Creating WebGUI Certificate
-
@gertjan said in Creating WebGUI Certificate:
It would be nice to put also IP's (RFC1918 !) into the SAN list ....
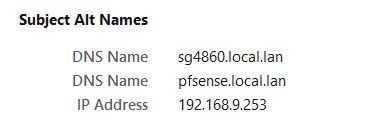
yeah I doubt they would ever allow that - but you can for sure do that when you create your own CA and create your own certs.. I have devices local IPs listed as SAN for all the certs I create - this way if have to access via IP if dns is down for some reason, I don't get warnings about the cert, etc..
example here are the sans for my pfsense
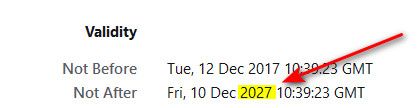
There are many advantages to just creating your own certs when they are going to be used just locally. Before the browsers use to balk at how good the certs was good for, you could do it once and never have to worry about them expiring..
Issue with your own CA, is you have to make sure your devices/applications(browsers) are going to trust that CA. This at times might not be possible depending on what is going to be accessing the resource via https.. But for local resources that only you or your devices you manage and can have them trust your CA.. it does have advantages.. Any domain, RFC1918 sans, etc. And if you want to get tricky, you could back date the certs to time before browsers only allowed like 1 year certs.. See my pfsense gui certs is good for 10 years ;)
At some point I will be changing these all out, since I do want to move to home.arpa vs my current local.lan.. Just haven't gotten around to it yet.. At that time unless do some changing of date time on the CA, etc. going to be limited to 1 year certs because most browsers now balk at certs created after specific time that have longer valid time..
-
I fully agree : for my local devices like pfsense, and Syno, several printers and airco, I don't need Letsencrypt certs.
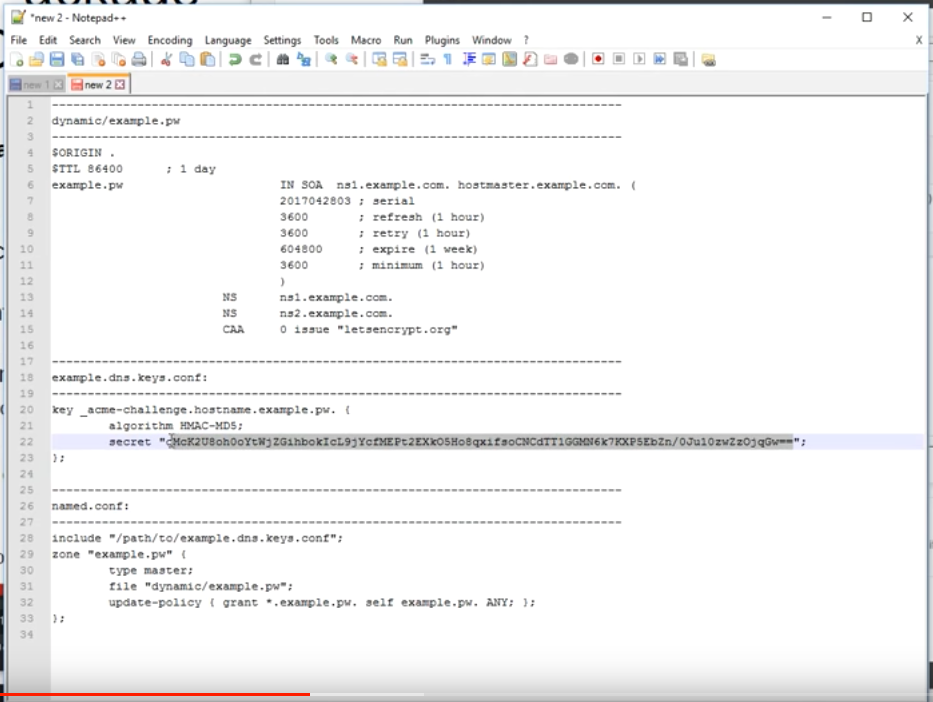
I'm running several web sites with multiple domains, and a mail server for all these domains thus I 'need' Letensrypt. I was using certbot before, switched to acme.sh afterwards as it is just 'one shell script'. I wanted to understand how the automation of obtaining cert worke, as it was an annual job, en somewhat complicated. Certs are used everywhere these days.
