connected but cant access vpn lan after upgrade to 2.4.4 p1
-
Hi
I just upgraded my sg-3100 and 2 sg-1000 to the latest 2.4.4 p1
before this upgrade everything works perfectly. i did NOT change any settings at all, simply pushed upgrade!
my sg-3100 is the main openvpn server
lan ip 192.168.1.1
tunnel (site to site) 10.0.1.0/24
the first sg-1000 still works and connects perfectly.
lan ip 192.168.2.1
tunnel (site to site) 10.0.2.0/24
the second sg-1000
lan ip 192.168.3.1
tunnel (site to site) 10.0.3.0/24
stopped connecting to the main server sg-3000, from it i can ping the main server but from the main server i cant ping back to this sg-1000my brother in law did the exact same upgrade process and he is having he exact same issue. he has the exact same setup as i do.
please help (my phones are using the vpn connection)
-
@ariban99 Please post vpn server config.
Screenshot.
There are small differences on how (mis)configuration is interpreted after upgrade -
Hi
thank you for your response.
here are the screenshots
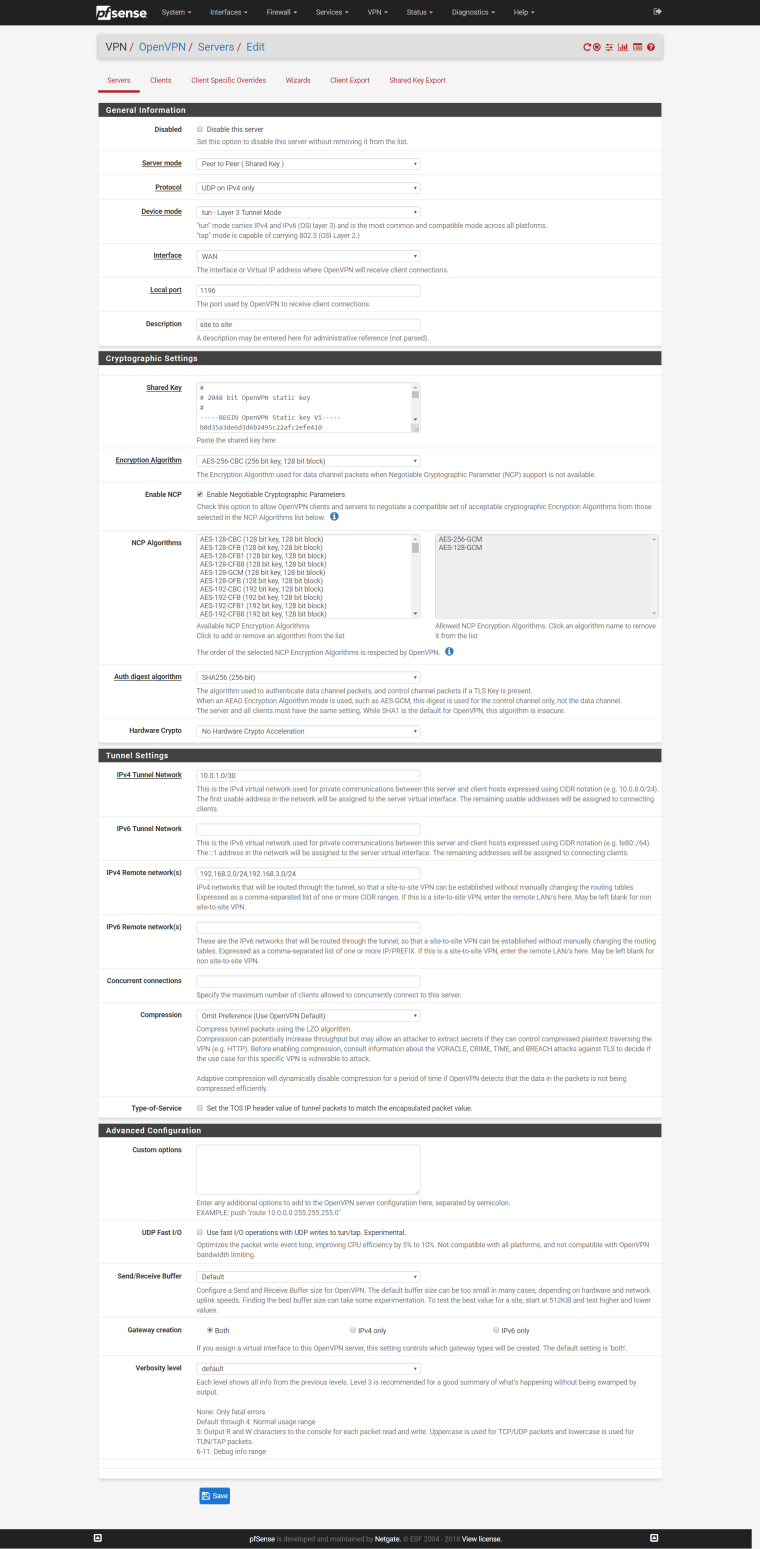
server for 10.0.1.0 (WORKING ONE)
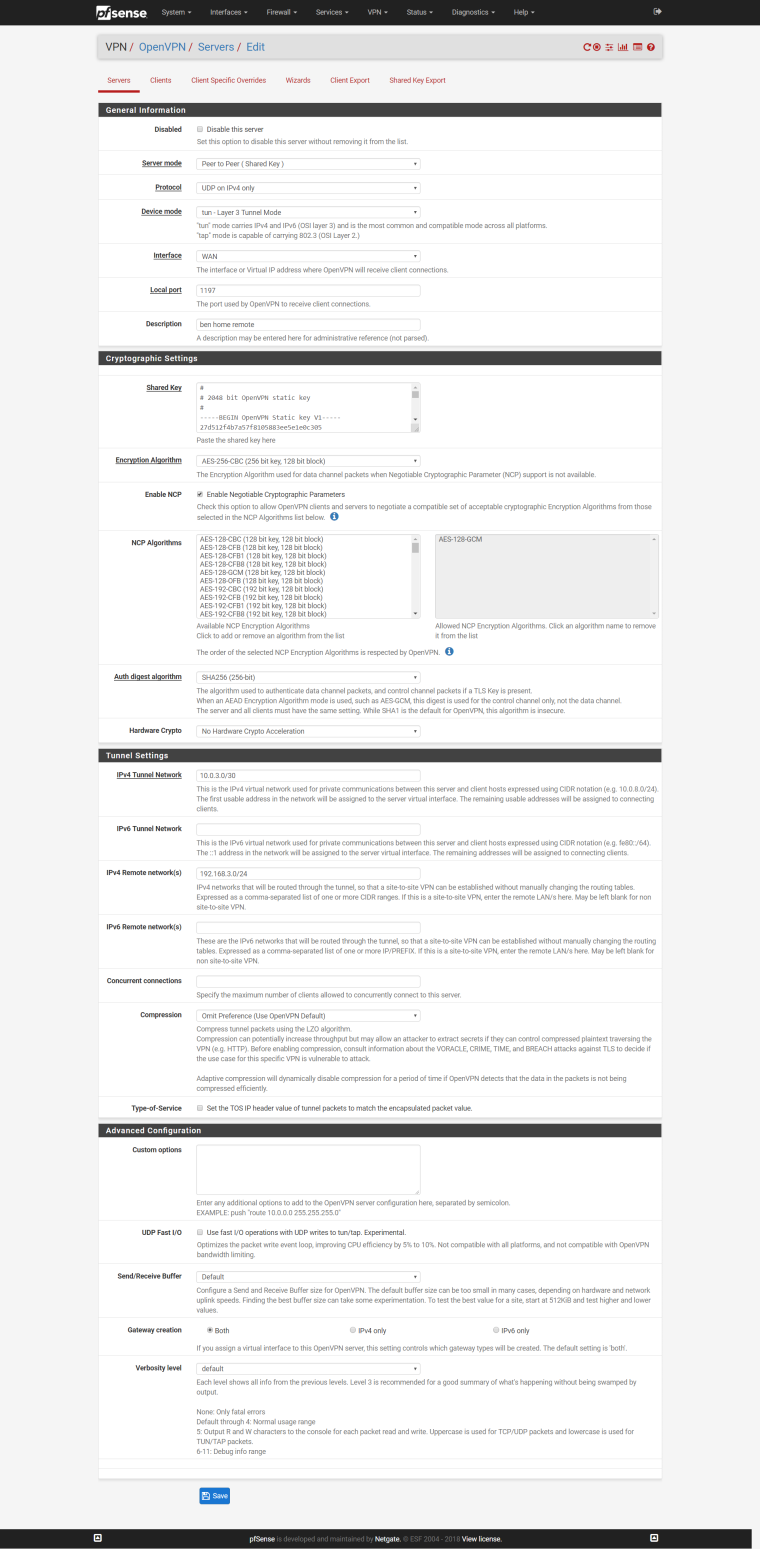
