Taming the beasts… aka suricata blueprint
-
go into suricata and disable inspection on each interface and save the settings. then you will see something along the lines of "DISABLED" on each of your interfaces in suricata.
Then go to diagnostics - tables and make sure the snort2c table is empty.
After all interfaces say DISABLED or something along those lines and your snort2c table is empty, you are no longer inspecting with suricata and can rule it out of your troubleshooting.
-
Thank you very much for your reply :-) !
I already did all your proposed topics - the snort2c table was always empty …
My next step will be to uninstall Suricata to - hopefully - get the final confirmation whether it is related to Suricata or not …So thank you very much for your help once again - I will - of course - replay if there are still some troubles
Have a nice week-end :-) !!
-
OK …
Suricata is uninstalled, unfortunately there are still interruption of Internet :-[I also figured out, if I unplug the WAN-cable an plug it again - it works again …
Even it ist not related to suricata, is there someone how can lead me to some topics I can read to continue to look for the root-cause ?
Any help is highly appreciated :)
Thanks a lot in advance !
-
Did you try those tests I suggested? What was the result, did any of them restore access?
Steve
-
Resaving the WAN settings.
Yes I did, I was able to connect to Internet.
Running ifconfig DOWN/UP on the WAN.
No, did not :-[
To be honest, I do not know what exactly I have to do - sorry :-[[quote]Disconnecting and resconnecting the WAN Ethernet cable.
Yes, that was my last test (Internet OK)Dariusz
-
Ah Ok. Interesting.
So to manually bring down and rebuild the interface run at the CLI or from Diag > Command Prompt:
ifconfig em0 downThen:
ifconfig em0 upWhere em0 is your WAN interface, swap that for whatever interface your actual WAN is.
If that brings back up your connectivity then it shows that simply reloading the existing settings in pfSense can do it. Physically re-connecting it also resets whatever it's connected to and re-saving recreates the settings if they are lost.
Check the system log to see what events were triggered when you ran that. There should be something there to point to the problem.Steve
-
Thank you Steve,
I will check that if this failure occurs again :)
My interface is re0 …Dariusz
-
Hi All,
Very new to Pfsense, just started to research snort and suricata. Came to this post and have read through it but still stuck. I am using Pfsense 2.3.4 and open VPN client with PIA, I have NAT setup to direct lan / wan to the PIA interface. I have a firewall rule for lan on LANnet to use the PIA DHCP gateway.As soon as I apply the below instructions, my internet access shuts down. Note only interfaces I have are LAN, WAN, PIA, OpenVPN (not used and does not exist, not sure why its on the list)
"Next up Floating tab:
Set up a rule but make these changes:
Action Block
Quick TICKED!!!
Interface Hold CTRL and click on all interfaces EXCEPT LAN(admin) and SYNC
Direction any
Source any
Destination any"I think I am misunderstanding this portion
"Head over to an interface's tab and set up a an allow rule. Source should be the interface's subnet. The destination should be any, and for the ports use the outgoing_ports alias created above. Destination should be any. Otherwise identical to the webgui rule. Warning! This allows any host to access any other host on other interfaces using those ports. If this is not needed (and generally it shouldn't), finish the rule, and head over to the floating rules tab."
What am I supposed to do here? The floating rule takes precedent over all other rules 1st, any rule after this would still be blocked no? I added another LAN firewall rule and set source to LANNet and destination ports to the outbound port alias and no luck.
Any tips?
Thanks!I’m also confused by this part of the first post in the thread. I realize it’s pretty old but I’m sure a lot of new folks start searching around to learn about setting up their firewall and end up reading this thread. That being said, is there any reason to setup a floating rule that blocks all traffic? It seems like a better way is to simply delete the rule that’s automatically created on the LAN interface that allows outbound traffic to ‘any’. By doing that, aren’t you blocking all traffic both in (by default based on how pfSense is designed) and out of your network? From there, simply create rules on the interface for your specific needs (i.e. HTTP, HTTPS, DNS, IMAP, etc.). If I’m understanding this correctly, this would only allow traffic that I specify outbound.
So again, what is the purpose of setting up a floating rule to block all traffic versus the method I mentioned above? The only thing I can possibly think of is that it would block outgoing traffic if it wasn’t originating from your LAN, but for a basic home setup with only one router (subnet), I don’t think it would matter since that’s the only interface outbound traffic would be coming from.
Edit:
I think I figured it out after watching more YouTube videos and doing more reading. I posted an explanation of my understanding of basic firewall rules on the pfsense reddit forum (https://www.reddit.com/r/PFSENSE/comments/79xzqi/basics_on_firewall_rules/?utm_content=title&utm_medium=hot&utm_source=reddit&utm_name=PFSENSE).One thing that still doesn't make sense on the very first post is this section:
Next up Floating tab:
Set up a rule but make these changes:
Action Block
Quick TICKED!!!
Interface Hold CTRL and click on all interfaces EXCEPT LAN(admin) and SYNC
Direction any
Source any
Destination anyMy understanding is that you would want 'Quick' to be NOT SELECTED (i.e. un-ticked). Otherwise, no matter what rules you create, it's always going to see that floating rule first and the frame/packets stop there (unless they are automation rules or NAT rules which will occur before any user defined rule). In other words, none of your user defined rules will be executed. If 'Quick' is NOT SELECTED, this would still assess that rule first, but it wouldn't apply it until all of your user defined rules have been assessed and none of them were applicable.
-
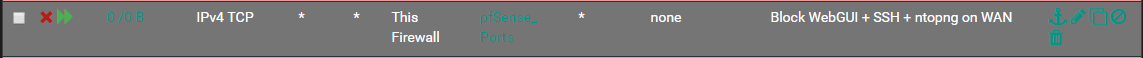
In your firewall rules you need to set the destination port range to the webgui ports you just changed
-
Thank you for this great guide. Question though. If one is on Openvpn how does that change this configuration and would interface of vpn provider be treated as wan or just set same rules on vpn interface.
How is the security effected by using openvpn as related to this topic.
-
@shred yup, I've been there, I also got confuse about that. but that rule is to block other interface to access management port. some of the link or pictures of this guide did not retrieve when netgate upgrade their forum.
-
 N NollipfSense referenced this topic on
N NollipfSense referenced this topic on