Only Some of my Port Forwards work ?
-
Starting to define the definition of insanity.
I have a phone system just installed and was given a list of ports that need forwarded to the phone system. However only half of them work ? I have deleted them, re-entered them, and they are identical to the working ones.
List of ports needed :
9300 - 9300 to 10.10.1.25 Closed
24493 to 2728 to 10.10.1.25 Open
16000 -16511 to 10.10.1.16 Closed
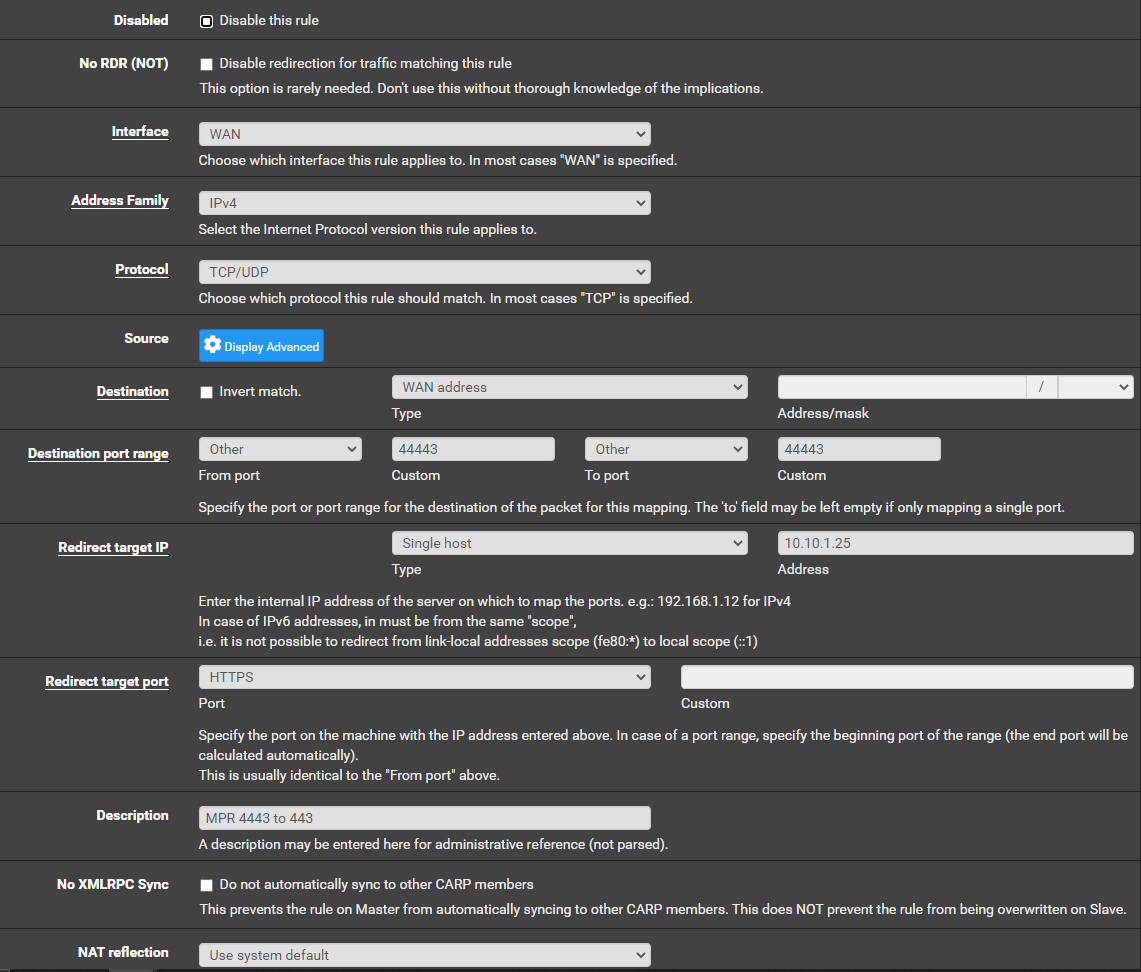
44443 to 443 to 10.10.1.25 OpenThe conversion ports for whatever reason work, but the port to port do not ?
PFSense 2.5.1 (Just upgraded it and made no difference.
Where to go from here ?
