OpenVPN clients no longer accessible from LAN after upgrade to pfSense 2.7
-
I found the cause of my issue but I don't totally understand it.
I have two OpenVPN clients - one to the privacy service (PrivadoVPN) and another "site to site" client connection to another friend's PFSense router that I open and create rules for only when necessary. That second client is disabled at the moment, but its outbound NAT rule still existed.
If I move the Privado NAT rule ahead of the private client NAT rule, my policy-based route starts working. So somehow the inactive client is interfering with the policy route function in the newer PFSense where it didn't before.
-
@djrobx The new release of pfsense does strictly enforce the firewall rules where the earlier version did not. Your action makes perfect sense.
-
@reberhar The policy based rule was preventing your Private NAT rule from reaching the system table.
-
@reberhar
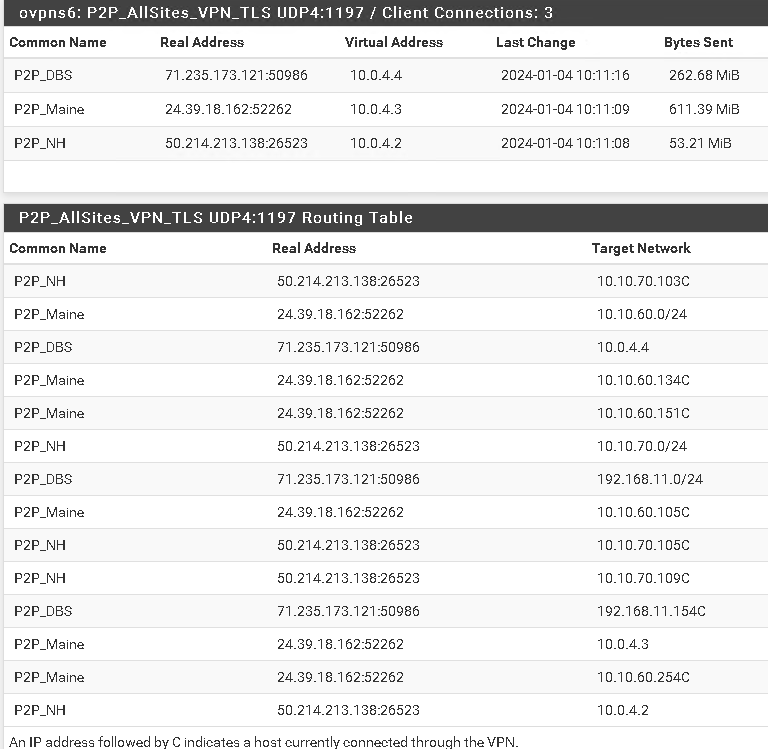
