Suricata process dying due to hyperscan problem
-
@bmeeks
Nice, ready when you are -
@kiokoman said in Suricata process dying due to hyperscan problem:
@bmeeks
Nice, ready when you areI haven't forgotten. Ran the ASAN-enabled package first on my virtual machine and right away discovered another bug in the custom blocking module I wrote. Color me doubly embarrassed
 . This one was a missing address-of ('&') operator in two key places. Surprised the compiler never complained about them, but they both tripped ASAN right away.
. This one was a missing address-of ('&') operator in two key places. Surprised the compiler never complained about them, but they both tripped ASAN right away.So, tidying up and retesting after correcting that bug before posting the ASAN-enabled package for you guys to test.
-
Here is a link to the ASAN-enabled (Adress Sanitizer) debug build of Suricata 7.0.2. Please install and try this version.
Here is the link to the package binary on my Google Drive: https://drive.google.com/file/d/1y3ohuWyhK3IrHb_p5nVVkc4OwJJBhg0U/view?usp=drive_link. The file has the same name (
suricata-7.0.2_6.pkg).Repeat the steps outlined in this post to install the debug package: https://forum.netgate.com/topic/184101/suricata-process-dying-due-to-hyperscan-problem/223.
You have two options for doing the initial test run. Because the ASAN runtime linked into the binary really only outputs information to the console, you must run Suricata from the command-line to get the ASAN output. But I would first just try to run it from the GUI to see if it crashes still. It is possible the last two bugs I found and fixed this morning in the custom blocking module were the cause of the Hyperscan issue. So, just first try starting this new version from the GUI. If it starts and stays running, then the bug is fixed. If it crashes, then proceed to the steps below to run it from a CLI prompt in order to capture the ASAN output.
To Capture ASAN Output
You will need to start Suricata from a shell prompt on the firewall. You will want to use PuTTY with an SSH session so that you can easily scroll back and see past console output.- Establish an SSH session to the firewall using PuTTY.
- Exit the menu into a shell prompt by choosing option #8.
- Identify the full path to the correct
suricata.yamlconfiguration for the interface you are testing. Look at the subdirectories under/usr/local/etc/suricata/and find thesuricata_xxxx_yyyydirectory that matches the interface you want to test. - Note the physical interface name used by pfSense (for example,
em0,vmx1, etc.). The interface name will be part of the subdirectory name. - With the above two pieces of info: (1) path to
suricata.yamlfor the interface; and (2) the physical interface name, start Suricata using this command:
/usr/local/bin/suricata -i <iface> -c /usr/local/etc/suricata/<suricata_xxxx_yyyy>/suricata.yamlFor example, here is the command for my virtual machine where I am using the
em0interface and the interface's conf directory issuricata_13473_em0:/usr/local/bin/suricata -i em0 -c /usr/local/suricata/suricata_13473_em0/suricata.yamlSuricata should start and begin spewing data to the console. If it hits a memory issue, the ASAN module will spit out some colorful data and exit the program. If there are no ASAN-detected errors, the program will just seem to freeze as it was not started in daemon mode. A simple CTRL-C from the keyboard will break out of the program.
-
 B bmeeks referenced this topic on
B bmeeks referenced this topic on
-
@bmeeks
still running man .. still running ....






for me it's a record, 10 min without any hyperscan error -
@kiokoman said in Suricata process dying due to hyperscan problem:
@bmeeks
still running man .. still running ....






for me it's a record, 10 min without any hyperscan errorThis is good! Maybe I did find it this time.
The ASAN-enabled debug package is going to run quite a bit slower. If your results continue to be positive into the next day, then I will prepare a pull request with the fixes and get it submitted to the Netgate developer team so we can get a new package posted for production use.
There were two places in the custom blocking module code where an IPv4 and an IPv6 address were being copied using
memcpy()and I had left off the address-of operator on one of the parameters (the destination memory address). That resulted in heap buffer overflows that would have produced random results depending on the runtime memory configuration of a particular installation. One manifestation could be corrupted pointers that were later passed to Hyperscan.This would explain the connection between disabling Legacy Blocking Mode and successful execution with Hyperscan enabled.