It was a small step from jimp saying : "Letsencrypt for pfSEnse ? : probably not", to "here is the Letensrypt pfsense package". A I had already everything set up on the 'DNS' side, it was a click-and-done for me.Btw : Your home made certs are valid until 2027.
Mine areNot after [indefinitely]
-
@gertjan said in Creating WebGUI Certificate:
Not after [indefinitely]
How did you do that?
Yeah I use the acme package for some certs on services I provide to the public, its pretty slick. I ran into some issues with cert being updated via dns and cloudflare - but that was easy corrected by changing the dns sleep setting from default of 120 to 180..
Since that change have had no issues with renew of certs. ACME for sure has many use cases, I just don't see making much sense for my local devices like my printer web gui, or my switches, or my unifi controller.. Some of these are a pain to change or update the cert.. And having to do it every 90 days would be PITA.. There is no way to automate renew of the certs on such devices/applications.
I might be able to automate it on my nas, but why? I am the only one that access the DSM, and if used acme couldn't put in a rfc1918 san, etc. And would need to use a public domain vs just my local one..
While I like the idea of no expiration for certs on your local devices.. When I created them I was like there is no way in hell I would still be using these things 10 years from now.. For sure the hardware would be replaced, and or some change in certs or domain or something that would require me to change within a 10 year period ;) heheh
-
@johnpoz said in Creating WebGUI Certificate:
How did you do that?
Of course I have a date, always 30 to 90 days in the future, for the validity.
With "indefinitely" I meant to say : one less thing to maintain. -
@gertjan ah ;)
Unless the auto fails for some reason.. And in my previous post I gave some examples of stuff that just can not be automated anyway.. There is no way could automate the cert on my switches or printers for example. While it might be possible on my nas or unifi controller.. 10 years makes sure I don't have to worry about it either ;)
Setting the cert on the unifi controller software is a real PITA.. I really wish they would just enable setting that in the gui, etc. They also need to update their ssh so you could use modern keys and ciphers.. But the AP are running really outdated dropbear..
Hallway-BZ.6.0.12# dropbear -V Dropbear v2017.75 -
OK one of these days read think learn improve
Wow Thx guys!
-
@johnpoz said in Creating WebGUI Certificate:
And if you want to get tricky, you could back date the certs to time before browsers only allowed like 1 year certs.. See my pfsense gui certs is good for 10 years ;)
Very creative here, indeed!
@gertjan said in Creating WebGUI Certificate:
Not after [indefinitely]
Wow, definitely the best!
-
So, this morning I decided to create a certificate using the certificate manage to make a root CA, then intermediate CA, and the certificate...the browser (Opera) would still not accept it. Wished I had saw John's date trick.
So for the time wasted, I just bought a domain to use specifically for my home-office-lab network and be done with that.
As a suggestion to Netgate, all community pfSense Plus accounts should come with a real certificate for Webgui...let's make it happened.
-
@nollipfsense said in Creating WebGUI Certificate:
As a suggestion to Netgate, all community pfSense Plus accounts should come with a real certificate for Webgui...let's make it happened.
Nope. Certificates are not something you put to a product so browsers don't complain. Its a tad more complicated.
As for the time wasted, If you didn't import custom root ca to your browser, what do you expect?
-
Hummm.
Here it is : Opera Not Accepting Certificate (solved) with the same players, the same questions, and the answers.
There is even the ancient TLS certificate--can I make a fake CA?.
Today, we're in 2022. Browser can/could 'hard code' the list with trusted CAs. Be aware.
Remember : a certificate will get trusted if and only if the browser has a copy of the original "CA" in it's local storage.
Also, if you visit your pfSense GUI with https://192.168.1.1/ and your certificate has only "mypfsense.local.lan" as it SAN, this will produce an error.
Two choices :
Add the IP in the SAN.
Visit your pfSense using https://mypfsense.local.lan/ - now the certificate matches the certificate, which is why you use a certificate the first place.Every device you use to visit your pfSense GUI has to have the CA (chain) imported first.
