server for the WAN and one for the VPN under the general settings. This does not do change anything at all.
I also changed the outgoing network interfaces to include the WAN (regular ISP) and VPN but that gives me a DNS leak as it shows the DNS from my location.I think that's my issue, my setup is more complicated than others out there, as I have a PIHOLE and also a Active Directory domain + DNS setup in between. So the clients get the IP from the PFSENSE box, the DNS is the PIHOLE which in turns points to the Windows DNS on the DC and DC DNS points to the PFSENSE box for forwarders. That's the only way I have been able to make it work so that the clients are able to get GPO's properly and at the same time the PIHOLE does it blocking. I have tried the PFBlocker NG package from PFSENSE but that slows down my internet connection considerable.
I guess my question is now, are there any issues/disadvantages if the devices that are not supposed to be behind the VPN show the DNS from the VPN?
The other thing is for the domains I have listed to bypass the VPN (under an alias), it does not work as it always uses the DNS for the VPN.
I have searched and searched about this but I can't seem to find a reason/workaround/fix.Thanks! :)
-
@oxibquieh I would say that generally speaking, it shouldn't matter if hosts that you don't want to go through the VPN for "general traffic" still perform their DNS lookups through the VPN. The potential downsides to this are:
If the VPN goes down, then even your hosts that "bypass" the VPN will lose their ability to resolve hostnames.
Also, content delivery networks will attempt to optimize performance by handing you a server that's close to you geographically. For example, if you live in Idaho, and perform a DNS query on a Netflix server, chances are you'll be directed to a server near Idaho. A VPN obscures your geographical location, so it can frustrate this attempt to provide you with a nearby server. Although again, in practice, it's probably unlikely that this would bite you in a noticeable way.
I can say that I use pfBlocker, and don't notice any slowdowns, so that may be something worth looking into. The other option might be to simply run two PIHOLEs, and have one routed via the VPN and the other not. Does that make sense?
-
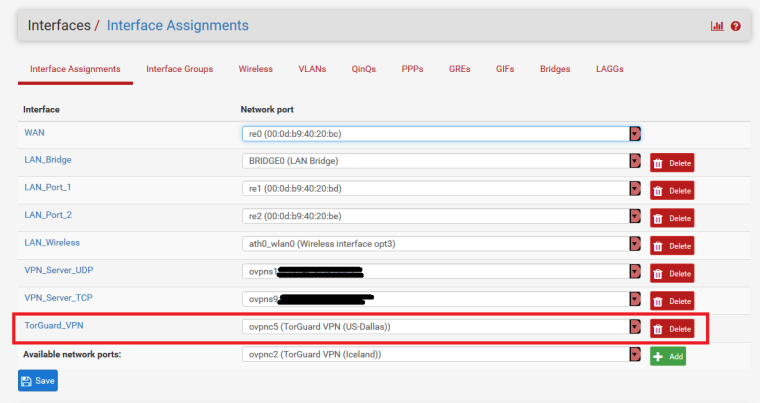
I have a similiar setup, Modem>LinkSys Router>PfSense Router....I use pgBlockerNG with DNSBL and IPv4 lists to function as a piHole rather than having a separate device... But I also run all my traffic through a Paid external VPN (TorGuard)...
