Setting up LAN Bridge and VLANs
-
I am planning to change by pfSense installation to take advantage of VLANs for my wireless network(s). Right now I am testing in my virtual lab and I am having trouble getting things working. I would rather not have to bridge interfaces in pfSense but I was unable to get my pfSense box, Ubiquiti access-points, their controller and my DGS-1100-24 D-Link switch to play nice.
My original plan when I was setting up pfSense was to configure my pfSense box to have a VLAN (for guest wifi) on the LAN interface which is an LACP trunk to my main DGS-1100-24 managed the switch. The trunked ports on the switch would be set to work a trunk/uplink VLAN ports passing all tagged and untagged traffic and then I would have 3 other ports assigned to be trunked as well, the remaining would be untagged. This should have allowed all non-tagged traffic to work normally and then anything that was tagged would follow the VLAN path.
In the Unifi Controller I setup 2 wifi networks, one with a VLAN tag and one without, No matter how I configured the DGS-1100-24 switch I could not get things working and once I made configuration changes to make the switch VLAN aware I lost connectivity and had to power cycle it.
Sorry for the long post but I wanted to provide as much detail as possible. This brings me to my new plan which is to use the extra interface on the pfSense box and have it be both a LAN connection via a bridge with the other LAN Interface and also VLAN aware so that I can set up guest wifi with a VLAN tag.
In my new test install of pfSense, I have a WAN interface setup with a DHCP address from my production pfSense box and can ping out to the internet. I have then selected the next interface and set it up with no IP address just simply enabled it and have called it Port1 even though pfSense uses LAN for its name. I then created a bridge containing only this Port1 interface and called the bridge LAN bridge. I then enabled the new LAN bridge interface and called it LAN and assigned it a static ip of 192.168.1.1 with a 24 subnet. I then turned on DHCP for the LAN interface and allowed a range of 192.168.2 - 192.168.1.10.
Finally, I went over to the firewall rules and have a single rule on the Port1 Interface that allows all traffic to any destination. I also have a rule on the LAN interface that allows all traffic from the LAN network to any destination.
When I connect a computer (which is a virtual machine also done in VirtualBox and connected to the same "network" as the Port1 interface on the pfSense box) I receive an IP address from pfSense in the appropriate DHCP range but I am unable to access the internet or ping the pfSense box.
What have I done wrong or what have I missed. Ideally, I would like to use the switches to handle the wifi access points and simply have them work on the LAN network with their wifi networks (SSIDs) be controlled via VLAN tags.
-
ok so where do we start ...
i can tell you how i have configured my cisco sg350x-24 for the vlan as i never had a dlink. at home i'm using it as a layer 2 only.
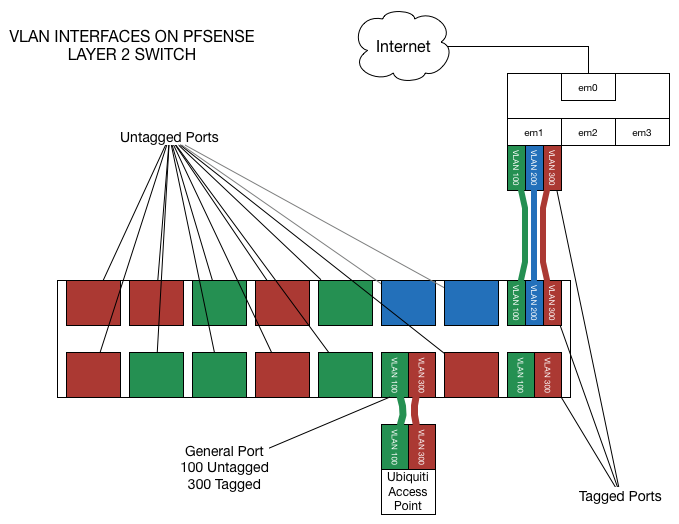
so i created new vlan interfaces on my pfsense with vlan tag 20 for iot and another interface with vlan tag 30 for wifi both have igb1 as parent interface (igb0 is WAN, igb1 is my LAN network interface)
i have enabled the interface and i have set a static ipv4/ipv6 address on it
LAN is 192.168.1.0/24
IOT is 192.168.2.0/24
WIFI-HOME is 192.168.3.0/24
the cable go from igb1 to my cisco on port XG1
i set the uplink port (XG1) to trunk that operate on vlan 1 UNtagged, vlan 20 tagged and vlan 30 tagged
i have added the vlan on my vlan settings
1 LAN Default
20 IOT
30 WIFI-HOMEall port from 1 to 24 are set as vlan mode access
i want port from 1 to 4 for IOT
i want port 5 for WIFI-HOME > (there is an access point connected here)
i want port from 6 to 24 as normal LANso i set port from 1 to 4 as this
vlan 1 excluded
vlan 20 UNtagged
vlan 30 excludedi set port 5 as this
vlan 1 excluded
vlan 20 excluded
vlan 30 UNtaggedport from 6 to 24
vlan 1 UNtagged
vlan 20 excluded
vlan 30 excludedso this make my vlan work as intended
for your second part
you have a pfsense ->dhcp-> pfsense -> dhcp -> pc on a vm ?
