Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?
-
I am unsure why this would be the case. If someone could shed some light on this, I would greatly appreciate it.
-
@code4food23 Perhaps pfBlocker updating its tables. Any fqdn's used in an alias are resolved every 5 minutes or so.
-
@kom I see. So this is normal? I also see some to other countries, such as VN, AT, UK, etc, but its always coming from 127.0.0.1 (which is unbound, correct?).
I was beginning to worry I had rogue devices.
-
@code4food23 Yes, that's Unbound. You have other packages like Snort or Suricata installed which may be doing the requests, or it might be pfB.
-
@kom said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
@code4food23 Yes, that's Unbound. You have other packages like Snort or Suricata installed which may be doing the requests, or it might be pfB.
It won't be Snort or Suricata. Everyone likes to blame those packages for DNS lookups, but they don't lookup anything except during the rules update cron task when they use
curlto check for and download the latest rules. Those lookups go to snort.org and emergingthreats.net (typically).The IDS/IPS packages do not perform DNS lookups on analyzed traffic. They have no need to ever do that.
-
@bmeeks i see..so if not those, then why would unbound be reaching out to those foreign domains?
-
@code4food23 said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
@bmeeks i see..so if not those, then why would unbound be reaching out to those foreign domains?
Because something asked
unboundto do that. Could be a client on your network. That is the most likely cause. Perhaps it is some app installed on smartphones that is phoning home or otherwise checking in? Based on the names of a couple of those domains, they appear to be mobile phone networks.The default setup for pfSense is to have DHCP running on the LAN and for the DHCP server to hand out the firewall as the DNS server for clients. So clients will ask your firewall's LAN IP (where
unboundis running) to lookup DNS names.unboundwill then, in turn, traverse the DNS root servers to find the answer and then send it back to the client. The log entries you see areunbounddoing the DNS resolving on behalf of some client request. -
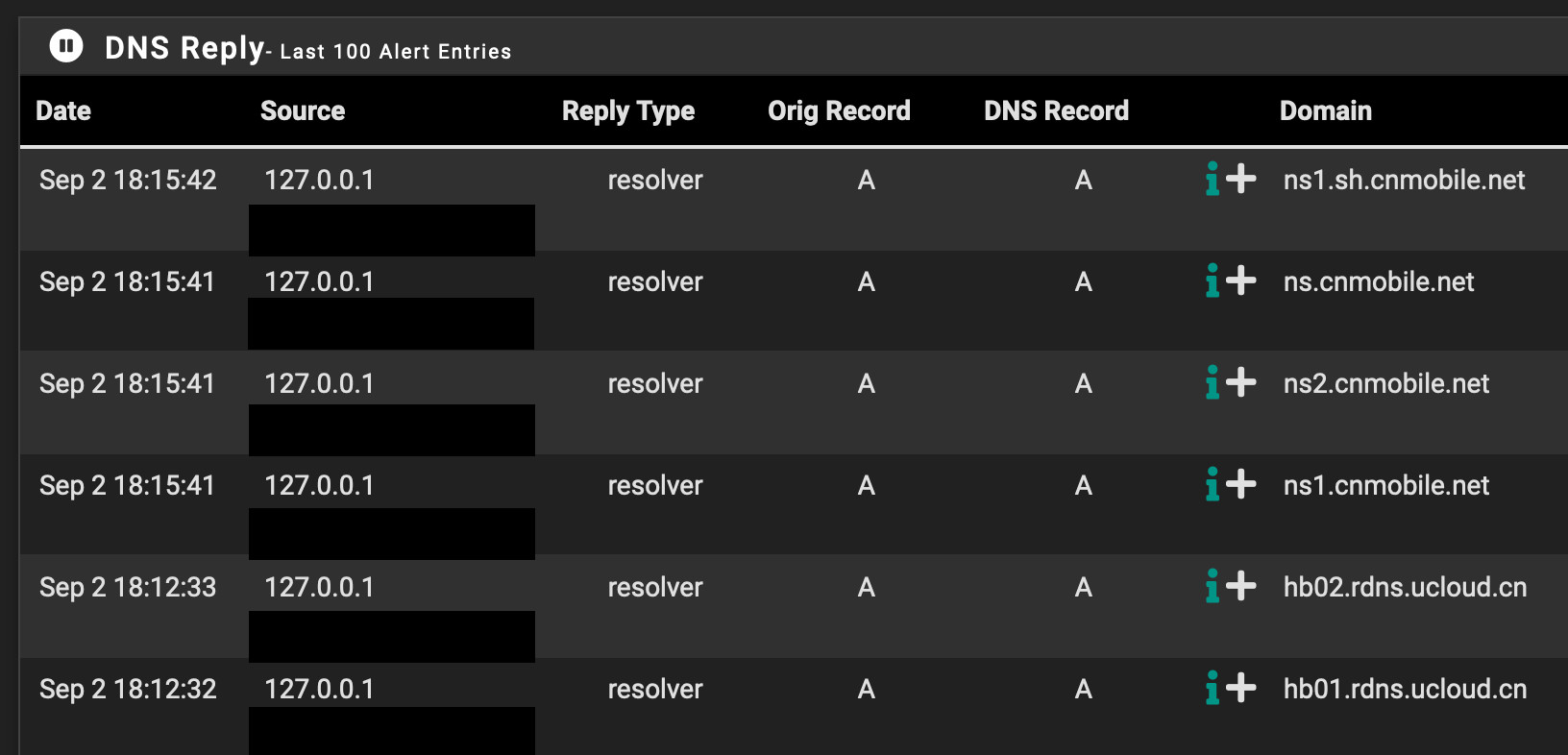
@bmeeks I see. Now that is very worrisome. Throughout the day the only devices connected were my raspberry pi and a ring cam. I've only started checking the logs recently so hard to say. But I just filtered for CN and was surprised.