-
-
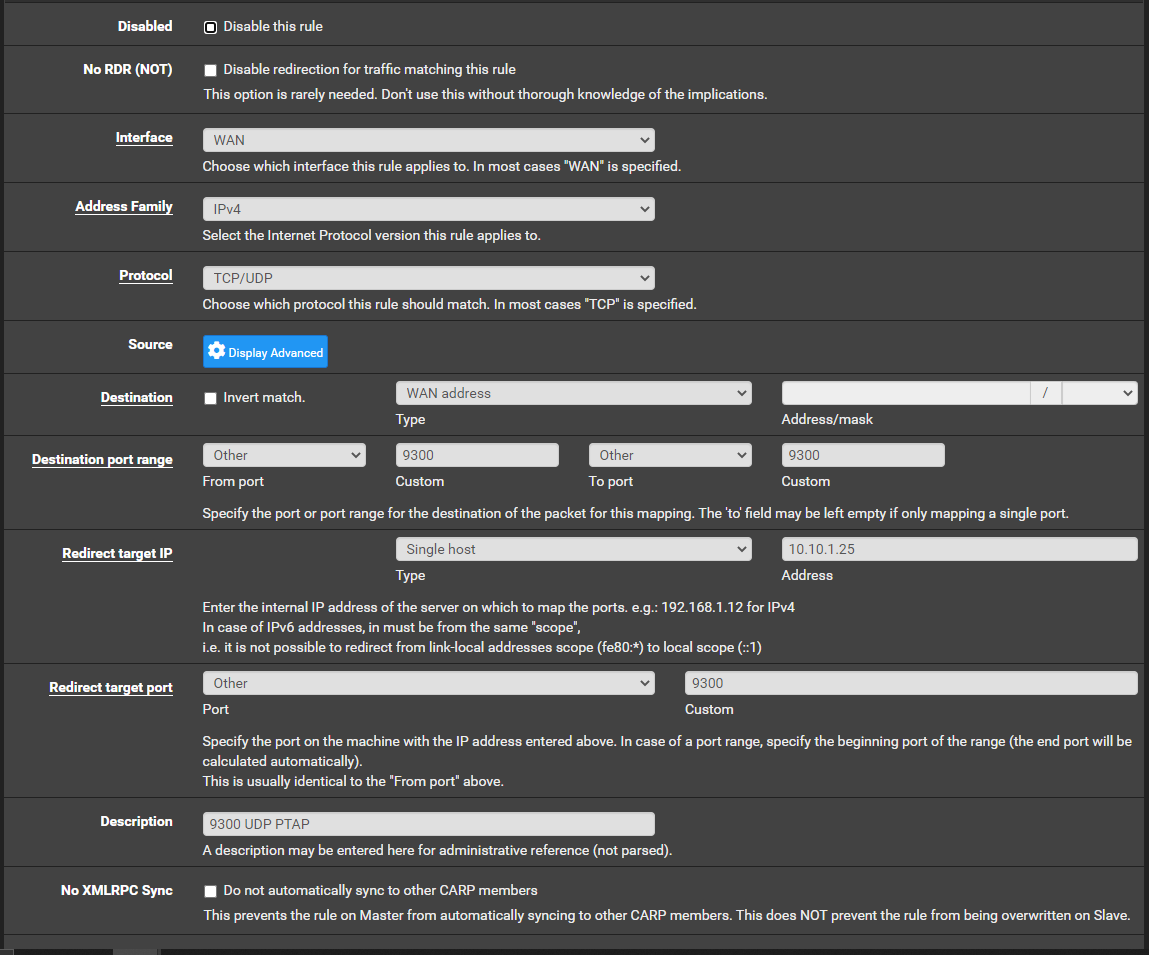
This one is not working.
-
Are you providing a VOIP server locally?
If the phone is local and the VOIP server remote you shouldn't need any sort of port forwards, I have a VOIP phone local and don't have any port forwards.
-
@nogbadthebad From my understanding the phone server is on site (Some Panasonic System) and the phone is off site (Cell Phone). Backwards in my opinion, but I believe they want to have a business phone in another location. I would use a server off site, not sure what he was sold or why.
This port forward is squeezing my brain though.
-
@cire3 Try killing the firewall states.
Diagnostics -> States -> Reset States
-
@nogbadthebad Yea, just tried that a little bit ago. Same issue.
