Unable to reach LAN IP after connecting to openvpn
-
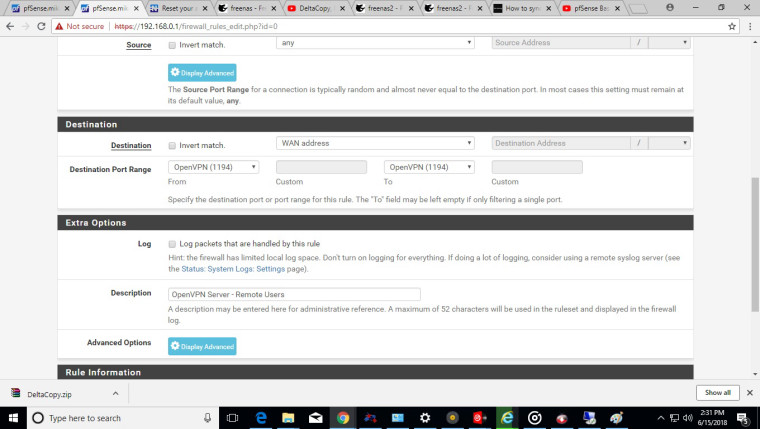
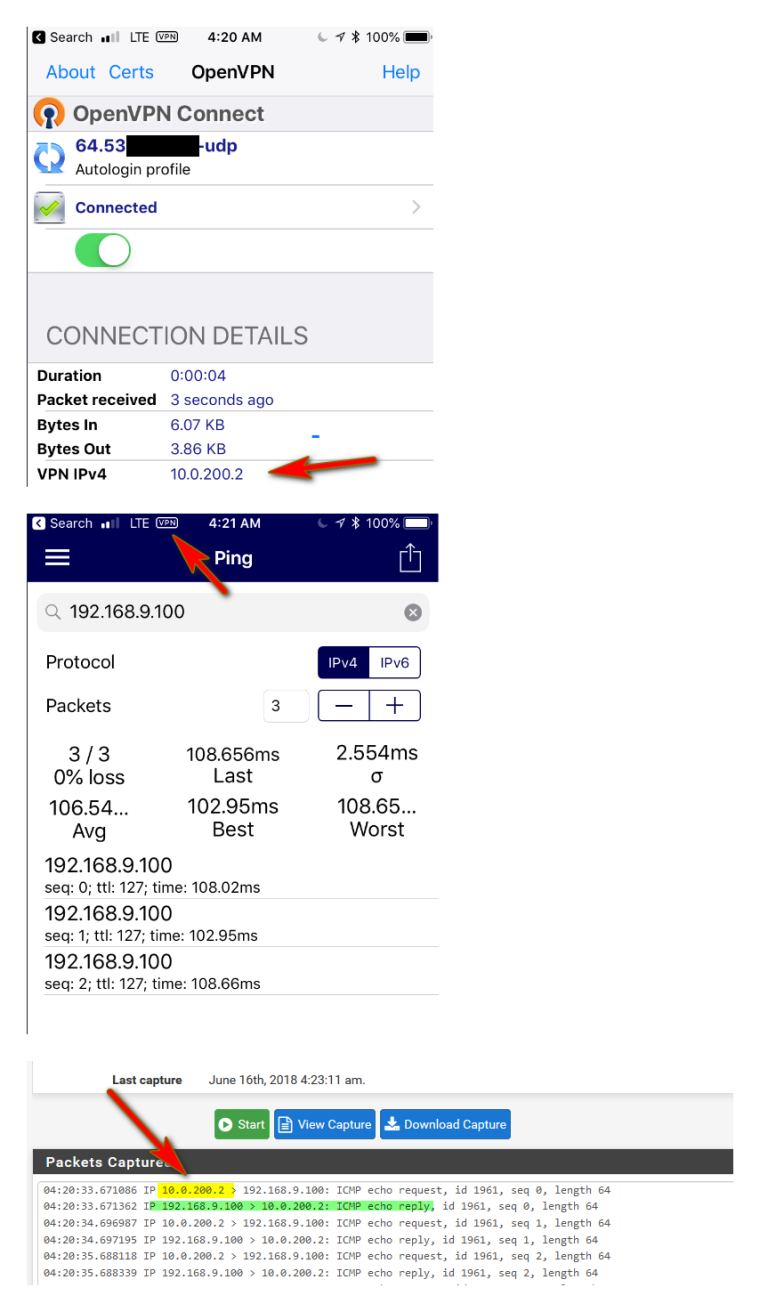
here is the Rules pics for the firewall for the openvpn -
@ayanbanerjee said in Unable to reach LAN IP after connecting to openvpn:
Fri Jun 15 22:54:07 2018 Warning: address 192.168.1.2 is not a network address in relation to netmask 255.255.255.0
That is not a network that is a host!!! network would be 192.168.1.0/24
-
you have 2 different people posting different issues. Its becoming a bit hard to follow..