There are no unknown devices in my DHCP lease list nor on my Unifi conroller that is running on my Pi.
I do not have any ports either, has my network been compromised?
-
@code4food23 said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
@bmeeks I see. Now that is very worrisome. Throughout the day the only devices connected were my raspberry pi and a ring cam. I've only started checking the logs recently so hard to say. But I just filtered for CN and was surprised.
There are no unknown devices in my DHCP lease list nor on my Unifi conroller that is running on my Pi.
I do not have any ports either, has my network been compromised?
Can't say. Those are DNS name servers (the ns* values) for cnmobile.net, and the other lookup is some kind of cloud services provider based in China. This could simply be from some add on a web page opened by a client. It doesn't automatically mean you are compromised, or that there are rogue devices on your network.
You can use the packet capture capabilities of pfSense, along with additional
unboundlogging, to see what client on your LAN is responsible for the lookups. -
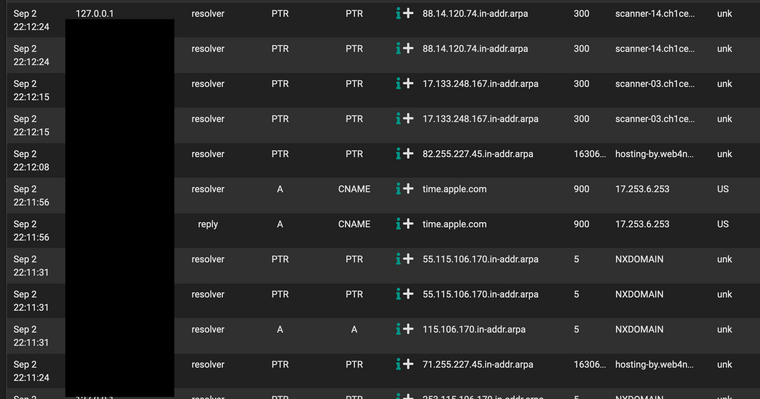
@bmeeks Thank you so much for taking the time to respond. I am now noticing even more strange behavior and have no idea what to do exactly..
Except for the apple.com, all of the rest are from unbound.
What could be going on?
-
@bmeeks Hope you are able to help. I saw the following

Thing is, I dont have anything on 10.10.10.1 that I know of, but I can ping it.
-
This post is deleted! -
@code4food23 @bmeeks disregard the comment about 10.10.10.1. Just realized the the DNSBL webserver virtual IP.
Nevertheless could you or someone please shed some light on the above PTR records being resolved to scanner-xyz domains
-
I see al kind of resolving in my DNS system.
Especially my Mailserver is resolving weird names.Whenever a "remote" is opening a connection to the server ( being a legal mail , spammer or scanner) the Mailserver tries to be nice , and reverse resolve the ip to the DNS name , for better log visibility.
That is in this case not dangerous , just informative.
/Bingo
-
Isn't the default configuration of unbound (at least in pfSense) set for a caching server? Basically clients get configured to talk to Unbound on the firewall as the DNS resolver, unbound goes out to the "internet" to satsify the request. I believe the default DHCP server config on pfSense hands out itself for the DNS server.
If so, and you are handing out DHCP from pfSense, anything that got a DHCP lease from your pfSense box could have made those requests and unbound is simply caching them.
Do you have iOT things on your network, like Ring doorbells, Nest thermostats, etc? It is possible something like that is making the request.
A packet capture is about the only way to figure it out, but you need to look at a lot of packets and the data inside them.
Maybe doing a whois on one or two of the names will shed information.
-
@mer said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
and unbound is simply caching them.
When this option is set :
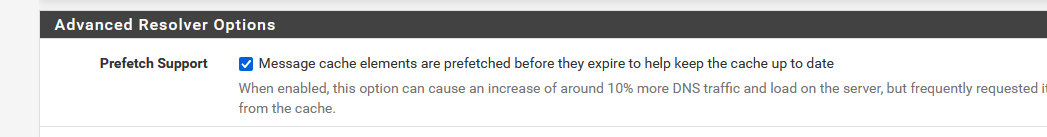
unbound will not prune the cache any more after TTL : it will refresh the content. So, ones a domain gets asked ones, it will stay there for future usage, as the TTL never reaches zero.