-
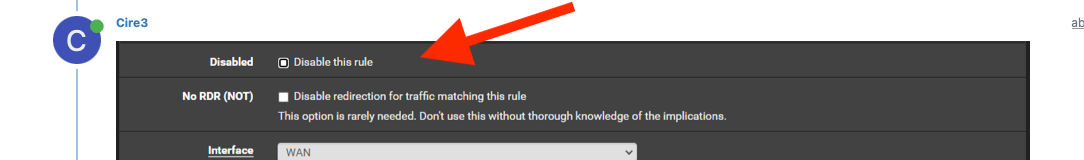
Those rules aren't disabled are they, there is a mini square in the tick box ?
I don't use that colour scheme.
-
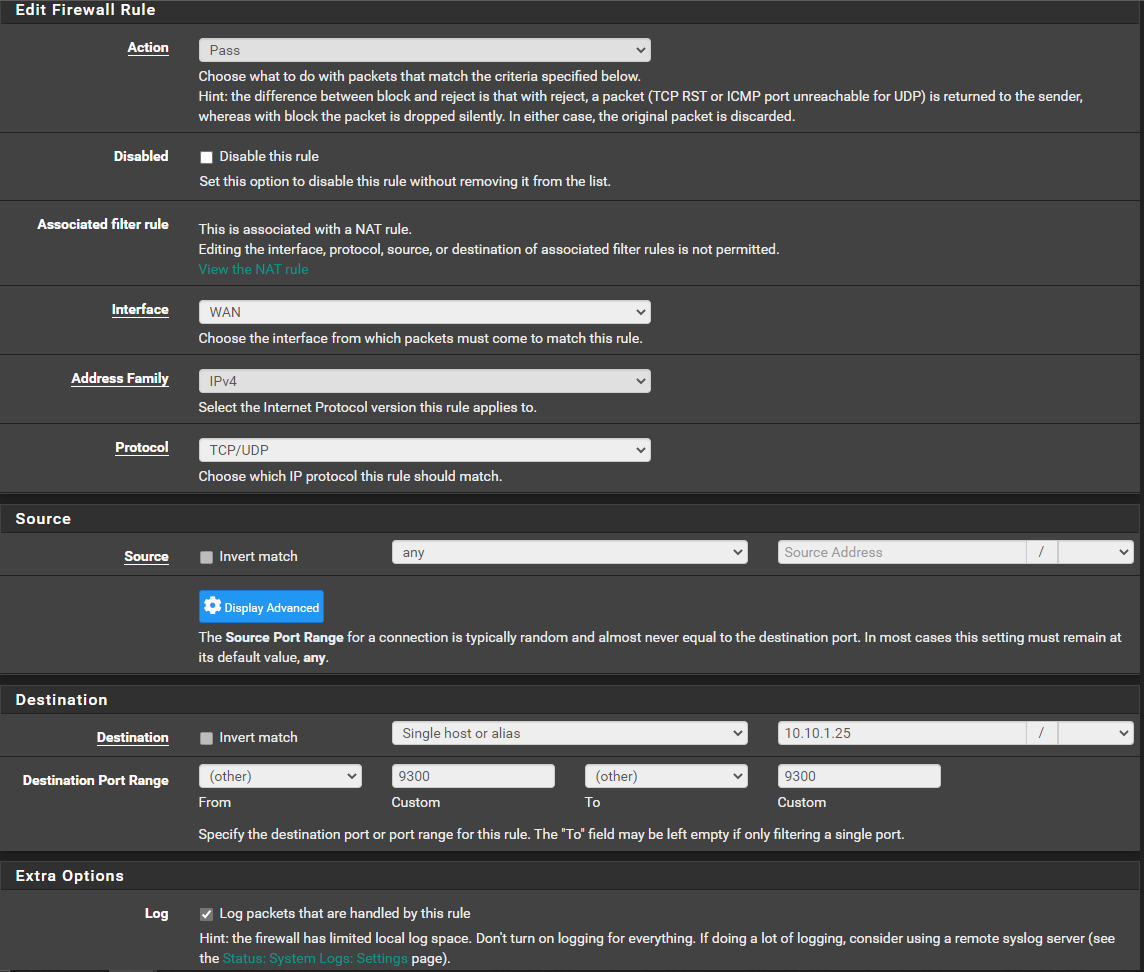
My 9300 rule that auto populated when setting up NAT Port Forward
-
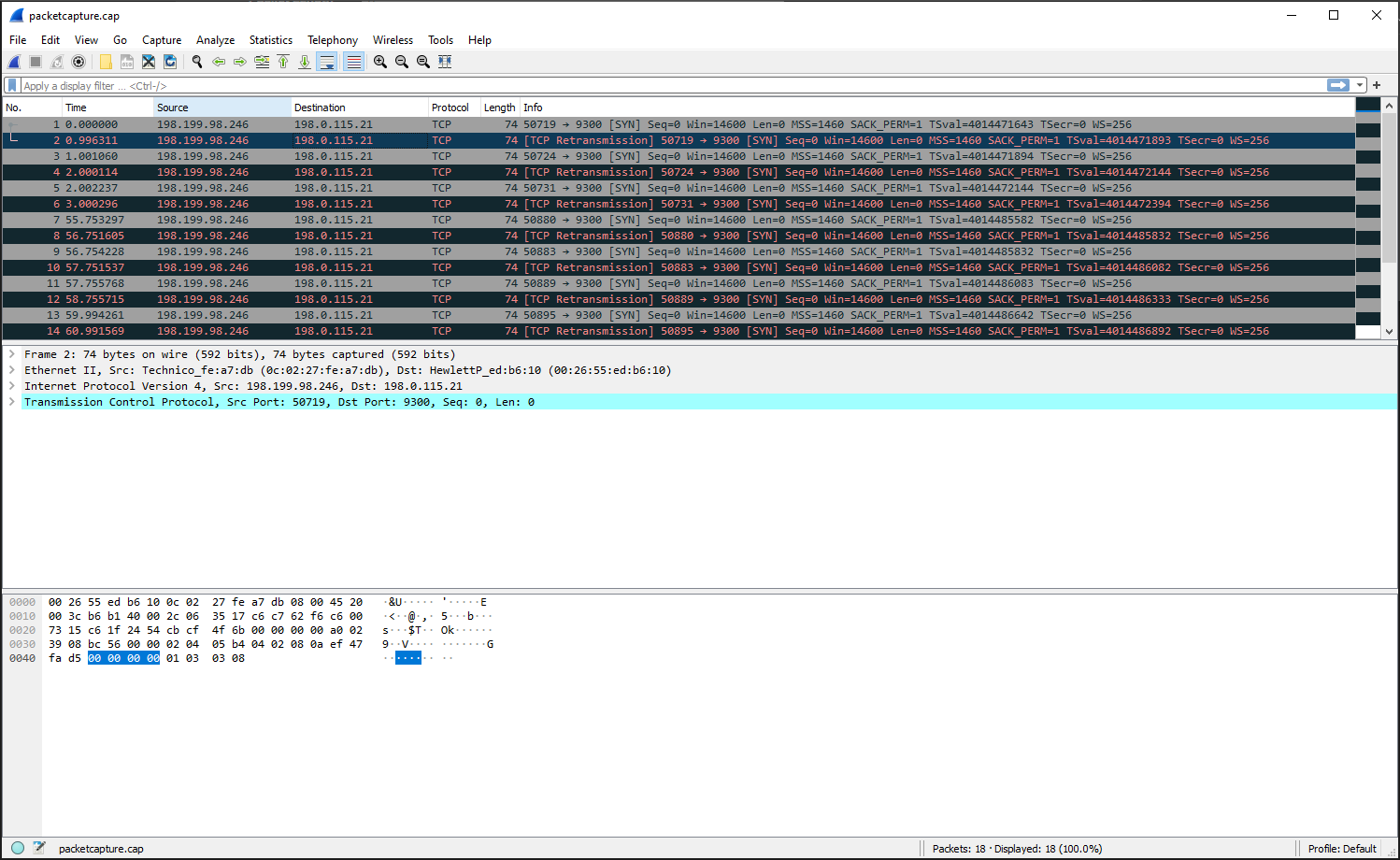
@cire3 I'd start doing a packet capture on the WAN interface to see if the packets are hitting the WAN interface, maybe the ISP is blocking some of the ports.
Also I was talking about the NAT rule with the mini square not the firewall rule.
-
@nogbadthebad said in Only Some of my Port Forwards work ?:
packet capture on the WAN
Sorry, thought you wanted rule, as I already posted the NAT Forward rules. My bad. However I double checked.
I'm connected over VPN, and know enough to be dangerous...lol Any way I can packet capture on the WAN remote ? Never had to do this.