-
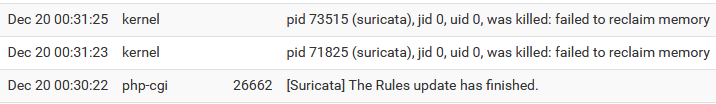
My Suricata instances have mostly been running fine since I installed your latest debug package. However, I've noticed a major change in the memory usage and during a rule update tonight both instances were killed due to lack of memory. I assume the memory usage will come back down once a non-debug enabled package is re-deployed, but I just thought I should point this out in case it's helpful.
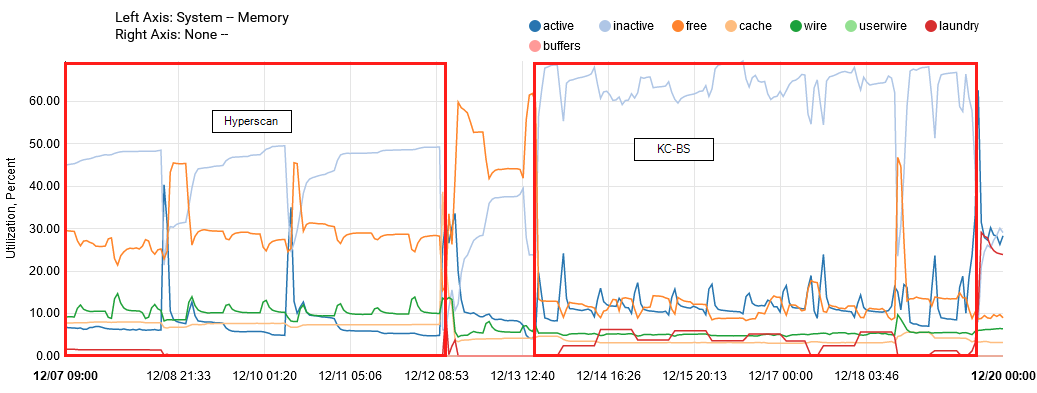
This graph shows memory usage for the past two weeks.
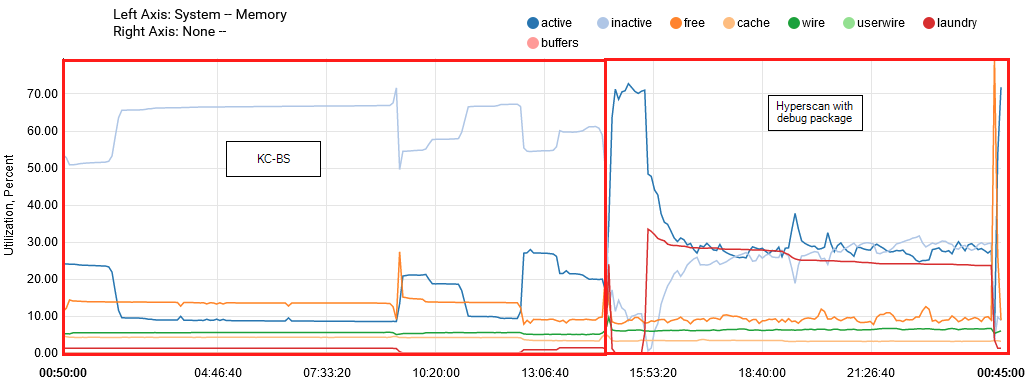
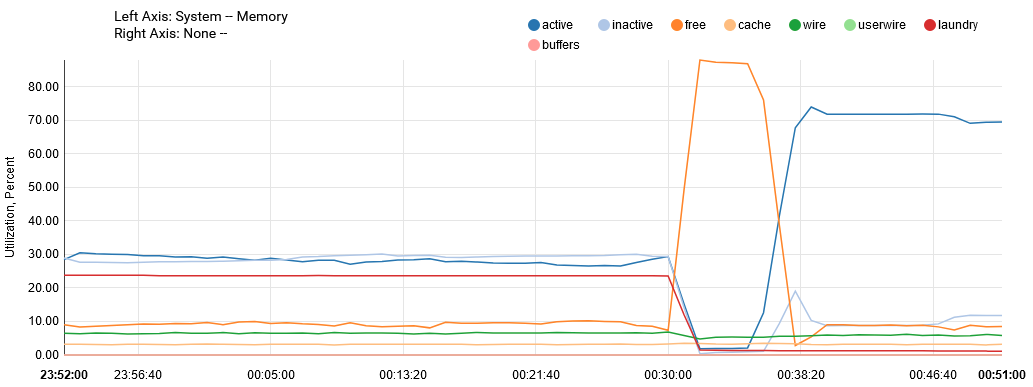
This graph shows memory usage before and after installing the debug package.