@code4food23 said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
Nevertheless could you or someone please shed some light on the above
It's easy to check what happens, and who does what.
You have a console port on your pfSense, use it.
If not, you have to use the SSH access - and keep the PC on which the SSH cients runs, connected to your LAN.
Now it comes : remove ALL other devices. No exception.DNS - unbound log traces will come to a complete halt, if you were using the console access, and nothing connected to your LAN's.
Unbound DNS traffic logs will only mention the what your PC is doing - if you have this one connected to your LAN if you were using the SSH client.Now, add one by one LAN based devices. DNS traffic accelerates.
Another side effect is the usage of CNAME DNS requests. Ubound (pfBlockerNG) will fetch them, and then fetch all of the possible domains the CNAME points to. because, if a device fetches a CNAME, it will also pick one domain and use it. By that time, pfBlockerNG is ready to block it.
This creates some sort of snow ball effect.
@bingo600 said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:the Mailserver tries to be nice , and reverse resolve the ip to the DNS name , for better log visibility.
Be nice ?
Mine reverse the PTR the IP of the sender, and if he isn't who he says he is during HELO phase, he drops the line. -
@gertjan said in [Can someone help me understand why is unbound resolving foreign domains
Be nice ?
Mine reverse the PTR the IP of the sender, and if he isn't who he says he is during HELO phase, he drops the line.You would not be able to receive mail from me.
I have a "fixed ip" , but no control over my IP reverse pointer (ISP won't play) , as i'm part of a pool.My mail server name is not set to be my reverse pointer name (yet).
I have a setting , where i drop if i can't resolve the reverse ip at all./Bingo
-
@gertjan said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
unbound will not prune the cache any more after TTL : it will refresh the content
Not really how it works.. With prefetch set - if something asks for that and the ttl is close to expiring it will prefetch it before it expires which will up the ttl back to full. Its not like unbound is asking for everything in its cache that reaches X% of the original ttl.
prefetch: <yes or no> If yes, message cache elements are prefetched before they expire to keep the cache up to date. Default is no. Turning it on gives about 10 percent more traffic and load on the machine, but popular items do not expire from the cache.Notice "popular items do not expire.. But if you ask for something.tld, and then never ask for it again - it will expire.
# perform prefetching of close to expired message cache entries. If a client # requests the dns lookup and the TTL of the cached hostname is going to # expire in less than 10% of its TTL, unbound will (1st) return the ip of the # host to the client and (2nd) pre-fetch the dns request from the remote dns # server. This method has been shown to increase the amount of cached hits by # local clients by 10% on average.This is more useful in increasing your cache hit, and can show performance increase if you have something that takes a bit to resolve for whatever reason, because vs letting something expire that is asked for, and then having to resolve it. Once something gets close to expiring - it looks it up in the background - so that next time someone asks its still cached.
serve 0 ttl also very useful, since even if something has expired - it can still get served before looking it up. Since it returns the last entry and then looks it up so if changed, it will have new value next time asked for.
Min ttl also handy - when you have stuff that has really low ttl in reducing number of times something has to be resolved. If something has ttl of 60, vs having to resolve that all the time you can set a min ttl of say 3600.. Now that will only be resolved every hour, even if something asking for it every 5 minutes.
-
@johnpoz said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
@gertjan said : unbound will not prune the cache any more after TTL : it will refresh the content
I'll (should have) add two words :
unbound will not prune the cache any more after TTL reaches zero : it will refresh the content
.@johnpoz said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
and then never ask for it again - it will expire.
Then that was me misunderstanding.
unbound maintains a "popular" indicator ?! (I just earned a visit to the source code repository to find out ;))
I understood that, for any TTL reaching zero, and prefetch is active, it will refresh.
This implies an that cache will steadily grow over time. Humm, that's good and very bad.
Thanks for the info.edit : for @code4food23 : What I meant to say was : ones you connected your device with "'foreign origins" to your network, you will introduce traffic related these origins in your network. even if you remove them, some related traffic still persists.
@johnpoz makes it clear that this traffic will fade out over time. -
@mer said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
Basically clients get configured to talk to Unbound on the firewall as the DNS resolver, unbound goes out to the "internet" to satsify the request.
Would unbound also try to satisfy requests made by services like pfblocker and suricata? Idk about those scanner-* domains but i saw i have a dnsbl for abuse ch and oisd nl.
@mer said in Can someone help me understand why is unbound resolving foreign domains (e.g. China)? Is this normal?:
Do you have iOT things on your network, like Ring doorbells, Nest thermostats, etc? It is possible something like that is making the request.
I do have two ring cameras. I think i ruled the rasberry pi and tv because I disconnected those and still kept seeing unbound resolve these odd domains.
Could this be a sign that they are compromised?