windows 10 openvpn connect to multiple remote clients
-
Hi
i have openvpn working perfectly fine on pfsense. and i can succesfully connect with my windows 10 computer to the main pfsense server lanso my pfsense server is 192.168.1.0/24, openvpn is remote access (user auth)
however i have 4 more pfsense routers all connected to this main one, they are remote clients (using peer to peer shared key)
so i have
192.168.2.0/24
192.168.3.0/24
192.168.4.0/24
192.168.5.0/24when i log in with my computer, i can ONLY view the main server and all its local devices on lan 192.168.1.0/24
but i can not access anything on the other remote clients such as 192.168.2.0/24is there a way to connect to all remote clients?
Thank you
Ben -
Simple matter of routing.
Your client will need to be sending all traffic over the tunnel or have routes for all of those networks (add 192.168.[2345].0/24 to the Local Network(s) on the OpenVPN server you are connecting to.)
Those sites will need to have routes to the OpenVPN tunnel network in the server you are connecting to (192.168.1.0/24).
Of course, all necessary firewall rules will need to be in place where traffic enters all of the various interfaces.
-
hi
so i added on my openvpn server, the following in the local ipv4 networks
192.168.1.0/24,192.168.2.0/24,192.168.3.0/24,192.168.4.0/24however i dont understand what i am supposed to do on the clients side? can you give me step by step?
i have openvpn firewall allow all is that not enough?
-
Adding them to the Local Networks on the server will push the routes to the clients as long as the client is not configured with the equivalent of Don't Pull Routes.
In most cases you do not need to do anything.
-
see attached screenshot of
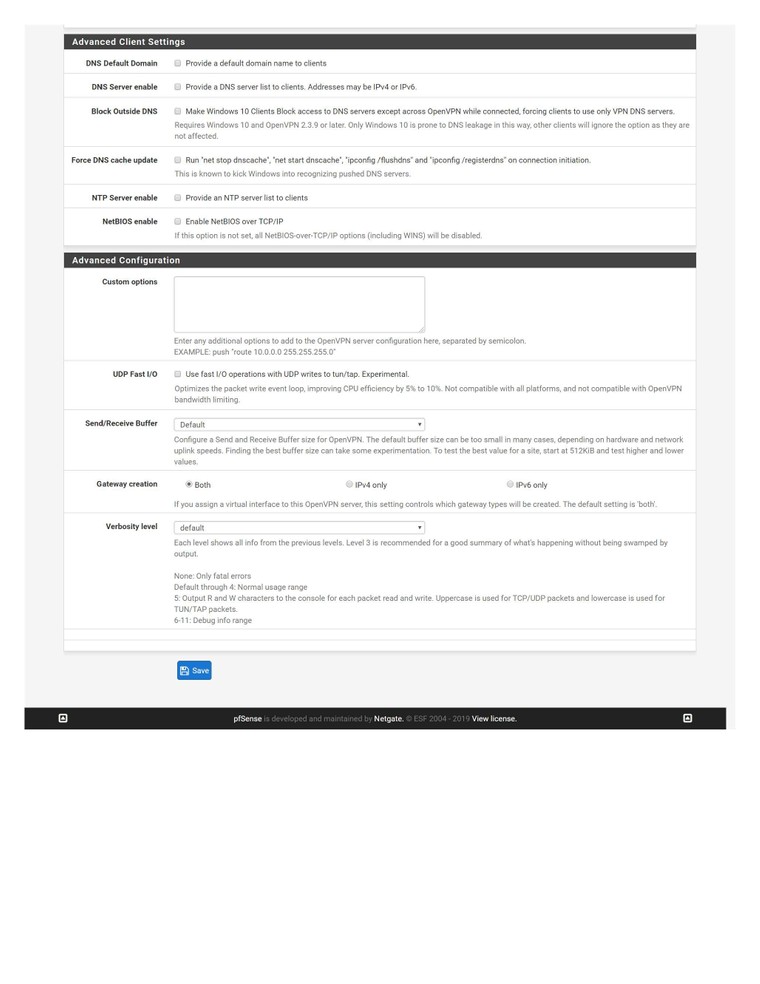
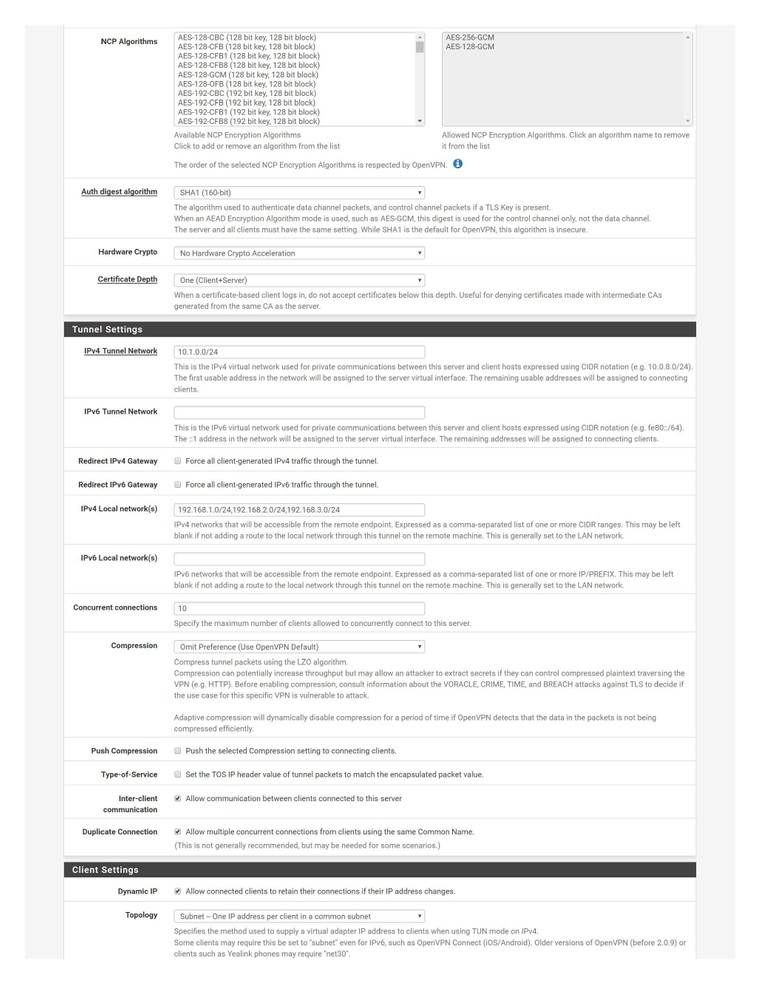
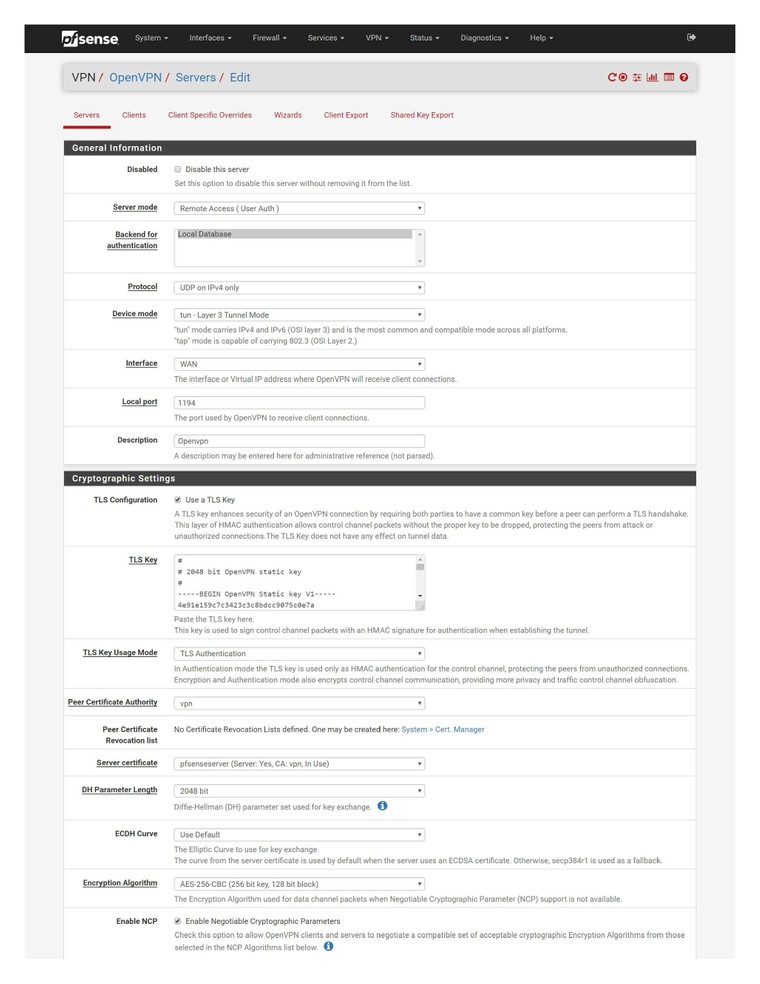 my server. as its still not working.