-
@cire3 yup have a look at the diagnostics section.
You can download the packet capture from the page and view in wireshark.
-
@nogbadthebad Just seen it after I asked the question. Way cool. Downloading now after trying to check port.
-
@cire3 Host address being my Static WAN ? And should I use a port or just capture?
-
And this from PFSense :
15:25:00.282522 IP 198.199.98.246.50719 > 198.0.115.21.9300: tcp 0
15:25:01.278833 IP 198.199.98.246.50719 > 198.0.115.21.9300: tcp 0
15:25:01.283582 IP 198.199.98.246.50724 > 198.0.115.21.9300: tcp 0
15:25:02.282636 IP 198.199.98.246.50724 > 198.0.115.21.9300: tcp 0
15:25:02.284759 IP 198.199.98.246.50731 > 198.0.115.21.9300: tcp 0
15:25:03.282818 IP 198.199.98.246.50731 > 198.0.115.21.9300: tcp 0
15:25:56.035819 IP 198.199.98.246.50880 > 198.0.115.21.9300: tcp 0
15:25:57.034127 IP 198.199.98.246.50880 > 198.0.115.21.9300: tcp 0
15:25:57.036750 IP 198.199.98.246.50883 > 198.0.115.21.9300: tcp 0
15:25:58.034059 IP 198.199.98.246.50883 > 198.0.115.21.9300: tcp 0
