Isolate Guest Network on AP
-
Did you set up DHCP servers on each of the VLANs? I assume you have different SSIDs for the VLANs.
-
Correct - Vlan 50, enable DHCP, set IP Range, etc
Different SSIDs for the vlans as well.
can I connect any port from the AP to Port 7 on the switch?
-
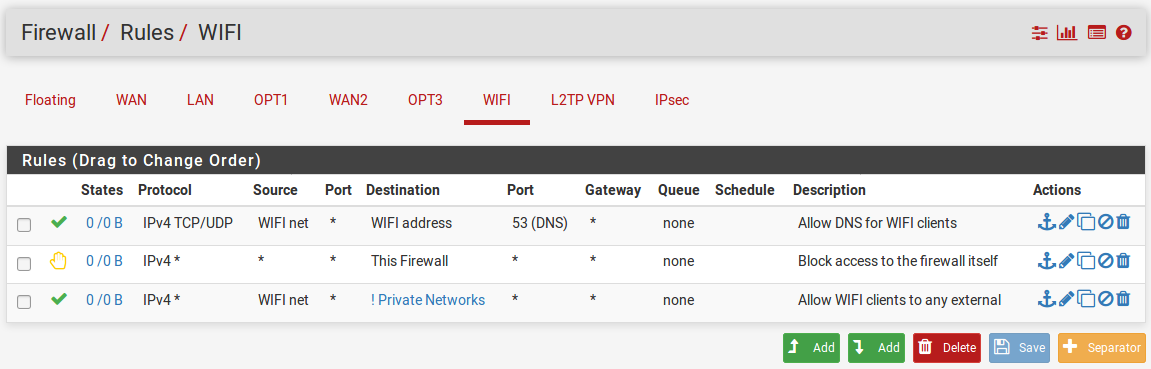
The ports connected to both pfsense and the AP have to be able to pass the VLANs. For example, my guest WiFi is on VLAN3. So, I configured VLAN3 on pfsense, my AP and on the appropriate switch ports.
-
In the switch you need those VLANs to be tagged on both the port connected to the AP and the port connected to pfSense.
And you need to remove port 7 from the default vlan, unless you have a third SSID there that's untagged.
However the fact you were still pulling an IP from the LAN subnet also suggests those new SSIDs are now using the VLANs correctly in the AP.
Can we see an ifconfig output from the AP?Steve
-
@stephenw10 Sorry I was wrong on that no IPs while connected to the ddwrt ap wireless.
Something still wrong with my config and trying to look at this as somewhat of a reference point - https://www.tp-link.com/us/support/faq/788/.
This is what I am after as a test ....
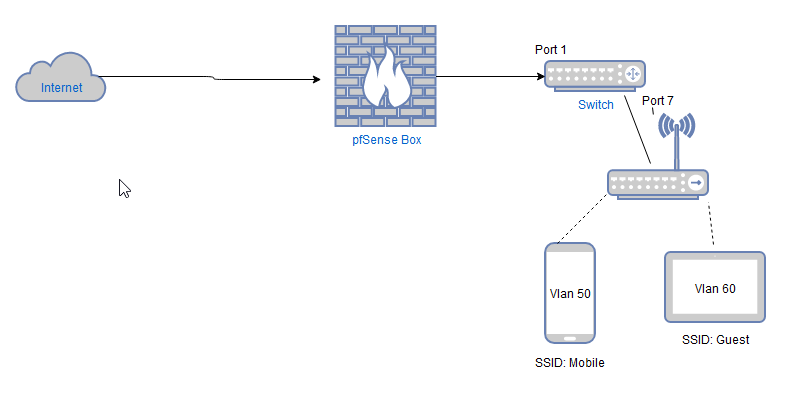
So Pfsense plugs into Port 1 on Switch.
Asus AP(DDWRT) plugs into Port 7 on Switch.Two Vlans setup on DDWRT
SSID: Mobile - Vlan 50
SSID: Guest - Vlan60 -
Yes, so the in the switch config VLAN IDs 50 and 60 need to have both ports 1 and 7 as members and tagged.
-
Ok got a step further and I have the Vlan60 working which would be my guest network.
So Vlan60 just needs internet access nothing else.
Right now I just have two rules in my test bed on this Vlan.
Allowing Vlan 60 clients Internet Access
Block Access to Lan when on Vlan60.
Allow Access within Subnet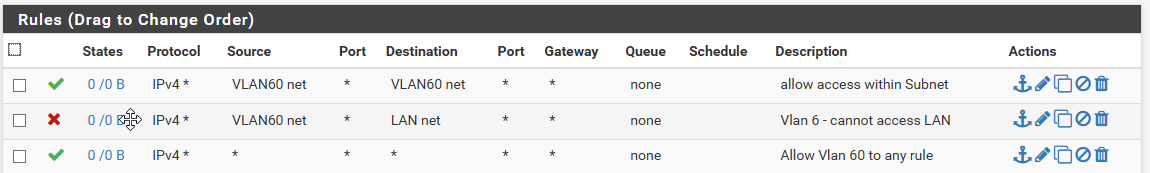
Am I missing anything on this?
-
Access between devices in the same subnet is not required, that doesn't go through the firewall.
