Can connect to OpenVPN Server but loose access
-
hi i have OpenVPN Server running on the pfsense for remote access got the certs and rules setup
when i connect with my cell phone from the network or from a remote location OpenVPN Client connects i get the green light.. but then i loose all internet.. what would normally cause that???
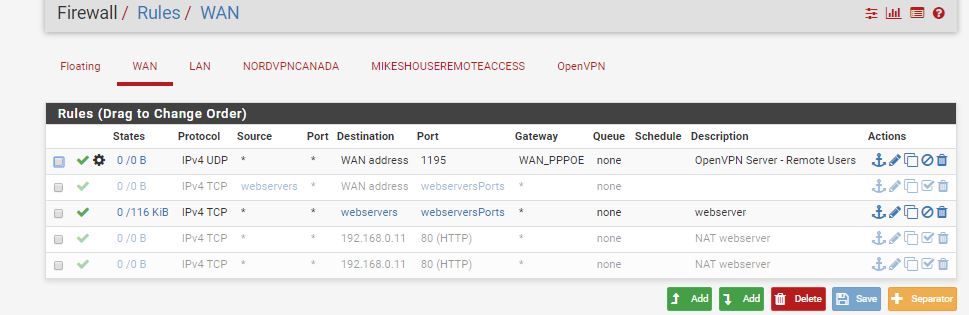
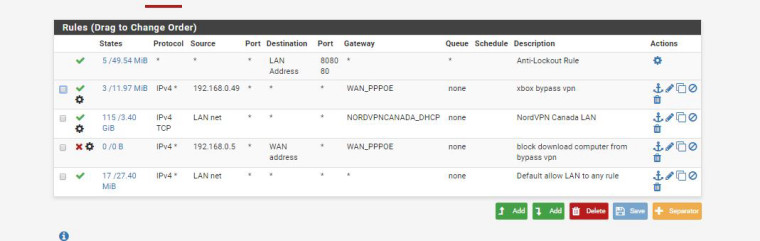
here is the rule i set
 .. let me know any other pics needed
.. let me know any other pics needed -
Why in the world would you have a gateway setup on your wan rule? Makes ZERO sense.
-
well i followed the Pfsense Tutorial from Cross Talk
https://www.youtube.com/watch?v=Q6YbCQEiC3cand im guessing its because its for incomming connections from the Wan port.
im guessing thats the reason?
why where should it be under LAN? i can copy it and make it to lan -
If they told you to put a gateway on your wan rule then their instructions are completely BORKED!! You would never do such a thing.. Nor would you put it on your lan rules..
I just skimmed through that video - they don't show putting a gateway on the wan rule.

-
ok so where would you put the port 1195 rule then in nat? or would i put it under the remoteaccess heading then?
-
Your 1195 port is setup on the server, and you have to allow that on your WAN - you just would not set a gateway on the rule!
15 min to setup a vpn server... My gawd these people love to hear themselves go on an on... Should be like 3 minute video ;)
-
8:40 seconds they choose the WAN setting and put the 1195 on the wan rule
not sure what you mean i wouldnt set a gateway on the rule
-
Here this is wrong
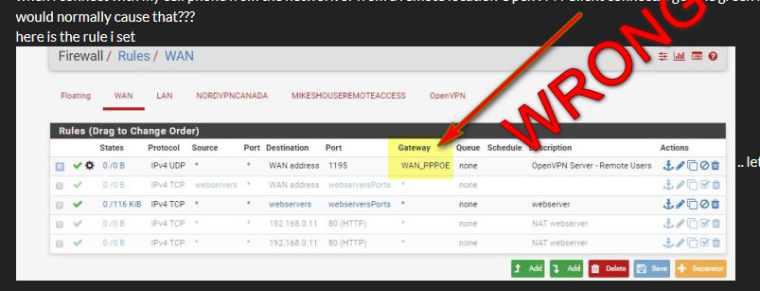
-
if you mean instead of a * for gateway and where i have it set for WAN_PPOPE
i dont want it going through the VPN service i just want it to bypass the vpn connection so its not double encrypted and slow down my connection more? if thats what you meanas i have some computers on VPN and some things bypassed the VPN and i figure setting it the WAN_PPOE that when i connect with my cell it goes to the WAN interface and not my nordvpn interface..
-
If you want to policy route clients on your lan side networks to use vpn or normal gateway you would do that on the lan side rules, NOT on the wan rule allowing access to your vpn server from the outside world
-
ah i not sure.. what i need?
im just the only user its my home network.. i wanna be able to connect when im not at home to my pfsense to access my local network
and i figured i need to set it to wanppoe as then it wouldnt use nordvpn..
as i figured the default gateway now is the nordvpn as thats how its set up on the lan side.. but ill change it back to *i figured since you can set which gateway id set it to the one that bypass's the nordvpn service... thanks for the help so far
i guess the only time ud change that is if you had 2 wan ports maybe?
