active directory domain trust
-
guys,
Am not sure if i am in the right subforum, but has anyone ever created, in a lab, a trust-relationship from Active Dir Domain 1 to 2(and back) when using pfsense as a firewall? I am trying that, but i dont get it fixed. Even ping doesnt work from router 1 to 2(and vs)
hope someone can help, thanks..
-
Well if you can not get connectivity working - simple ping... How would you think your going to get anything else to work?
Domain trust through a firewall, no matter what firewall is as simple as opening up the required ports. MS has articles on it..
https://support.microsoft.com/en-us/help/179442/how-to-configure-a-firewall-for-domains-and-trusts
How to configure a firewall for Active Directory domains and trustsSo yes pfsense can do it without any problems.. You need to figure out why you can not even ping would be step 1..
With the zero amount of info given, its impossible for anyone to even suggest what you might be doing wrong to be honest.
-
many thanks for the reply. can you provide me with the necessary info needed? The installation of Pfsense is out of the box although i did add a rule in the firewall part to allow icmp traffic.
-
You added a rule to allow icmp from where to where? No I can not provide you help without SOMETHING to work with!!
-
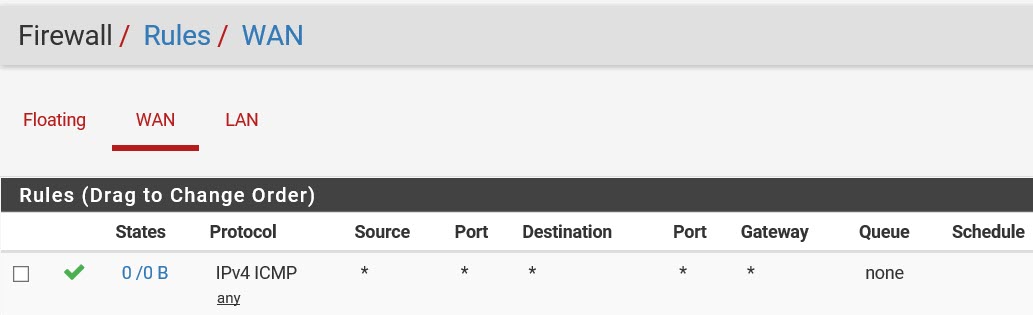
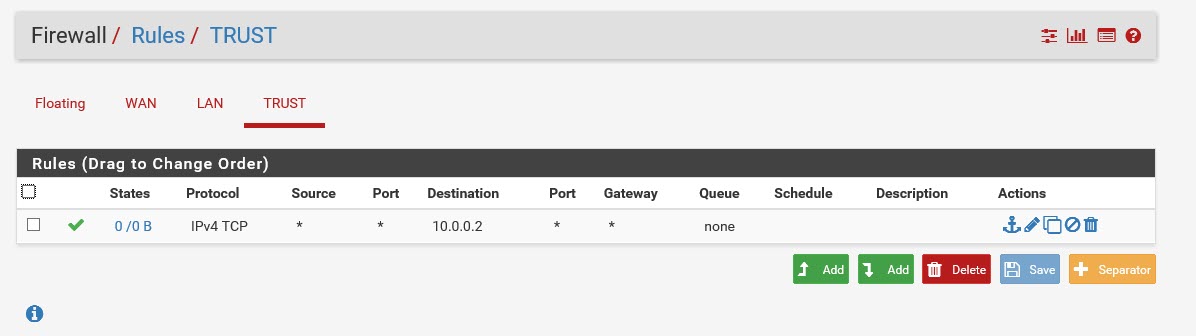
i tried this
-
Yeah so that would allow ping to your WAN IP from stuff out on the wan or internet.. Where exactly are you trying to ping that.. And the rule is not really good anyway... Dest should actually be your wan address.
Is your wan address public? or are you behind a nat?
Again - your going to actually have to provide some details if you want any help!