To all, I have this same situation and I am using the System tables, however the Routes set up within the system tables are using the same IP address as the default gateway for each Point-2-Point VPN connection: 10.0.4.2Common Name: Remote sites IP DG in the <Diagnostics-IPV4 Routes>
P2P_Maine 10.10.60.0/24 10.0.4.2
P2P_NH 10.10.70.0/24 10.0.4.2
P2P_DBS 192.168.11.0/24 10.0.4.2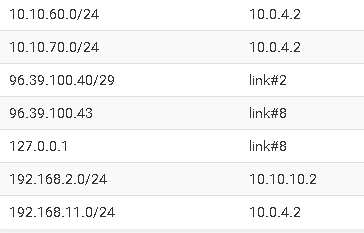
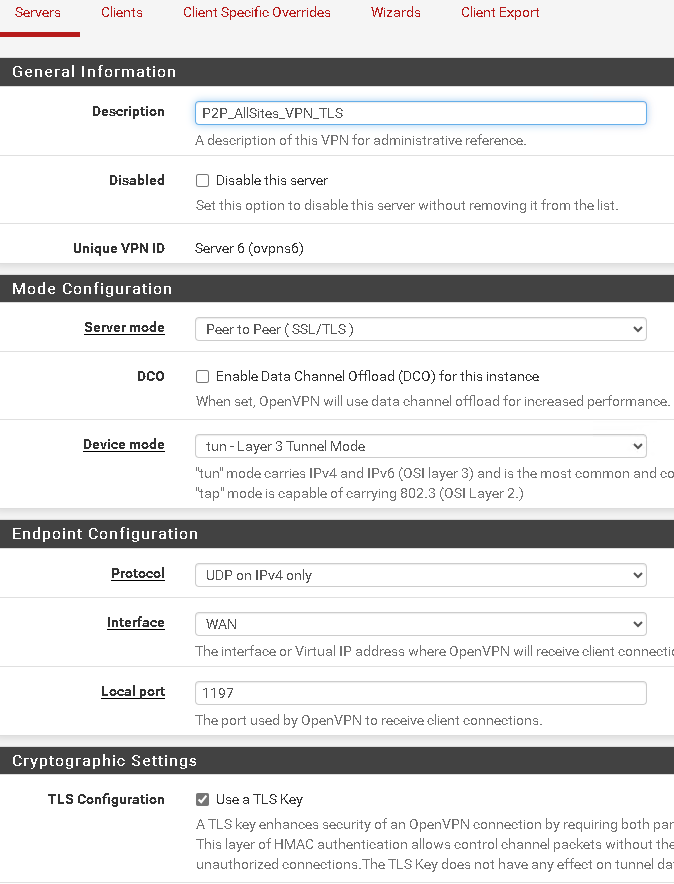
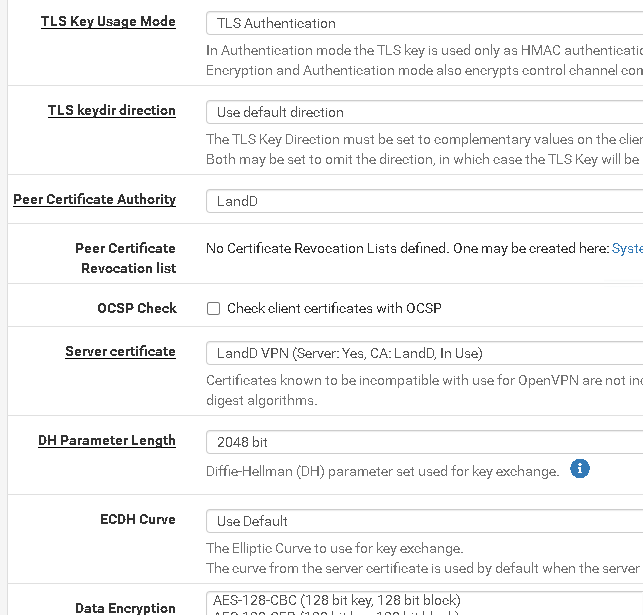
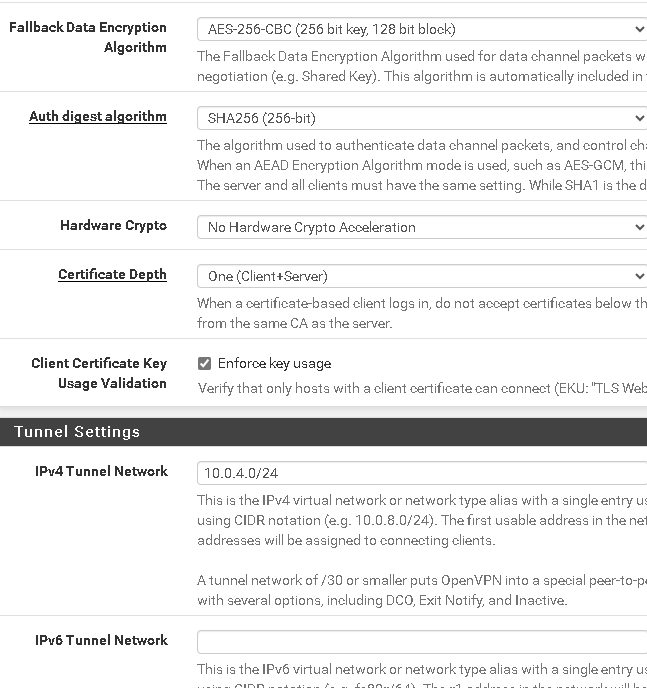
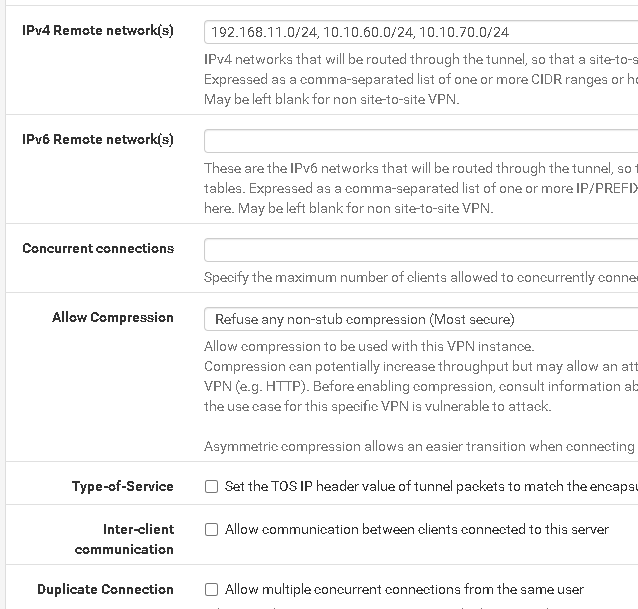
In the server configuration: VPN/OpenVPN/Server
IPV4 Tunnel Network: 10.0.4.0/24
IPV4 Local Networks(s) 10.10.30.0/24, 192.168.11.0/24, 10.10.60.0/24, 10.10.70.0/24
IPv4 Remote network(s) 192.168.11.0/24, 10.10.60.0/24, 10.10.70.0/24
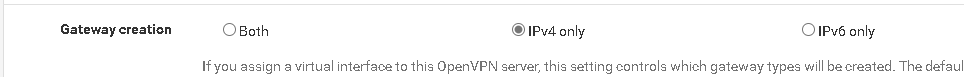
Gateway creation: IPv4 onlyunder Status/OpenVPN
Common Name Virtual Address
P2P_Maine 10.0.4.3
P2P_NH 10.0.4.2
P2P_DBS 10.0.4.4The hose: 10.10.30.16 has a virtual address on the VPN interface of 10.0.4.1
The problem I have is the same as discussed, I cannot connect to any device on the client sites.
