Suricata/Snort on LAN with VLANs enabled
-
Hi,
I am testing Suricata and Snort on SG-2100 box with 4 VLANs. I've increased the pcap size from default 1518 to 1522. Where in the logs is it possible to see which VLAN triggered the alert? I know the VLAN as per my subnet addressing to easily identify, howevever in the SNORT or Suricata widget it only show the parent interface (LAN). I couldn't find the VLAN id in any logs. any idea? -
Neither package actually bothers with VLAN ID information because their capture engines run on the physical parent interface. They see all of the traffic that passes through the interface, but they do not segregate it by VLAN ID.
-
@bmeeks thanks. regarding pcap length. is it correct changing the value to 1522? do you know any tool or website to perform a test, I mean, to force a rule to be triggered? cheers
-
@jorgek said in Suricata/Snort on LAN with VLANs enabled:
@bmeeks thanks. regarding pcap length. is it correct changing the value to 1522? do you know any tool or website to perform a test, I mean, to force a rule to be triggered? cheers
It is generally better to leave the capture length setting at the default. That works in 99% or more of cases.
I strongly suggest users run an IDS/IPS on their LAN interface instead of the WAN. The firewall is already going to block any unsolicited inbound traffic, so why bother wasting CPU cycles inspecting traffic the firewall is going to drop anyway? Put the CPU horsepower to work on the LAN side and inspect only what gets past the firewall (meaning accepted traffic). Also, when you run on the WAN, all local IP addresses behind the firewall are masked by NAT and show up as only the public WAN IP on the firewall. That makes it very hard determine what internal hosts are triggering rules.
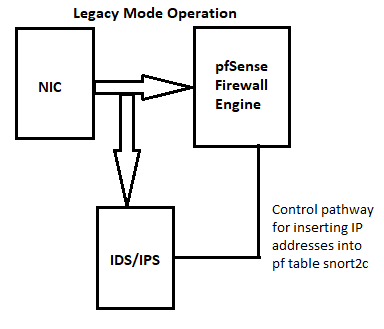
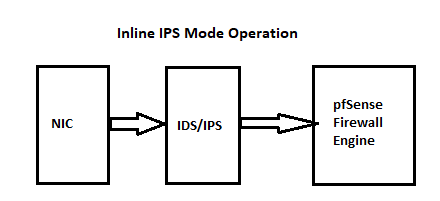
Here are two diagrams that illustrate where the IDS/IPS resides in the traffic path. Notice that traffic will always hit the IDS/IPS before entering the firewall engine.
As for testing, there aren't a large number of options these days due to the extensive use of HTTPS everywhere. You can test from LAN hosts to the firewall's LAN IP address, but many rules will not fire in that scenario because the HOME_NET and EXTERNAL_NET conditions of the rule logic will not be properly satisfied.
-
@bmeeks thanks for your explanation. I will do a test using the default. I had an impression that the default values was not capturing anything and when I've increased I saw some alerts popping up. cheers
-
@jorgek said in Suricata/Snort on LAN with VLANs enabled:
@bmeeks thanks for your explanation. I will do a test using the default. I had an impression that the default values was not capturing anything and when I've increased I saw some alerts popping up. cheers
I don't mean to say "never" change the default. After all, I did put the option there because it is a configuration option in the underlying binary. And for some situations, you might need to change it.
I am just of the opinion that changing defaults in a package should only be done after you fully understand what the parameter is about and what impact changing it might have. Not aiming this comment at you or anyone else in particular. But there are some folks who immediatey begin the equivalent of "pushing all the buttons to see what happens" when configuring things on pfSense. These are the ones that inevitably wind up later posting on the forum complaining and saying pfSense is trash because it isn't working; when in fact they broke it themselves by proceeding with preconceived (and frequently badly wrong) notions of how things work. This seems to happen most frequently in the area of DNS configuration ...
 .
. -
@bmeeks thanks for your reply. I've found the correct size for the pcap length and now I am getting the alerts. Now, I am fine tuning with the ones relevants to monitor ;) cheers
-
@jorgek if you dont mind, can you share your spec and your pcap length? i'm still tweaking my suricata too, thanks.
-
@sysadmin_on_call I am using pcap length of 1522