-
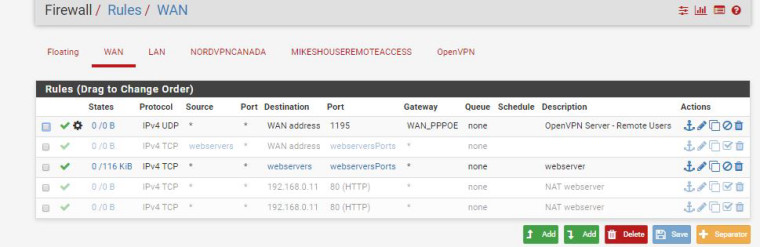
ok i set it back to * what else do i check as it still doesnt work
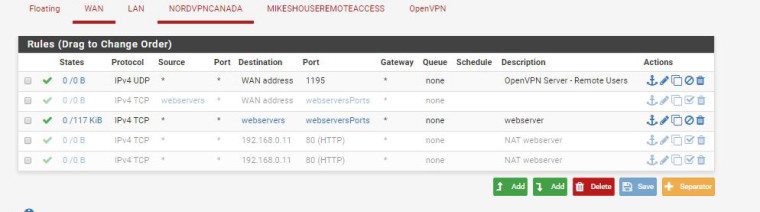
-
here my lan rules
-
Well your forcing all your lan net clients out your nordvpn connection, so how would they get to your vpn clients..
You need a rule above that that lets dest to your tunnel network (your vpn clients IPs) to use normal routing so pfsense can send the traffic back out the vpn connection.
-
well how i thought it was. was the computers on the local network when they want internet they would be forced to use the vpn service
but if im away from home when i access my network it bypassthe vpn service
so how would that rule look like im guessing it goes in the LAN section just above the nordvvpn canada lan and under the xbox bypass vpn
always learning i appreciate the help so far
-
would it look like this
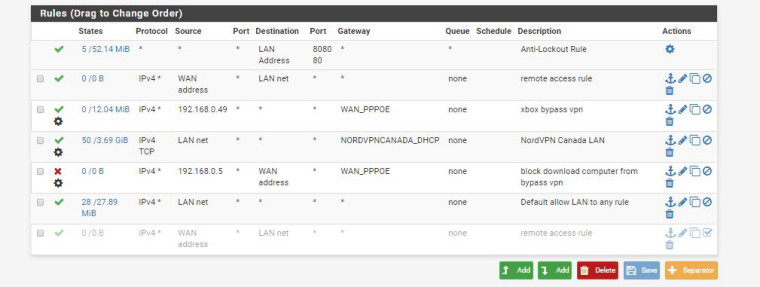
source is coming from the wan address to the lan ips -
What is you want exactly? If you want to get to your lan clients then you would need a rule above where you force them out your nordvpn to get to your tunnel network.
Also that 3rd rule makes zero sense as well.. If your blocking 192.168.0.5 from talking to your wan address - why would it have a gateway??
I think you need to take a look at the pfsense book that is available about policy routing.
-
NO it would not look like that... When would wan address ever be a source into your lan interface.. I think there is a disconnect on how rules are evaluated..
-
i want all my computers on my home network to go out the NordVPN when im at home
when im say at a friends house i wanna connect to my home network access all my computers and not go through the NordVPN by pass it.. as that be double vpn and then my internet be even slower would it not???
the 3rd line is for my downloading computer.. so when the NordVPN stops working that downloading computer can not use regular internet.. it forces that it can not use the wan_ppoe gateway ever... as if you disable nordvpn client on pfsense the downloading computer keeps downloading.. and i wanted a kill switch so if nordvpn goes down so does the downloading computer
well then i not sure how to do it then i need pictures
welll if the wan address source is never to be used under lan why is it an option
i thought its so for any WaN incomming WAN side connections it goes directly to the LAN address's
then i lost
-
Well your 3rd rule doesn't do what you think it does... downloading stuff from the internet is not dest of your wan address.. All that is whatever your wan address is.
What is your tunnel network? If its 10.0.8/24 for example then create a rule above your nord policy route that says if dest 10.0.8 NO gateway set.
When you vpn in, if you have your vpn clients set to use vpn ad def gateway - ie route all traffic then it would use your normal connection and not your nordvpn. As long as your actually policy routing that and not pulling routes from the connection so your default route is nord..