I have read the TLS configuration and many documents regarding the settings and cannot find any inconsistencies.
This worked pre-2.7.1Looking for any assistance to identify if this is the same issue as above or completely different.
Thanks in advance.
-
@itinfo Hi itinfo,
So I am trying to wrap my mind around all that you have said here. First do you have any policy routings at all? You were running a pre 2.7.1 version of pfSense and upgraded to 2.7.1 right? Were you running 2.7.0? Do you have Suricata or Snort or pfBlocker? Are you getting any error messages or do your attempts just time out? What are the logs telling you? Have you tried a trace route to see where the system thinks it is going? What does ping do? What about your output wan that is sending out and receiving the queres? Has that changed? I recently changed my Internet facing wan and had some configuration to cover that. It does not seem like that is your problem however. Do you have a DMZ? How many lans do you have?
2.7.0 began to strickly enforcing firewall rules, That was why the work around is needed for anyone who was using policy routing rules., but if you were already running 2.7.0 without your OpenVPN problems, then the problem is elsewhere.
One of the problems I had in upgrading to 2.7.1 was that Suricata began to block some of my IPs. There have been several Suricata updates since then.
How far are you getting? Are you able to look at the pfSense gui on the other side?
-
To answer your questions.
I was running 2.7.0 with the same issue.
pfBlockerNG came with the upgrade - so yes running it.
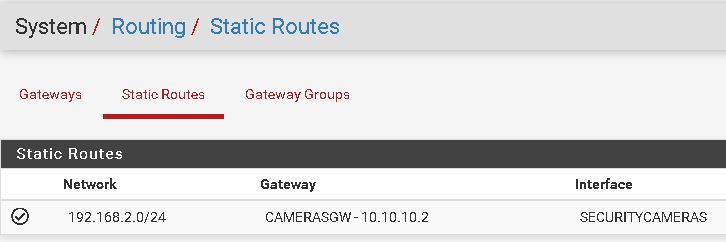
