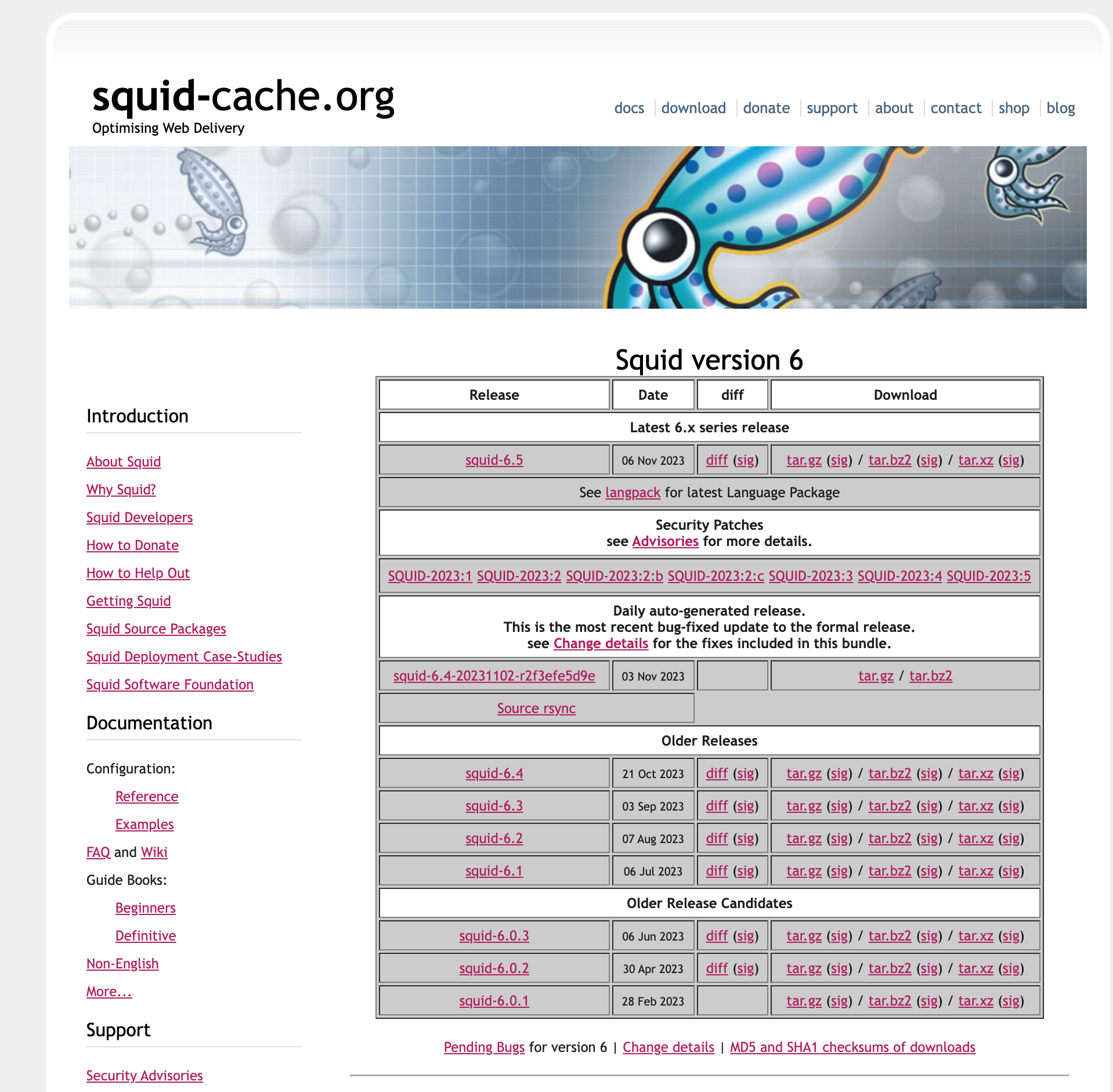
Squid 6.5 !! Nov 6th
-
Hi everyone, since version 2.7.1 pfsense Squid is deprecated and that's why all these strange errors occur.
I was hoping for Luiz's patch. Before abandoning pfsense+squid I will do some more tests because it is an excellent solution.
If you have other solutions to try let me know.