Also rather than using DNS Forwarder (dnsmasq) I am using the DNS Resolver (Unbound)
If you try this config, please make a backup of your current config before making changes. That way, if changes are undesirable you can just restore your config.Here is my General Settings setup:
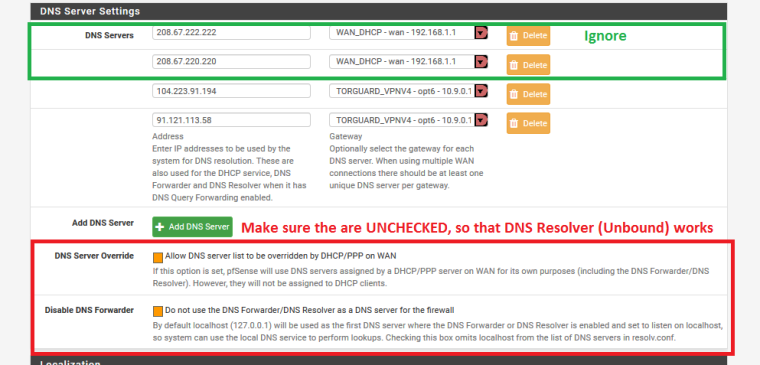
Here is my Unbound setup: (NOTE : I have DNS QUERY FORWARDING UNCHECKED)
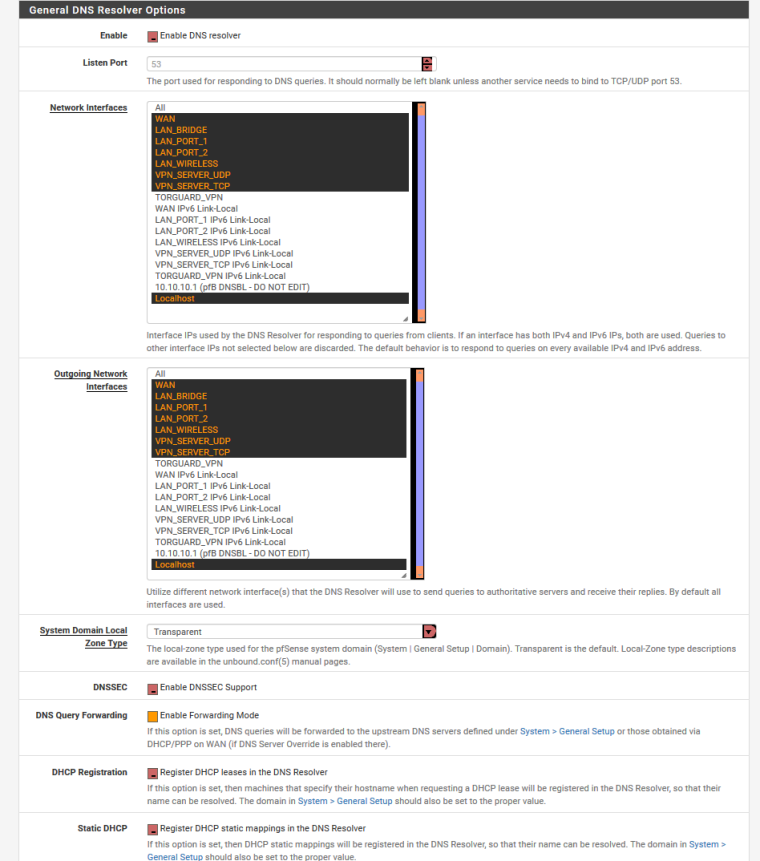
I have DNS Forwarder (dnsmasq) DISABLED
On the LAN Firewall Rules, or In my case the LAN_Bridge I have the following policy based rules to route traffic to