here is the server for 10.0.3.0 (NOT WORKING ANYMORE)
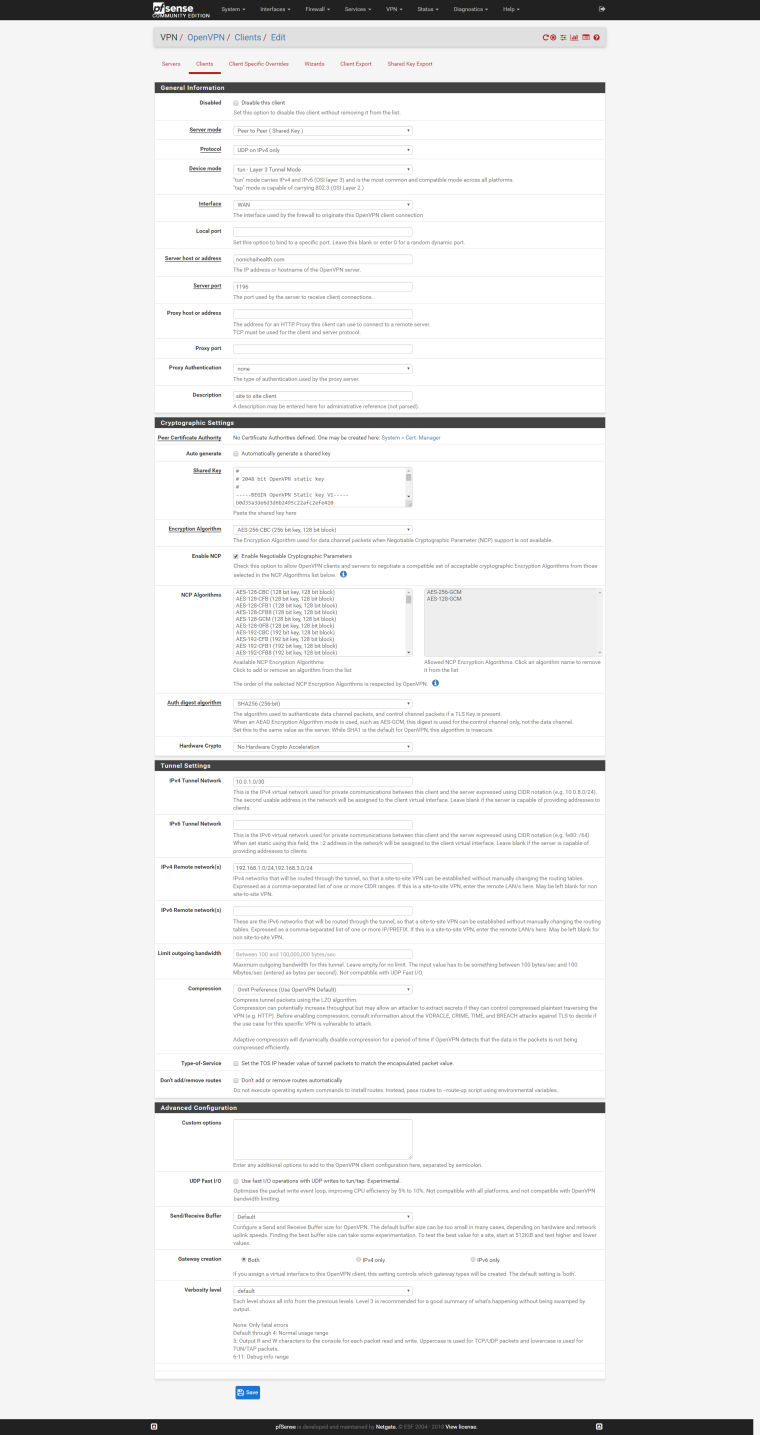
here is the client side for the working one 10.0.1.0
-
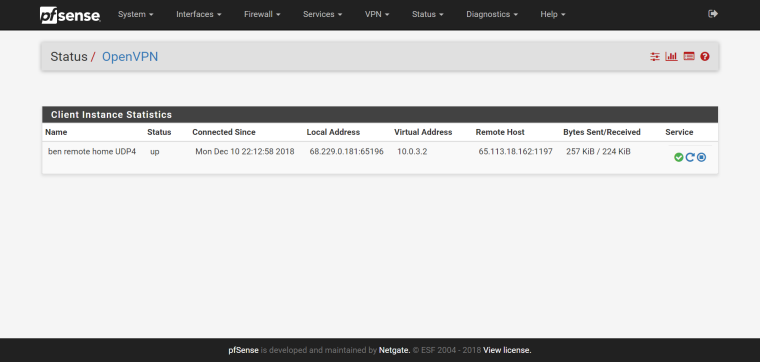
this one shows the status of the openvpn that is NOT working, it shows connected and UP
-
and here is the client side for the one NOT working 10.0.3.0/24
link text
somehow i cant upload this screenshot, every time it gives me an error, so i uploaded it to my google drive as a screenshot
thank you -
@ariban99 try removing 192.168.3
.0 from remote networks on the working config.
