VLAN an Firewall rule not matching
-
@interessierter Please show us the blocks... And your rules - I want to see if there is any triggers 0/0 like you showed that none of those rules have matched.
-
@johnpoz its solved, its working after a reboot of pfnblocker
-
@interessierter said in VLAN an Firewall rule not matching:
@interessierter Hm after a restart of pfnblocker it works
The Part of DHCP is working now.
I got a xaomi vacuum cleaner, and this device needs WLAN to work fully. However I want to seperate this device from the rest of my network, but I strugle here.I have created vlans, a seperate WLAN SSID, and tag this SSID of VLAN ID 4000. This is configured on the switch between, the AP and the pfsense. But right now all other devices are NOT tagged with vlans, I have to do that step by step. However I want to start with the new xaomi device.
What I want to do is, to allow on the VLAN 4000 only Internet access, but DENY all access to my existing network infrastructure. I have tried several DENY rules on pfsense, but the access is still possible.
How should such a rule look like to work?
thanks -
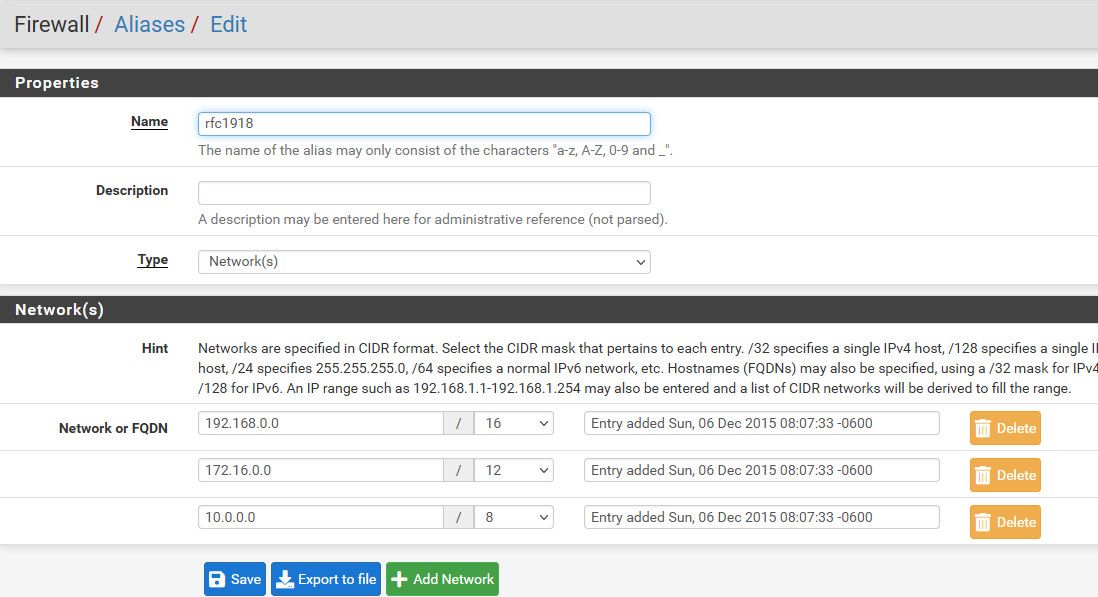
@interessierter here is a typical common configuration for a locked down vlan

Create an alias that contains all the rfc1918 space, this way as you add more vlans you don't have to worry that they would not be blocked.
Certain services are normally required like dns, etc.. But if the device points to outside for dns, you could remove that, same with ntp, and if you don't want it to ping its gateway.