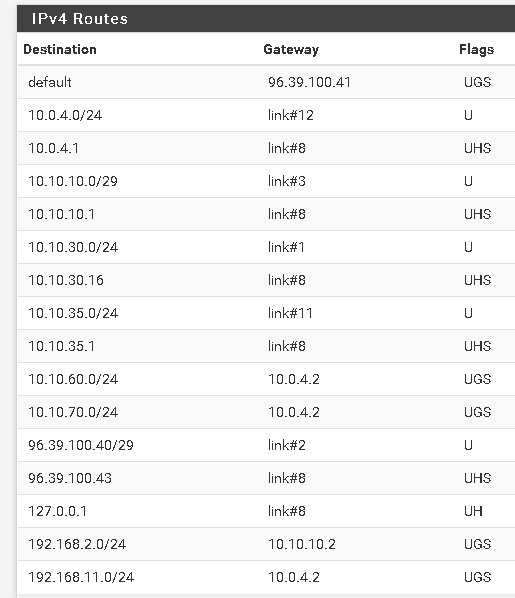
Here are my static routes:
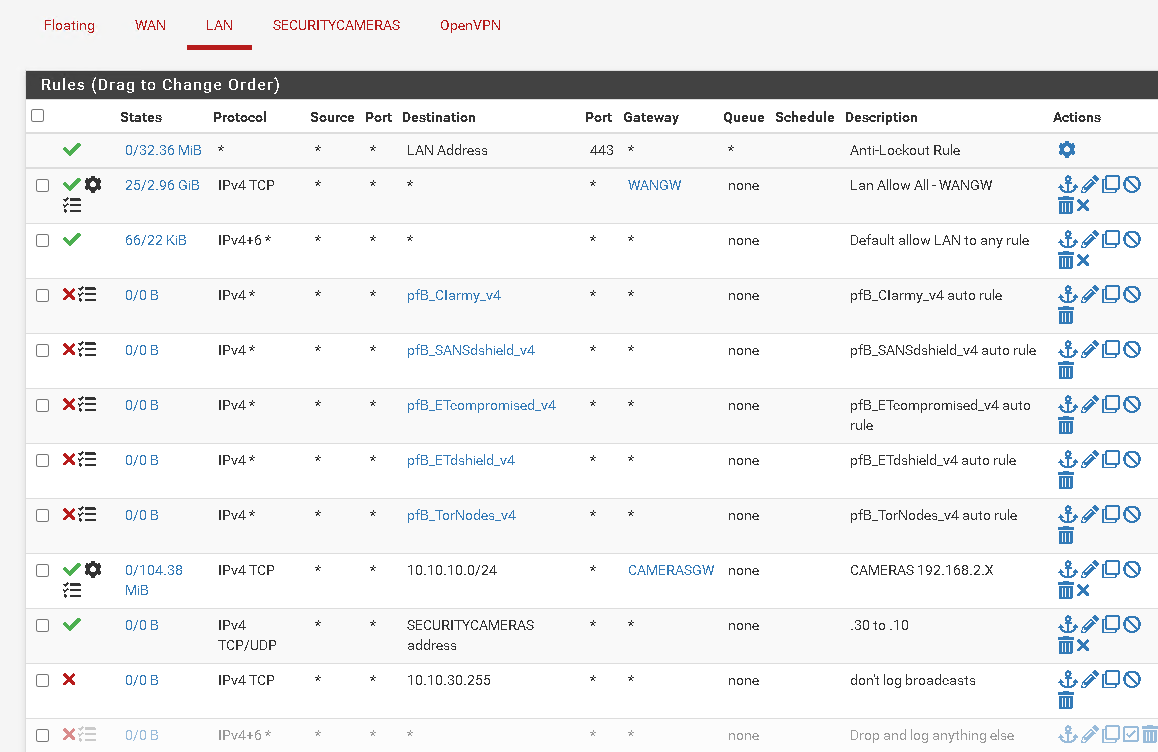
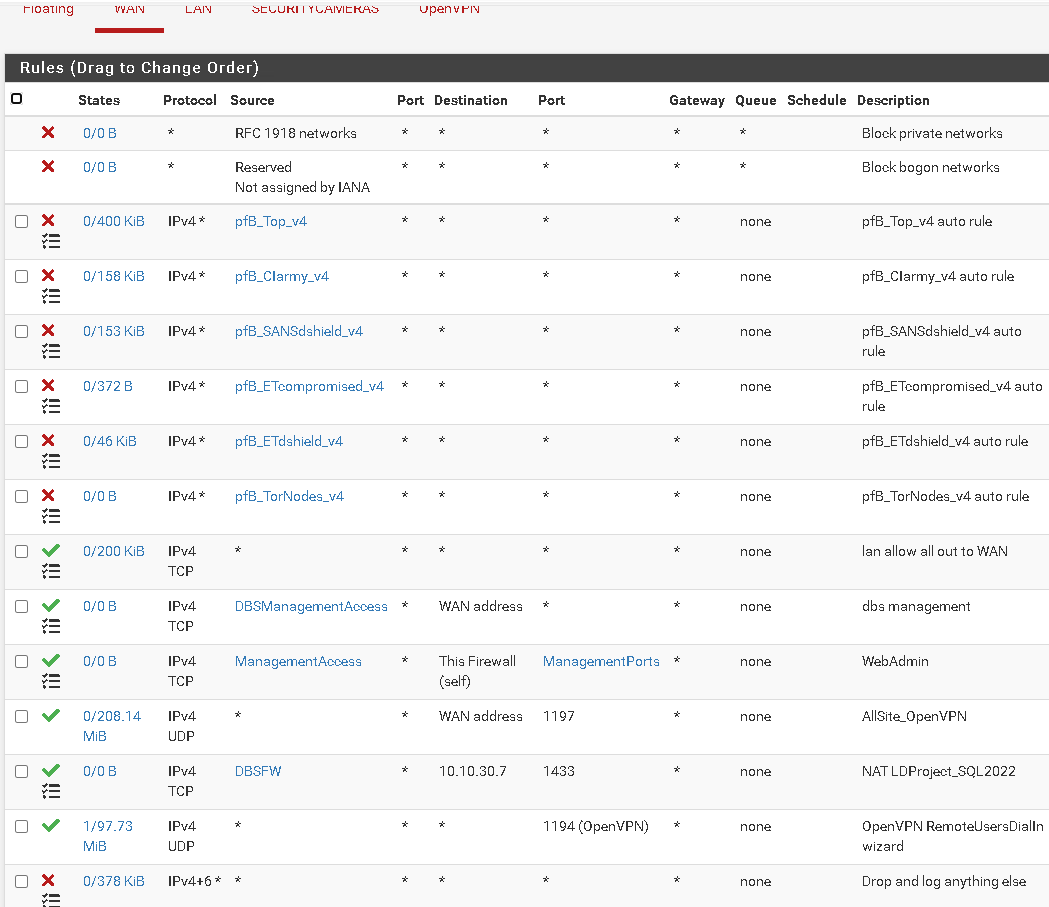
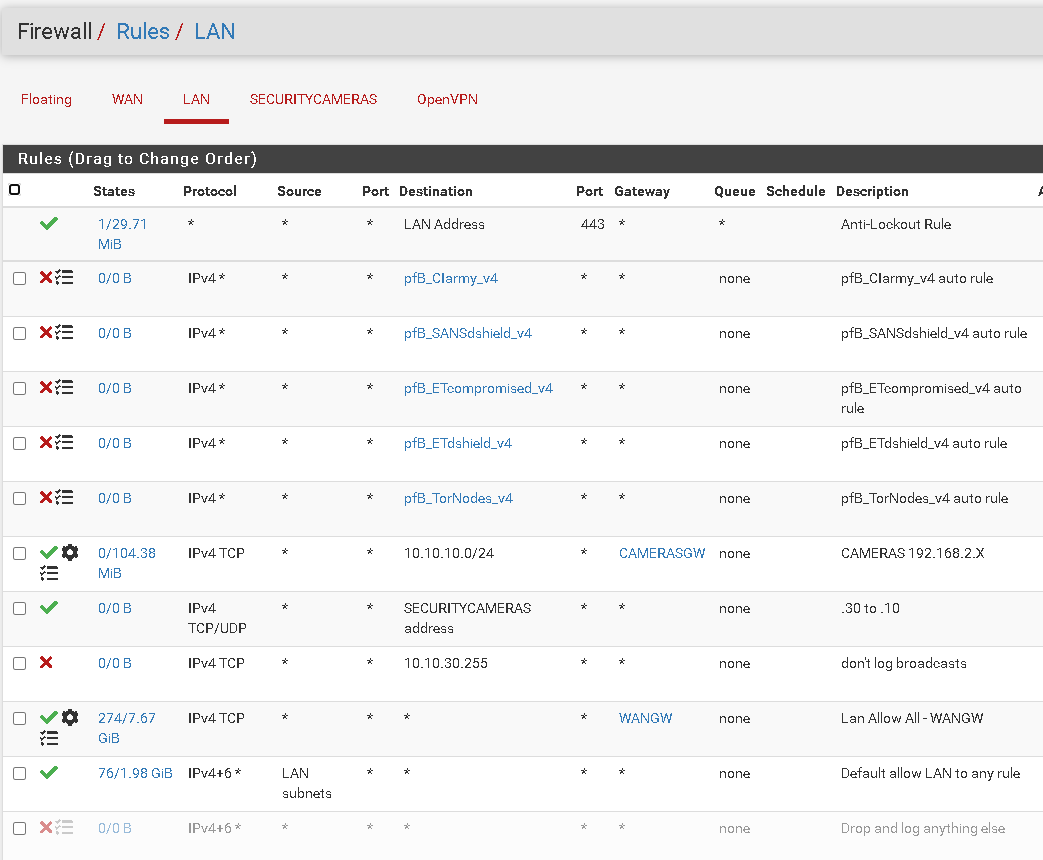
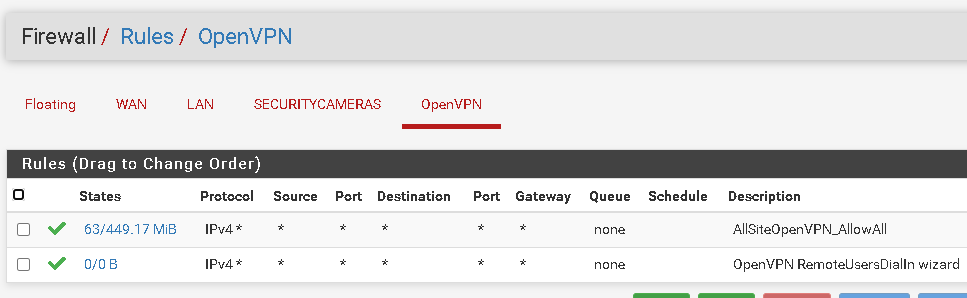
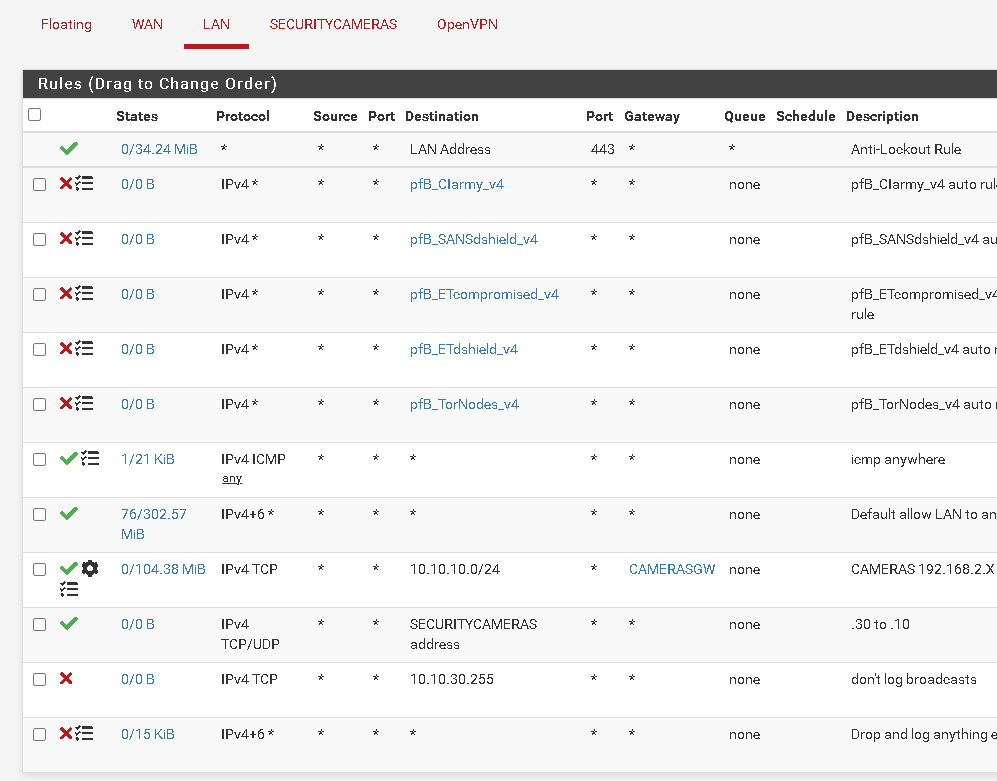
Here are my Firewall rules:
WAN:
LAN
OpenVPN
OPenVPN Server config
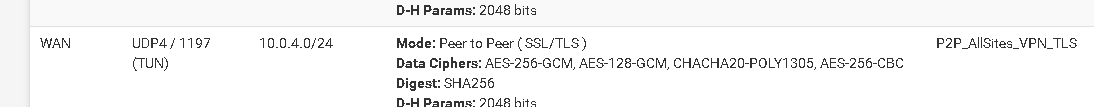
<Status-OpenVPN>
-
@itinfo
more:Note 3 VLANS have the same gateway - yet above in the <status-OpenVPN) we can see for instance P2P_Maine has a target network of 10.0.4.3 for VLAN address of 10.10.60.0-/24
Here we can see that the route to 10.10.60.0/24 has a default gateway of 10.0.4.2 (this is the endpoint of P2P_NH above)
<Diagnostics-Routes>
Here is tracert to 10.10.60.254 (Netgate router on Vlan 10.10.60.0\254)