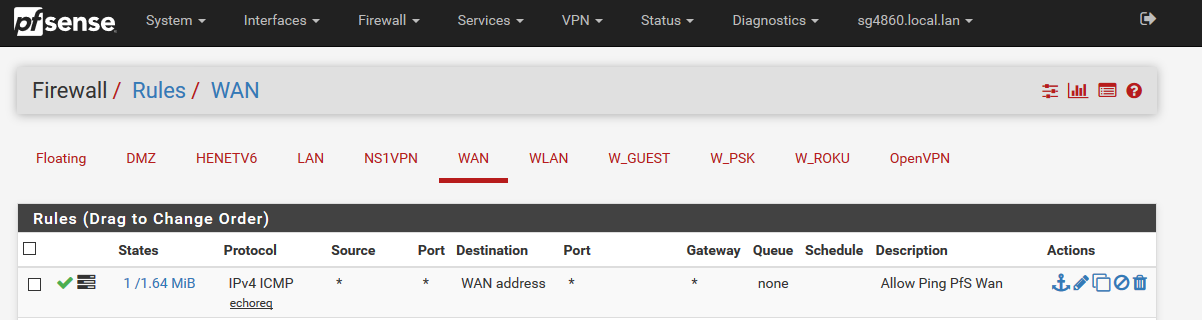
Test it from outside - here is site you could test ping from.
https://tools.keycdn.com/ping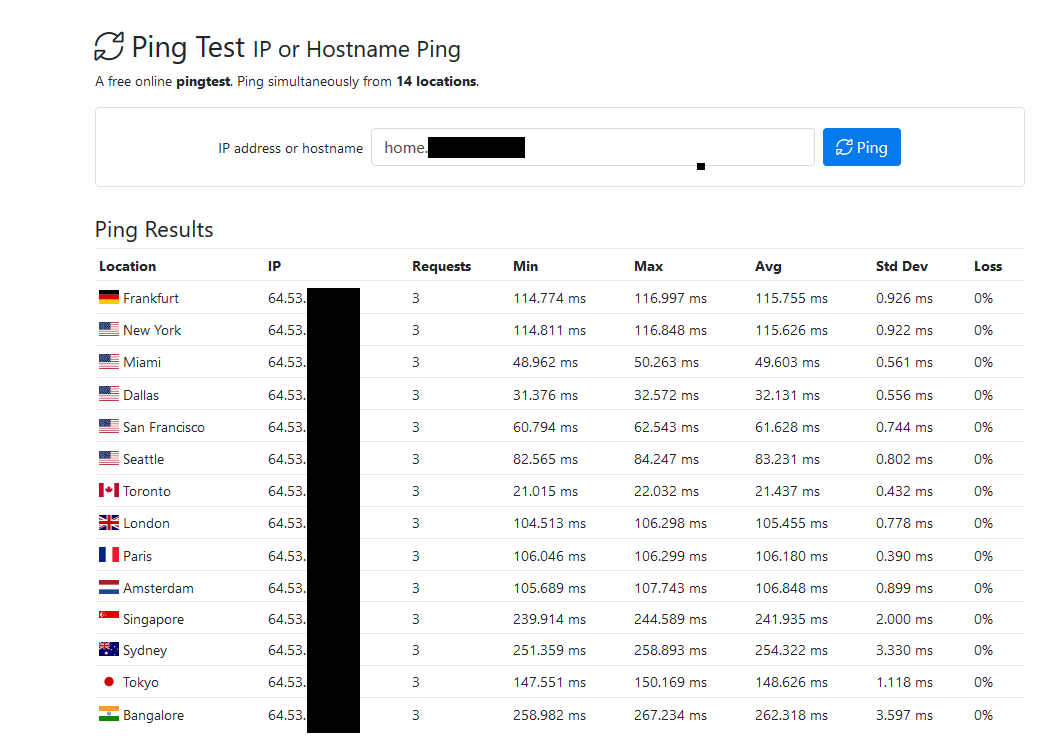
That is using a fqdn that resolves to my public IP, you can see my public IP which is pfsense WAN ip in that test 64.53.x.x
-
hi, it is in a lab environment, not available from outside. I am just trying to figure out how to get a trustrelationship working when there are routers with different ip-ranges in the game. Noticed all the tutorials i found at Youtube or at blogs, dont explain that and use the same ip-ranges for their DC's. Heck, most of them dont even use a router.
