Pass all trafic via OpenVPN client
-
I have installed OpenVPN client on pfSense and it is reporting it is
upand operational.What next? How to ensure traffic is going to it? How to pass all trafic via OpenVPN?
-
@dimskraft
Its a good advice to assign an interface to the client instance.
Firewall > Interfaces > Assignments
Assing an new interface to the client (e.g. ovpnc1), open its settings and enable it.Then you have to configure the Outbound NAT on the OpenVPN interface.
If you outbound NAT is in automatic mode, maybe pfsense added rules automatically. Otherwise you have to change into hybrid mode first, then add a rules to the OpenVPN clients interface according to the existing WAN rules.If you want to direct all upstream traffic over the VPN go into the clients settings and add the line
redirect-gateway def1to the Custom options.
-
@viragomann why configure NAT on pfSense? Doesn't VPN server do this? Can I configure normal routing to VPN?
-
@dimskraft
You have to NAT the source IP in packets, when they are going out on the VPN interface to the server, otherwise the packets would have a source IP of your local devices, but the the VPN provider don't know this IP and has no route to it. So you'd never get a response.
It's the same behavior when packets go out on WAN to the internet.Doesn't VPN server do this?
The VPN server has to nat the traffic again, when he sends the packets out to the internet, of course.
Can I configure normal routing to VPN?
You can either policy route the traffic in case you only want partial traffic to route over the VPN, or you may enter specific networks in the client settings at "Remote Networks".
In both cases you can remove "redirect-gateway def1" again. But in you upper post you said you want to route the whole upstream traffic to the VPN server.But it's not recommended to set static routes to remote VPN endpoints, because the route will fail if the VPN connection is not established.
-
I have 3 wans and in the end I want to connect all of them to remote ovpn server to avoid usage round robin gateway group feature. So I can't tell to route all traffic to ovpn because I will have 3 of them.
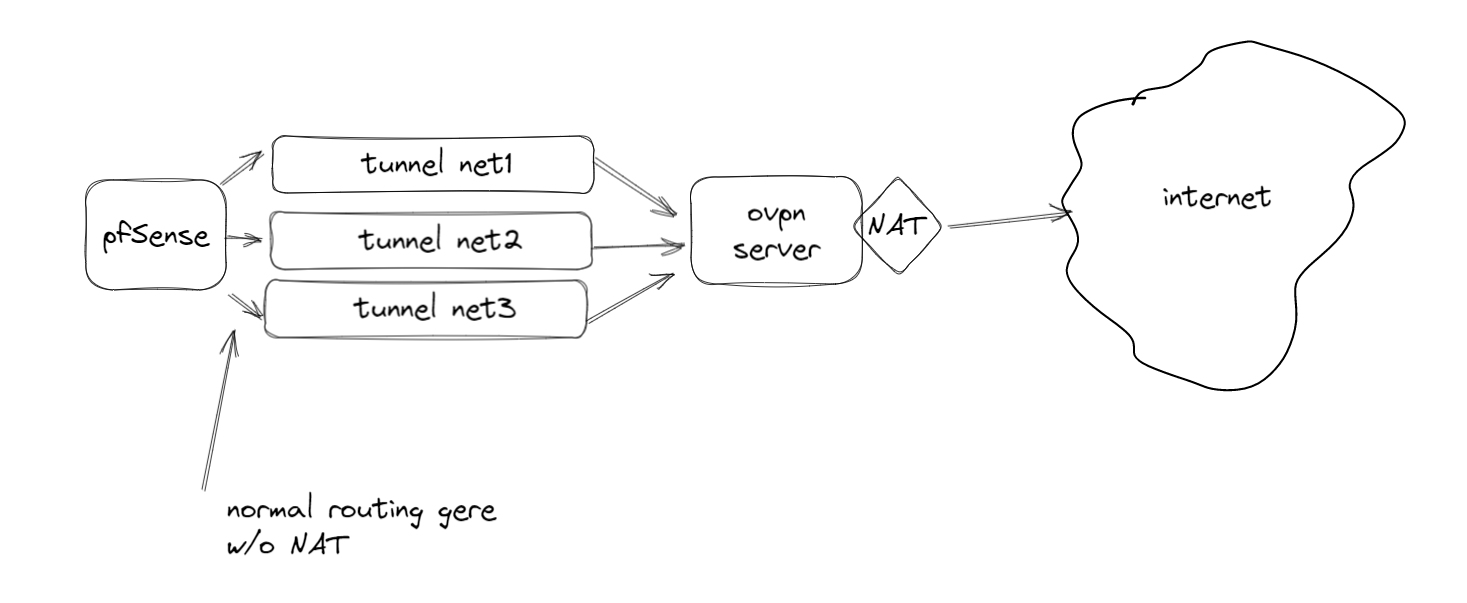
But currently I am trying to understand, how to do this with one ovpn connection.
I have created ovpn client
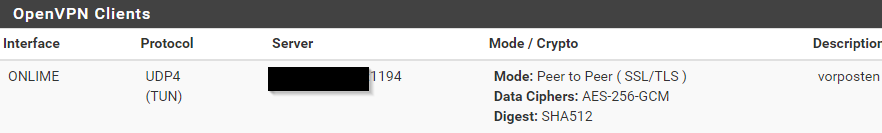
it works
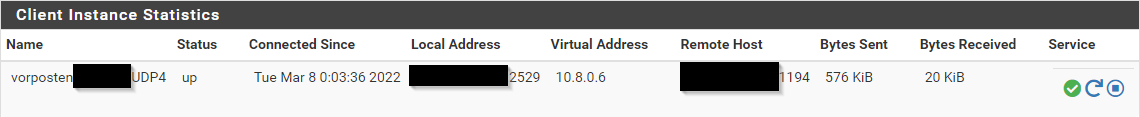
(btw it ignores my explicit virtual address setting)
I have created interface,
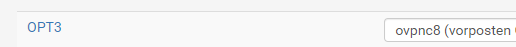
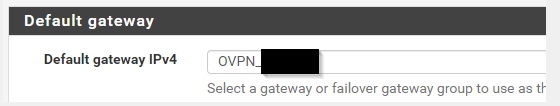
I have created gateway with this interface
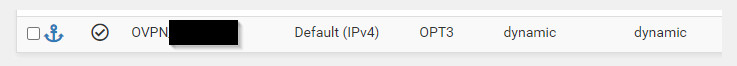
and set it as default
also have added firewall rule for it
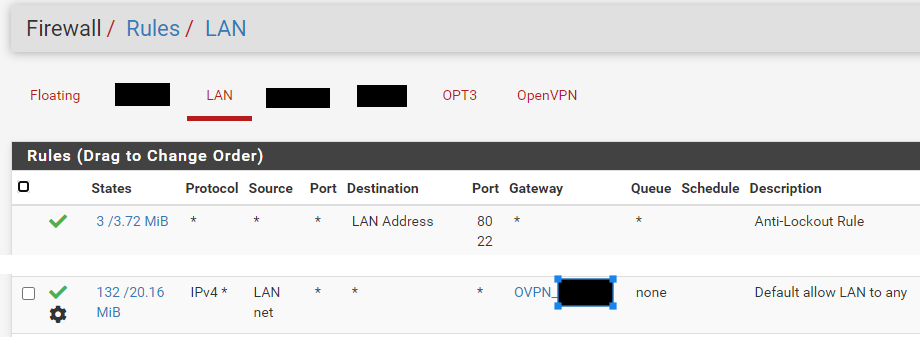
But everythong is ignored and traffic goes via normal WAN
What I am doing wrong?
-
@dimskraft said in Pass all trafic via OpenVPN client:
I have 3 wans and in the end I want to connect all of them to remote ovpn server to avoid usage round robin gateway group feature.
That's not necessarily a reason for using a VPN server.
If you have a gateway group for round robin for whatever reason, you can add an additional one with gateway prioritization using the same gateways and use this gw group in policy rouging rules for the concerned traffic.(btw it ignores my explicit virtual address setting)
The virtual IP is given by the server, especially in an site-to-site connection.
I have created interface,
I have created gateway with this interfacepfSense adds the gateway automatically if the VPN is set up properly. So you'd better remove this again.
and set it as default
That's a pretty bad idea. I think, I mentioned that above already.
Do not add static routes for VPN gateways.also have added firewall rule for it
But everythong is ignored and traffic goes via normal WANSince the rule already matched some traffic before (possibly before changing the gateway), it should also match after.
But maybe you had open connections, which are not affected by the changes. You probably have to flush the states.Also consider that a policy routing rule directs all matching traffic to the gateway, hence it doesn't allow any internal access. So you might have to add additional rules for that, e.g. DNS, without stating a gateway.
-
@viragomann sorry, still don't understand, how to stop traffic from passing to normal gateways and pass it to openvpn client instead; don't capture general idea