Changing VPN provider
-
I currently use the included VPN from Usenetserver. I have their VPN working with my pfSense router. I'm trying to switch over to their new provider Privado.
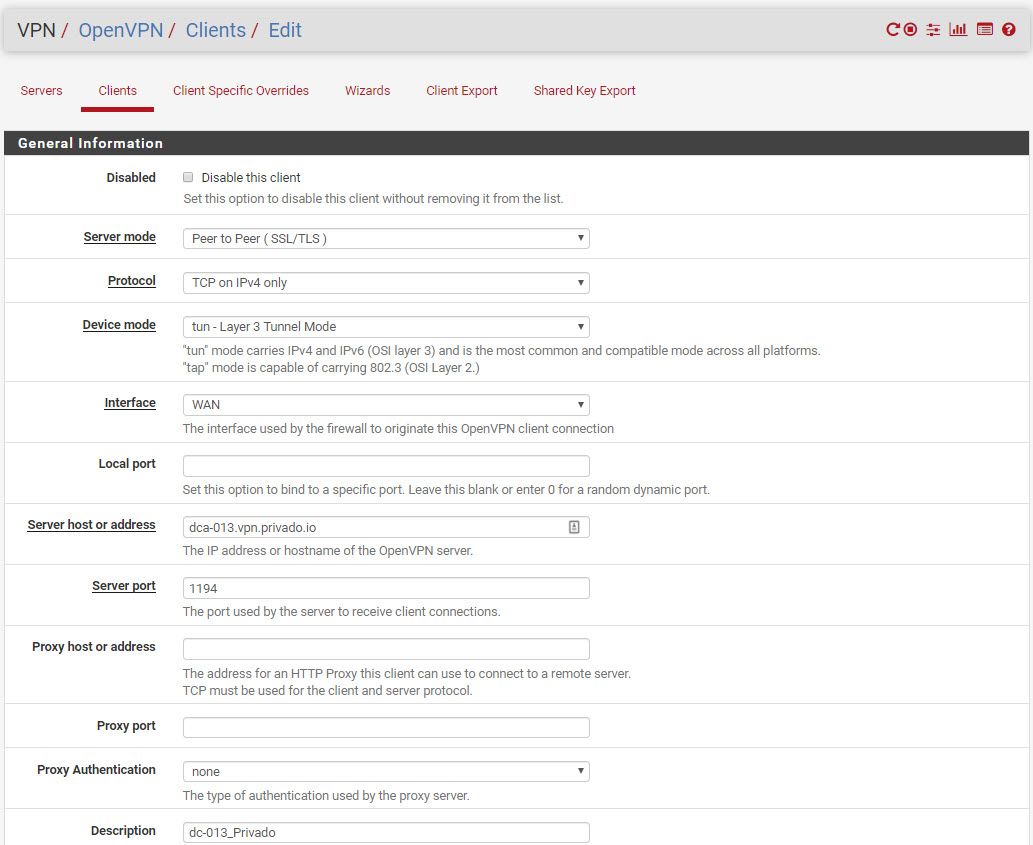
I created a new CA and then a new VPN client based on the ovpn files they supplied. When I go to Status/OpenVPN/client instance statistics is says the new VPN is up. Then I changed my VPN_WAN interface assignment network port to ovpnc2 (the new VPN) from the old ovpnc1. When I reboot the firewall I lose internet as I don't have DNS anymore. Any idea what I'm missing?
To get the internet working again I have to reload the prior config and reboot the firewall multiple times.
-
Found the problem. My new provider uses TCP and the old one used UDP. After changing the VPN_WAN rule to use TCP/UDP it all works.
-
I'm in the same boat. It's been years since I initially set this up and I'm having trouble getting connected (my old brain can't remember that far back!). I don't suppose I could trouble you for screenshots of your settings?
lol, nm. Double-checked the settings from the ovpn and I'd missed one!
-
@riggs said in Changing VPN provider:
I'm in the same boat.