15:25:58.038290 IP 198.199.98.246.50889 > 198.0.115.21.9300: tcp 0
15:25:59.038237 IP 198.199.98.246.50889 > 198.0.115.21.9300: tcp 0
15:26:00.276783 IP 198.199.98.246.50895 > 198.0.115.21.9300: tcp 0
15:26:01.274091 IP 198.199.98.246.50895 > 198.0.115.21.9300: tcp 0
15:26:01.277837 IP 198.199.98.246.50897 > 198.0.115.21.9300: tcp 0
15:26:02.273897 IP 198.199.98.246.50897 > 198.0.115.21.9300: tcp 0
15:26:02.278893 IP 198.199.98.246.50899 > 198.0.115.21.9300: tcp 0
15:26:03.277951 IP 198.199.98.246.50899 > 198.0.115.21.9300: tcp 0 -
@cire3 OK so it looks like 9300 is hitting the WAN interface.
-
@nogbadthebad Yea, It would have been great to blame Comcast. Not today I guess...lol
-
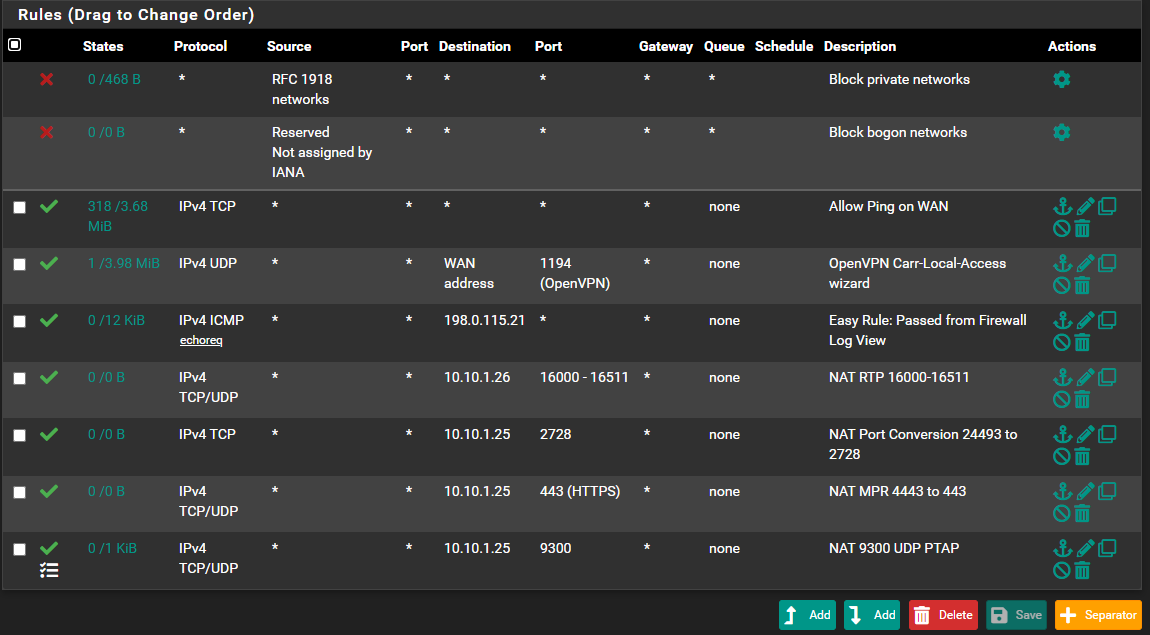
Figured I would post in case something didn't look right
-
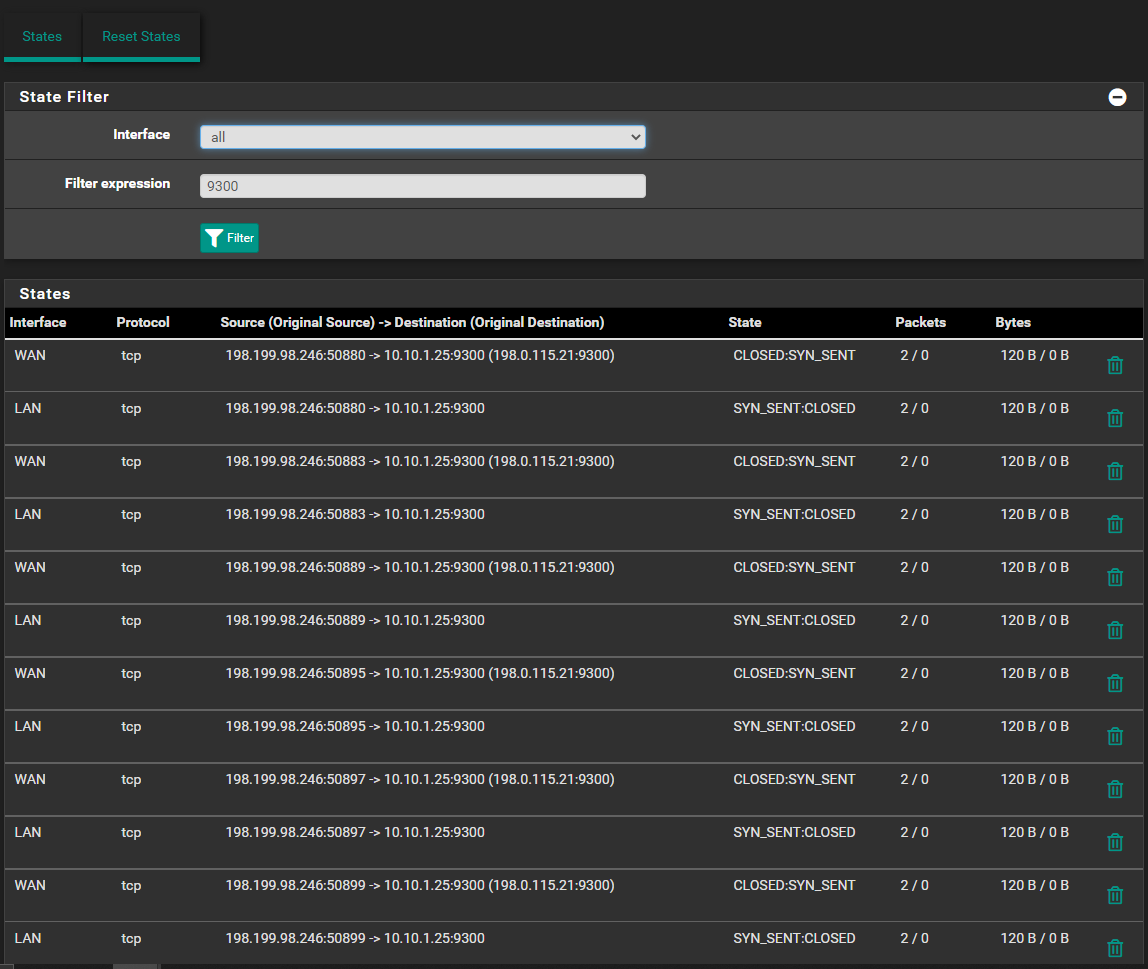
This is what's back in states
-
@cire3 Rules are read from the top down, I suggest you have a read:-
https://docs.netgate.com/pfsense/en/latest/firewall/rule-list-intro.html
Everything TCP will hit the 3rd rule down.