Blocking SSH - Firewall Rule Troubles - SOLVED
-
Hey guys, so, long story short (maybe), I have 2 pfSense boxes setup as CARP master and backup, both with dual WAN connections running BGP with a routed subnet to us via our ASN. These are running 2.2-release. I keep getting scanned and hammered by SSH attacks, and I'm having a problem blocking them - I'm pretty sure I have SSH blocked every way I can on my interfaces, but they still get through.
Following are the related rules I have, top down (identical on both boxes, only running IPv4). I will call interface our BGP routed subnet is on Public for reference.
WAN1:
Block source Any to WAN1_network port SSH (it's a /29, so this rule should cover the real and CARP addresses)
Block source Any to Public_real port SSH
Block source Any to Public_CARP port SSHWAN2:
Block source Any to WAN2_Network port SSH (also a /29 subnet)
Block source Any to Public_real port SSH
Block source Any to Public_CARP port SSHPublic:
Block source Any to Public_real port SSH
Block source Any to Public_CARP port SSHAgain, those are the top rules in those interfaces. There are some others that block or pass specific things afterwards, with an allow all at the end. I still see piles of log entries showing failed password attempts from outside networks. I prefer to VPN in and then do anything I need from there, so I would like to have SSH inaccessible from the WAN and routed interfaces.
Thanks in advance.
Aaron
-
you do understand there is a default deny on any wan interface.. Unless you opened ssh on it or in floating there would be no way that 22 would be open.
What are you wan rules? Can you post the screenshot. Your floating tab?
example here are some blocks from my log, default rule blocks this.. So if your seeing password attempts you have some rule allowing it.

-
Yah, I understand how the default "implicit block" rule works. My floating tab is empty. Here are screenshots of my WAN1 and WAN2 rules.


-
Also, with my understanding of the default block rule, I feel like I shouldn't even need the top couple of rules since I don't allow SSH (or HTTPS) anywhere (except the very last rule to the Public interface), but I tried adding them anyway, with no change.
Also, for reference, the Public subnet routed via BGP is the 64.141.x.x subnet. It looks like most of the SSH attempts come into the Public interface IP (real) of the CARP failover box (based on flow data), although they show up in the System logs of the Master.
-
Well, it seemed like the best approach (or the only one that worked) was to change the port number SSH is on. I really have no idea why the traffic was being allowed through, based either on the default block or even the rules I manually added. I suppose this will do for now.
-
You sure firewall is on??
Sorry but something is clearly F'd up and you need to fix it, if you have 1 port that is getting through, how do you know you don't have all the others? There should be no reason to create those rules, and clearly they are not working anyway.What is your openvpn tab show.. There was something that openvpn was exposing something to real world..
what does
pfctl -srshow for your rules..
edit: Ok one thing that could be the problem is you have a any any rule for public net.. So what exact address are they hitting? For what possible reason would you have such a rule? Any any on your WAN??
-
I'm glad someone agrees that something isn't right here. Thanks. I only have one rule in my OpenVPN tab - allow local net to any.
For the allow any any rule for the Public net, I assumed for the subnet that is routed to us via BGP that I would need to allow that net through the WAN interfaces. I have ~600 residential WiSP customer NATed behind 1-10, and about 180 commercial customers directly on that network (20 and up).
-
I'm baffled with this situation as well and certainly agree that something isn't right. I too would like to block inbound ssh requests from the WAN (while leaving LAN connectivity enabled) and nothing I'm trying is working properly. When I scan my port 22 and the server is off, it obviously won't respond. When I enable the ssh server and scan, it responds without any rules defined (as expected). So then I decided to attempt a rule to allow LAN access but block all WAN requests. I clicked on my WAN tab and my 3rd entry was entered as follows:
block IPv4 TCP/UDP * 22 (SSH) WAN address 22 (SSH) * none
I enabled the server again, with the rule in place, and I was still seeing that the port was open from the WAN. I googled around and figured I might try a floating reject rule as well. I left the previous entry in the WAN rules but added the same as above to my Floating rules. I put this in as the 1st entry. I saved the config, bounced the SSH server (checkbox from System > Advanced), scanned again and sure enough it was still seeing port 22 as open.
I should also point out that I do have OpenVPN enabled as well. I'm at a loss as to what I could try next.
-
Here is the thing.. By default pfsense blocks all inbound traffic to wan.. So unless you create a rule to allow it - its going to be blocked.. Do you have firewall off?
He clearly has a rule that is any any to "public net" My my guess that is what is being hit for him.
I have ssh enabled on my lan, I hit it every day to be honest.. But from public its denied.. I see hits to it all the time, see previous pic.. If its not being blocked you got something wrong in your rules.. Please post your floating rules and wan rules..
-
An interesting article by Fireeye about recent SSH brute force attacks. Almost makes you want to open ssh on the WAN ;D
https://www.fireeye.com/blog/threat-research/2015/02/anatomy_of_a_brutef.html
-
If you want to have fun with ssh, run a honeypot and see the IPs from china light you up like a xmas tree ;)
To be honest anyone that would run a ssh server that allows passwords is asking for trouble, whenever I bring up something that has ssh enabled - first thing I do is enable public key and turn off password auth.
-
block IPv4 TCP/UDP * 22 (SSH) WAN address 22 (SSH) * none
Don't use a source port. Source ports are random. That rule will never match.
Those block ssh rules do nothing because you never pass ssh below them.
What do PUBLIC address and PUBLIC net expand to? You are probably passing the TCP/22 traffic with that last pass any to PUBLIC net rule.
This would be a lot easier to diagnose without all the obfuscation of IP addresses.