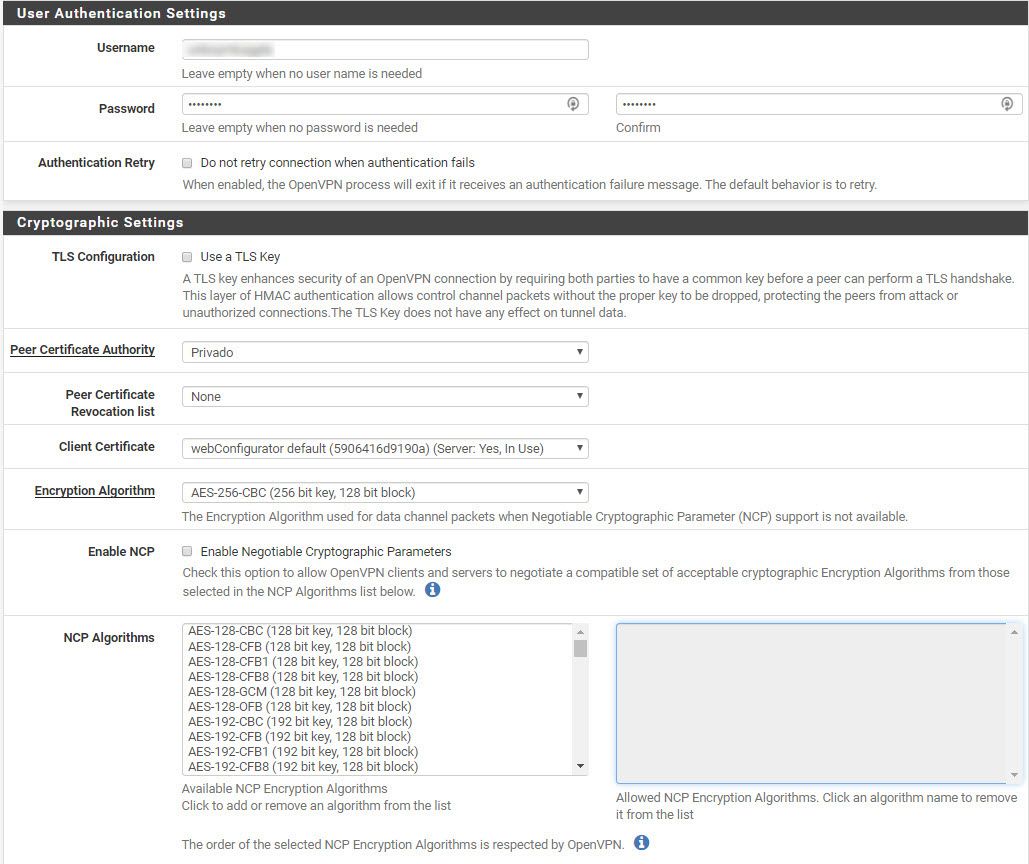
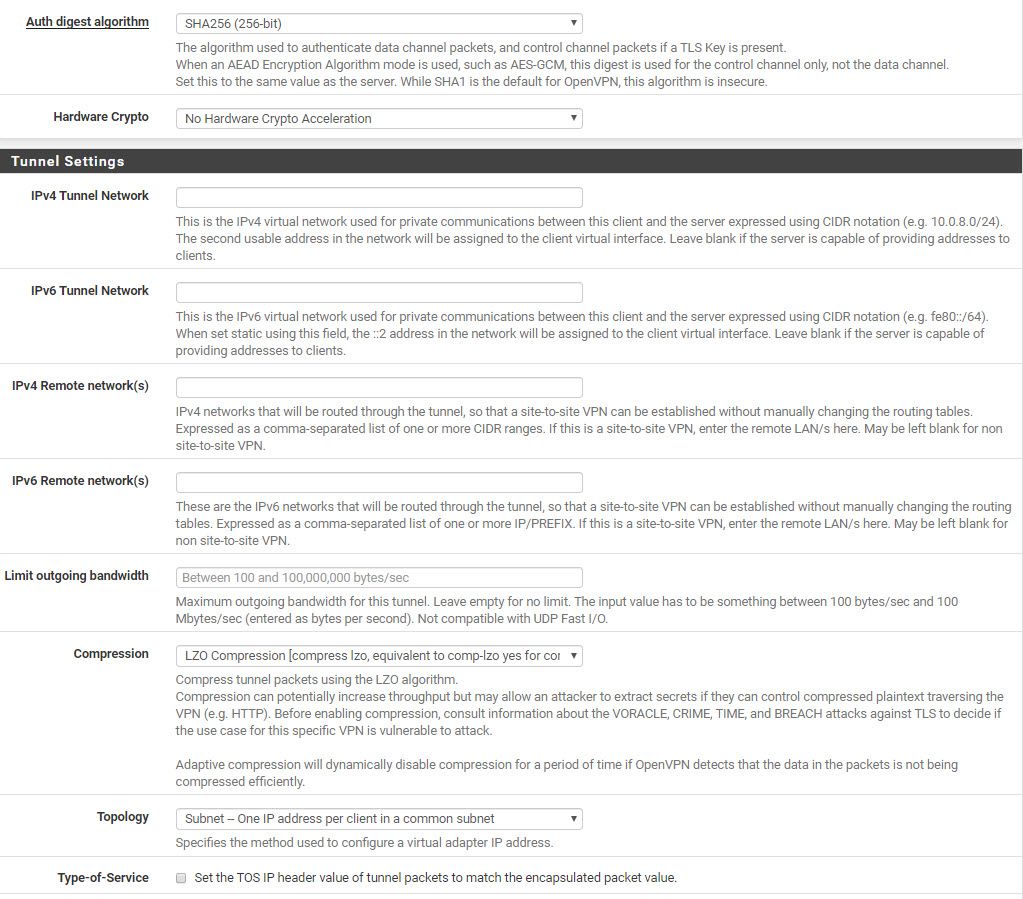
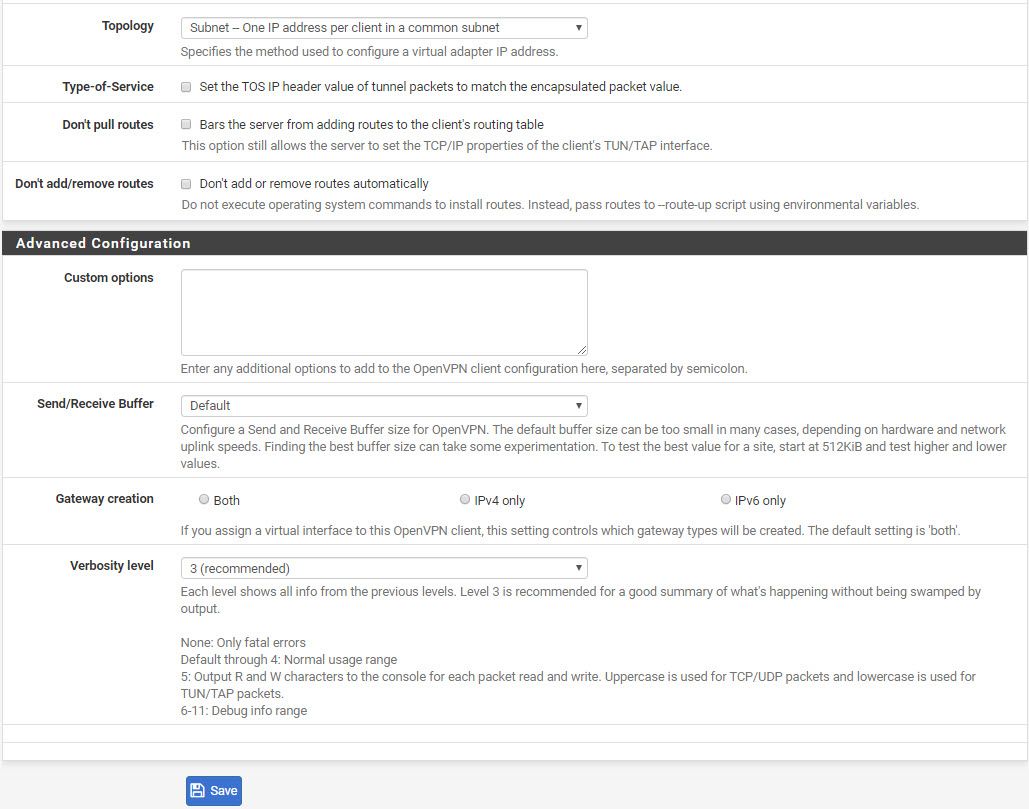
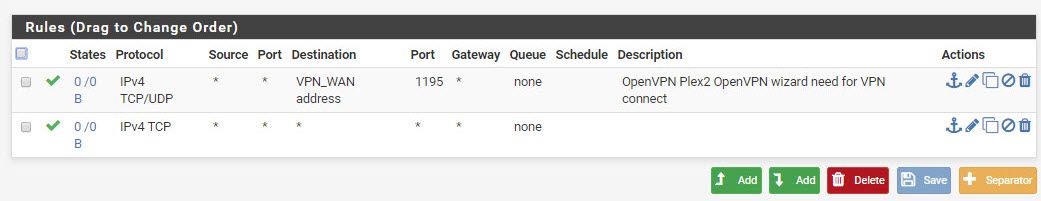
Here are my settings. I'm curious to know if yours differ?