Finally, this graph shows the Suricata instances being killed following a rule update. I had to delete the PID files in order to get Suricata to start.
-
@masons:
1, How much RAM is installed in the firewall?
2. Are you running with a ZFS or UFS installation?The ASAN-enabled build will run quite a bit slower than a regular build, but I would not expect it to consume all that much more memory.
Changing the multi-pattern matcher algorithm can have a very large impact on memory usage, though.
-
@kiokoman: do you still have good news for me about the patched Suricata code
 ?
?If you do, I will create the pull requests for the production update and get them submitted.
-
I have submitted the pull request that hopefully contains the final fix for this Hyperscan crash. It should also address the instances of Signal 11 segfault crashes some other users have experienced in Suricata.
Here is the request: https://github.com/pfsense/FreeBSD-ports/pull/1337.
There is also a GUI package update to match: https://github.com/pfsense/FreeBSD-ports/pull/1338.
Look for a new 7.0.2_3 version of the Suricata package to show up soon.
-
@bmeeks
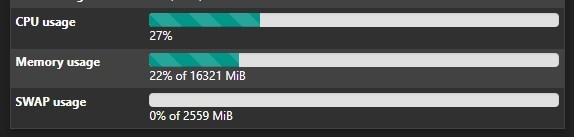
yup, still running, i didn't check the memory usage before the patch, i'm around44% of 16321 MiB
maybe i have 4% 5% more ram usage in total but i have other services like telegraf / haproxy / 5 openvpn / 1 wireguard and at this time there are alot of traffic
-
@kiokoman said in Suricata process dying due to hyperscan problem:
@bmeeks
yup, still running, i didn't check the memory usage before the patch, i'm around44% of 16321 MiB
maybe i have 4% 5% more ram usage in total but i have other services like telegraf / haproxy / 5 openvpn / 1 wireguard and at this time there are alot of traffic
Great news!
As you see immediately above, I've posted the pull request containing the bug fix for the Netgate developer team to review and merge. Also sent them an email request. Hopefully they get to it soon.
The new package version will be 7.0.2_3 (for the GUI) and will be a normal non-debug production build.
-
@bmeeks
Great news indeed. Bill, do you have a paetron or some method that we, the community, can contribute to you? Your hard work, your efforts, are not unnoticed, and truly appreciate the efforts you place into making pfSense better with the integration of Suricata. -
@michmoor said in Suricata process dying due to hyperscan problem:
@bmeeks
Great news indeed. Bill, do you have a paetron or some method that we, the community, can contribute to you? Your hard work, your efforts, are not unnoticed, and truly appreciate the efforts you place into making pfSense better with the integration of Suricata.No, I do not have a Paetron account. I do this in the spirit of open-source free software, so I don't expect to make money from it. But thank you for offering.
-
Just installed 7.0.2_3 a few minutes ago, thanks for getting it fixed....