Greetings
Michele -
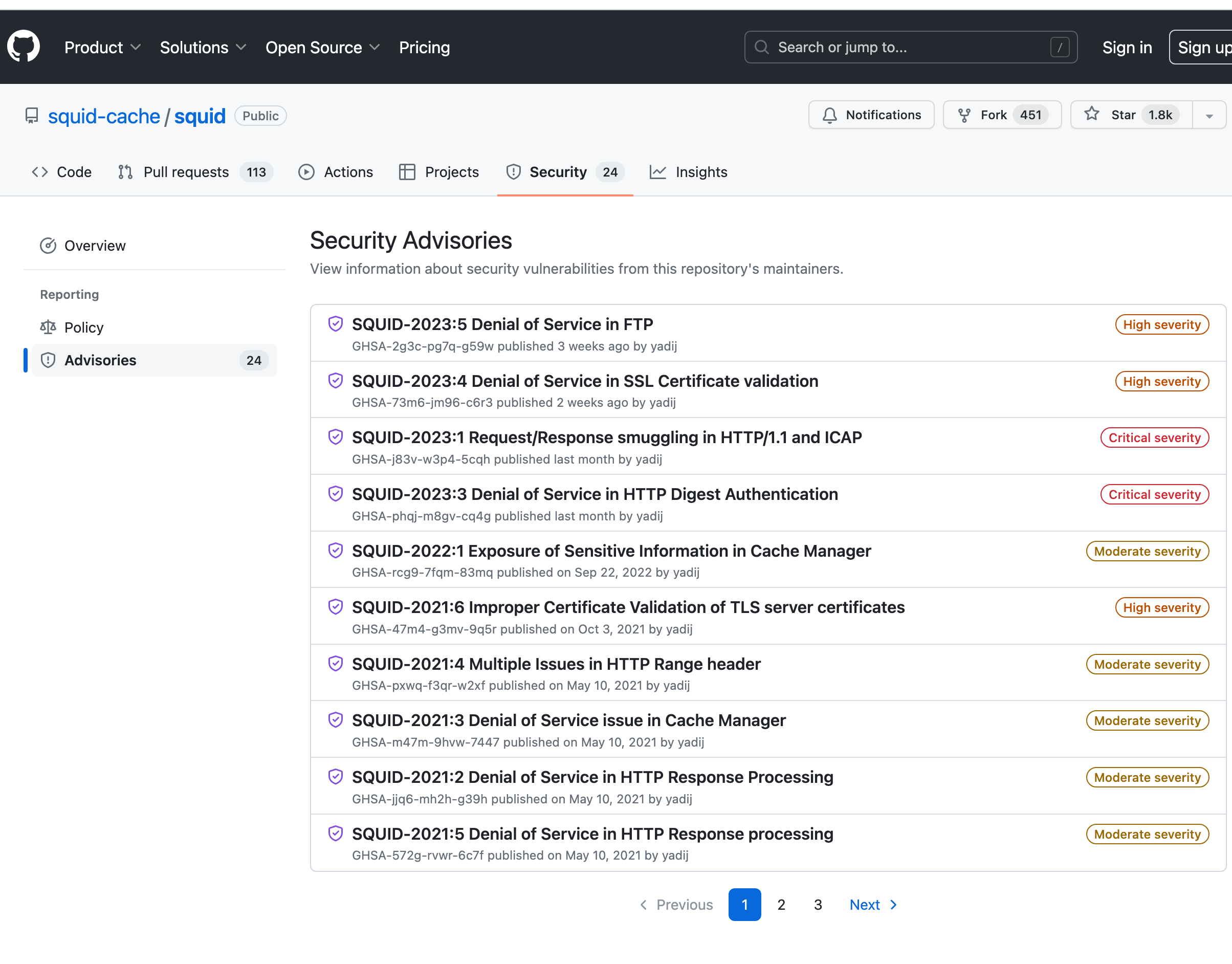
@Michele-Trotta hello everyone on this post is already aware. This post is for work arounds. Squid itself has many new security updates already available. I am sure you are aware. Thanks, this post is just the open source community coming together to help find ways to make it work. Solutions are needed and being tested in here with high hopes of bring the latest Squid version online for die hard users. Just some open source discussion at its finest. Seems it still has some bugs with that error you see above.