But this is a very limited vlan setup. It can not talk to anything on local networks, only internet
-
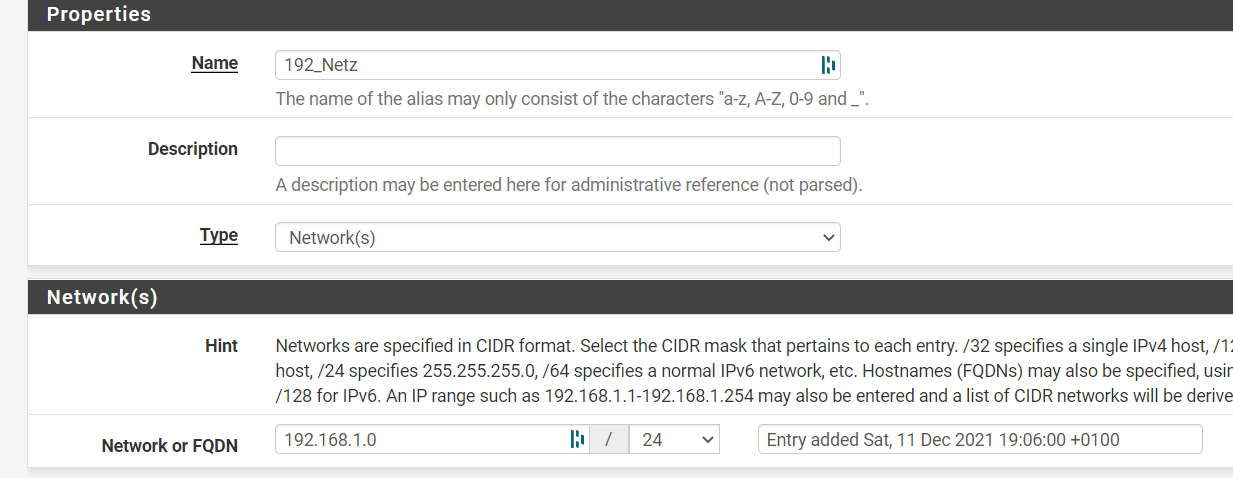
@johnpoz I have a Alias with 192.168.1.0/24 and this Firewall rule to block:

But the browser access to 192.168.1.30 is still possible. The Test Client is in 10.40.23.99 net.
-
@interessierter did you clear states after you created a block rule?
States are evaluated before rules, so if there was an existing state, that state would allow it before your rules are even looked at.
I don't see any triggers on that rule.. It shows 0/0 for states - so it was never evaluated.
Do you have any rules in floating that would allow the traffic?
-
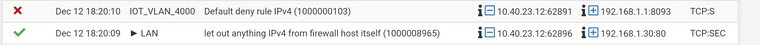
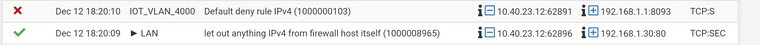
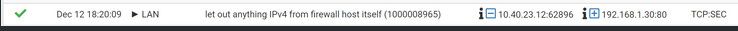
@johnpoz I have found this in the logs. It seems like all traffic will be blocked, only the connection to 192.168.1.30 is working. Why is that threaded differently?
-
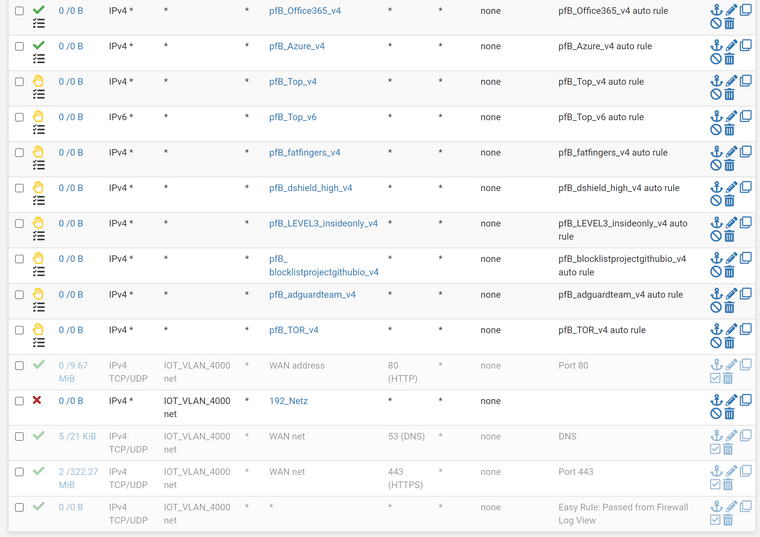
@interessierter the other rules on this vlan. No floating rules
-
@interessierter well your rule is not triggering, again you have a 0/0 for states..