-
Just installed 7.0.2_3 on two 6100 in HA. Suricata on three interfaces with MPM: Auto and ET Pro ruleset. No Signal 11 segfault on suricata start now but the three processes of suricata takes 100% cpu and interface goes down with failover to secondary node. After failover, primary node gui hangs and ssh reveals that the three suricata processes takes 100% cpu. Around 30 seconds after failover on secondary node gui hangs there aswell and suricata shows 100% and never let go. After gui hang traffic stops on the interfaces. Suricata 7.0.2_2 was removed and 7.0.2_3 was installed and fw was rebooted after install.
Same behaviour was observed with AC-BS on 7.0.2_2.
No issues with 21.05.1 and that suricata version.
-
@bmeeks said in Suricata process dying due to hyperscan problem:
1, How much RAM is installed in the firewall?
4GB
- Are you running with a ZFS or UFS installation?
ZFS
After uninstalling the debug Suricata package and installing the new Suricata plugin, memory usage is back down to around 30%.
Thank you so much @bmeeks for getting to the bottom of this Hyperscan issue!
-
@btspce said in Suricata process dying due to hyperscan problem:
Just installed 7.0.2_3 on two 6100 in HA. Suricata on three interfaces with MPM: Auto and ET Pro ruleset. No Signal 11 segfault on suricata start now but the three processes of suricata takes 100% cpu and interface goes down with failover to secondary node. After failover, primary node gui hangs and ssh reveals that the three suricata processes takes 100% cpu. Around 30 seconds after failover on secondary node gui hangs there aswell and suricata shows 100% and never let go. After gui hang traffic stops on the interfaces. Suricata 7.0.2_2 was removed and 7.0.2_3 was installed and fw was rebooted after install.
Same behaviour was observed with AC-BS on 7.0.2_2.
No issues with 21.05.1 and that suricata version.
This is more like what I'm seeing as well on my 2100, only one WAN, though, so no failover, and AC-BS works for me. Suricata uses 100% CPU for a while after it launches, then the kernel eventually kills it, if I'm lucky. If not, the system gets VERY unstable for a while, eventually ending with Suricata and unbound both dead, and I have to log in from the LAN side to the IP address directly to fix things, since there's no DNS response.
As I've noted several times above, this is not just Hyperscan for me - it's all algorithms except for AC-BS. The latest update did not fix it. :(
-
I installed package version 7.0.2_3 as soon as it was available, I set the Multi-Pattern Matcher Algorithm to Auto again and so far everything is working perfectly. I haven't had any errors caused by hyperscan.
Great job @bmeeks! Thank you for your efforts to identify the problem! -
@Maltz said in Suricata process dying due to hyperscan problem:
This is more like what I'm seeing as well on my 2100, only one WAN, though, so no failover, and AC-BS works for me. Suricata uses 100% CPU for a while after it launches, then the kernel eventually kills it, if I'm lucky. If not, the system gets VERY unstable for a while, eventually ending with Suricata and unbound both dead, and I have to log in from the LAN side to the IP address directly to fix things, since there's no DNS response.
As I've noted several times above, this is not just Hyperscan for me - it's all algorithms except for AC-BS. The latest update did not fix it. :(
The SG-2100 has an ARM Cortex CPU (not Intel architecture), so Hyperscan does not and cannot work on that platform nor any other ARM platform. The Hyperscan library is completely excluded from the Suricata binary build on ARM platforms. Hyperscan is a technology written by Intel exclusively for use on their CPUs.
When you choose Auto for the Multi-Pattern Matcher algorithm, Suricata will use Hyperscan if it is available, then default to use AC otherwise. Because you have an ARM CPU in the SG-2100, then Suricata will never choose Hyperscan when set to Auto. It will instead automatically use AC.
Fiddling with the Pattern Matcher settings can lead to huge increases in RAM usage, and your SG-2100 has a very limited amount of RAM to begin with. Leave it on Auto. If you are also using ZFS, that will compound the limited RAM problem because of competition from the ARC cache. And during the rules update process, the amount of RAM needed by Suricata will sharply increase (especially if you have "Live Rule Swap" enabled).
-
@bmeeks
7.0.2_3 system all green