Web Site whitelist
-
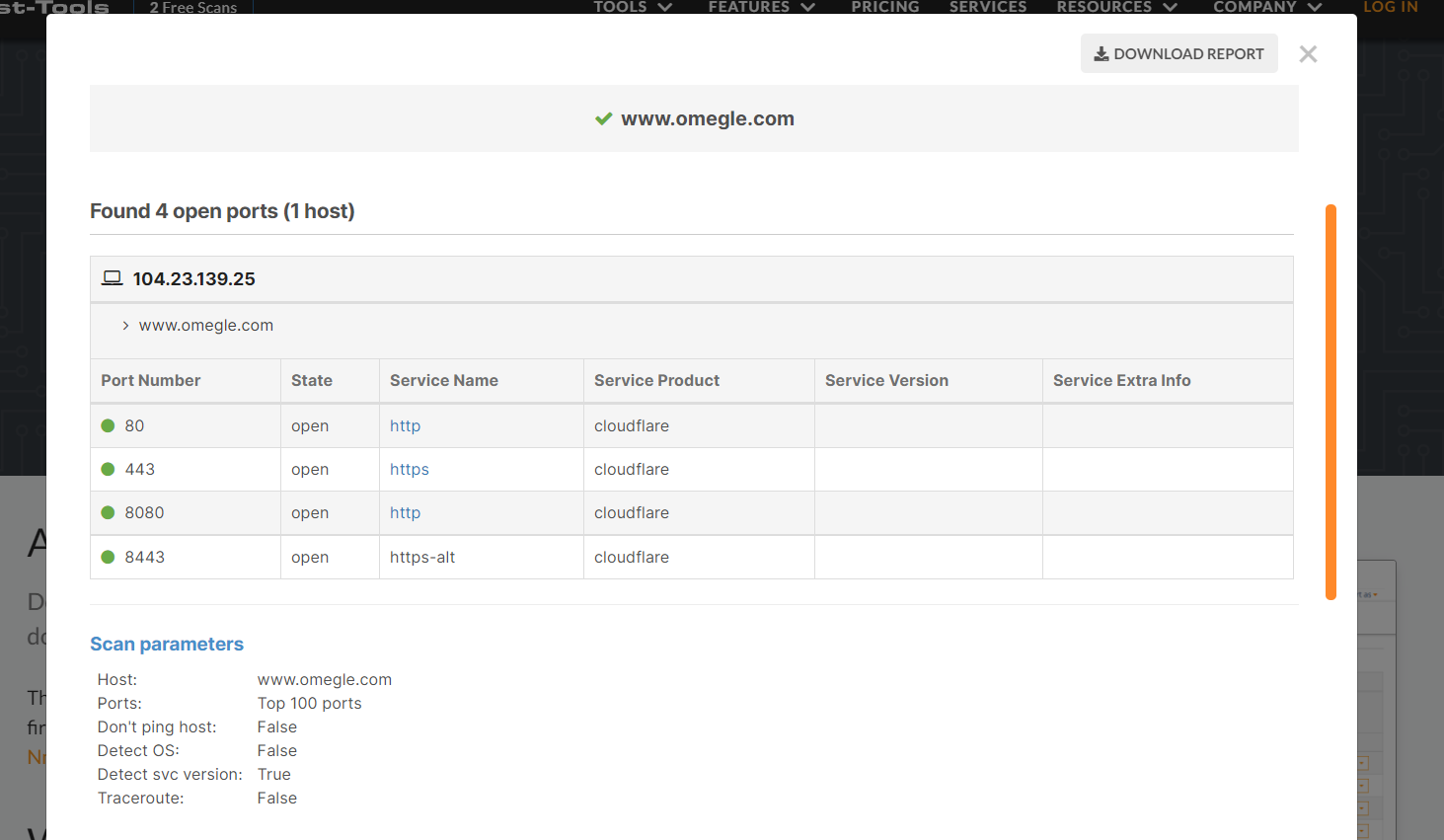
@natethegreat21 I was able to pull this from a port scanning site and tested the ports on the Diagnostics / Test ports and its says they all pass so I'm just more lost.
-
Again : pfSense is not blocking 'some ports' to some random destinations..
I advise you not to scan ports on "some" cloudfare servers. They protect their servers, and what do they do with IP's - for example your WAN IP - if they detect some one is scanning ? The same thing you would do : you will blocked the scanner. Cloudfare is equipped with such a protection.
@natethegreat21 said in Web Site whitelist:
and looking at the logs it looks like it may be blocking
Firewall rule don't rule dice.
It a pass or no pass.
What did you saw when you looked at the logs ?
The only traffic that might get blocked is incoming traffic on your LAN interface.
