Windows Server 2016 using Advanced Firewall + pfSense with pfBlocker (for GEO Location blocking)
-
Hello,
I just built a pfSense system with pfBlocker for the specific purpose of GEO location IP blocking.
I have this one system running Windows Server 2016. It is a domain controller, name server, webserver, runs Microsoft SQL and uses Windows Advance Firewall. This setup works and has been for almost 3 years. Recently, there have been increased attacks from countries such as China & Russia, which at times could flood the network and eat up processing power. The attacks go for the SQL server which uses NTLM to authenticate. Having at times maybe 50 attempts/sec on the server. All authentication requests fail because the attacks focus on clear text access to the "sa" account versus NTLM...which are rejected. Upon seeing an attack from viewing the Network Resource monitor, I simply note the offending IP address and enter it into a blocking rule of Windows Firewall. This is more reactive and at times...takes time, but it works.
With that said, I want to simply the process and be proactive by simply blocking out the country.
Where I'm stuck at...and I'm still learning to use pfSense...is configuring it to be in front of this Windows Server 2016 box and after the modem.
How do I go about doing this?
Thank you in advance - Irwin
-
You already have a router that is forwarding your server ports to the Internet. You need to either replace that router with your pfSense box, or you need to put the pfSense box between the router and the server. It's hard to be more specific without knowing any details of your current config.
-
From my fiber connection which is in bridge mode, it simply runs to switch. The server plugs directly into the switch. There is no router in place. The Windows Server 2016 is setup with a public IP on one network port, and local LAN on another. The server also runs DNS and Active Directory.
-
You've got a live Windows Server directly connected to the Internet, with just the software firewall protecting it, and it's acting as the router for the rest of the LAN???
You're a braver man than I.
I would connect your fibre directly to the pfSense box WAN port and then connect your switch to the LAN port. Create Virtual IPs to handle any extra IP addresses from your ISP. No wonder your server is getting pounded. I was wondering why you were exposing SQL ports to the Internet and I guess I now know why. Your config was common in the late 80's/early 90's but nobody does it like that anymore.
-
@KOM said in Windows Server 2016 using Advanced Firewall + pfSense with pfBlocker (for GEO Location blocking):
You've got a live Windows Server directly connected to the Internet, with just the software firewall protecting it, and it's acting as the router for the rest of the LAN???
You're a braver man than I.
All I can say is that it works! Just have to open ports that are needed and lock down everything else. Windows Advance Firewall has come a long way. But no way near what pfSense can do. Since all the attacks are focused on cracking NTLM to authenticate with SQL...and most times, they go for the standard "sa" login which is evident withing the logs of the Event Viewer.
I would connect your fibre directly to the pfSense box WAN port and then connect your switch to the LAN port. Create Virtual IPs to handle any extra IP addresses from your ISP. No wonder your server is getting pounded.
OK, this is doable...but what is the process of configuring the WAN port? Upon initial setup, I entered the public IP of the server that I want to protect...obviously this needs to change.
I was wondering why you were exposing SQL ports to the Internet and I guess I now know why. Your config was common in the late 80's/early 90's but nobody does it like that anymore.
This is still fairly common practice with Microsoft SQL server products.
-
Your config was common in the late 80's/early 90's but nobody does it like that anymore.
This is still fairly common practice with Microsoft SQL server products.
Sorry, I was referring to using the main office server as the router.
but what is the process of configuring the WAN port?
You take the same details that you configured the server's WAN & LAN NIC and put them on the pfSense WAN & LAN. That means you only need the one LAN NIC in your server. You can still use the Windows server for DHCP and DNS to your LAN clients.
-
@KOM said in Windows Server 2016 using Advanced Firewall + pfSense with pfBlocker (for GEO Location blocking):
Sorry, I was referring to using the main office server as the router.
Ah...I have 5 Class C IPs...one of them has a Netgear WIFI router handling internal LAN networking. Here is the overall setup. I actually have 2 separate fiber lines coming in and both have 5 Class C IPs.
Group #1 (1000mb down/100mb up - Email Server Windows Server 2019 Core with Exchange Server 2019 Core...that's it) only 1/5 Public IPs used
Group #2 (1000mb down/300mb up) 4/5 Public IPs used
- General Internet Access for Internal LAN (Netgear WIFI router)
- Server #1 (Windows Server 2016 - Domain controller, Name server, webserver, SQL server)
- Server #2 (Windows Server 2016 - Domain controller, Name server, webserver, SQL server)
- Server #3 (Windows Server 2019 Core, webserver)
but what is the process of configuring the WAN port?