specific gateway interfaces... All Computers and mobile device pass through the VPN, my kids tablets and all other defined traffic is defaulted to bypass the VPN and go directly to the WAN. And then I have a DNS rule to allow traffic to the DNS Resolver
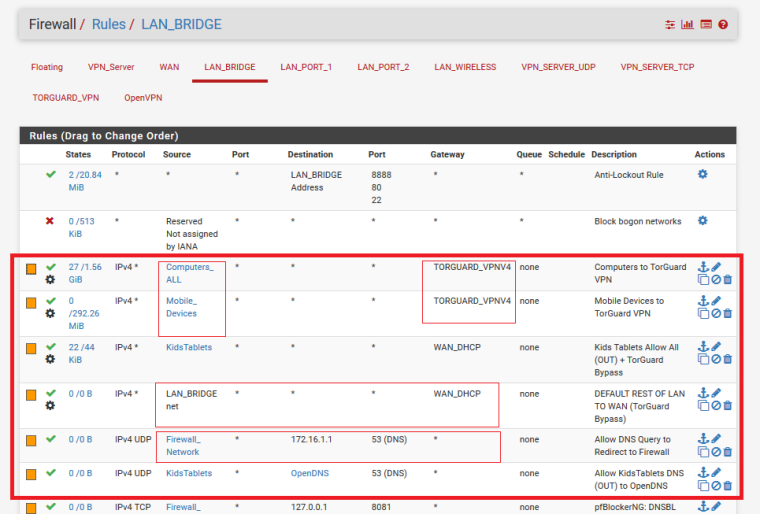
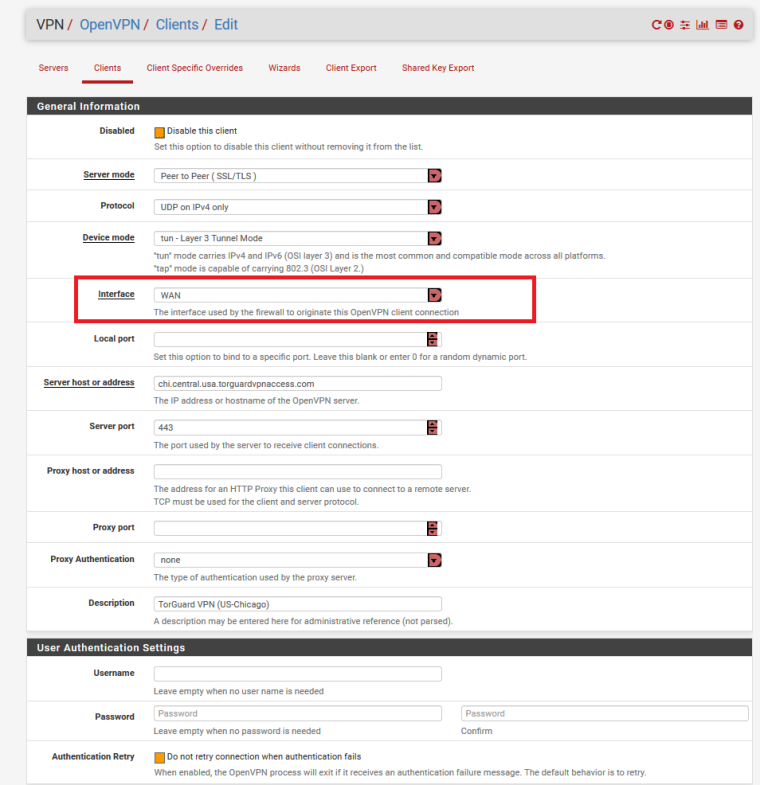
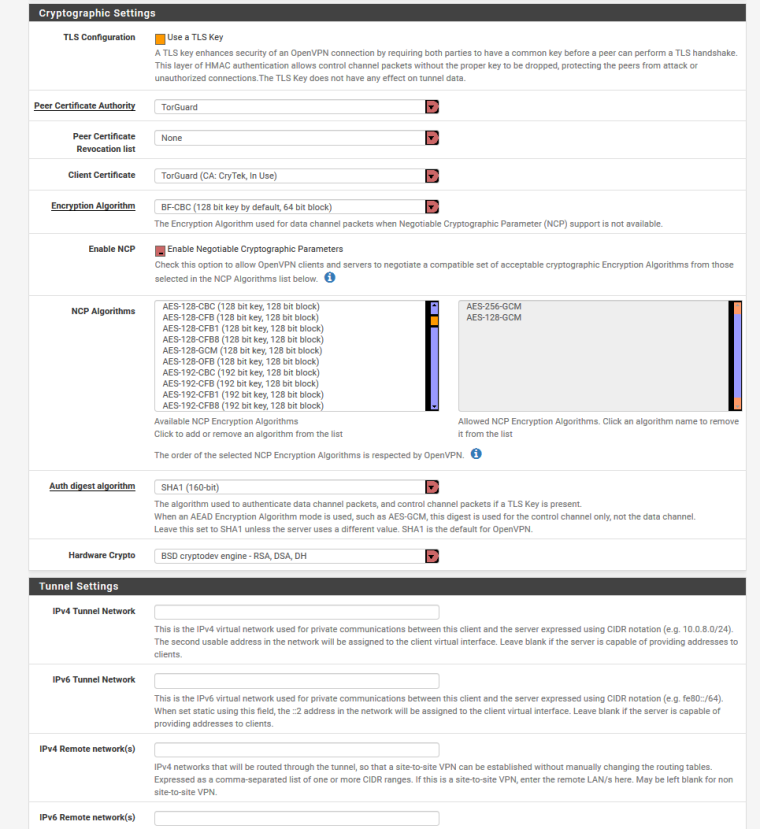
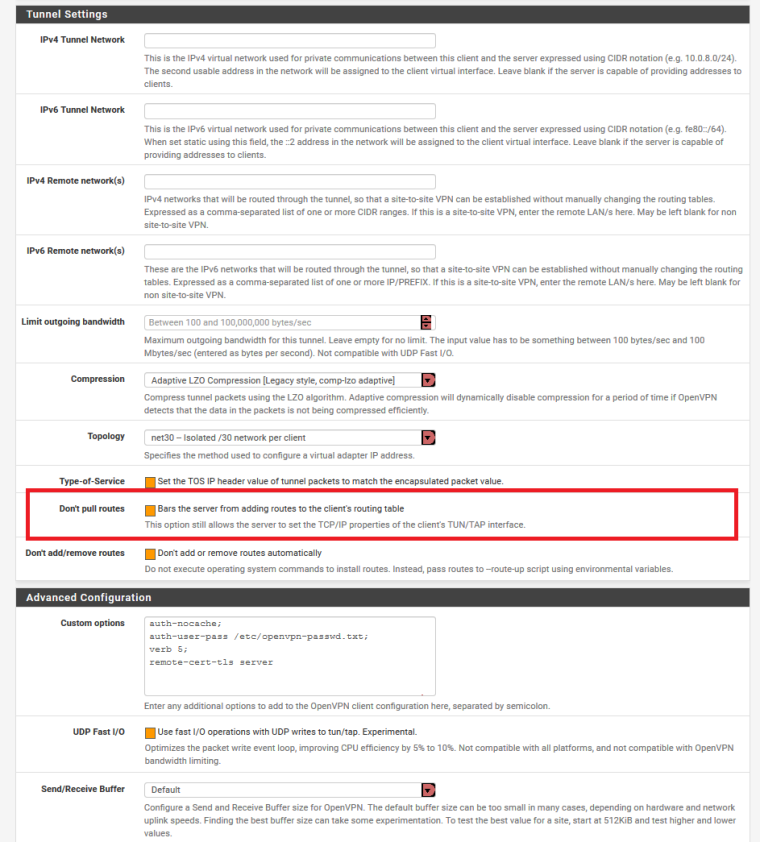
Here is my OpenVPN setup...Make sure you have the "Do Not Pull Routes" UNCHECKED...so that when the VPN is active the DNS routes go through the VPN rather than DNS Resolver (Unbound)