The default LAN firewall rule is "a pass all traffic" rule. -
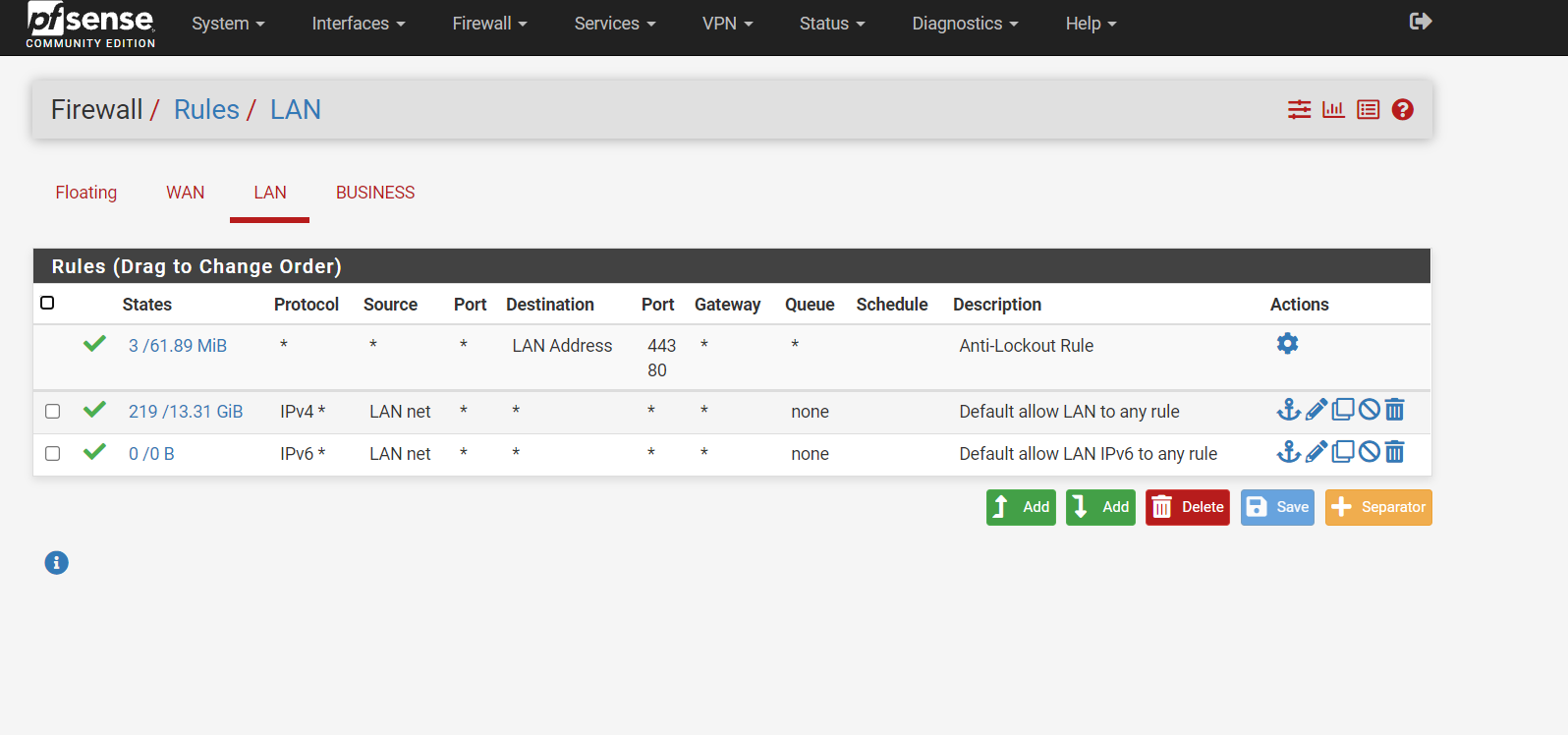
@gertjan Understood. Please see the LAN rules attached below.
-
You LAN is not blocking.
-
@gertjan So what do you think is causing me to not be able to see video feeds? The only happens on the PFsense network so obviously, there is something going on.
-
I don't use Omegle.
Some one is filtering upstream ?
-
@gertjan said in Web Site whitelist:
Some one is filtering upstream ?
Yeah I don't use that site either - but, video comes from where - the person your chatting from. If so then your pulling it from them, not some central site. Its quite possible there is issue/block between where the video is coming from and you.
Or if their service does do mitm sort of video where both people flow through that service - maybe they are blocking your IP where the video comes from.
But unless you are using IPS on pfsense, those rules on the lan are not blocking anything.
The best way forward in troubleshooting this - is prob a sniff, do you see the request for the video feed. Do you get an answer, do you get a RST?