You take the same details that you configured the server's WAN & LAN NIC and put them on the pfSense WAN & LAN. That means you only need the one LAN NIC in your server. You can still use the Windows server for DHCP and DNS to your LAN clients.
With the above mentioned layout in Group #2 and to understand a little more of the process...
- Attach the fiber connection to the WAN port pfSense
- Assign 4 Virtual WAN IPs (WIFI router & 3 Servers) to the LAN port pfSense
- From the LAN port on the pfSense, I connect to the switch
- From the switch, I attach the WIFI router & 3 Servers
Does that sound right? If so, how is that WAN port on pfSense configured? (Since now it is a bridge)
-
Close. The Virtual IPs in step two are attached to WAN, not LAN. I use IP aliases for that, but some of the other types will also work.
https://docs.netgate.com/pfsense/en/latest/book/firewall/virtual-ip-addresses.html
WAN won't be a bridge, it will use one of the 5 IP addresses you've been assigned. You configure it like a static IP. The others will be virtual. Your ISP should provide you the IP addresses, the gateway and the netmask. Apply one of the IPs and the other details to your WAN.
-
@KOM said in Windows Server 2016 using Advanced Firewall + pfSense with pfBlocker (for GEO Location blocking):
Close. The Virtual IPs in step two are attached to WAN, not LAN. I use IP aliases for that, but some of the other types will also work.
https://docs.netgate.com/pfsense/en/latest/book/firewall/virtual-ip-addresses.html
WAN won't be a bridge, it will use one of the 5 IP addresses you've been assigned. You configure it like a static IP. The others will be virtual. Your ISP should provide you the IP addresses, the gateway and the netmask. Apply one of the IPs and the other details to your WAN.
OK! Got it. I'll tackle this later in the evening. Thank you for the insight...will report back sometime tomorrow on the results.
-
Once you have the VIPs created, you can use them as Destinations when creating a port-forward (Firewall - NAT - Port Forward) to map that VIP to a LAN server. I have 14 addresses that I used to forward to all sorts of internal servers until we started moving stuff to the cloud. Now all I have is one forward to a Nextcloud instance.
-
@KOM said in Windows Server 2016 using Advanced Firewall + pfSense with pfBlocker (for GEO Location blocking):
Once you have the VIPs created, you can use them as Destinations when creating a port-forward (Firewall - NAT - Port Forward) to map that VIP to a LAN server. I have 14 addresses that I used to forward to all sorts of internal servers until we started moving stuff to the cloud. Now all I have is one forward to a Nextcloud instance.
Ah Ok...the picture is a lot more clearer now. Thank you!
-
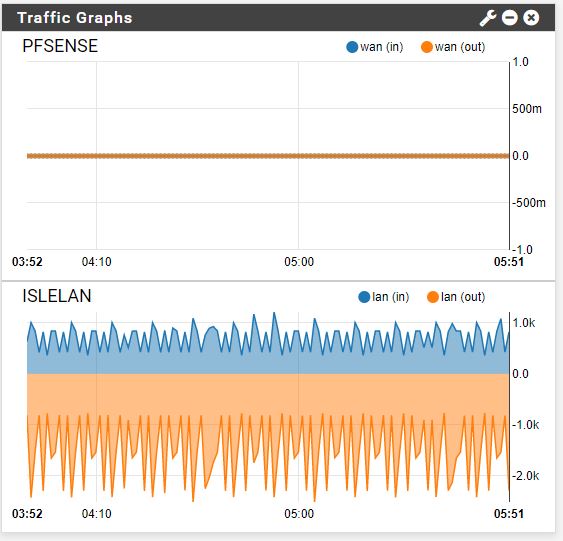
Alright...I had it working for about 35 minutes and the interface gave up

Anyway...its an old server board, but I have an Intel Quadport 1gb coming in a few days that was supposed to go into the system. I believe it'll be OK....I only put in one Virtual IP...the main server I wanted to protect.... I was viewing the resource monitor on the server as pfSense was displaying the blocks....pretty cool.
Well...thank you for your assistance...it's truly appreciated!
-
FYI...i got it back up and running. Wasn't hardware...i was adding on Virtual IPs and made a mistake...deleted one of the IPs while in a rush. Double-checked and just added it back in....back online!!