Devices there may need access to the firewall itself (VLAN60 address) for DNS and NTP etc. Otherwise you probably want to block access the all other IPs on the firewall itself and all other local subnets.Something like this:
The Private_Networks alias there is just 192.168.0.0/16 in my case. If you have mutltiple subnets in an alias I would recomend using block then pass rather than pass invert like that.
Steve
-
@stephenw10
Great I will have to look into that a little later.Thanks for everyones help on this so far!
-
Wow way too much time spent on this lately but finally getting it to where I want it to be.
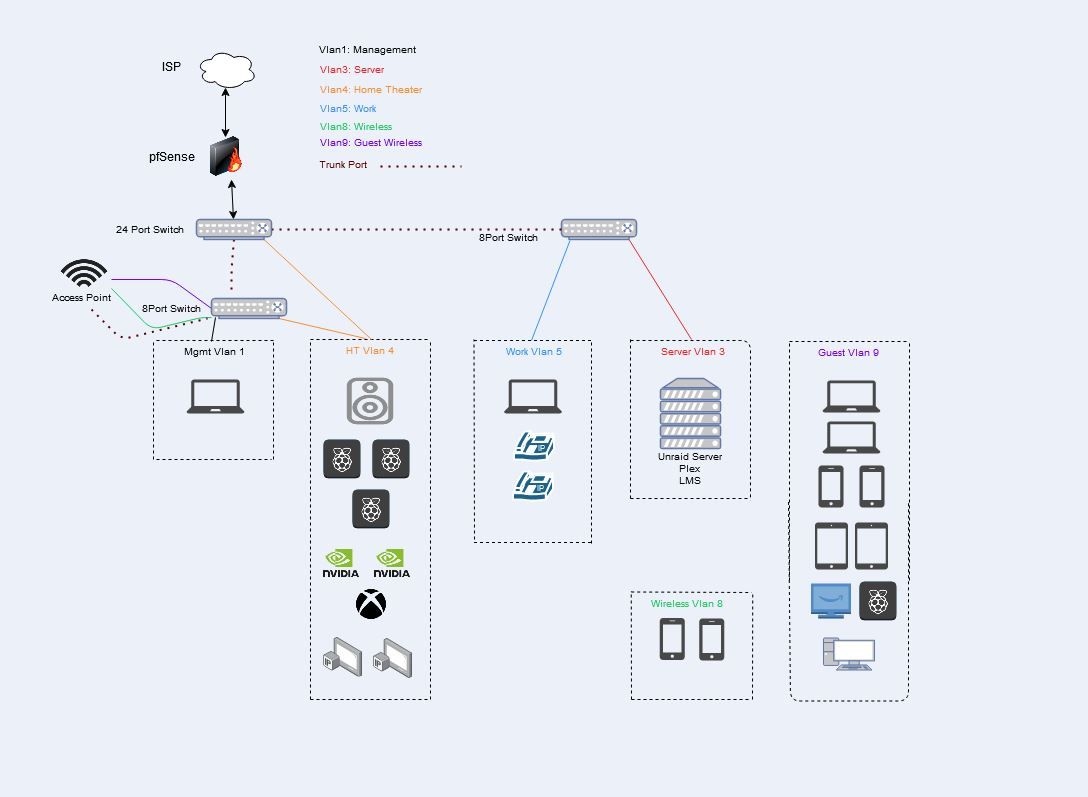
Vlan1: Management
This is the Lan off the pfsense firewall. It has access to pfsense gui, all switches, ap, vlans.Vlan3: Server
Unraid server running plex, LMS, a few other things
Allowed: pfBLockerNG, DNS, Plex to HDHomeRun tuner on Vlan4, Internet
Blocked: Firewall & Internal communication.Vlan4: Home Theater
Denon Receiver, (3) piCorePlayers, (2) Nvidia Shields, Xbox, (2) HDHomeRun Tuners
Allowed: pfBLockerNG, DNS, Plex players to Plex on unraid, piCorePlayer to LMS on unraid, Internet
Blocked: Firewall & Internal communication.Vlan5: Work
Work laptop, (2) VOIPs
Allowed: pfBLockerNG, DNS, Internet
Blocked: Firewall & Internal communication.Vlan8: Wireless
(2) Iphones
Allowed: pfBLockerNG, DNS, Internet
Blocked: Firewall & Internal communication.Vlan9: Guest Wireless
(2) Chrome books, (2) iphones, (2) kindles, PicorePlayer, roku, PC
Allowed: pfBLockerNG, DNS, Internet
Blocked: Firewall & Internal communication.Equipment:
Pfsense box: HP Intel(R) Core(TM) i5-2400 CPU @ 3.10GHz, 16 gigs of ram, HP 4 port ethernet card - Packages running: aprwatch, iperf, nmap, ntopng, pfBlockerNG, RRD_Summary, Status_Traffic_Totals, TelegrafAccess Point: Netgear R7800 running Openwrt
Switches: TP-Link TL-SG1024DE, (2) TP-Link TL-SG108PE
Server: ASRock X99 Extreme3, CPU 2GHz 12 cores(24 HT), 32gigs ram
Unraid
Parity Drive: 4tb
15TB HD Space
Cache Drive for Dockers
Unassigned drive for VMs (Windows, Hassio, Linux)Things still testing:
Iphone control while on Vlan8 to items in Vlan3(plex), Vlan4(Receiver, PiCorePlayers, Shields, Roku).Verify anything in Vlans 3+ can't get to pfsense box, switches, APs, Server.
I am sure I am forgetting something.