You created your alias wrong maybe..
Rules are evaluated top down, first rule to trigger wins.. no other rules are evaluated. If default deny rule is being trigger then non of your rules above it either block or allowed were triggered.
As to that lan rule anything from the firewall itself are you natting this vlan for some reason?
-
@johnpoz The Alias is correct:
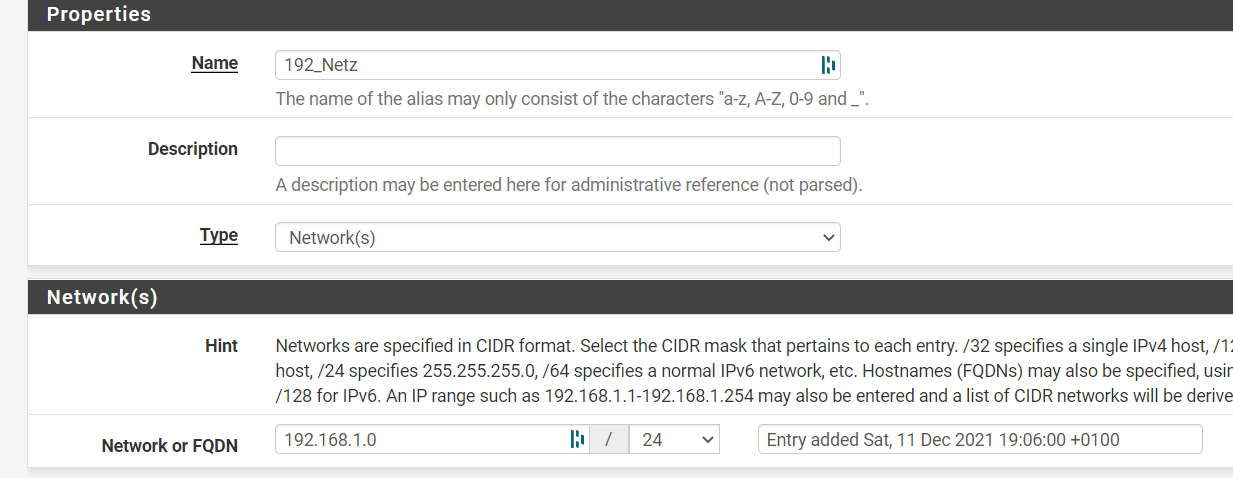
OK the Block rule was not on the first position, but it does not make any difference. Access is still possible.