there is a typo i think -> 192.168.2 - 192.168.1.10. do you mean 192.168.1.2 - 192.168.1.10 ?
why a bridge with only one interface ? is the range 192.168.1.0/24 different from the range assigned by the pfsense to the wan of the other pfsense? -
It sounds like all you have to do is grasp the concept of VLAN tags and how it all fits together.
Start small, get it working, then duplicate it for other VLANs.
-
Yes, that was a typo my DHCP range for the test pfSense box is 192.168.1.2 - 192.168.1.10 with the LAN interface using 192.168.1.1.
I have since tried setting it up on my production box to see if it will work under a simpler method. The topology is as follows:
Internet -> Modem -> pfSense -> switch -> WIFI access point
I set the pfSense to use VLAN 20 (desc of Guest VLAN) for guest wifi and added it as an interface and called it GuestLAN. I then created a bridge called LAN Bridge and combined the LAN and GUESTLAN interfaces. I copied the allow rule from the LAN interface to the GUESTLAN interface.
I went into the switch software and only changed port 10 and port 16 to say that if they are untagged use VLAN1 like everything else, which is the default and I added if the port is Tagged to use VLAN20.
Finally, I went into the Unifi Controller and created a second network that uses the VLAN 20 tag and assigned an SSID to it.
I can still connect to the switch and my normal wifi seems to be working on my tablet but not on my phone and guest wifi is not yet working.
-
Just forget bridges exist. You do not need them.
-
I have just tried that, I removed the bridge gave the GUESTLAN a static IP address of 192.168.5.1 and then set up a DHCP server.
I also adjusted the firewall rule to allow traffic from the GUESTLAN net to any destination but my phone is having trouble getting an IP Address.
-
forget about the bridge, the problem is on the switch
-
Yeah configure your VLANs correctly and it will all work.
tagged vs untagged. Learn what that means and how it applies to pfSense, the switch, and the APs and you'll be all set.
-
it is definitely the switch from the looks of it but not sure what settings to change and d-link wasn't so helpful. I have ports 10 and 16 set to tag as VLAN20 and also untag as VLAN1 and the rest are all just untagged VLAN1.
I am hoping there is someone with d-link experience that knows where I am going wrong.
-
that's the problem, you don't tag the port you have to make the port join the correct vlan
you should have some option somewhere where you set
vlan1 excluded - vlan20 untagged -
It has nothing to do with what switch you're using. tagged/untagged. That is all you need to know (and understand).
If you set the switch like you describe and assign an interface to VLAN 20 on eth0 and connect that to port 10 or 16 it will work.
If you put an SSID on the UBNT AP and tell if to use VLAN 20 and connect that to the other port (10 or 16) it will work.
You can put off the wireless for now by making another switch port UNTAGGED on VLAN 20 and connecting a laptop there. You should see DHCP/etc from pfSense there.