-
Well you have some sort of connectivity issue if something on the wan network of pfsense can not ping the wan IP if you allow for that on the wan..
I gave you the link to ports required for trust with MS..
But your going to have more fun with that and NAT... which I would NOT suggest... So your different networks should not nat between them.
So you should have say 2 networks
192.168.1.0/24 pfsense lan
And then an OPT network say
192.168.2.0/24 where the other domain and its DC sit. -
It is correct that one shouldnt use NAT for a trust relation, read that earlier this day.
So i should add at my pfsense router at both sites a dedicated NIC with an ip in the same range so the clients can connect?
I was thinking about the WAN for connection to the internet, the Lan for the internal network and the OPT for connecting both pfsense together.Or should i create a site to site vpn link and after that the AD trust?
-
Your not going to be able or want to run a AD trust over the public internet.. So yeah a vpn would be the way to go.
But for your "lab" just put 2 lan side networks connected to your pfsense for testing. Or sure you could use vpn tunnel between your lab pfsenses.
DC_domainA --192.168.1/24-- lan (pfsense) wan --- vpn tunnel --- wan (pfsense) lan --192.168.2/24-- DC_DomainB
-
i am stills tuck at the connecting part, tried the following but still i cant get them connected.
 image url)
image url)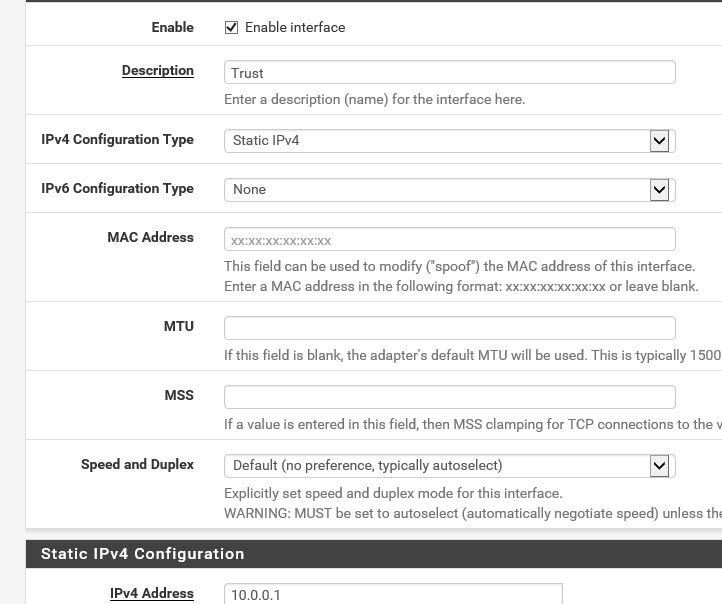
-
So you created a new network? on pfsense
And what rules did you put on it? You didn't set a gateway on it did? so you have
lan 192.168.1.0/24
trust 10.0.0.0/24?
And you have a box in 192.168.1/24 say 192.168.1.100 and using pfsense as its gateway? which is what 192.168.1.1
Can this .100 box ping 10.0.0.1?
Rules on lan would default to any any... Where are you creating this "tcp" rule exactly? On the trust interface??? And who is 10.0.0.2?
Rules are evaluated as traffic enters an interface from the network its connected too, top down, first rule to trigger wins, no other rules are evaluated..
How about you draw up your testing setup!!
192.168.1/24 -- lan (pfsense) trust -- 10.0.0/24
??