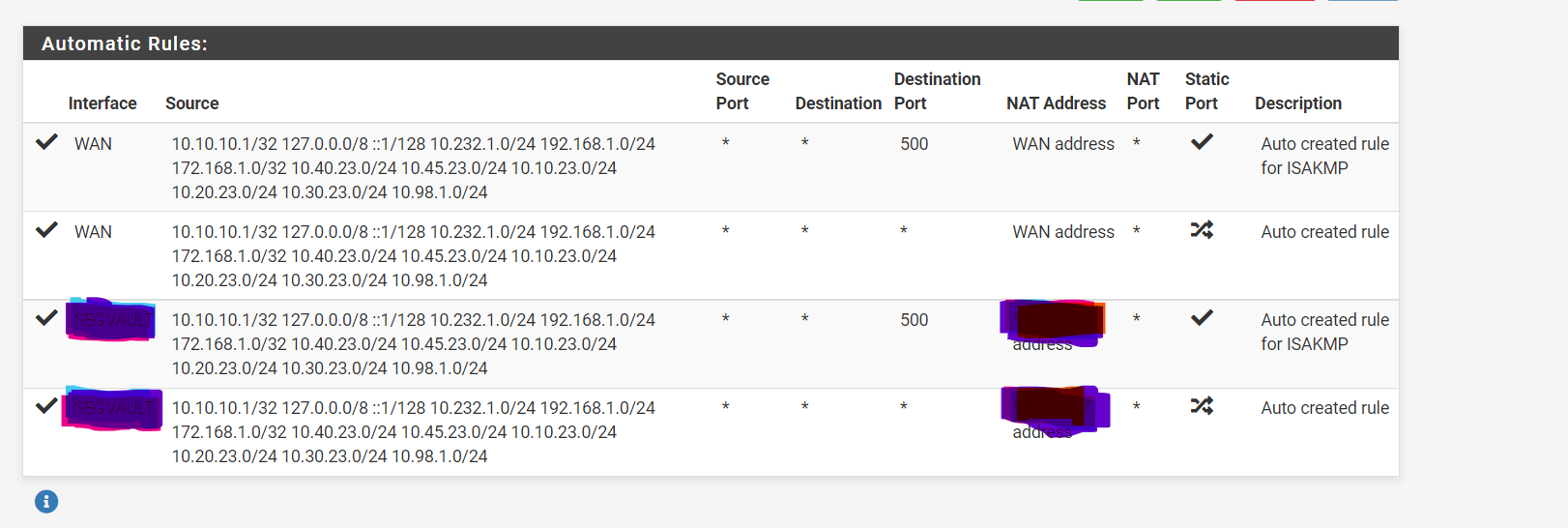
What I found is here some old NAT rules from a TEST for VPN:
-
@interessierter said in VLAN an Firewall rule not matching:
Why are those IP ranges identical and why LAN has a triangle. Maybe your NAT rules are wrong? Better show all the NAT rules and Portforwarding too.
Or start with a fresh install.

-
@bob-dig
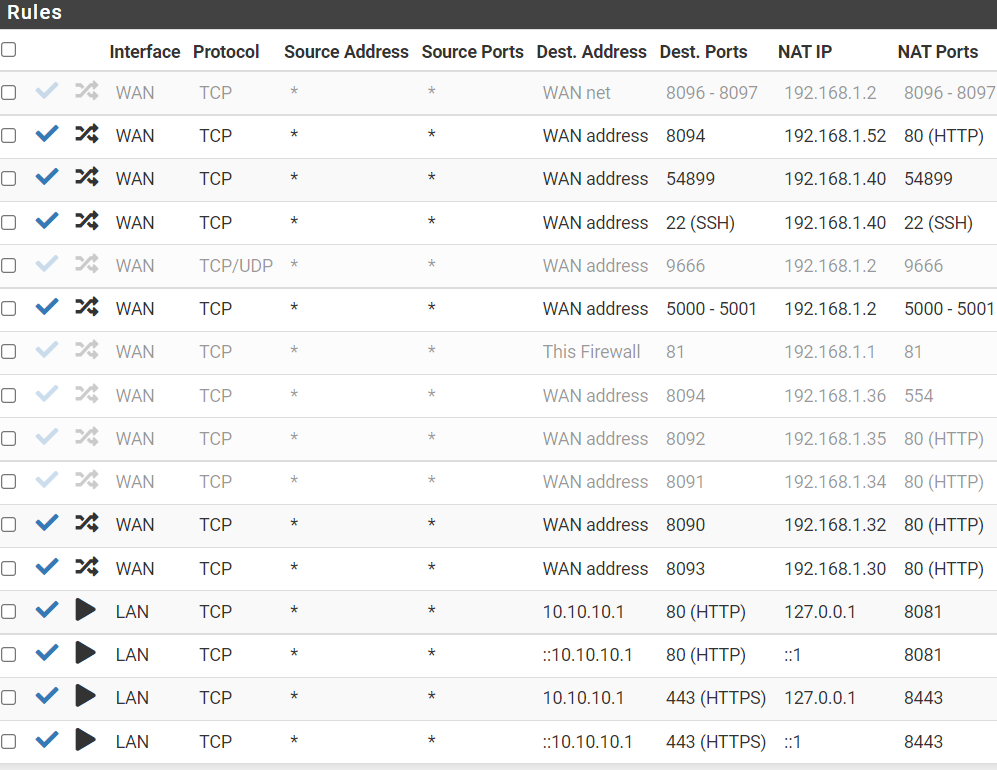
The last 4 lines are created from pfnblocker, is that the reason?