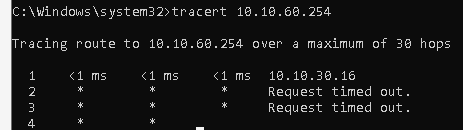
from 10.10.30.19
Here is a package capture on the LAN interface for a TraceRT from 10.10.30.19 to 10.10.60.254
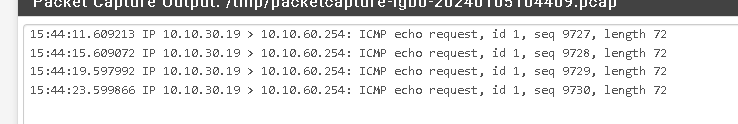
no response
here is an RDP request to a workstation 10.10.60.151
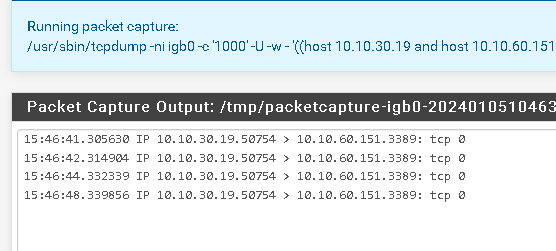
No packages on the WAN interface from or to 10.10.30.19 nor 10.10.60.151
Seeing traffice on the WAN to the IP 10.10.60.151 tracing Port 3389
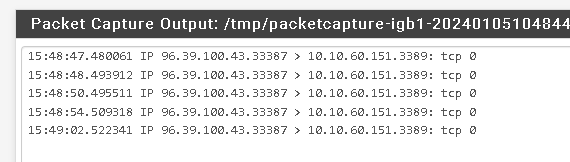
However I don't know what the destination (gateway) that the packages are looking for
Traffic on the VPN interface (OVPNS6) from the 10.10.60.x/24 network, but nothing to the network when trying to RDP to 10.10.60.151
The site: 10.10.60.x/24 has a gateway on the VPN of 10.0.4.1 (the Server side of the Tunnel) thus their traffic is flowing.