And post up your rules for lan and trust
-
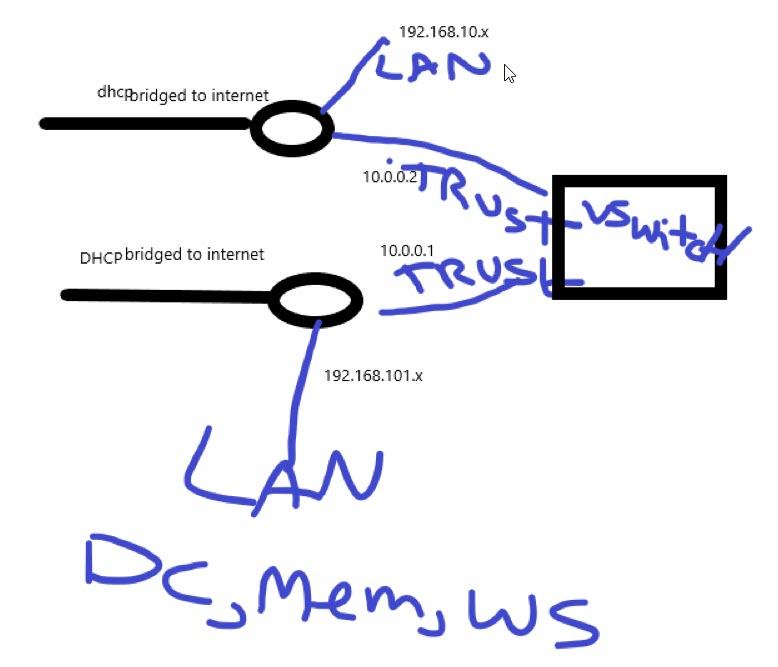
Hope this 3Dpaint picture makes some sense, whas thinking about Visio or packetracer but it is easier sometimes do draw in paint
-
-
vswitch? So this is vm pfsense setup?
Sorry but no that drawing doesn't make a lot of sense... where exactly is pfsense in that drawing, and why do you have 2 different bridged to internet connections?
I don't mind a paint or napkin drawing but its hard to make heads of tails of that nonsense.
If trust network is 10.0.0/24 - then rule to get to 10.0.0.2 is WORTHLESS!! a box on 10.0.0/24 wouldn't talk to pfsense trust IP to get to something on the 10.0.0/24 network.
-
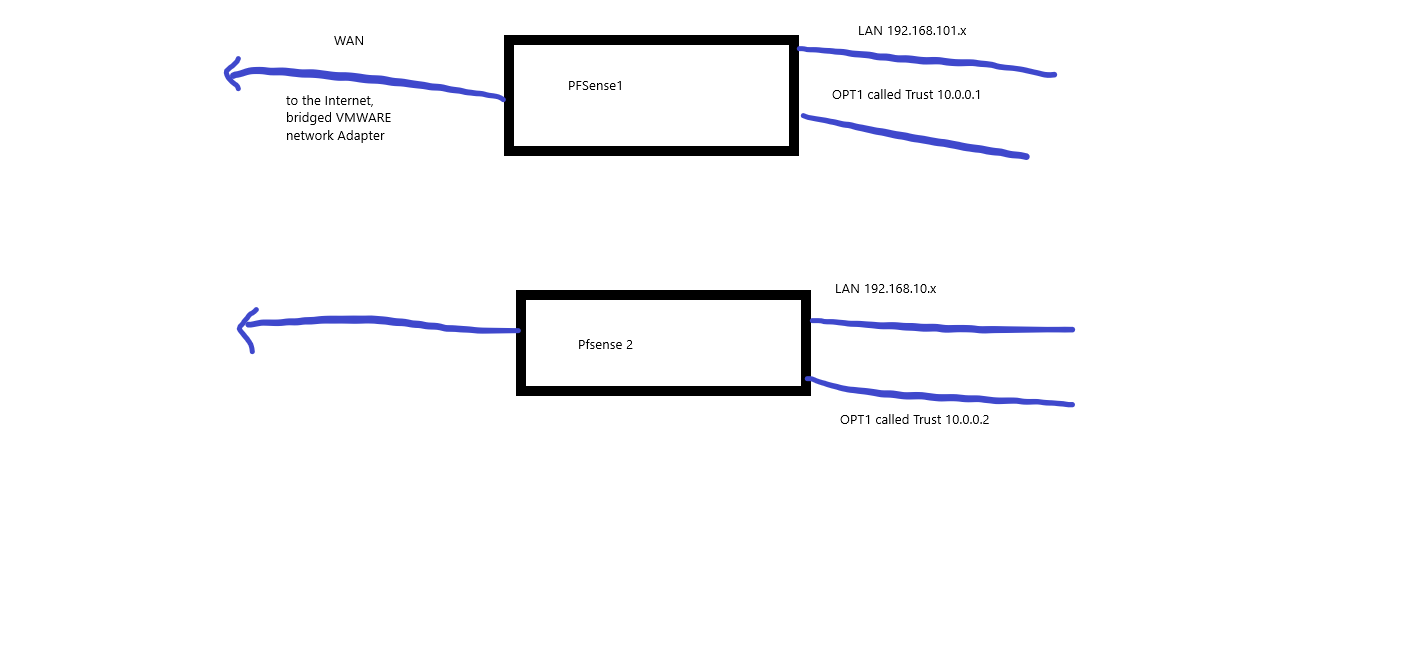
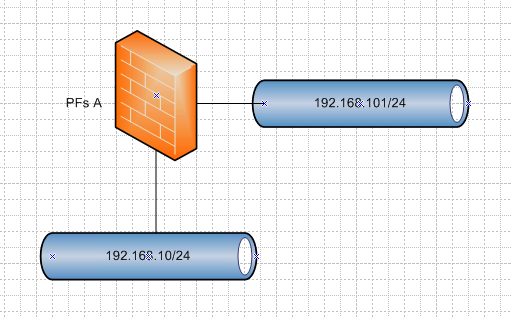
Is this more understandable?
the idea is to let the vpn-connecting for the trust be used by opt1 to have a dedicated connection.
-
And about the routing part, i am still playing with that. All the traffic that needs to go to subnet 192.168.101.x and is coming from 192.168.10.x, should go through the trust(OPT1) connection. other traffic for the Internet should go through the Wan connection. At least, that is what i am thinking, but maybe everything(besides the internet) can be done through the LAN only .