-
@interessierter said in VLAN an Firewall rule not matching:
@johnpoz The Alias is correct:
OK the Block rule was not on the first position, but it does not make any difference. Access is still possible.
What I found is here some old NAT rules from a TEST for VPN:
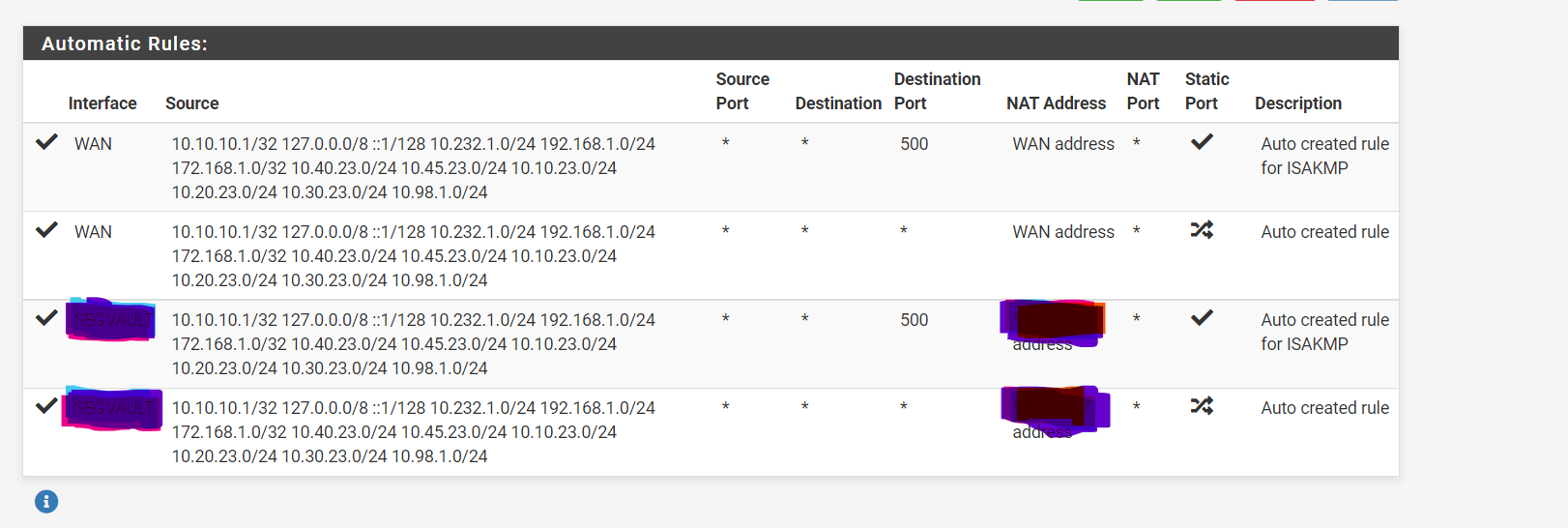
I have removed and deleted all VPN and IPSEC configuration however this rules are still there. And this NAT WAN defintily include the subnets that I use for VLAN
-
@interessierter any interface that has a gateway and considered a "wan" would auto create outbound nat rules when your in auto mode.
You can see only wan as outbound nat auto.