Leading to Ecap over icap I wonder if that would improve security as it can work directly with DoH I am told.
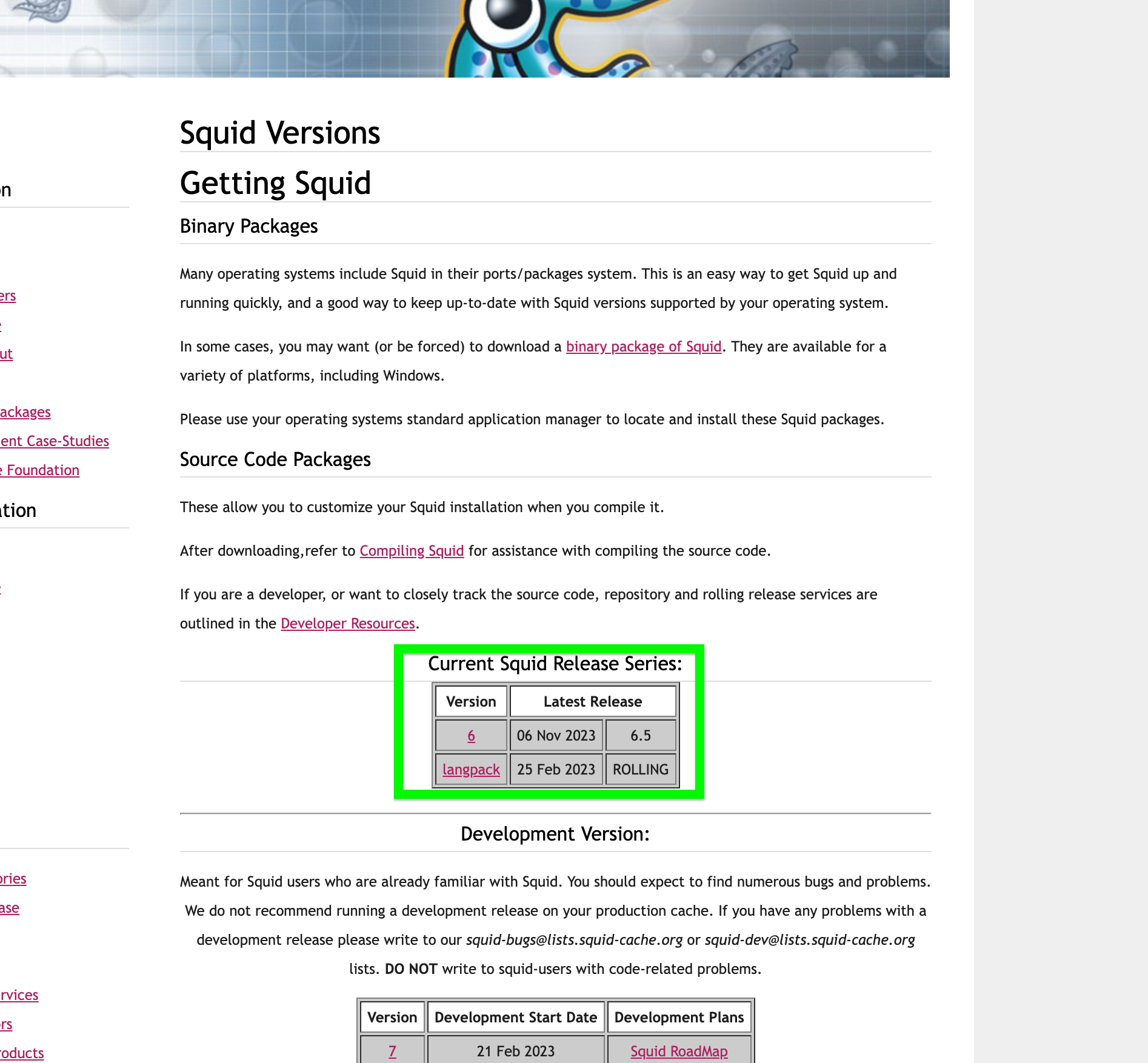
DoH is a big issue with dns based security….. it’s pure https based DNS you can’t force it and it’s reaction based when you block it, ever worse is QUIC. The latest Squid updates have QUIC protocol tools to detect and inspect. That’s https over udp, and it’s a big issue within dns based cyber security detection also. That’s why Squid can’t and won’t die. It’s because Squid has solutions for all the new protocols.
We make solutions not problems.
-
@Michele-Trotta Squid has custom options you can check them on there website, I wonder if something is automatically activated when the new version is installed…
-
@Michele-Trotta check this out…
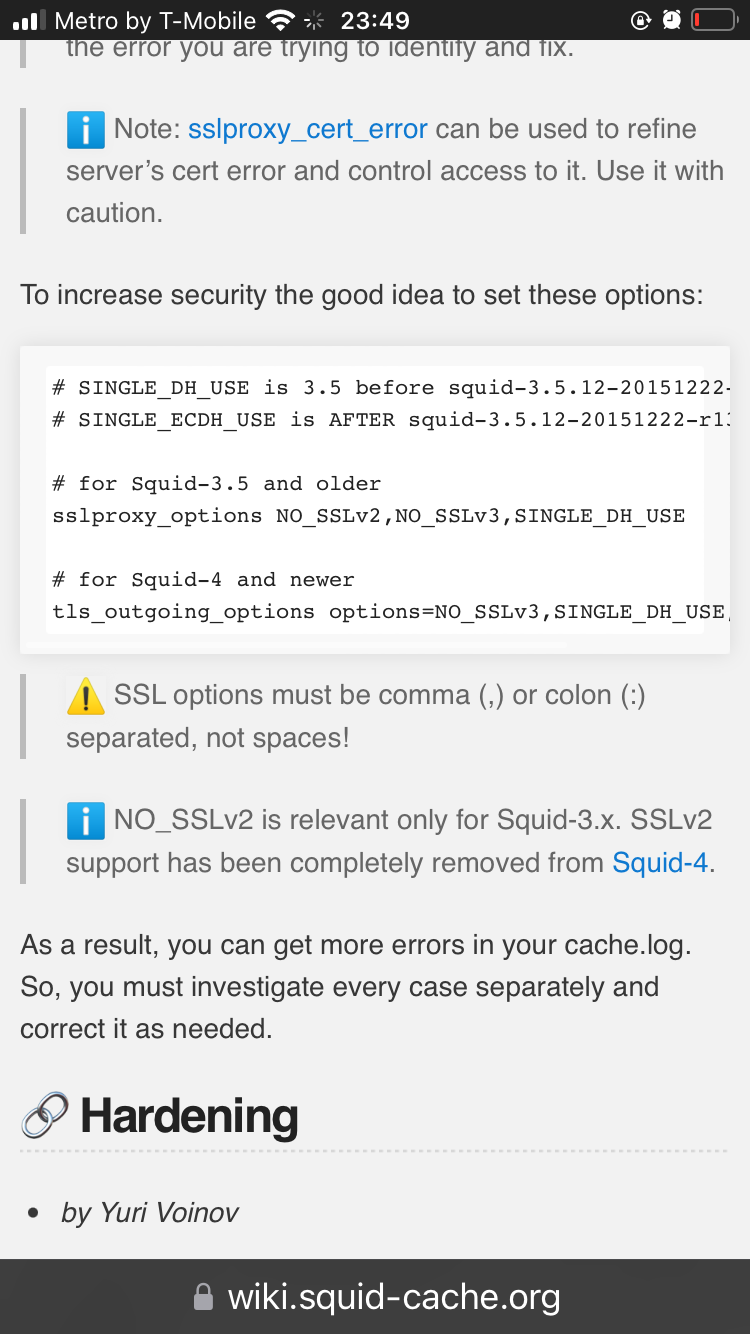
https://wiki.squid-cache.org/ConfigExamples/Intercept/SslBumpExplicit
You might have a certificate issue
-
Hi,
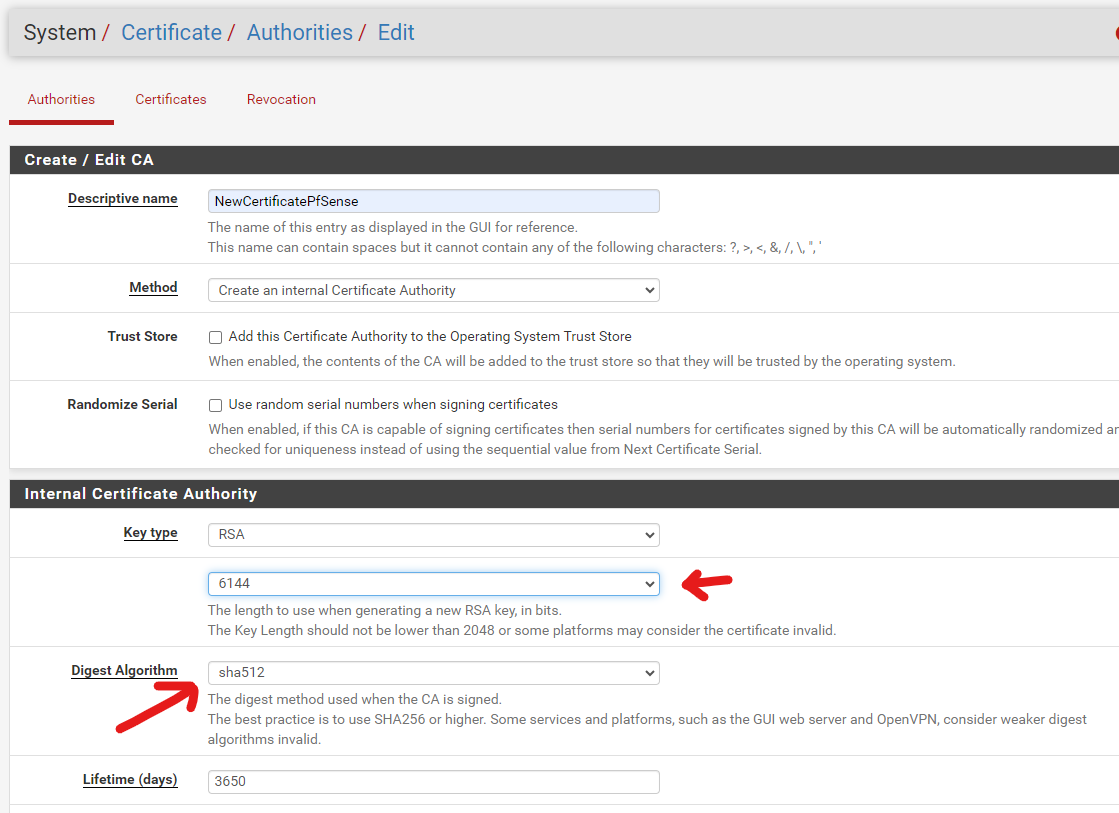
I added a new certificate and assigned it to squid.
the result is always the same
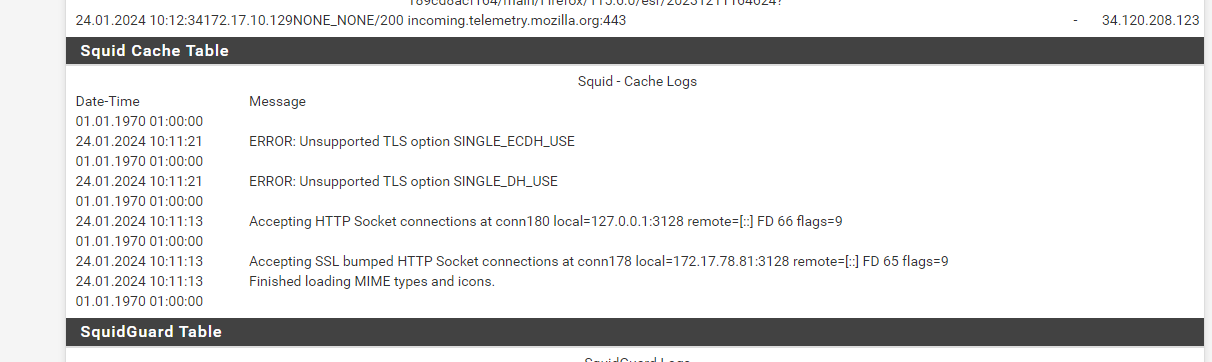
where 172.17.78.81 is proxy
and on client
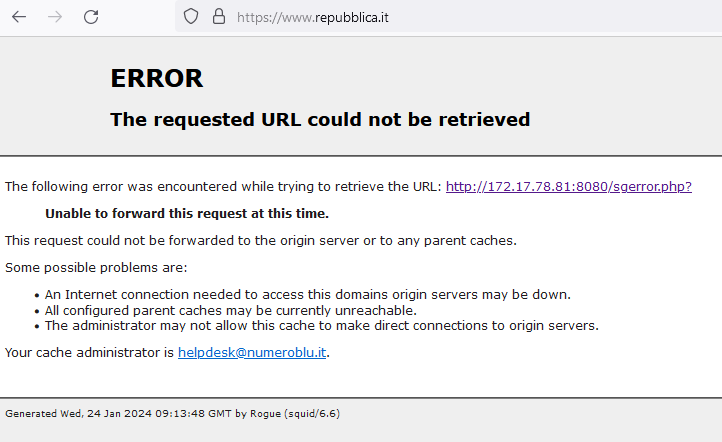
What other tests can I do?
Thank you
-
Try to change settings in this area and see if the error goes away..
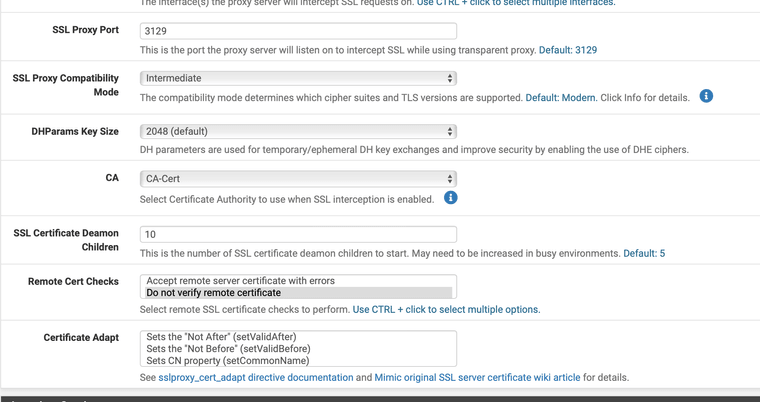
Also try to make the SSL certificate with OpenSSL in command line and import that one into pfSense so its made with Squids application
"Step 1. Configuring the root Certificate Authority (rootCA)
This is probably the part that is most confusing for people and why their setups have failed, Squid need to have a CA assigned to it so that it is able to decrypt parts of the HTTPS header so that it can determine what to do whit that traffic, otherwise all traffic is passed.I used the built-in openssl tool of pfSense to generate this rootCA, for this you need to ssh in to your firewall or connect to it over console, when at the console menu select option 8 Shell, when you are at the shell prompt you need to manually edit the openssl to give you the necessary prompts and questions for you to configure the rootCA
vi /etc/ssl/openssl.cnf
under the [ REQ ] option change the following line from: prompt=no to prompt=yes
under the [ V3_REQ ] option change the following line from: basicConstraints=CA:FALSE to basicConstraints=CA:TRUE
Then save and quit (to save and quit vi editor use :wq!).
Now we would make a known location in the filesystem to save our rootCA and key file as they need to be imported into pfSense GUI at a later stage, I like to use /tmp for any temporary filesCommand:
mkdir /tmp/ProxyfilesNow move to the folder you created whit:
cd /tmp/ProxyfilesWhen you are in this folder you are ready to start the openssl tool and start to create your rootCA, you start whit generating your KEY file by running the command:
openssl genrsa -out myProxykey.key 2048
This will create an rsa key file named myProxykey.key that we use to sign our rootCA whit in the next command for generating the pem file for the rootCA
Create a pem file signed whit key using command:openssl req -x509 -new -nodes -key myProxykey.key -sha256 -days 365 -out myProxyca.pem
This will prompt you to answer some questions to generate the needed pem file in my case it is as below, you need to change this for where you are
US []:NO - Country code
Somewhere []:Oslo - State or province
Somecity []:Oslo - Your city or town
CompanyName []:IT-Monkey - Name of your company or business, "make something up if you are a home user"
Organizational Unit Name (eg, section) []:IT-Department - What part of the company issued the cert, can also be left blank
Common Name (eg, YOUR name) []:Admin - Your name or identity in the company
Email Address []:admin@it-monkey.local - Your contact emailAt this point you should have 2 files in your /tmp/Proxyfiles directory
myProxyca.pem
myProxykey.keyThis can be double checked whit command:
ls -la
If both are there then you are ready to download them and exit the shell environment and continue to the GUI of pfSense, if not you need to look over any error or try again.