Then the remainder of the trick lies within the NAT-Outbound section...the easiest way to do this is first click make sure the Auto Rules have been generated by have is set to Auto Rules and SAVE...then Click MANUAL RULES and SAVE so that the auto rule are converted to manual rules, then click HYBRID RULES and SAVE to the the auto rules are regenerated. Then you will still have the Manual rule that are now duplicates left behind... Manually edit each rule, and only change the INTERFACE from WAN to the VPN interface....then you will need to add a DNS rule here in the outbound NAT
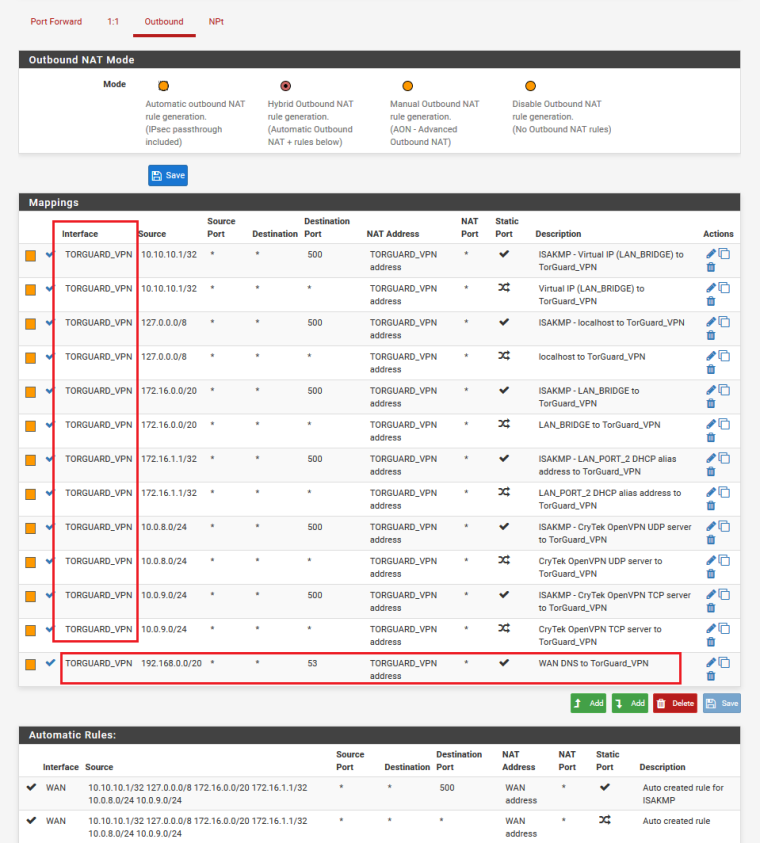
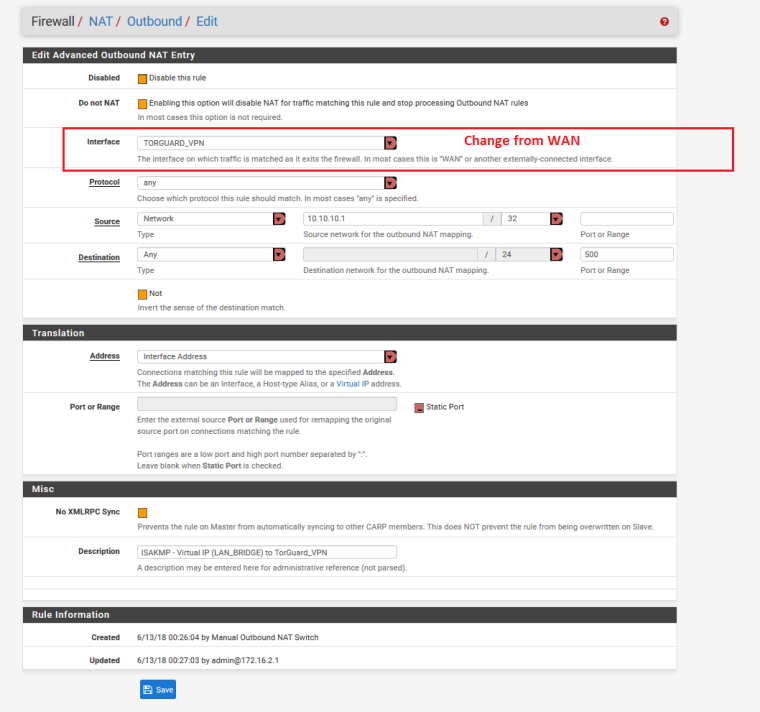
Here is a closer look at changing those WAN Manual rules to VPN manual rules
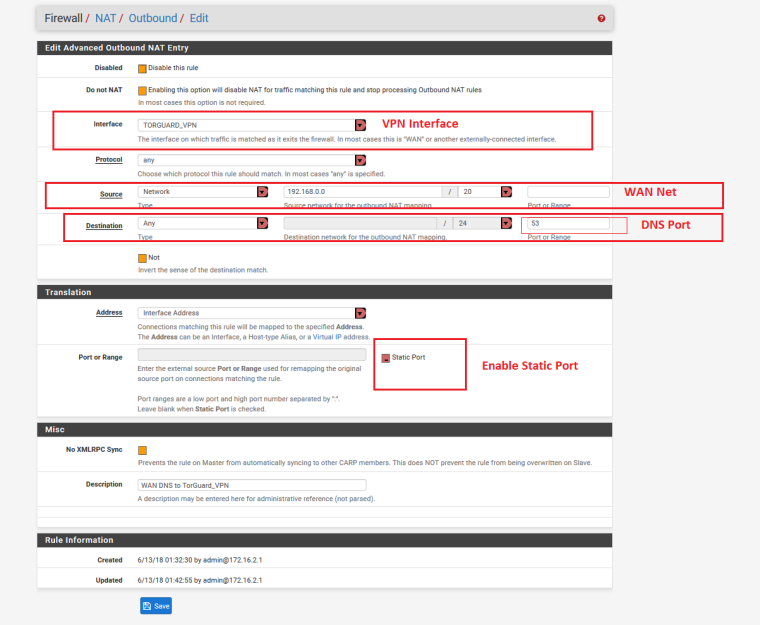
And here is a closer look at the DNS rule in the NAT outbound
If you have done the NAT outbound correctly.... now when you connect to your VPN service and it is active, your policy based rules will route traffic and dns requests to the VPN and route other traffic and DNS requests directly to the WAN and Unbound. AND we should have eliminated the DNS leaks when the VPN is active
-
Also for reference...