Firewall Rules on VPN_WAN
-
@NasKar Thanks man. All looks pretty similar tbh, although I am using an older version of pfSense so some of my options aren't as detailed (last time I tried updating it totally broke my DDNS, so I just stuck with v2.3.5).
It's all up and running now anyway, I'd initially missed one of the settings. Thanks again.
-
@riggs
It kept disconnecting so I changed some of the custom options to include:
persist-key
persist-tun
persist-remote-ip
tls-client
remote-cert-tls server
tls-cipher TLS-DHE-RSA-WITH-AES-256-CBC-SHA:TLS-DHE-DSS-WITH-AES-256-CBC-SHA:TLS-RSA-WITH-AES-256-CBC-SHANow it seems to work without error in the log file
-
I also have the Usenet change to Provido, I still cannot get it to work. I can ping IP address but NO dns is working. I am looking at your changes but this is not working for me. any more Hints or others that have made this switch could please share what needed to change between the USENET config and this Privado one?
-
@Dudleydogg said in Changing VPN provider:
I also have the Usenet change to Provido, I still cannot get it to work. I can ping IP address but NO dns is working. I am looking at your changes but this is not working for me. any more Hints or others that have made this switch could please share what needed to change between the USENET config and this Privado one?
My setup was a mess. I removed some old VPN servers so they were not on the same port 1194 and it worked. I think if your setup in Status/Openvpn/Client is up then the OpenVPN client setup is ok and your issue is with the other settings like the rules for the VPN interface, NAT outbound tab, DNS resolver or rules on the WAN
-
If i go to DNS settings on my Computer and override DHCP and put in 198.18.0.1 for DNS the Vpn works as expected. when I do nslookup it fails like there is no dns assigned. but if I specify dns nslookup google.com 8.8.8.8, i get a response.
-
@Dudleydogg If you want secure dns lookups through the new VPN, go to Service->DHCP server and look down to server and remove any entries there.
Then go to system->general and under dns server settings add a few dns ips and select your new vpn interface from the drop down on the right. You did create the interface?
This will force dns lookups through the vpn.I have had and am still getting the vpn dropping even after following the suggestions here. The logs suggest the server end is dropping my connection and refusing to reconnect.
May try two or three vpns in a group route and let it swap over to another and give the original some time to come back, its a plan but so far untried. -
This has been working for Years just how it was, only thing different now is its Privado instead of Usenet same Openvpn, So only things I changed were UPD to TCP, and diff user name and password, and Hostname.
I don't use any DHCP other than IPV6 with pfsense.
Thank you for the Reply but I see what everyone means in this thread, even though my DNS is not working i can ping IP addressses, and it keeps dropping almost like they time out the VPN and it does not auto connect. this is no where near as reliable as the Usenset one and no iphone app either.
-
@Dudleydogg said in Changing VPN provider:
This has been working for Years just how it was, only thing different now is its Privado instead of Usenet same Openvpn, So only things I changed were UPD to TCP, and diff user name and password, and Hostname.
I contacted Privado and they support TCP and UDP. Don't know why their ovpn files are set for TCP by default. I can't get their service to work anymore with pfSense and they currently don't support it officially. There windows app connects with IKEv2 but not with openVPN. I'm guessing therefore it's an openvpn problem on their end. I agree that everything was working fine with the old VPN provider.
-
@NasKar It seems to depend on which city you connect to, Manchester for instance went down often and some I tried in the US of A. I have found one which seems to work so far but I won't give it's name or it will be swamped. Keep trying cities I'm sure some will function better. Mine has been up for 6 days..fingers crossed. Does however suggest they are being inconsistent with their setups from city to city.
-
@NasKar Using most of the Same Settings it is working with PFsense, the problem is they are blocking DNS internally some how have not figured that out. So you connect to the Vlan or SSID that is on the Provido vpn, then manually go set your dns to 8.8.8.8 on that device and it does work. Just stupid each time you disconnect from the vpn you have to go change your dns back to what you had it set to before. Its not Automatic like it was before. I have not reboot my pfsense in like a year LOL so maybe ill reboot here soon and see if that is what the problem is with DNS.
other than dns it does connect to the VPN and I can ping ip's and verify my ip is that of the VPN.