 -
So, I did mention it in the original post, but the "Public" net is the one that is advertised by us via BGP. Consider it a DMZ of hosts - 64.141.y.x. To permit routing to those hosts via the two WAN interfaces, do I not need to implicitly allow traffic to them, to avoid the default block rule???
-
Yes.
Please post all applicable interfaces, subnets, and rules. Trying to help you with everything obfuscated is nearly impossible. PM if you must. They're just IP addresses.
-
You would need to allow the services you want to run on those IP.. that sure and the hell wouldn't be a any any ;)
-
So if I am serving Internet to multiple commercial/industrial customers on that network, shouldn't I be passing everything to them and letting them control their own firewalling? I will take new screenshots of all rules and post them in a minute…
-
Okay, soooo….
Shaw WAN (WAN1) - 64.141.127.248/29
Telus WAN (WAN2) - 204.191.241.0/29
Public (~DMZ) - 64.141.125.0/24 - advertised on both WANs via BGPShaw WAN Rules:
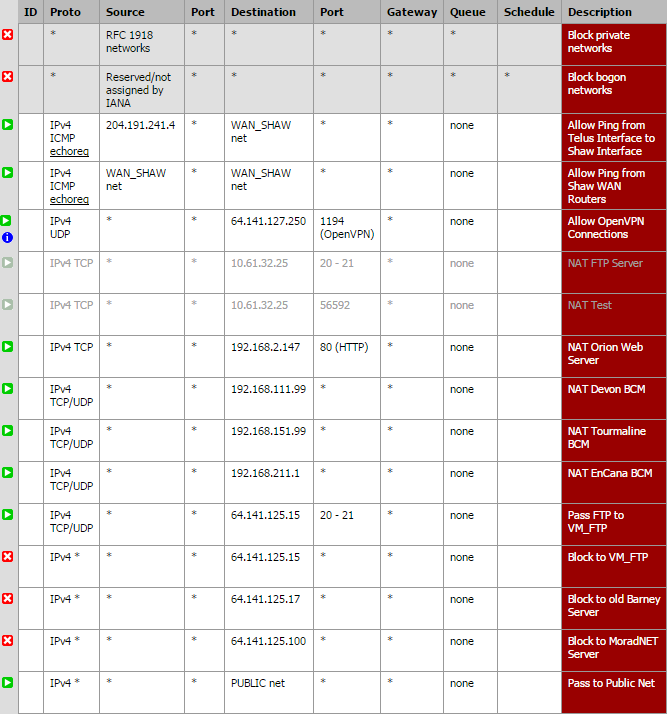
Telus WAN Rules:
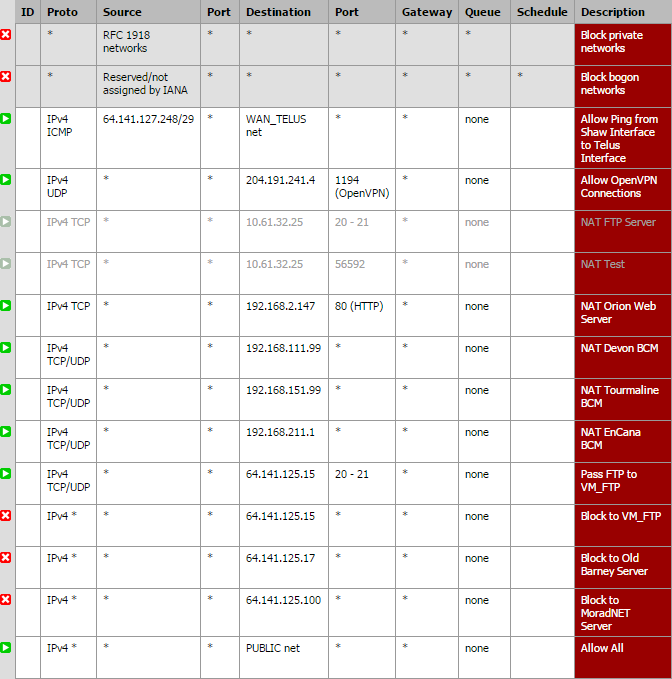
Pubic Interface Rules:

All of these are for VoIP devices - companies host POTS lines here and we connect them to VoIP adapters and transport to their remote facilities via our microwave network.
Also, there are no rules in the floating tab.
-
To be honest anyone that would run a ssh server that allows passwords is asking for trouble, whenever I bring up something that has ssh enabled - first thing I do is enable public key and turn off password auth.
I'm all for more security. What do you mean? Do you use a hardware credential? On these two systems I am the only one that ever uses SSH for access (but limited access).
-
public key auth - look it up. Takes 2 seconds to implement.
So your routing traffic to this segment behind pfsense. So pfsense has an IP in this network, and it listens on ssh because you enable ssh. So block ssh to that interface IP.
So this segment
Public (~DMZ) - 64.141.125.0/24Pfsense is what 64.141.125.1 ?? Block traffic to pfsense IP from the public internet - I agree your customers need to do their own firewall if not using your services for that.
-
That's what I had done originally - I had rules to block SSH to the interface's real IP and the CARP IP. I will add them again right now.