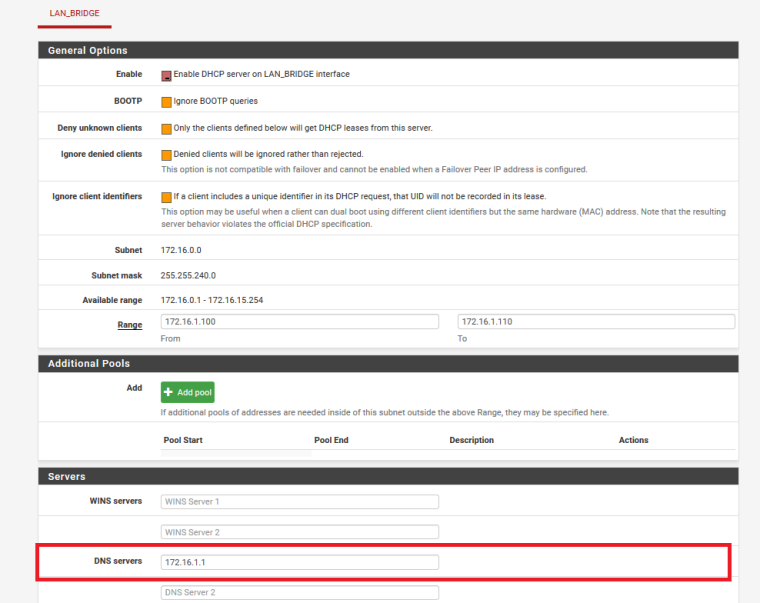
Here is my DHCP setup:
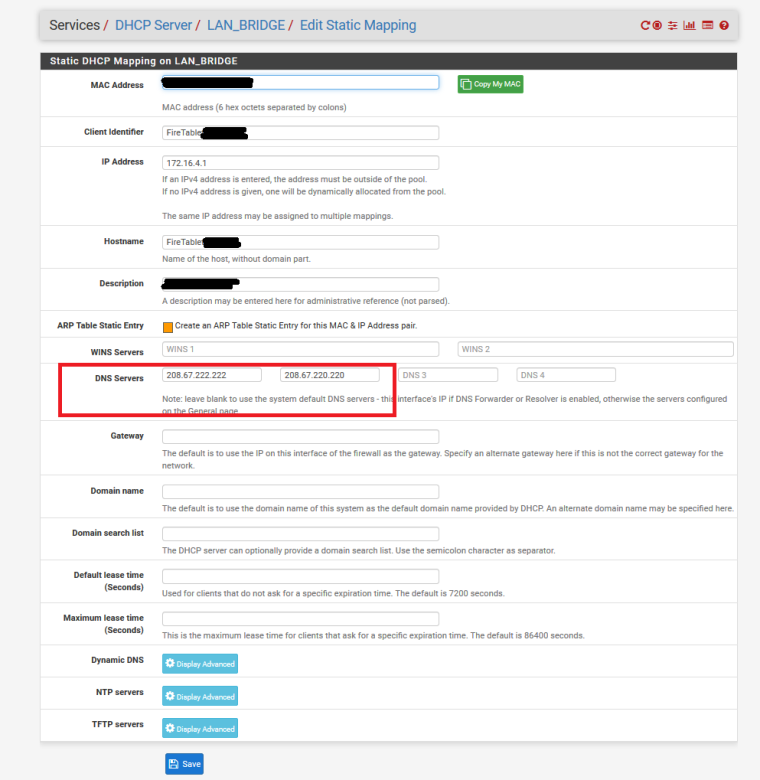
and then to have my Kids tablets use specific DNS servers and NOT use Unbound DNS Resolver.. I have a static mapping in the DHCP server for that device and that mapping specifies the DNS servers to be pushed to that device
-
another option might be to use Unbound DNS Resolver and DNS Forwarder (dnsmasq) at the same time
you'll need an NAT port forward rule:
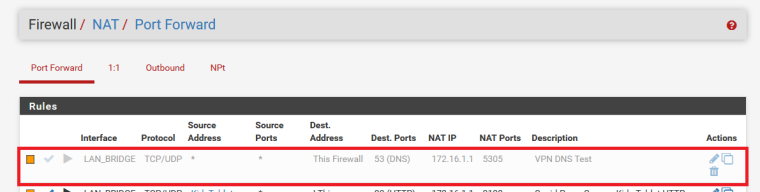
Closer look at that rule:
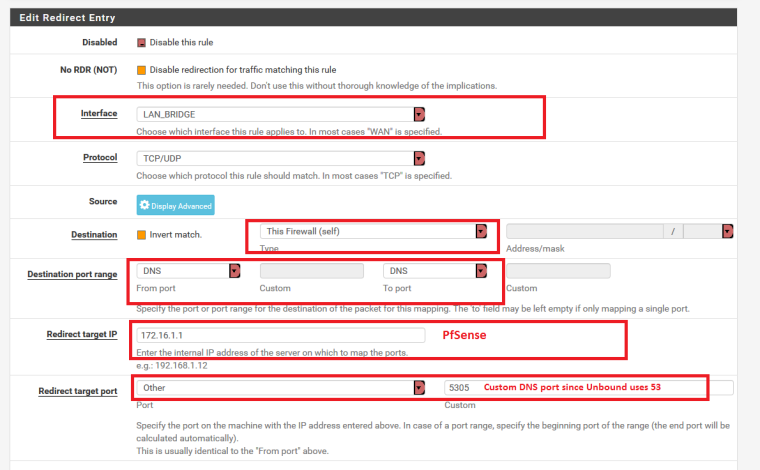
Go to General settings and specify DNS servers for the VPN:
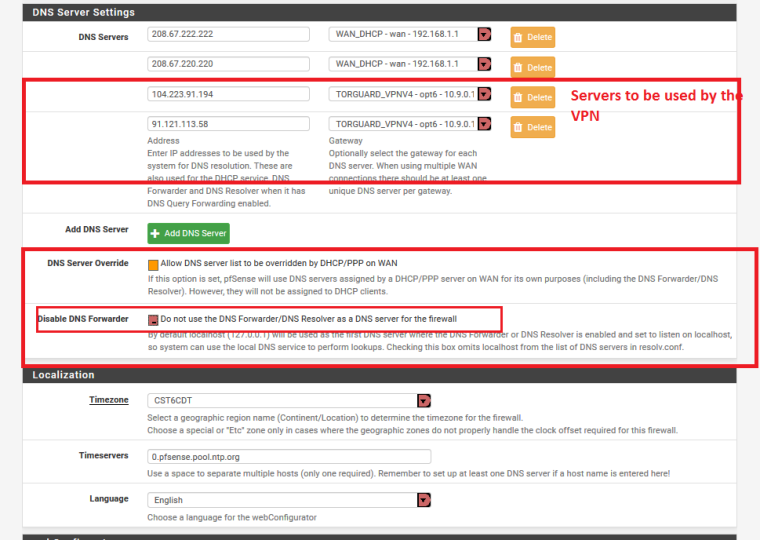
Then enable DNS FORWARDER (dnsmasq):
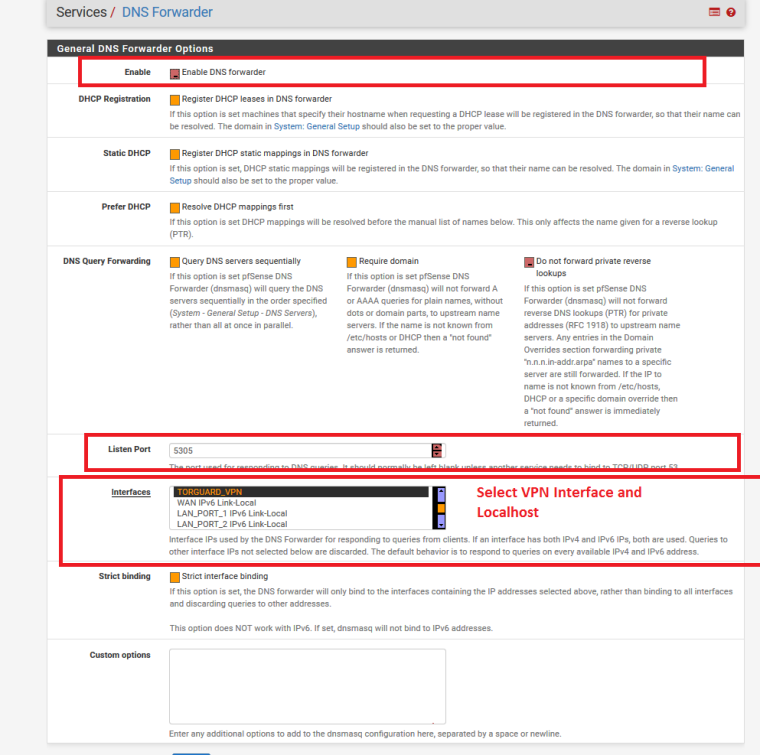
Using this method, the DNS queries for the VPN would be forwarded to the server specified in General Settings
but also using this method, when the VPN is down, DNS queries will still be sent to the server specified in General Settings all the time...and devices matching the policy would never use unbound...so you could adjust the port forward rule to suit your needs with aliases, so that some device use Unbound and others use DNSmasqI used to use this method....but am now using the first method I posted
(NOTE : If you use this method, you do NOT need the NAT>Outbound DNS mapping rule I mentioned earlier AND I THINK that in the VPN settings you MIGHT need to CHECK the "Do Not Pull Routes" option for this method to work) -
@teknikalcrysis
WOW - Thanks very much for taking the time to provide all this info!