-
In the Unifi Controller, I have set up two networks, 1 as the private wifi and the second for the guest wifi which has the option to use a VLAN tag, which is set to 20 the private wifi is not tagged. I have removed the VLAN settings from the switch and my main wifi works but the guest wifi will not receive an IP address and fails to connect.
-
Because you have to tag VLAN 20 through the switch between the AP and the firewall.
-
I have removed all VLAN tagging from the switch and turned on port-based VLAN, I then connected my laptop to port 24 and set it to VLAN20 and all other ports are set to VLAN1. I am just installing the VLANsoftware on my laptop so that I can eventually set the tag on the laptop to either 1 or 20
I have not yet used VLANs before, which I am sure is obvious but I feel I know how tagged and untagged works just not sure of the settings in the switch that are needed for that desired outcome.
My understanding is that for most devices that support VLANs they default to VLAN1 which is set as an untagged VLAN. once you want to add another VLAN you need to either add the tag to allow both VLAN1 and the other VLAN or you need to explicitly say that the untagged VLAN is now the new VLAN.
-
No, no, no. You want 802.1q.
This is a solved problem. It all works. Just configure it correctly.
untagged is untagged. It doesn't matter what VLAN it is. You can connect two untagged devices, both untagged on different VLANs. They will both be in the same broadcast domain. The only way the switches would know there is a mismatch is if they participate in something like Cisco Discovery Protocol (CDP) which is completely outside the scope of this conversation.
Tagged
Untagged
That's all there is.
-
I have decided to simplify the setup that I am using in order to better understand things. I am using my desktop which is running VirtualBox to allow me to create a virtual lab of sorts as I don't have any spare hardware to test this out on.
I have created a new install of pfSense that has 4 interfaces assigned to it. the first I set up as the WAN interface and is bridged through to my production pfSense box and gets a DHCP address (which is 17.2.39.239).
I then assigned the second interface as the LAN which is connected to an internal VirtualBox network which I called OPT1 in VirtualBox.
I then assigned the LAN interface an IP address of 192.168.1.1 and using a 24 netmask. I created a DHCP server on the LAN interface with a range of 192.168.1.2 - 192.168.1.10.
Finally, I added the following firewall rules: 1 on the WAN interface to allow for remote administration so that I could use my desktop to access the GUI. I created a second rule to allow all traffic to any destination on the LAN interface.
When I then set up a second VirtualBox VM as an Ubuntu 18.04 desktop and assigned it an internal VirtualBox network interface on OPT1 I was then able to connect to the pfSense machine and receive an IP address of 192.168.1.2 and have access to the internet.
I now want to replicate how my Ubiquiti NanoHD will being connected eventually, so I created a second Ubuntu VM and assigned it to the OPT2 VirtualBox network for its network interface and then went into pfSense and selected the third interface which is on the same VirtualBox Network. But how do I then allow this machine to be on the LAN network? I tried adding it as an interface and creating an allow all rule but still was not able to connect. I then created a bridge which did give it an IP of 192.168.1.3 but I could not ping anything or access the internet.
Eventually I want to have my 3 NanoHD access-points connected to the same LAN network as all my other computers so that they can be controlled by an Unifi Controller on the 17.2.39.1 network but I want to then make different WiFi networks and have them either as part of the 17.2.39.1 network or on other isolated networks such as guest WiFi on 17.2.38.1 with only specific cross-traffic allowed such as allowing users on the guest WiFi to access my media server which is at 17.2.39.121 and I have a DNS override setup so that you can access it from media.local.network
I have been reading all day and watching videos about VLANs and how they work with pfSense, Unifi and D-link but I am clearly missing something, in the chain and so I have tried this setup to remove the switch from the equation to see if I can do it that way as I have enough interfaces on the pfSense box that I will use in production.
I also have an unmanaged D-Link switch if I that would help eliminate the need to VLAN tag things on the other managed switch and just have it pass things through between the Unifi and pfSense.
-
If you want it on LAN then you have to make a VM bridge to the LAN interface and put the VM interfaces on that network.
You should not be removing the switch from the equation you should be embracing the switch since it is the key to everything you want to do.