my server. as its still not working.
the clients are my openvpn software on windows 10. not sure how to see the config files on windows 10. i dont think they are saying dont pull routes.
i simply used the export wizard to export the setup file for windows 10. -
And? Look at the routing table on a connected client.
-
@Derelict
how do i see that in windows 10
the config file for windows 10 openvpn program shows only
dev tun
persist-tun
persist-key
cipher AES-256-CBC
ncp-ciphers AES-256-GCM:AES-128-GCM
auth SHA1
tls-client
client
resolv-retry infinite
remote xx.xxx.xx.xx 1194 udp
auth-user-pass
ca firewall-UDP4-1194-ca.crt
tls-auth firewall-UDP4-1194-tls.key 1
remote-cert-tls server -
route print-Rico
-
This post is deleted! -
OK so the routes are there. Are you passing the traffic into pfSense on the OpenVPN firewall rules?
Are the services on 192.168.1.0/24, 192.168.2.0/24, and 192.168.3.0/24 being blocked by some local firewall on the target hosts? (think windows firewall there.)
-
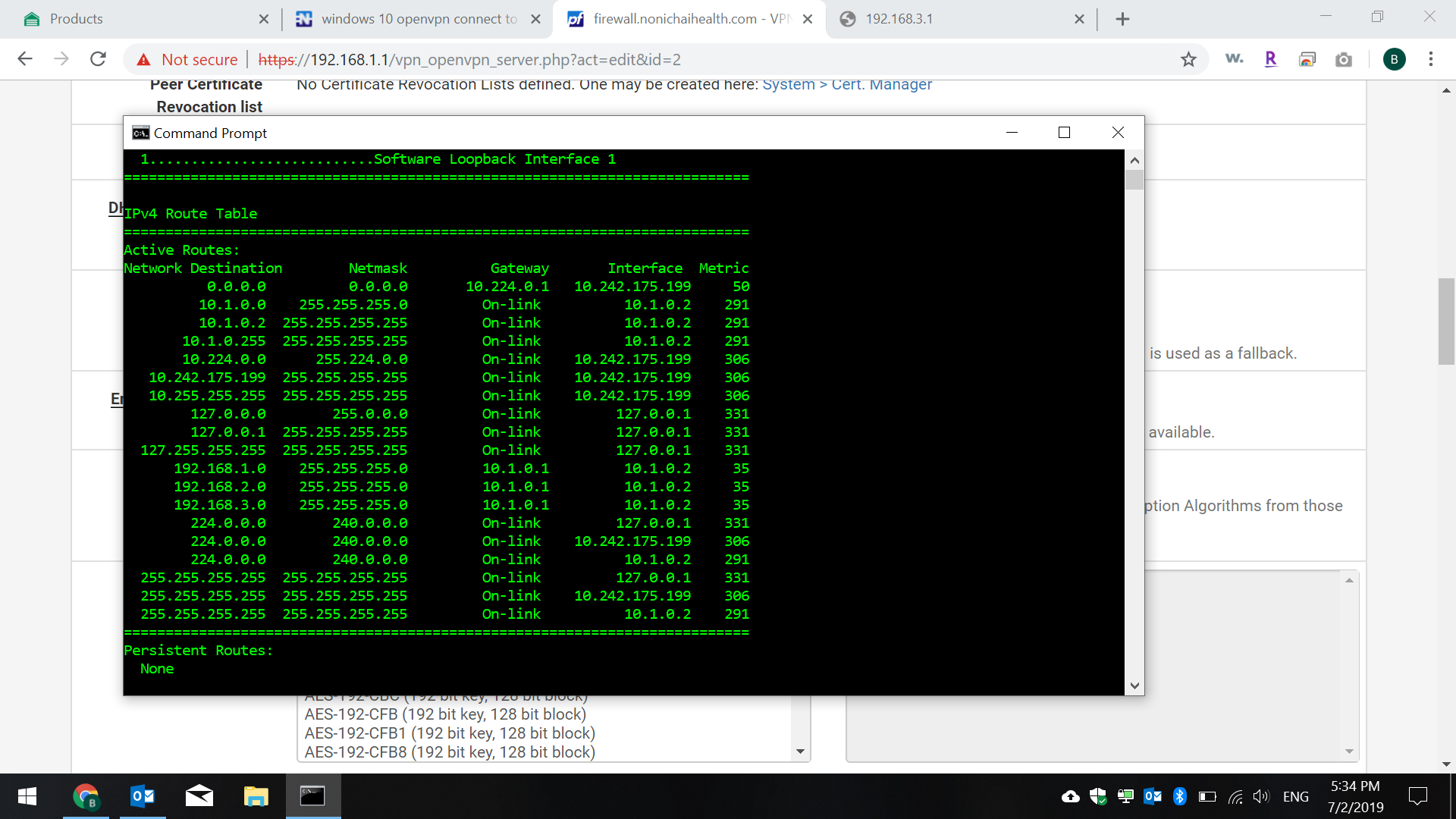
i imagine i type that command in CMD of windows? if yes, here is the screenshot of the results.
-