I use outgoing NAT to map vpn traffic since I have multiple Vlans on my pfsense. -
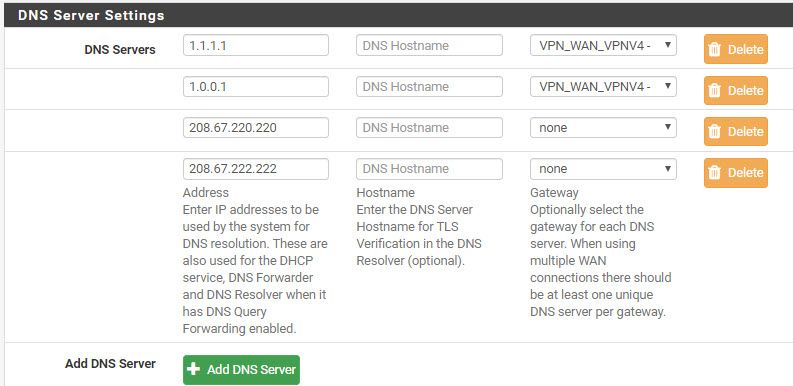
@Dudleydogg As I said in a previous post, the dhcp from pfsense will automatically give your pc it's IP as the dns lookup. What your missing is telling pfsense what external dns ip to forward requests to and on what interface.
Go to System->General and go down to dns and enter the external dns ip there and three boxes to the right select your vpn interface from the drop down list.
There are lots out there which can be used here are some better than google (not secure)
1.1.1.1
1.0.0.1
208.67.220.220
208.67.222.222You can put them all in and punt them out all the interfaces if you want including the unencrypted ones but if your using a vpn for security best to punt 1.1.1.1 out the single vpn. This has the added benefit that if the vpn goes down and pfsense re-routes the data out via an none encrypted gateway, which it will do, nothing will work as the is not dns lookup unless the vpn is up.
You can stop the traffic even trying to go out the unencrypted gateway by setting up lan rules to force all traffic from the lan to the vpn gateway.Pfsense is a very flexable and powerful tool, love the control it gives me. My wife's tv traffic to amazon prime and bbc iplayer is routed out via the wan port and these don't like vpns. Also Lan rule for this has a timer set so it cuts the traffic at 11pm which blanks the wifes screen and her tv shuts down. She is asleep by then and gets a better sleep in the dark.
FEEL THE POWER!!!! -
@oggydoggy said in Changing VPN provider:
It seems to depend on which city you connect to
I gave another one a try and so far so good. I've also tried their windows app and it doesn't work with openvpn just IKEv2. I'm waiting to here back from Privado tech support.
@oggydoggy said in Changing VPN provider:
You can stop the traffic even trying to go out the unencrypted gateway by setting up lan rules to force all traffic from the lan to the vpn gateway.
I tried this setup
@oggydoggy said in Changing VPN provider:
You can put them all in and punt them out all the interfaces if you want including the unencrypted ones but if your using a vpn for security best to punt 1.1.1.1 out the single vpn.
I use the tag/tagged command per https://www.infotechwerx.com/blog/Prevent-Any-Traffic-VPN-Hosts-Egressing-WAN
to kill the internet if my VPN goes down. -
Don't understand why but changing the gateway for the DNS servers broke my plex remote access. So I switch back to a prior config
-
@NasKar I can't help you with your plex issue as I removed it once it required an online account as this was not secure anymore, it was a "nice" thing to have but I can easily survive without it.
Lookup the system logs and see if there is something being blocked on the firewall, filter for traffic going to the plex server ip.
Interesting thing the tagging of the packets on the vpn I will implement this today. I do worry that the vpn is not proven to be reliable and the more things I put in place to force the traffic only through the vpn, I then have to undo them if the vpn goes down, even to just trouble shoot it.
I think I will save the current config, remove the vpn and get it all running and save that. Then restore the current and apply the tagging and save again . So if the vpn goes down I just restore the non vpn config. -
@NasKar OpenVPN client for windows is working on my pc. Install tap drivers, make sure you select a city different from the one in your pfsense OpenVPN and create a rule in the lan to catch your pc ip and OpenVPN port and push it out the wan not the default OpenVPN.
IE your windows OpenVPN should not authenticate to the same servers as another instance. Also a vpn doesn't need to go through a vpn, not saying it can't just saying I currently don't. -
@oggydoggy
My current setup to have an alias for IPs to go thru the VPN on pfsense and a rule before that one that allows another alias (nonvpn) of websites to not go thru the VPN. Maybe problem with windows client is it was set for same VPN server. Will leave windows VPN client off and see how long the openVPN client stay up on pfsense.BTW I added my plex server to the alias to go out the WAN gateway and now remote access stays up. I had to specify the WAN gateway in the novpn alias rule as it wouldn't work with the gateway being set as default.