I will certainly try this config but will need to back up what I have now just in case.
I don't have a router in between my modem and the PFSENSE box. Do you think it's necessary to set one up in there?
To confirm - the orange boxes in the screenshots are unchecked and the red ones with a dot are checked, correct?
Will let you know how it goes and thanks again for this great info. -
You shouldn't need a router in between, and yes checked boxes have the dot or line in the box and is more of a red color
-
@oxibquieh and no problem... Hopefully one of those methods works for your needs
-
If you have full vpn setup you should only see 2 wan states one for vpn connection and other for dpinger in the state table under diagnostics
-
@teknikalcrysis - Hi just to let you know I sent you a message over chat.
I hope that's OK.
Thanks,
OXIB. -
just to keep it open for all to see...
OXIBQUIEH said,
Hi Teknikalcrysis, I hadn’t replied about this as I hadn’t had time to try it but I have now and unfortunately, it did not work. There was connection using DNS unbound but unfortunately, DNS was leaking. I could not figure out how to fix it. I will try again with the DNS forwarder and Resolver tomorrow if I have some time available. Just a couple of questions: 1 - is the 172.16.1.1 in your screenshots, your PFSENSE router or another device in your network? Under network interfaces and outgoing network interfaces, is your VPN connection not selected?
On your Outbound screenshot - Why did you choose 192.168.0.0/20 for the WAN DNS to VPN? In my case - since I have all my devices from 192.168.1.100 to 192.168.1.160, could I use the 192.168.1.1/24 as source?
When I changed the mode on the rules from manual to Auto, then to manual again, and then to Hybrid, I was only able to auto-populate 8 rules. I changed everything to the VPN interface but nothing seemed to change.
Also under the general server setting for DNS, you mentioned to ignore the first two entries, I did specify or try to enter at least one of the DNS servers for my VPN provider but I was only wable to find one. Is this good enough or do you need two?
As I mentioned before, I will try again with the DNS Resolver and see if I am able to get it. I think in my case, this might work with those two working side by side.
Are you able to let me know the Alias you created for the DNS rule?
Thanks again
OXIB
Tteknikalcrysis said,
1)Yes 172.16.1.1 is my pfsense box
i will screenshot my oitgoing interface setup for you later today…3)on NAT outbound, the reason 192.168.1.1 is shown is because pfsense sits behind another router and the 192.* is the address of that router which is the pfsense WAN
after changing those outbound rules from WAN to the VPN interfaces, you need to add the NAT outbound rule for DNS on static port 53The portion that said ignore was to ignore thay IF you did the first method… But it is used in the second method… And yes one dns server address is fine, you do not NEED two… However, if that dns server goes down, you will fail to resolve since there is no second address… Using the first method tho, dns will not use the servers listed in general setup, it should tunnel the dns query through the vpn
On your vpn client setting… Have you made sure the “do not pull routes” option is UNChecked?
-
@OXIBQUIEH here ya go...sorry for the delay on getting you a screenshot
-
and were you referring to the NAT>Outbound DNS rule...or the NAT Port Forward redirect rule for using DNS Resolver and Forwarder simultaneously?
-
@teknikalcrysis - thanks for the reply and info.
I will try again this upcoming weekend. Hopefully I get it this time.
I am 100% sure that the do not pull routes option is unchecked under my VPN client settings. I will double check though.
i was referring to the both the NAT > Outbound DNS Rule and the NAT Port Forward redirect rule.