-
@netblues said in Creating WebGUI Certificate:
As for the time wasted, If you didn't import custom root ca to your browser, what do you expect?
I am using the latest Opera exclusively for pfSense that does not allow the root certificate to be imported...it relied on the MacOS and that also would not import that certificate. This is not my first time dealing with certificates...I am a Mac veteran on the platform close to forty years.
It seems that my waste of time statement appears as a rude remark; however, none intended...I really have a lot to do on my plate and wished I never embarked on the webGUI certificate. I lived with it for several years so far.
-
@gertjan said in Creating WebGUI Certificate:
Two choices :
Add the IP in the SAN.
Visit your pfSense using https://mypfsense.local.lan/ - now the certificate matches the certificate, which is why you use a certificate the first place.
Every device you use to visit your pfSense GUI has to have the CA (chain) imported first.I had tried that, first, using both the host/FQDN (nolli.lan) then got the insult that it's not a real FQDN...then, tried the IP only to find Google wanting to resolve it and quickly switch to Duckduckgo which I use exclusively on all devices. I never visited any site using Opera as it's only for pfSense webGUI.
I gave up and registered a domain after that. Not sure why MacOS Keychain would not import the root CA certificate and instead placed the certificates (all three) in login. In fact, the original pfSense webGUI was in login as well. -
@nollipfsense said in Creating WebGUI Certificate:
atest Opera exclusively for pfSense that does not allow the root certificate to be imported...it relied on the MacOS and that also would not import that certificate.
What are you trying to import... You sure and the hell can import trusted CA.. I don't care what freaking browser or OS your using.. Failure to be able to do that would be the death of that OS or browser.. Nobody would use it that could say who or not they trust or don't trust..
