DNSBL modify default bloked webpage
-
Hi, is there any way to edit the DNSBL default 1x1px blocked page into a decent text like: "The page you are attempting to access has been deemed inappropriate"?
-
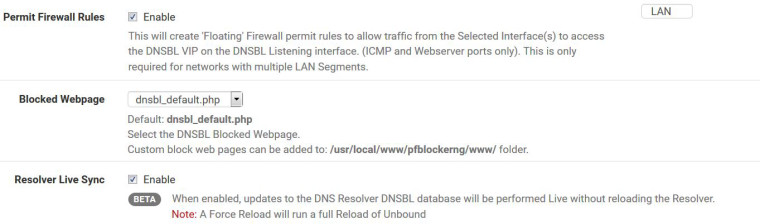
Install pfBlockerNG-devel which has a default block page when the root domain in blocked, otherwise it will still use the 1x1 for all other AD type blocks. The page can also be copy/paste and edited as required and associated in the DNSBL Tab options.
-
Thank you Mr. BBcan177.
Do ihave to uninstall the pfBlockerNG package and replace it with pfBlockerNG-devel? I thought its as simple as editing an html file in dnsbl directory. -
@rjabellax5 said in DNSBL modify default bloked webpage:
Do ihave to uninstall the pfBlockerNG package and replace it with pfBlockerNG-devel?
Yes you have to uninstall first.
Also, The pfBlockerNG-devel under 2.4.4 has issues with PHP, so 2.4.3 max.
@rjabellax5 said in DNSBL modify default bloked webpage:
I thought its as simple as editing an html file in dnsbl directory.
It is : Custom block web pages can be added to: /usr/local/www/pfblockerng/www/ folder.
-
Thank you Mr. RonpfS.
How am i going to do that? do I have to create a new html file for my custom blocked page? or jus edit one of this .php files?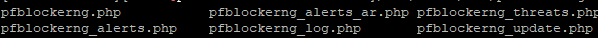
-
or this file ?

-
@rjabellax5 said in DNSBL modify default bloked webpage:
How am i going to do that? do I have to create a new html file for my custom blocked page? or jus edit one of this .php files?
-
@ronpfs Thank you. Sorry I didnt get that quickly.
Removed PFBlockerNG and installed devel version, i can now see the blocked webpage option.
again, thank you.
-
Did you ever manage to enable this option and create a page? Just curious, I'd also like to have.
Actually what I would like is a basic error page that told me "Blocked by pfBlockerNG using thisparticularfeed" -
@occamsrazor
You can copy the default file and modify it to your taste.
Or create you own html file. -
I found and downloaded the default page in /usr/local/www/pfblockerng/www/
What I'm realising now is I am never seeing this default block page at all (this was same for me pre -devel version), I just get a timeout.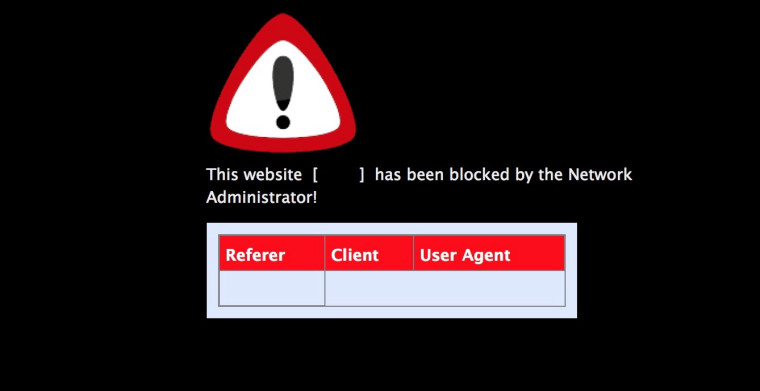
A ping from client machine to the blocked address confirms it is being redirected to 10.10.10.1
-
@occamsrazor That a page you get when you access a blocked domain name directly : http://js.agkn.com
In case of an image URL you get a 1x1gif page, for a .js you get another page, etc -
@ronpfs said in DNSBL modify default bloked webpage:
@occamsrazor That a page you get when you access a blocked domain name directly : http://js.agkn.com
In case of an image URL you get a 1x1gif page, for a .js you get another page, etcWhen I ping that address it's clearly being blocked
ping js.agkn.com
PING js.agkn.com (10.10.10.1): 56 data bytesBut when I try to access the example you gave http://js.agkn.com in a web browser no page ever loads, just a timeout.
-
@occamsrazor said in DNSBL modify default bloked webpage:
But when I try to access the example you gave http://js.agkn.com in a web browser no page ever loads, just a timeout.
Do you get something from http://10.10.10.1/
-
@ronpfs said in DNSBL modify default bloked webpage:
Do you get something from http://10.10.10.1/
No, just a "Waiting for......" in the bottom of the browser screen and page never loads.
-
@occamsrazor Under Firewall / NAT / Port Forward You should have NAT entries pointing to the VIP.
Did you enable Permit Firewall Rules under Firewall / pfBlockerNG / DNSBL ? Do you see those Rules under Firewall / Rules
-
@ronpfs said in DNSBL modify default bloked webpage:
@occamsrazor Under Firewall / NAT / Port Forward You should have NAT entries pointing to the VIP.
Did you enable Permit Firewall Rules under Firewall / pfBlockerNG / DNSBL ? Do you see those Rules under Firewall / Rules
That check box was not enabled. I've enabled it now, restarted router and client machine, and see the rules under Floating:
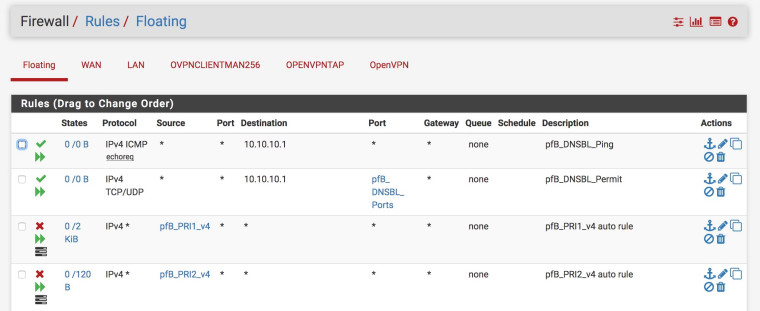
But still don't get any response from http://10.10.10.1/ or that domain you posted.
-
Aha... I notice the pfB_DNSBL_Ports alias refers to ports 8081 and 8043 only. When I type http://10.10.10.1:8081/ in the browser I get a response:

But even if I manually add port 80 to the pfB_DNSBL_Ports alias it doesn't give me that page when going to http://10.10.10.1
-
@occamsrazor The NAT should take care of redirecting port 80 and 443.
-
@ronpfs said in DNSBL modify default bloked webpage:
@occamsrazor The NAT should take care of redirecting port 80 and 443.
I see a corresponding port-forward in Firewall > NAT Port > Forward but it doesn't seem to be working:
