Please help me to get it floating quick vs Interface rules
-
Hello all,
Please show your generous teaching for poor me.
So far, what I understand is:
a. Interface rules are including 'quick' function as default.
b. Rule orders are: Floating quick - interface group - interface
c. without Floating quick, rules in floating tab are applied very last match. (final match)Before I explain, I don't have WAN interface, this firewall is generally using for internal traffic control. In this case, LAN port is connected to Core switch, ServerZone port is connected to Servers. I'm trying to protect incoming Server traffics.
so I create rules like below:
a. There is nothing in floating rule. (Empty)
b. LAN interface rules. (Allow All traffic from Core switch flows to LAN, SERVERZONE)
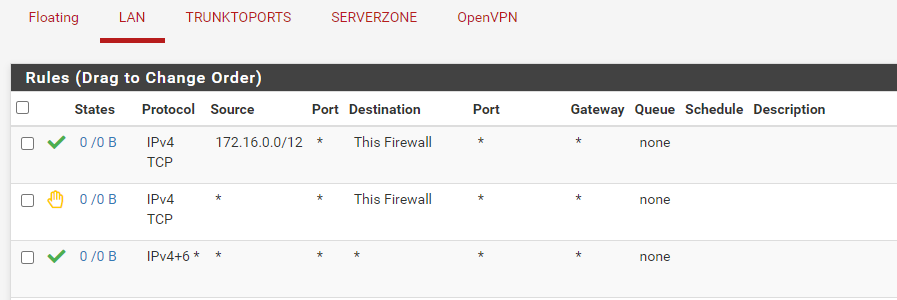
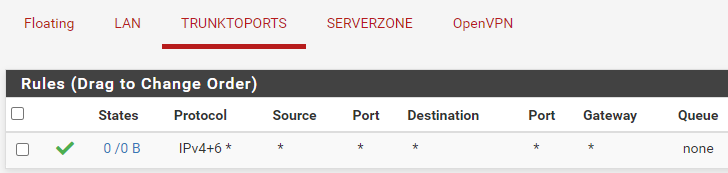
c. TRUNKPORTS = Bridge between LAN(has IP address)-SERVERZONE (No ip address)
d. ServerZone rules (Allow all inbound traffic)
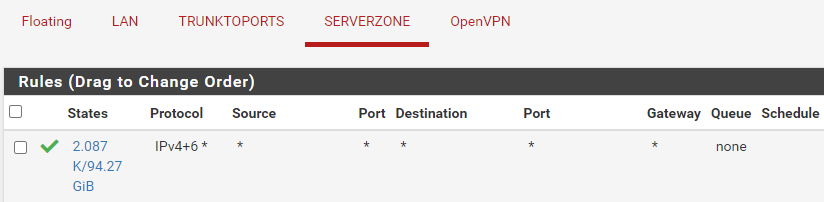
However, when I put allow all rules like upper a-d, Servers from ServerZone can send packet to outbound (which means can contact to Core switch, I have checked on States) but opposite is blocked.
This problem is solved when I make a floating quick rule.
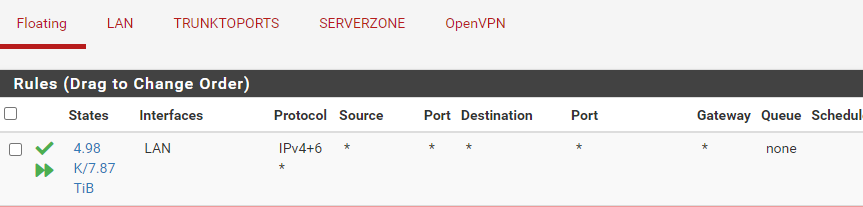
Can anyone explain why I have to create floating quick rule? I thought just creating allow rules on interface port (except floating quick) is enough to communicate.
I am a super beginner, so please give your opinion easy way.
I appreciate your reply.
-
@eeebbune said in Please help me to get it floating quick vs Interface rules:
TRUNKPORTS = Bridge between LAN(has IP address)-SERVERZONE (No ip address)
Huh?? If you have lan and server networks, why would you also bridge them?
ServerZone rules (Allow all inbound traffic)
Inbound to what, the interface yes.. But rules on that interface have nothing to do for inbound from other networks into the servernetwork
Traffic is evaluated as traffic enters an interface from the network its attached to... That rule you have on serverzone would have to do with stuff on the serverzone network talking outbound to something other than serverzone.. That rules has nothing to do with say something on lan wanting to talk to serverzone..
-
Hello Johnpoz,
The bridge is for making trunk port.
ServerZone port is connected to L2 switch for several server connections so I have to create the interface port to trunk. (I gave the VLAN tag information to serverzone port)One more question, how can I understand about serverzone network?
Actual serverzone interface port doesn't have IP / network range. they only knows about vlan tag number. Can I take the serverzone network means actual server's IP addresses? -
@eeebbune said in Please help me to get it floating quick vs Interface rules:
The bridge is for making trunk port.
Bridge has nothing to do with making a trunk port.. Running multiple vlans over a port or even a lacp connection (multiple ports) has nothing to do with creating a bridge in pfsense - nothing!
-
Really..? so, If I remove bridge between LAN - SERVERZONE interface port and just giving multiple vlan tags are enough to make trunk port, am I correctly understand?
-
Wait, the rules in serverzone is nothing to do with outbound (other than serverzone), than what does my allow rule mean? I thought (any) to (Serverzone, traffic goes to server) is allowed.