My guess is you were trying to install the cert vs the CA as trusted..
-
@johnpoz said in Creating WebGUI Certificate:
@nollipfsense said in Creating WebGUI Certificate:
atest Opera exclusively for pfSense that does not allow the root certificate to be imported...it relied on the MacOS and that also would not import that certificate.
What are you trying to import... You sure and the hell can import trusted CA.. I don't care what freaking browser or OS your using.. Failure to be able to do that would be the death of that OS or browser.. Nobody would use it that could say who or not they trust or don't trust..
My guess is you were trying to install the cert vs the CA as trusted..
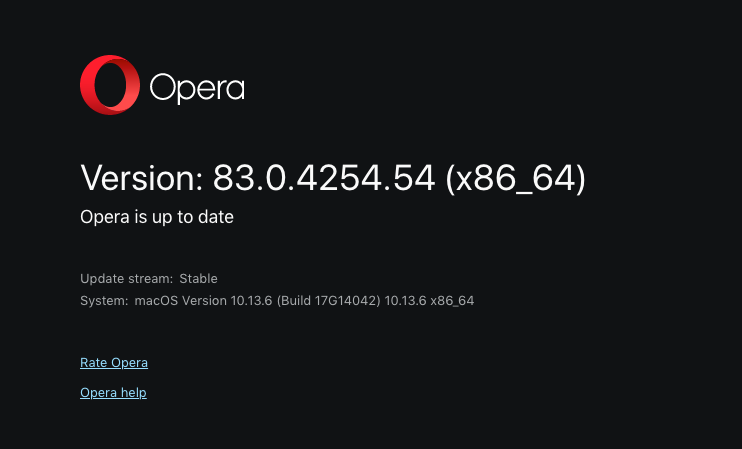
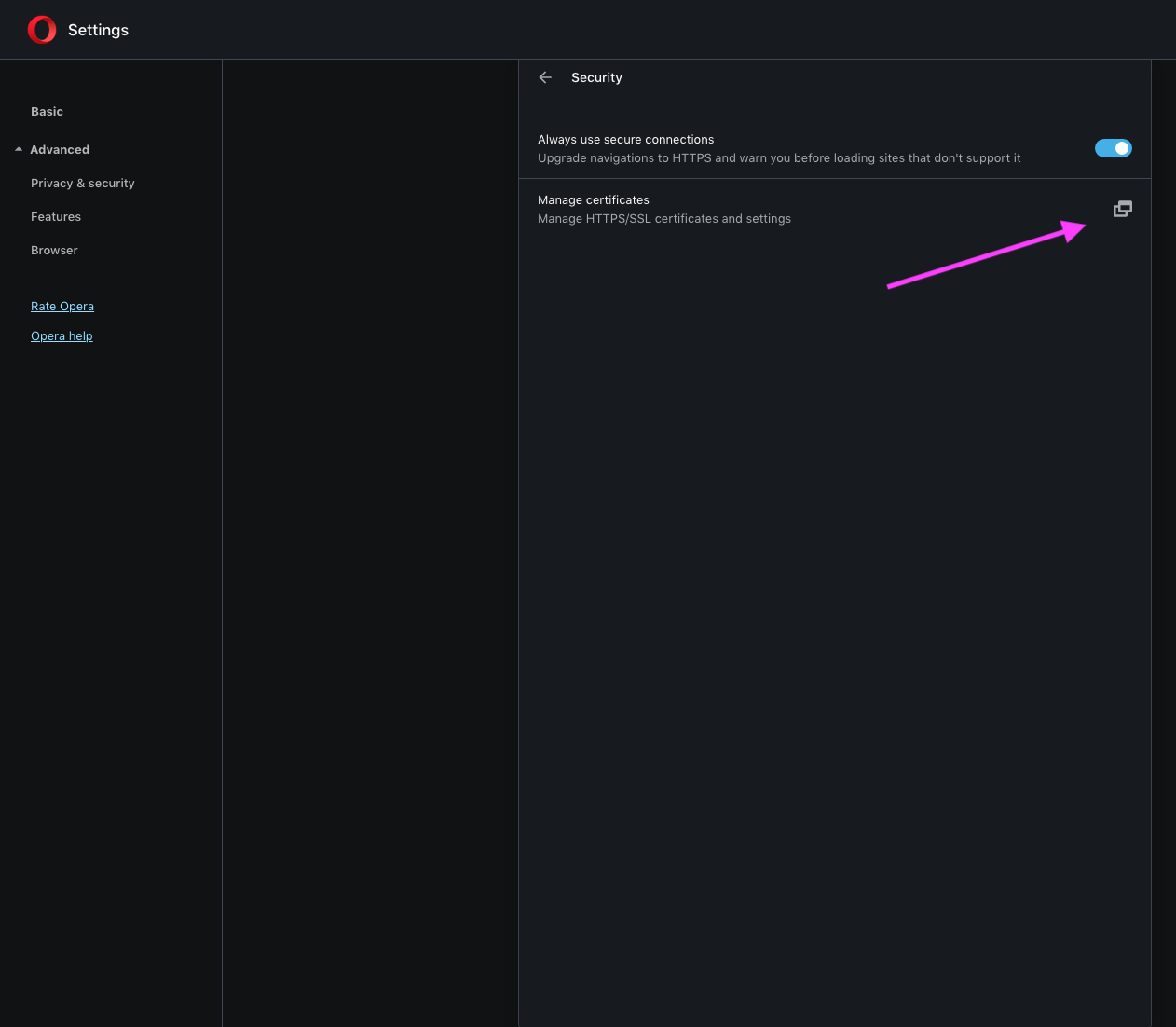
Below is Opera showing it's up-to-date and below that is a screen shot showing manage certificate (arrow point)...when one clicks on that, on a Mac, it opens Keychain Access...there is no import certificate button on that Opera page. Hope someone with a Mac can replicate; to make sure mine was not installed properly when I drag it to the application folder. Also, if one import the certificate into Keychain, it places it under login for the user and not in the root. I tried several times, even tried dragging it to root...no luck, would not go. Note: the certificates were set to always trust after importing into Keychain.
-
@nollipfsense said in Creating WebGUI Certificate:
the certificates were set to always trust after importing into Keychain.
The CA cert.. wasn't this all gone over back in 2019
https://forum.netgate.com/topic/144141/opera-not-accepting-certificate-solved
-
@johnpoz said in Creating WebGUI Certificate:
@nollipfsense said in Creating WebGUI Certificate:
the certificates were set to always trust after importing into Keychain.
