VLANs having same mac address causing flapping error on cisco switch
-
Host 0008.a2**.**b2 in vlan 1 is flapping between port Po2 and port Po1
Host 0008.a2**.**b2 in vlan 1 is flapping between port Po1 and port Po2I would assume this is because each one of my vlans on pfsense reports as having the same mac, thus causing the cisco switch to think that the host is flapping between channels, when in reality all the interfaces have the same mac?
-
Well yeah, all VLANs from the same interface will have the same MAC. What is it you're trying to do?
-
The MAC address table (CAM table) is segregated between VLANs (broadcast domains)
It is absolutely not a problem to have the same MAC address from a device on different VLANs on the same properly-configured switch port.
In fact, that's pretty much how the world works.
-
@Derelict said in VLANs having same mac address causing flapping error on cisco switch:
It is absolutely not a problem to have the same MAC address from a device on different VLANs on the same properly-configured switch port.
The OP's post implies the switch thinks the MAC is on 2 different ports and that shouldn't happen, unless they're doing something strange.
-
What im trying to do is have each vlan on the fw have its own group of physical ports for lagg.
I have the xg-7100 so it has that marvell integrated switch.
If I run an ifconfig on the fw it shows all the vlans as having the same MAC (and every port on the marvell switch as having the same mac)
Now if I have each vlan with its own channel group on the switch, and the switch sees the same MAC on every lagg group, it sends the flapping error message.I am not 100% whats happening in detail, but I do know when I went in and changed the mac addr for each vlan using ifconfig lladdr, the flapping errors stopped.
-
Perhaps you could provide a sketch, as I'm having a WTF? moment.
How many ports are you using on pfSense for the VLANs? If only 1, then every VLAN that uses that interface will have same MAC. There's no way around that, as it's determined by the hardware. What comes after psSense?
-
You generally see this type of issue in a HA setup, i've seen it many times with an all Cisco setup and HSRP.
Are you running a HA pair, if you are there probably is a connectivity issue between the pair.
-
I am using 7 ports on the marvell switch on the xg7100 connected to my cisco 3560.
eth2-3 are vlan 5
eth4-6 are vlan 10
eth7-8 are vlan 30I wanted to setup a lagg for each vlan, but since the xg7100 marvell switch does not support lacp, I had to throw everything to basic load balancing. I have the cisco ports set up within channel groups, and the pfsense ports I had to manually add them to their own lagg groups through ssh using etherswitchcfg.
As far as I can tell, it works properly, on the switch it shows the proper ports per vlan have bundled.
The 3560 will have the flapping error if I leave each vlan mac addr the same (as shown in ifconfig when run through ssh on the xg7100).
I can draw something up later today to better illustrate.
-
You should be setting up the load balance laggs using the web gui and changing the lagg numbers by clicking on the lagg number in Interfaces > Switches, Ports. Just use a unique number for each group.
-
I should be, but when I go to add a LAGG in the gui, the ports on the marvell switch do not show up. So I cannot make a LAGG with the ports I want to use.
-
Screenshot please. That should not be the case. Unless maybe something you did under the hood is preventing that from working any longer somehow.