When trying to connect from the server side (10.10.30.19) to 10.10.60.151 there is no traffic on the VPN interface (OVPNS6)
So, with all this I welcome your insight.
-
@itinfo What was the version of pfSense you upgraded from? Do you have any policy routing rules?
I am not with Netgate so I am trying to think this through when I have a chance. I have 8 pfSense servers plus other servers behind them that I maintain.
Look carefully at you Lan firewall rules. From what I see and what you are telling me, that is the first place to look.
-
-
@itinfo Ok I see a couple of policy rules. The one at the very top is sending all your OpenVPN queries out to WANGW. You don't want that. It would be wise to move that rule below your OPENVPN rules and see what happens. That policy rule prevents your OpenVPN Quieres from reaching the system routing table.
It seems to me that you may want to change the way you are driving your gateways. If you have only one gateway, you don't need this policy rule. It is literary sending everything out to WANGW. There are better ways to do this.
You may want to put the policy rule that is at the top BELOW the other policy rule with CAMERASGW. I am not sure what the other rules do so you may have to play around to find the place you want it.
-
@reberhar thanks for the insight.
I did see the icmp requests from 10.10.30.19 to 10.10.70.1 being sent out over the WAN interface.
Now they are being sent out over the OpenVPN interface
I removed many of the 'test' rules -much longer story - had an ISP router that went bad and I had to get Netgate/pfSense onboard to prove that it was not my router but theirs. ~ $2,000 of costs
and I now have
Best part of your help is......
It works!!!!!
Thanks a million
-
@itinfo I am glad my help worked. We have all worked frantically into the night hoping, wishing that someone could simply answer our questions and relieve our anxiety and frustration, and that of our users too sometimes.
The switching to 2.7.0 was pariticulary difficult because it broke functioning systems. If you look through the forums here you can see that it was a real struggle for me too. When the light finally went on, I wrote a post that several people found helpful.
At that point some documentation on HA actually helped me understand the problem better too, thus the questions about other Lans and a DMZ. Lan to lan communication can also be broken by policy routing rules.
God bless you,
Roy Eberhardt
-
@Further up your WANGW policy rule is further down in the rules list, but was certainly impacting your tunnel access. I read your rule comments more carefully and understand your system better. Yes you did need to remove this rule WANGW, or insert others that trapped for your tunnel addresses and sent them out to the system routing table.
For me, since I need policy routing, I setup an alias list in a rule that traps my server addresses and sends them to the system routing table. This rule I placed above the policy routing rule.
FYI
-
R rlabaza referenced this topic on
-
@reberhar I'm a little confused by your comments about "policy rules". What are policy rules / policy routing rules or are they just another name for firewall rules that you show in the screen shots you posted?
-
@lifeboy Hi lifeboy,
So normally, when a rule matches conditions in the firewall or a query falls out the bottom the next place it goes is to the system routing table.
If you change that and direct the output somewhere else that is policy based routing.
At near the very bottom of any firewall rule in the advanced area you see something like:
Gateway "HereIsMyGatewayGroup" (quotes mine)
Leave as 'default' to use the system routing table. Or choose a gateway to utilize policy based routing.
Gateway selection is not valid for "IPV4+IPV6" address family.
This is the place you put policy base routing.
Roy
-
@reberhar I can understand if you have multiple gateways that you'd have to add something like this, but I have a single WAN gateway and OpenVPN that connects site-to-site. On the client side I have an LAN rule that allows all traffic. There is only one way for traffic to leave the client and that is via the default gateway.
-
@lifeboy Hi Lifeboy, ...
So does this information help you? Policy routing will break your OpenVPN connections if you're query ends up there. You gotta grab them beforehand and send them to the system table. Then it works.
Roy
-
@reberhar Hi Lifeboy,
I'm sorry that I didn't understand your frustration was coming from your broken VPN. I just answered your question about what policy rules are.
You MUST send any VPN queres to the system table before they reach policy rules or they will fail.
Roy
-
@reberhar Thanks for your patience! I still don't see a way to achieve this, unless the comment below the "gateway" means that if I leave the gateway as default, the traffic will go the routing tables.
Should I not have a rule to manage "all from any" traffic for the LAN then? Or a rule that only allows traffic that's not for OpenVPN?
-
Dear All,
I am very glad that this does get discussed in plain language, now. Please take a look at my situation an point me to the right direction.
My situation is dual WAN with site to site OpenVPN and remote access OpenVPN. Inbound OpenVPN ports are forwarded to localhost, so that OpenVPN is available on both WANs.