My advice is to slow down, stop trying to do everything at once, and make a simple pfSense VLAN interface on, say, VLAN 20, enable it, add the rules, enable DHCP.
Then put a tagged port on VLAN 20 on the switch and connect it to pfSense.
Then make an untagged port on vlan 20 on the switch and connect a laptop to it.
It will work.
Then worry about adding more VLAN interfaces, APs, etc. Do every step and test along the way.
-
I started this morning with a fresh mind and kept things simple. Here is what I did.
I added the spare interface on my main server into the pfSense VM so that pfSense could now see and use that interface. I then added it to pfSense under interface assignments and called it WIFI. I enabled it and did not assign an IP address to it. Next, I created a bridge between the WIFI interface and the LAN interface and called it BRIDGEDLAN. I then went over to the firewall and created 2 rules. One for the WIFI and one for the BRIDGEDLAN to allow all traffic through.
Once this was done my Unifi controller was able to see my wifi access point that I had plugged into the WIFI interface on the back of the server. I then modified my wifi networks so that my wifi that is plugged into the switch will only serve the normal wifi SSIDs which are PrivateWIFI and GuestWIFI. I then created 2 new SSIDs and assigned them only to the newly connected AP and called them TESTWIFIPrivate and TESTWIFIPublic. On the Public WIFI, I assigned a VLAN of 20.
Going back to pfSense I created a VLAN of 20 and assigned it as an interface (called GUESTWIFI) with an IP of 17.2.38.1 (my main network is on 17.2.39.1) and a 24 netmask. Next was to create the DHCP server of 17.2.38.2 - 17.2.38.10 and apply the changes.
Finally, I created 2 rules for the GUSTWIFI one blocking traffic to BRIDGELAN and the other allowing traffic to not BRIDGEDLAN.
When I connect my tablet to TESTWIFIPrivate everything works perfectly I an on the same network as the other devices and I can access internal resources. However, when I connect to the TETWIFIGuest I do get the right IP address from the DHCP of 17.2.38.2 but I cannot access the internet. I expectedly cannot access local resources which is correct as I will only be allowing one resource though after this first part is working.
The resrouse I will be passing through is a media server that has an entry on the pfSense as a DNS override to send the URL of media.local.domain to a nginx reverse proxy server so that I can hide the port numbers and used Lets Encrypt SSL certs. Any help on this next step is also appreciated.
By removing the switch and keeping it simple I have made a lot of progress, I will have to do more learning and research to make the switch part work after this setup is working so i can control the variables at play.
-
Why and the F would you create a bridge on pfsense for different interfaces as a VM? That is just utterly BORKED!!
There would be zero reason to ever do such a thing.. All the interfaces are virtual - if you want multiple vms to be on specific L2, you just connect them to the same vswitch port group.
And you sure and the F should not be using pfsense bridge on a vm to connect different physical ports... Just do that on your switch..
-
The reason I bridged the LAN and the WIFI interface is so that the Unifi AP which is a NanoHD can communicate to the Unifi Controller on the LAN network. I am in the process of learning and testing out using VLANs to segregate a Guest WiFi network and I had a spare NIC on the server that hosts my current pfSense setup.
I am running my pfSense in a VM so that I can leverage the power of the server for other things as pfSense takes very little resources to run, and because of the hypervisor (Proxmox) layer I decided that instead of passing the entire NIC to pfSense I would create virtual interfaces for pfSense to use that would be linked to a physical card, that way I did not have to have more cards and unused ports in the machine.
The only VMs that are running that are related to this thread is the pfSense VM and the Unifi Controller VM which each have their own ports because I wanted to separate pfSense from the rest of the LAN network. The Unifi Controller has a virtual NIC assigned to it what goes to a trunked (LACP) set of NICs that it shares with other VMs on the same server. I have been running this setup for the better part of 2 years without any negative impacts or issues. This is a home-based setup that is more my playground that a production business environment.
I believe the problem I am having with the internet on the GUESTWIFI is coming down to firewall rules and or configuration on how pfSense handles DNS lookups and also the configuration of my multiple gateways.