The CA cert.. wasn't this all gone over back in 2019
https://forum.netgate.com/topic/144141/opera-not-accepting-certificate-solved
John, it seems that I have been a fool for awhile...haven't learn jack sh*t. I had looked earlier in Firefox and that allows one to import the certificate with a dialog box just as you showed in your Opera 60 in that thread; however, there is no such dialog box in Opera. I might use that other browser that I had mentioned and used in that thread.
-
@nollipfsense I do not have mac to play with.. But I could for sure install opera whatever the current version is on my windows box. Doesn't matter if the browser stores CA it trusts in its own store, the store for the OS.. But you need to trust the CA that signed the cert, be that public be that one you created yourself..
Along with any intermediate ca's etc. that you might of created, etc. I don't really see the point of doing intermediate CA on a home setup, on really the only reason to do any of it locally https is to stop the browser from complaining.
I mean who what would be sniffing your own local traffic over your own secure network in the first place, so what does it matter if the traffic is https or http.. Problem with http only these days is more likely your browser will balk at you that its not "secure" ;)
So personally I don't see the point of going through the extra steps of creating an intermediate CA, etc. Just create your local CA, create/sign whatever cert you want for your service with its fqdn as the CN, as the SAN and add any other SANs you might want to access the service with be it rfc1918 IP or some other fqdn... This should stop your browser from complaining..
Here I just installed Opera.. version 83.0.4254.47
Clickly clicky and there you go my home CA is now trusted.. As you can see I went to pfsense IP and error about not trusted. Install my CA and now trusted.
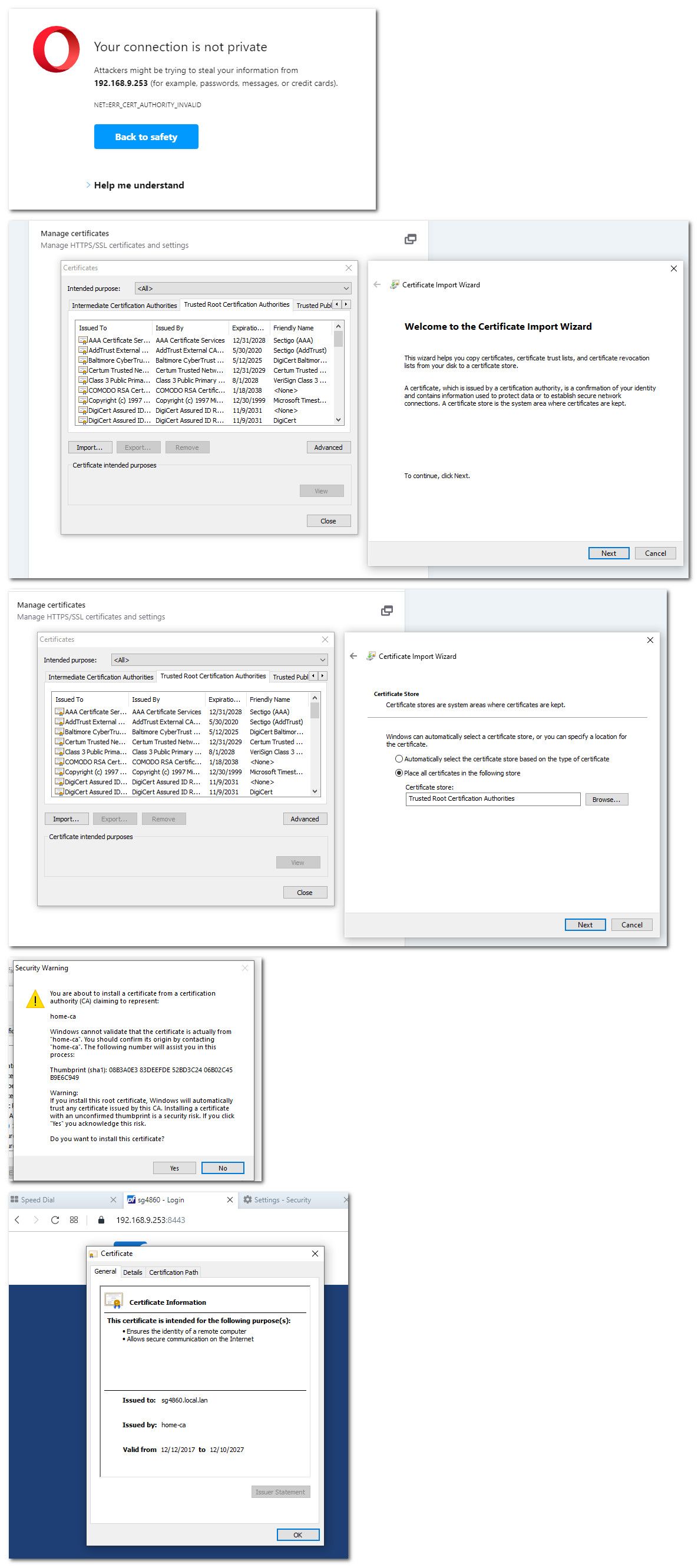
That took all of like 20 seconds to do - including the download and install of the browser.