One guy says he has no problem getting to the internet through the vpn, the other says he can't etc. Just because your both having issues getting to your lan behind pfsense does not mean they are related to why.
I wold suggest the 2nd guy start your own thread.
-
@comet424 Based on your screenshots, your outbound NAT only allows the specific IPs of 192.168.0.51 and 192.168.0.52 outbound to internet. Any other clients will not be NAT'd so they will not be route-able on the internet. You need to add outbound NAT for your VPN subnet. If you are receiving an IP of 192.168.100.2 on your phone than I am guessing your VPN subnet is 192.168.100.0/24. You should create a NAT rule for that network outbound. You will not need to select static port on that entry. As a side note, if you want the VPN to just give you access to things on your local network and don't need or want VPN access, you don't need the NAT entry but you need to make sure the box that says "Force all client generated traffic through the VPN" is unchecked in your VPN server settings.
Hope that helps.
-
@bloodlogic ah I not sure and I posted a new article as I didn't wanna tick off johnpoz and confuse everyone more the 192.168.0.50 is for the router nat.. the 51. is to try to get xbox one to work properly throught pfsense which didn't work... and I did the check all clinent generated track because I was told to try that for conflicts when I uncheck it it didn't help I was told like I thought if I use 192.168.0.x as my local network and I connect to a coffee shop that uses 192.168.0.x as there network if there would be a conflict.. I tried both ways check and uncheck no difference once I connect to vpn I loose all internet connection and no longer can ping expect the virtual IP for the cell
-
@johnpoz Ok but could you please check the line stating regarding route addition failed
-
Dude you can not had a host address as a route.
-
@johnpoz thanks.. I was done some mistake on configurations.. but the ping issue still not solved.
-
@johnpoz Hi some more inputs from my side ,
after vpn connection people from LAN able to ping my vpn ip, so its look like its working in one way. by any chance is there anything I need to do in firewall side ?Please help.
-
THE HOST FIREWALL!!! ie the client on the lan side your trying to ping, its software firewall... Went over this way back in the thread..
Windows out of the box is not going to let some IP (tunnel network your remote guy got from vpn) ping it..
-
@johnpoz I have disabled all the Windows firewall but no luck
-
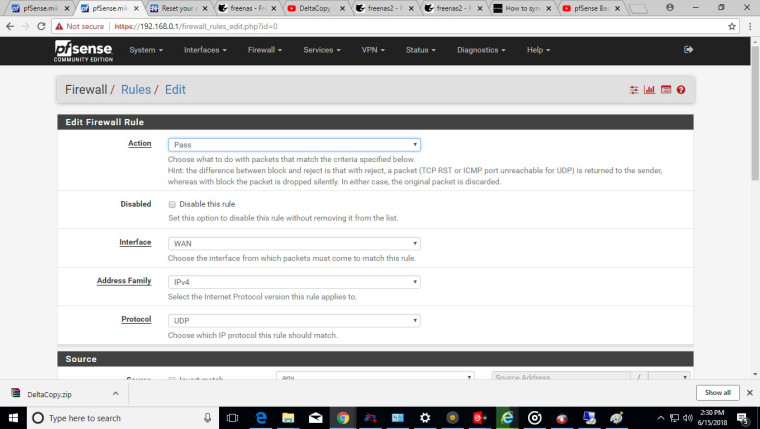
If you can ping your lan IP of pfsense, then your going down the tunnel.. Then that means you can get to the lan network... So sniff on the lan interface while you ping some lan client from your vpn... Do you see it send ping go towards the client. Do you see a response..
Here is example from my phone pinging my 192.168.1.100 box..
-
did you mess with openvpn firewall rules.. The wizard will create a any any rule.. Did you delete this - not use the wizard? Modify it?
-
@johnpoz the rule is there, i have used the wizard.
look like problem is different, all the clients are getting same ip after connecting vpn :(
-
Are you connecting multiple clients at the time? Multiple clients connected at the same time would not get the same IP. But yes client A connects, then disconnections and client B connects then sure it could get the same IP that A had before.
What does that have to do with pinging inbound to something on the lan?
-
@johnpoz Yes I am connecting multiple client in same time and getting single ip for all the client, I think if we solve this issue we will be able to solve the ping issue as well.
-
Are clients as using the same creds/certs access?
Did you setup some client override following some previous guide that you did not remove?
-
@johnpoz Yes right you are i am using the same access and cert for 2 number of vpn connection.
-
@johnpoz Thanks for the pointing out the user access thing.. now ip is different for the different users.. please please help me on the ping issue please :)
-
So your client can ping the pfsense lan IP - right?
If so then the tunnel is there and your client is going down the tunnel. Then again this screams firewall on the host your trying to ping on the lan, or the device not having a gateway or pointing to different gateway that pfsense, or having a route that says your tunnel network uses a different gateway.
Please sniff on your lan interface while you ping one of your lan IPs.. Like I showed in my example.