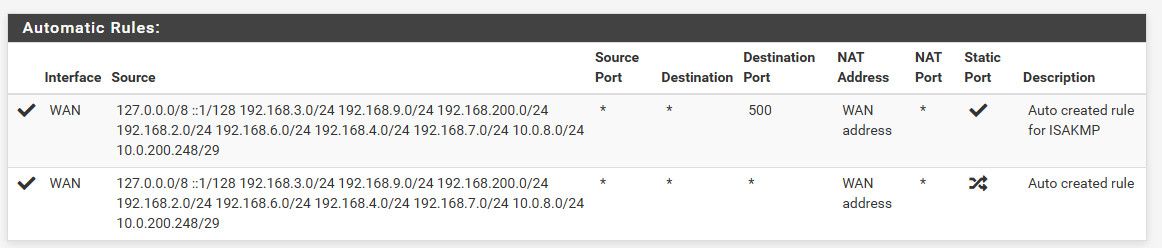
I then created a gateway on one of my test interfaces - and it auto created the test outbound nat
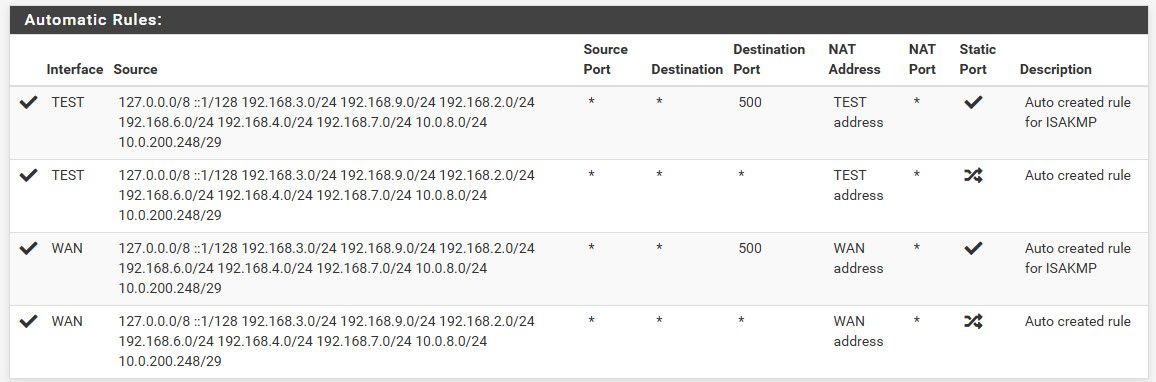
If you have some interface with a gateway set, it would create auto outbound nats. If you want to get rid of those you would need to remove this gateway your no longer using.
edit: BTW this firewall entry is the firewall itself creating traffic, not pfsense allowing traffic from 1 vlan to another
-
@johnpoz I have a second interface thats right, its a power Beam connection that use 10.224.1.14 as IP address, so thats not the subnet of my vlan.
Yes I have my used subnet in the NAT rule, but I don t know why
-
@interessierter just saying that is why you have auto outbound listed. Any interface that can be used as wan (ie has a gateway) with auto outbound nat will be seen.
-
@johnpoz But the seperate network (power beam) use 10.224.1.14/28, so it does not overlap with my networks 10.40.1.99/24.
Also the overlapping subnet is not only in the power beam NAT, it s also in the WAN source list. I still don t get why he list the IPs here.
So what is the solution? Disable the automatic Nating ?
-
@interessierter nobody said it overlapped?
edit: as to solution for what? You can have more than 1 wan, routing will just use normal routing via the default gateway or other routes you have setup, or policy routing via the firewall rules.
-
@johnpoz I plan to have 4 different VLANS, and the first vlan should be a iot Vlan that only allow Internet access. Right now this nating route route to my "main" network so the separation does not make sense.
-
@interessierter you lost me..
Your traffic is not matching from the last you posted, the firewall rule shows 0/0
The other firewall entry you listed was firewall generating traffic.
If you say you can get to this IP from another vlan.. It wouldn't have anything to do with outbound nat, port forwards could be.. But I don't see any portforwards on your lan that would match that traffic.
If your saying your client can get to that IP, maybe its taking a different path... Maybe its on the same L2 and you have the client with the wrong mask?