Remember to clear states and restart openvpn. -
Hi
thank you. that works now.
however, now i can not access between the 2 remote locations. so from each remote i can access the main server. but between remote locations, i cant access each other.
is there a way to talk to the 2 remote locations. so in this example
from 192.168.3.0 (tunnel 10.0.3.0)
to 192.168.2.0 (tunnel 10.0.1.0)thank you
-
Assign ovpn interfaces ( if you havent done already) and policy route among the two is probably the way to go.
Put roules on openvpn tab sending traffic with specific source and destination to relevant openvpn interfaces respectively.
It should work -
hi
so i am lost, how do i do all the above? sorry i dont know this stuff very well.
any tutorials to follow? -
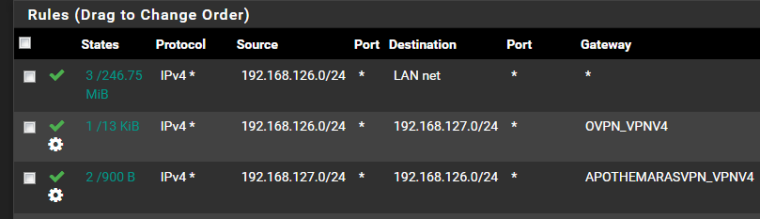
Here is an example.
There are two tunnels 192.168.126.0/24 and 192.168.127.0/24 with two interfaces
One rule specifies source 192.168.126.0/24 target 192.168.127.0/24 and send packets to 192.168.127.0 assigned gateway.
a second rule does the opposite
All this under firewall rules openvpn. -
i will try that, thank you for all your help
-
Tunnel addresses are usually in the same subnet..
-
so i dont think i am doing it correctly.
i assigned OPT1 and OPT2 for the openvpn
so OPT1 is for 192.168.2.0
and OPT2 is for 192.168.3.0then enabled them.
under rules, OPENVPN tab.
i create a new rule.
interface, WAN
IPV4
ANY
source, i selected OPT1
destination OPT2and i did the reverse for the second openvpn but its still not working.
what am i doing wrong? -
Your "Tunnel" networks.. put both sides of the VPN tunnel in the same subnet.
tunnel 10.0.3.0/30 When you do this each box will take an address in this subnet.
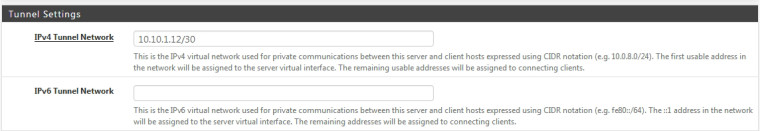
-
@chpalmer
On your second VPN tunnel use a different subnet.. -
I never assign my own OpenVPN sessions to an interface on the box. So you might be seeing another issue that I wouldn't see but the information above is correct either way. IP Tunnel network on each side should be in the same subnet.
Remote network is the network(s) of the box on the other side.
-
@ariban99 said in connected but cant access vpn lan after upgrade to 2.4.4 p1:
so i dont think i am doing it correctly.
i assigned OPT1 and OPT2 for the openvpn
so OPT1 is for 192.168.2.0
and OPT2 is for 192.168.3.0You do not number OpenVPN assigned interfaces. You simply assign them then enable them then bounce that OpenVPN instance. You do not specifically number them in the interface configuration. Might be misunderstanding what you're doing but that's what I read.
-
Just assign interfaces to openvpn tunnels.
DON'T put ip's there, it will happen automaticaly by openvpn. -
@netblues said in connected but cant access vpn lan after upgrade to 2.4.4 p1:
Just assign interfaces to openvpn tunnels.
DON'T put ip's there,Just like Derelict said..
What does assigning tunnels to interfaces get over just building the tunnel on the router and not assigning them to interfaces? Just curious..
-
@chpalmer said in connected but cant access vpn lan after upgrade to 2.4.4 p1:
Just assign interfaces to openvpn tunnels.
DON'T put ip's there,It creates the interfaces so you can policy route, add rules, monitor traffic, etc...