bump ^
-
@Derelict
my firewall in pfsense has a rule for openvpn interface to pass any protocal from ipv4
source and destination is set to any.
do i need another firewall rule in pfsense? -
Post said rule.
-
@Derelict see attached
sorry for the delay in responses, i have to wait 120 seconds between each post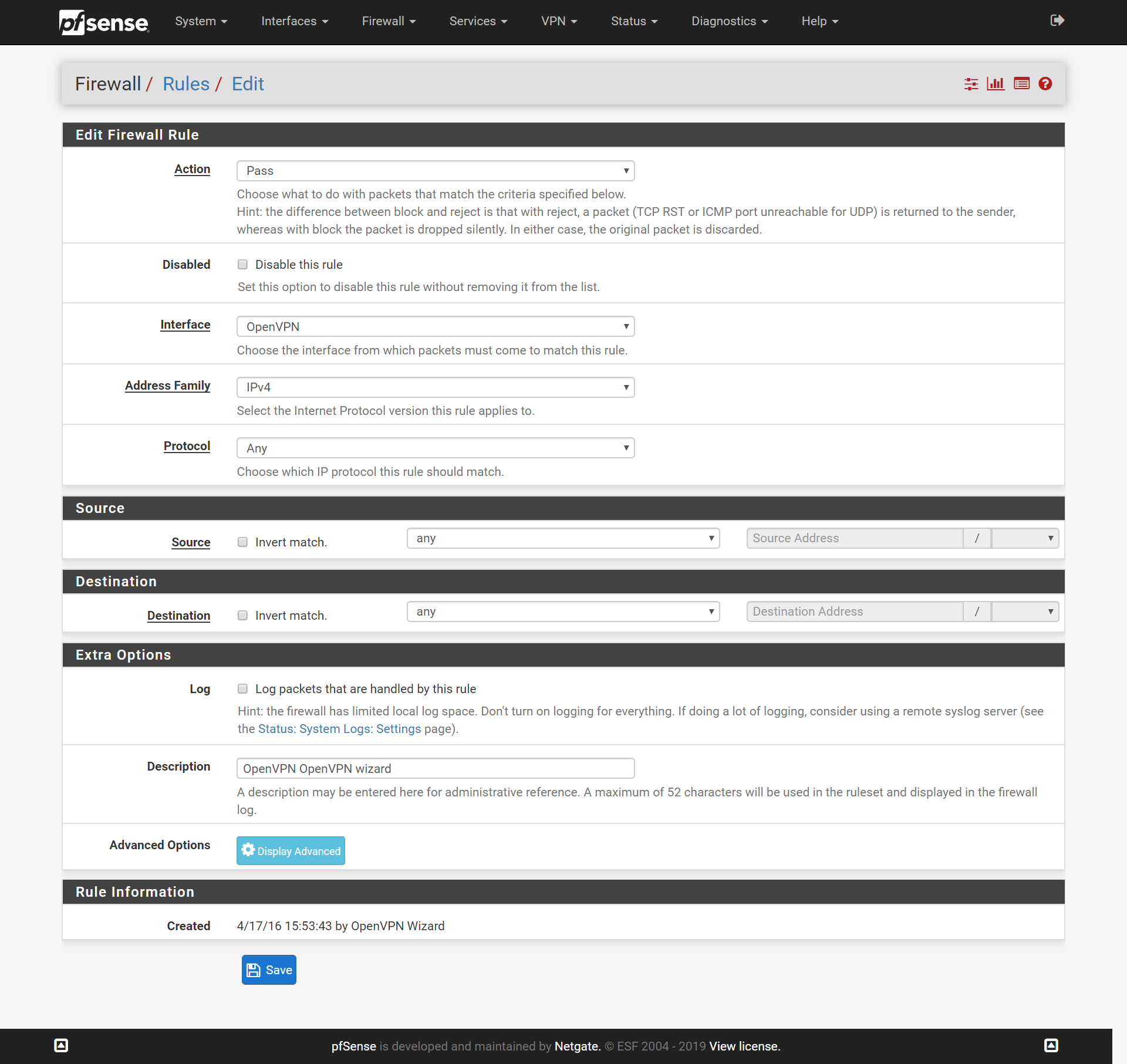
-
OK it's not that. check the firewalls on the target hosts.
Try to ping the pfSense interface addresses.
-
ping from pfsense router 192.168.1.1 to a remote one 192.168.3.1
PING 192.168.3.1 (192.168.3.1): 56 data bytes
64 bytes from 192.168.3.1: icmp_seq=0 ttl=64 time=31.684 ms
64 bytes from 192.168.3.1: icmp_seq=1 ttl=64 time=34.436 ms
64 bytes from 192.168.3.1: icmp_seq=2 ttl=64 time=33.773 ms--- 192.168.3.1 ping statistics ---
3 packets transmitted, 3 packets received, 0.0% packet loss
round-trip min/avg/max/stddev = 31.684/33.298/34.436/1.173 msping from CMD windows 10
Pinging 192.168.3.1 with 32 bytes of data:
Request timed out. -
No. From an OpenVPN client, man.
-
im sorry if im new and not understanding this properly and i appreciate your help.
isnt my windows 10 computer considered the client? this is a vpn connection on my laptop when i travel i have openvpn installed and i login and i can connect only to the main pfsense server that is hosting my openvpn to my laptop client as a remote access user auth.
however the same pfsense main server has other openvpn connections to remote pfsense routers in 2 other office locations using peer to peer shared key, and from my laptop i can not access those remote offices that are connected to my main pfsense server at the main office -
Your client is connecting and getting an address in the tunnel network, 10.1.0.0/24 (10.1.0.2)
It is being pushed routes to route 192.168.1.0/24, 192.168.2.0/24, 192.168.3.0/24 over the tunnel. That looks like it's working.
So from that connected client, ping 192.168.3.1. If that works, the VPN is working.
Then try to access a host on that network (or one of the others.) if that fails it is almost certainly a firewall on the TARGET host, not on the pfSense firewall. Windows in particular likes to filter connections to it to just it's local subnet. Yout 10.1.0.0/24 tunnel network will be outside of that subnet.