-
@deheugden said in active directory domain trust:
should go through the trust(OPT1) connection.
What?? So you want to create a transit network of 10.0.0/24 Did you setup routing and gateways for that to work?
-
So you want something like this
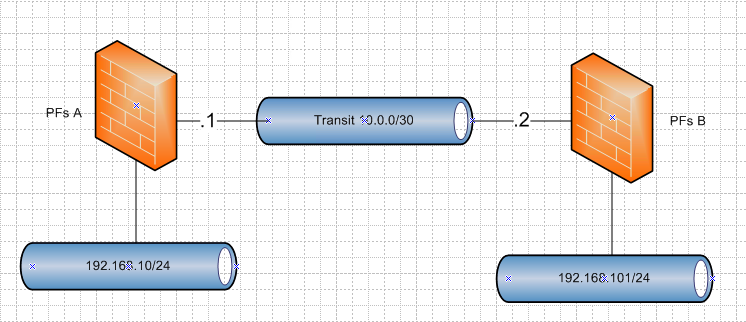
In that case you would have to create
PFs A
gateway 10.0.0.2
route 192.168.101/24 gateway 10.0.0.2PFs B
gateway 10.0.0.1
route 192.168.10/24 gateway 10.0.0.1Be much easier to work out your firewall rules with just single pfsense so you don't have to play with any routing in this phase
-
Your drawing looks better than mine, which tool do you use?
About the 2 Pfsenses, i would prefer the scenario to be realistic. Thats why i am trying to get this done through 2 Pfsenses with a site to site link through VPN. That VPN would be used for my AD Trust.
Maybe 2 Nics will fine, the Wan for both domeins to connect to the Internet and the Lan for the clients and servers. maybe the vpn site to site can be use the WAN or i should start using the Opt1. There is a lot of info on the Internet but often it isnt right for a specific situation. letting 2 domains communicate to each other through their Pfsenses is something i still have got fixed.