-
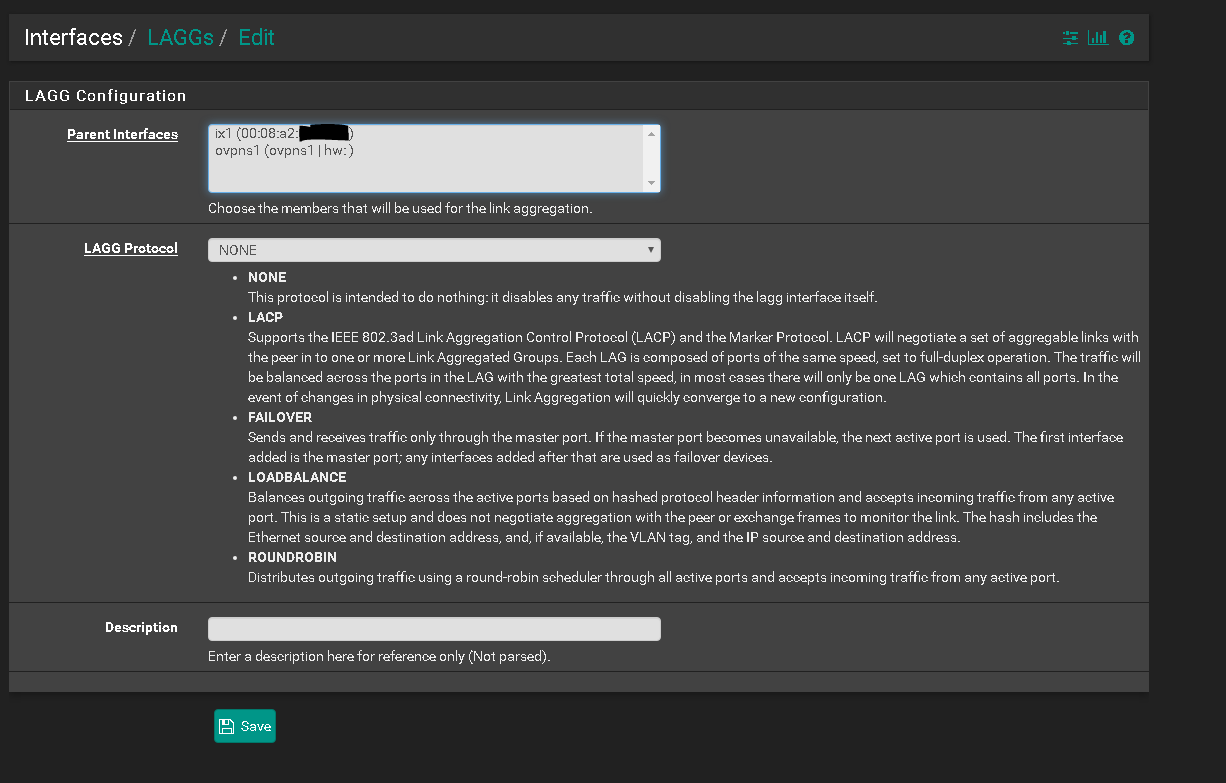
ix1 is only the 10gig sfp+.
Eth1-8 are not shown. -
No.
Interfaces > Switches, Ports
-
If you are referring to inputting the lagg id manually there... that instantly destroys the web gui and requires the firewall to restart.
-
Don't do it on a port you are trying to manage the firewall from. Same way you would not make a change to a switch port you are managing the switch from.
-
Sure, I understand that.
Referencing back to the original question, the xg7100 has the same MAC addr assigned to eth1-8 on the marvell switch, right?
So wouldnt creating separate LAGGs across that marvell switch cause a downstream switch to see the same mac for multiple channel groups, then cause the flapping error?
-
No. MAC Address tables should be separated in the switch by VLAN/broadcast domain.
The MAC address being seen by the switch is actually the MAC address of the lagg0 created by ix2 and ix3 on the pfSense software on the uplink.
Layer 2 switch ports do not have individual MAC addresses. The have MAC address tables and forward traffic between different MAC addresses in the same broadcast domain.
-
Okay, but the downstream switch has its own mac address table and when the vlans all show up as the same mac, I'm pretty sure that causes the flapping error.
I'm not 100% sure what the flapping error exactly is, but I don't really see what else could cause the error since it stops when I change the macs for the vlans.
-
Perhaps the load balance lagg/port channel in that switch is incompatible with the load-balance lagg in the Marvell chipset. Really hard to tell from here.
The port channel should allow input from any MAC on any of the ports at any time.
Are Po1 and Po2 in your OP members of the same port channel? Is the port channel properly-configured?
-
Your original post showed the MAC as switching between interfaces. That wouldn't normally happen with VLANs.