-
@eeebbune said in Please help me to get it floating quick vs Interface rules:
am I correctly understand?
You would create a "trunk" port by putting vlans on specific interface.. Example you see my interface igb2, it has 3 networks on this "port/interface" it has my wlan which is 192.168.2/24 and then 2 vlans 4 and 6. which are 192.168.4/24 and 192.168.6/24
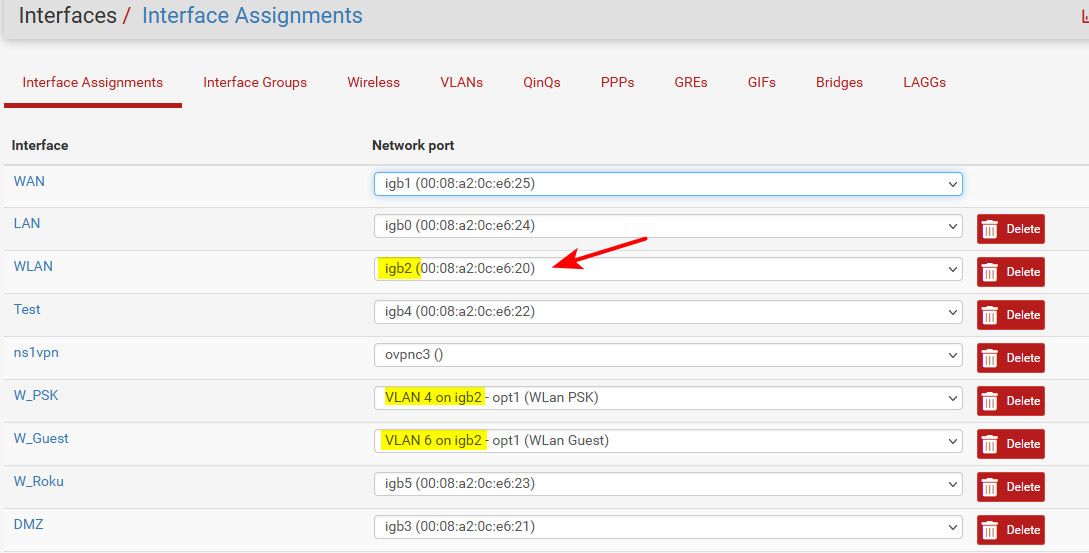
This is connected to a switch port, that is configured as "trunk" which allows for vlan (2) in my case this configured on the switch only.. Pfsense has no idea about his vlan ID because to pfsense this is an untagged vlan, just native directly on the igb2 interface.
In the case of vlans 4 and 6, pfsense knows about them and they ride on igb2, and tagged 4 and 6. The port on the switch is setup for vlan 2 to be the native and pvid vlan, and vlan 4 and 6 are tagged.
interface gigabitethernet5 description "sg4860 WLan and vlans" switchport trunk allowed vlan add 4,6 switchport trunk native vlan 2There is no "bridge" in pfsense..
-
Aha, now I get it clearly.
Do you have any rules in W_PSK, W_Guest?
if I create rule to W_PSK (VLAN4 on igb2), then packets which has tag#4 got caught and passing/blocking by rule? -
@eeebbune Yeah I have rules on all of my interfaces to prevent them from talking to stuff.
Example here is my guest rules
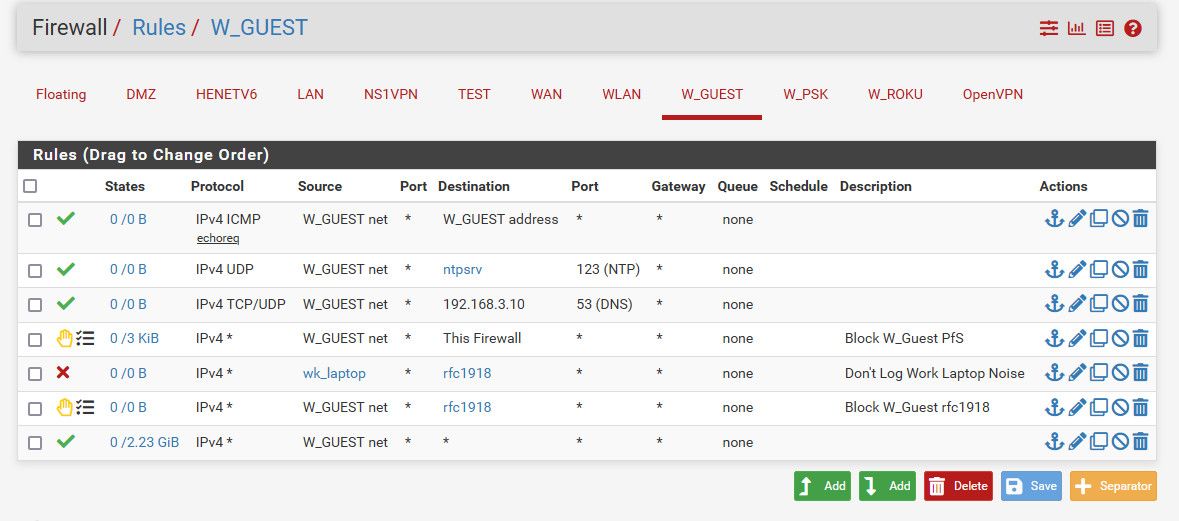
Yes your switch would tag the vlans towards pfsense.
-
I appreciate from the bottom of my heart.
I will change the configuration and check the server communication again.Thank you so much.
-
@eeebbune Any questions - please just ask, here to help!