What fqdn or url is the video being requested from - possible dns related problem with resolving where the feed needs to be requested from.
-
@johnpoz I could post a Wireshark capture if that would help.
-
@natethegreat21 information is always the key to getting to the root of the problem.. But I do not use that website - nor do I have any desire to try and use it.
But sure we can look at the sniff and see what we see from a request and reply sort of thing.
-
@johnpoz I appreciate everyone's help. the concern is that I will be running into this issue with other sites and then I have a bigger problem. This is the only reason I'm even giving it a second thought.
-
@natethegreat21 well give another example then where you have this problem, that we can try and duplicate. I wouldn't touch that website to be honest.
-
@johnpoz This is the only site that I have noticed at this moment. I will just disregard this issue and raise another flag if I notice anything again. In regards to the other question I have about the AP do you have any suggestions? The Ap only gets about 100Mbps and I have noticed that it stops getting internet access at times and the only way to get it to come back up is to reboot the AP. I noticed in the logs its saying something about an attack at that IP.
-
@natethegreat21 well you sure and the hell not going to see 1g over wifi ;) Might be possible with ax and ax client that connect at high enough PHY... But unlikely currently for your client to be able to do that even if the router/ap could.
What specific device are you using for AP.. Nighthawk has lots of different models.. What is blocking what? Pfsense is blocking what exactly, or the AP is blocking something?
There is nothing to do in pfsense to tell it anything about some AP.. An AP bridges traffic from wifi to the wire.. Pfsense would see all the macs of all the different clients connected to that wifi.. As they use pfsense as their gateway, etc..
-
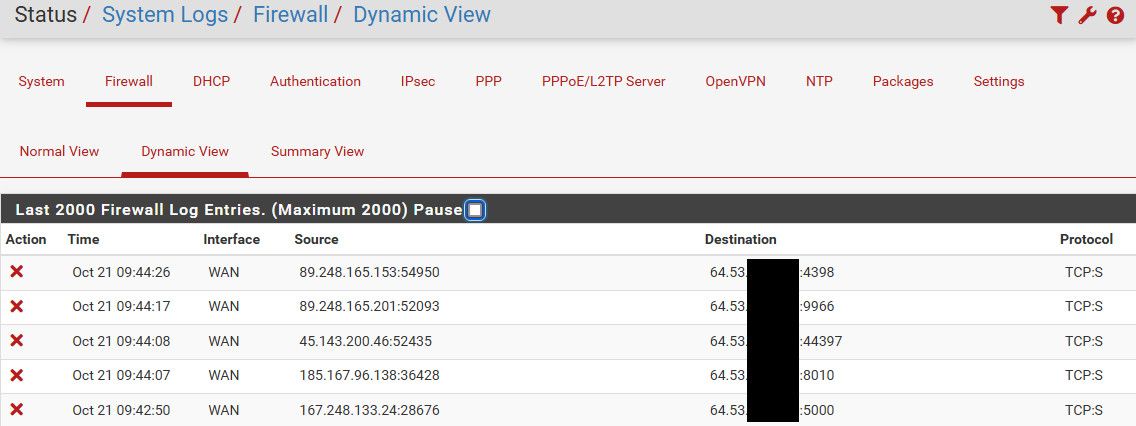
@johnpoz I know I won't get a gig over wifi haha. I have a Netgear AC1900 AP. I see a bunch of these for today in the firewall log for LAN and WAN: Default deny rule IPv4 (1000000103). Im not currently seeing the log for the block that I previously saw for the IP associated to the AP.
-
@natethegreat21 said in Web Site whitelist:
Default deny rule IPv4 (1000000103)
Yeah you for sure will see tons of those on the wan - lan should be far less, but what exactly is it being dropped by the default deny on lan?
Unless you have edited the default any any lan rule - really the only thing you should see dropped on lan is noise sorts of traffic - link-local sort of stuff ipv6 broadcast, etc.. Maybe some out of state stuff..
-
@johnpoz Its almost all on the WAN side.
-
@natethegreat21 well yeah - the internet is a very noisy place ;)
If you don't like seeing the noise, then create a block rule that doesn't log, below any port forwards you have, etc. If anything mine is lower amount of logs because I only log syn, and common udp ports.. All the other noise I do not log..
-
@johnpoz Thank you for the advice. I will set up some rules for it. Im thinking about switching the AP out with a Unify unit. What are your thoughts on that?
-
@natethegreat21 I run 3 different unifi AP (uap-ac-pro, -lite and -LR) for many years, and setup one (flexHD) at my son's house for him.. They work, have not had any issues with them.. Very stable.. not bad pricing, etc. etc.
-
@johnpoz Okay Im going to buy one. I appreciate all your help.