To download these files I like to use WinSCP as its fast to navigate and find the files you want to move you can also do this from pfSense Diagnostic -> Command Prompt option and select the file path of:
/tmp/Proxyfiles/myProxyca.pem
/tmp/Proxyfiles/myProxykey.keyIn the download box, this is somewhat slower to navigate but works just fine.
Now as you have these files on your desktop or computer you need to open them in a text editor, I prefer Notepad++ as it's able to adjust the formatting layout of the text but any text editor will work as you will need to copy paste the information in these files to fields in the pfSense GUI.
Navigate to System -> Cert. Manager -> CA's
Here you want to add a new CADescriptive name: SquidCA
Method: Import an existing Certificate Authority
Certificate data: Copy \ Paste the info from myProxyca.pem file
Certificate Private Key: Copy \ Paste the info from myProxykey.key file
Save and apply"Ref:
https://forum.it-monkey.net/index.php?topic=23.0 -
How as this compiled ? With Clang? I want to compile one for me I am using the arm processor
-
@Michele-Trotta what is the IP address of your firewall is it 172.17.78.81?
Is that cider network included in the allow use of proxy area under access control list in Squid?
-
can the proxy portion of this be handled by haproxy instead of squid?
if squid is gonna be such a pain about this then...?all of my research said it can absolutely be done. you won't get the inline virus scanning of clamav but i'd think you could piggy-back another device running linux and clamav (or any antivirus package) to perform the scanning we want before sending it on to the requesting client on the backend..
yes?/no?
-
@jc1976 If you want to run another device you can also run squid on another device haproxy can't do web caching or certificated ssl inspecting
-
Hi everyone,
I also created new certificates with openssl but with the same results posted yesterday :-(Pfsense is installed on a traditional test server with IP address 172.17.78.81 where Squid+Squidguard has been configured and with few firewall controls.
What other tests can I do?
Thank you
-
@Michele-Trotta said in Squid 6.5 !! Nov 6th:
Hi everyone,
I also created new certificates with openssl but with the same results posted yesterday :-(Pfsense is installed on a traditional test server with IP address 172.17.78.81 where Squid+Squidguard has been configured and with few firewall controls.
What other tests can I do?
Thank you
Hello Michele, Hello Everyone !
I've been following the conversations but I just haven't had time to respond. At least say "hi" here now to say that.
As soon as I have time, I will do more tests regarding these reports and try find the fixes/solutions.
Very thanks for this report @Michele-Trotta
@JonathanLee
I am having problems with dependency packages compiling against the available public repositories. Without knowing exactly the tunings used in ARM environments (which are closed in the Netgate repository), I find it difficult to find a solution.With more time, I will study the environment a little more.
Thanks!
-
i'm not concerned about web caching.. really, with internet speeds the way they are, unless you're running dial-up, not having it is not a deal-breaker..
regarding haproxy not being able to do cert ssl inspection; again, that might not necessarily be a deal breaker. if i'm wrong correct me, but from what i've read/researched/etc.. it can decrypt and re-encrypt ssl/tls certs.. so, in a transparent proxy scenario, when https traffic comes in from the wan, it would be decrypted, FULLY inspected by suricata/snort and then it could either be re-encrypted and sent onward to the clients on the lan side, or sent through another device that's inline for antivirust scanning, either clamav, or anything else at that point.. a lot of commercial AV packages are available for linux, so you could run a simple linux machine.. yes, it adds complexity, but it also adds flexibility by not being limited to a pfsense package that may or may not be available down the road.
It's great that people are devoted to keeping the package going, but what happens when they grow tired of it? keeping those packages going takes a TON of time and effort. What will happen when BBCan decides he can no longer be the sole developer of pfblockerng for example? from what i've read there are only a few people working on keeping squid afloat. unless they get a cash infusion with more devs to reinvigorate the project, it seems like it's days might be numbered..
i HOPE i'm wrong. -
https://forum.netgate.com/topic/186331/new-squid-6-7-and-clamav-1-3-0