My classical LAN firewall rules are:
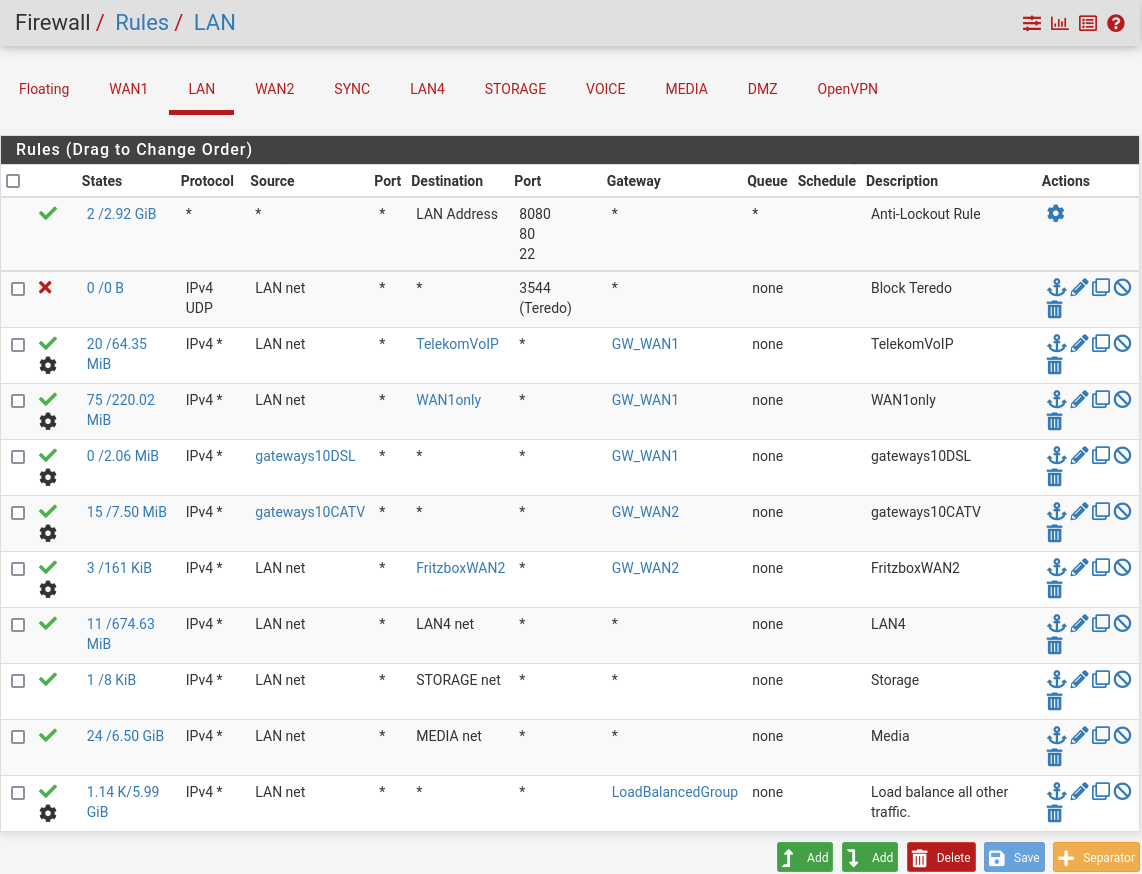
The problematic "policy routing" is everything where the gatewway colum is different from "*" (also showing the "advanced settings" wheel) - did I understand this correctly?
To not break OpenVPN in pfSense 2.7 I need to remove policy routing from the LAN rules, also correct? From all of them or only those which may end up pointing outbound to the OpenVPN tunnel (please see below)?
Then my take is:
-
The bottom rule "Load balance all other traffic." This will handle traffic going though the site to site OpenVPN tunnel. Should be easy to fix: Normally, I have one of my WANs as the default gateway, but I could just select a gateway group as the default gateway, right?
-
The other rules are more difficult to manage but these will not send traffic to the OpenVPN tunnel - this is where I would need some hints, please - if there need to be changes:
-- The first policy rule is such an example: The VoIP running in the LAN does only work, if traffic goes through a particular WAN (my GW_WAN1). How can I achieve that without "policy routing"?
-- Similarly, I have DSL and CATV modems in front of my pfSense that I would like to reach for admin access (for example rule "Fritzbox WAN2". Of course, I can reach them only through the WAN in front of which they are sitting.
-- Third, my mail server should serve both WANs inbound and outbound - and know which WAN each connection is using. I realize this by assigning source "gateways10DSL" to "GW_WAN1" and source "gateways10CATV" to "GW_WAN2"?
Are those functions still possible with 2.7 using multi-WAN and OpenVPN?
The traffic directed either to GW_WAN1 or GW_WAN2 odes NOT use VPN. Are these policy rules still a problem or is only the "Load balance all other traffic." the issue? Simularly itinfo also redirects to "CAMERASGW" for some destinations. If these rules need to go, the devices in front of pfsense could be put into a different LAN, but binding some output to specific WANs/IP addresses would be challenging.
Regards,
Michael
-