edit: then another 10 seconds to uninstall it ;) And set firefox to be default browser again - wtf, it never asked me if opera should be default, it just did it.. Ugggh that is not nice!
-
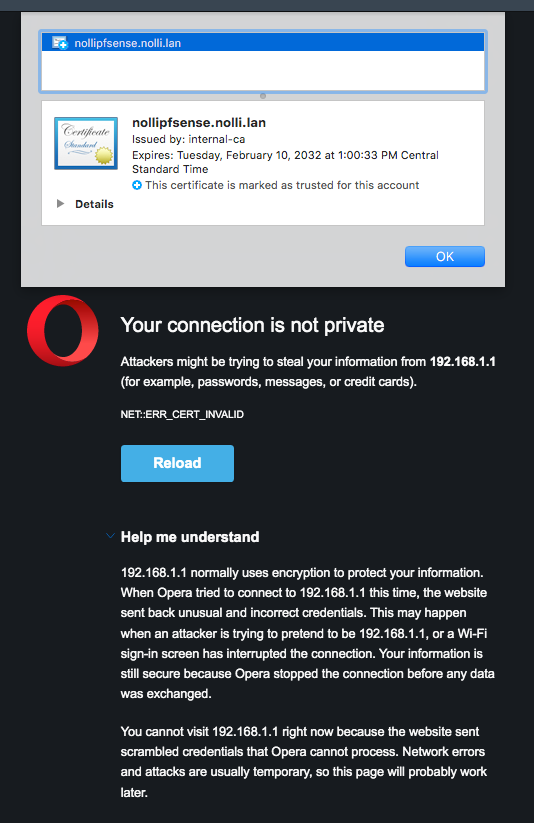
@johnpoz John, I tried again...not sure what I am doing wrong...I give up again. I have the root CA in system for all users, and the intermediate CA as well as the certificate in user login...all marked trusted in Keychain. As you can see, the certificate marked in the screen shot.
-
@johnpoz This time I know what's the problem...it's embarrassing I forgot to change the port to 443 or 4443 as I had it on port 35; so, I am locked out as I don't think restarting webGUI from the console CLI will resolve...gone take a nap. Download 2.6rc later.
-
@nollipfsense That is not a CA cert that is a cert.. And if you just issued a cert that is good til 2032 no browser is going to take it.. They can only be good for like 1 year now.. Or 398 days..
You need to install the internal-ca cert and trust it.. But even if you did browser not going to like that cert since its valid too long.. You would have to have issued it before the new limits were put in..
"after September 1, 2020 with a validity period greater than 398 days will not be trusted by Apple’s Safari browser and iOS/iPadOS/watchOS/tvOS devices."
"Thus, effective Sept. 1, 2020, Mozilla, Google, and Apple will no longer trust any newly issued certificates with a valid lifespan of longer than 398 days."
So for yoru browser to trust that cert good until 2032, it would have had to been issued quite some time ago.. Which you could prob trick by dating your system you have your CA on, etc. Back into 2019 or something.