OpenVPN mobile connexion to another remote networks from same server
-
Hi,
My OpenVPN mobile connexion works like a charm with freeradius and 2FA. I can ping what I'm needed at openVPN server side who we will name Site A.
Site A server is client to an OpenVPN P2P tunnel with Site B = this tunnel working normally
My question : How my Mobile OpenVPN client can connect to Site B through his connection to Site A?
On OpenVPN server settings Site A, I tried to add the SiteB networks at "IPv4 Local Networks" without success. I tried to use the option "Inter-client communication : Allow communication between clients connected to this server" without success again.
Maybe I can just push some routes in Custom options?!?!
I need some suggestions or best practice for that please before go further ... I dont want to do that the wrong way!
Thanks
-
@m0l50n said in OpenVPN mobile connexion to another remote networks from same server:
On OpenVPN server settings Site A, I tried to add the SiteB networks at "IPv4 Local Networks" without success.
Yes, you were right, this is needed.
Additionally you need to edit the P2P settings at site B and add the tunnel network of the remote access server to the "Remote Networks".
This ensures that response packets to requests from your mobile client are routed back to site A. -
This post is deleted! -
@m0l50n
Ok I've done waht you tell me ... but problem persist. Do you have any other idea where to check?192.168.7.0/24 Site B
192.168.1.0/24 Site AMobile OpenVPN connect to Site B and I still can access this network but can't ping Site A pfsense 192.168.1.1 or any other IP on that network.
On my Site B router, I make sure the first rule is Allow any source ICMP to Site B LAN network.
Thanks again!
-
@viragomann
Ok I've done waht you tell me ... but problem persist. Do you have any other idea where to check?Mobile OpenVPN connect to Site B and I still can access this network but can't ping Site A pfsense 192.168.1.1 or any other IP on that network.
192.168.7.0/24 Site A (server for mobile VPN)
192.168.1.0/24 Site B (Server for P2P tunnel)
Site A-B P2P tunnel is on 192.168.135.0/24
Mobile VPN to Site A tunnel is on 192.168.137.0/24In P2P config, both server side I've put 192.168.137.0/24 in IPV3 remote network and on client side do I have to add something?!?! Or in CSO on the server?!?!?
Thanks!
Thanks again!
-
@m0l50n said in OpenVPN mobile connexion to another remote networks from same server:
Mobile OpenVPN connect to Site B and I still can access this network
Above you wrote the mobile clients connect to site A.
Now what?In P2P config, both server side I've put 192.168.137.0/24 in IPV3 remote network
At both sites? That makes no sense for routing.
A site-to-site tunnel should have a /30 mask.
Maybe you can provide a drawing of what you have and what you want to achieve for clarification.
-
@viragomann
When I wrote these line yesterday, I said to myself that wasn't clear. And I think I got mixed up with my site A and B ... :)Now it will be clear :
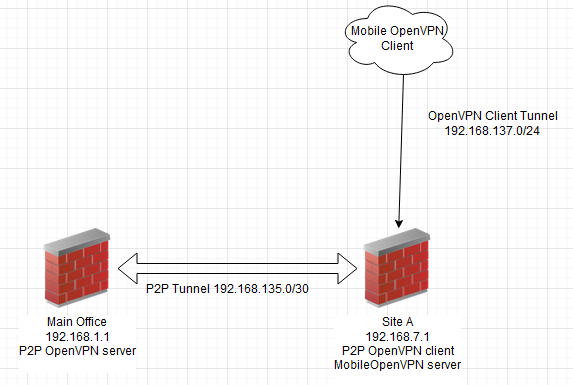
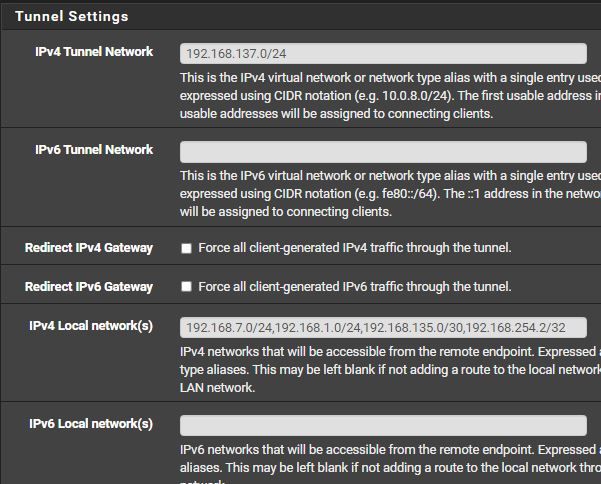
Main Office P2P OpenVPN
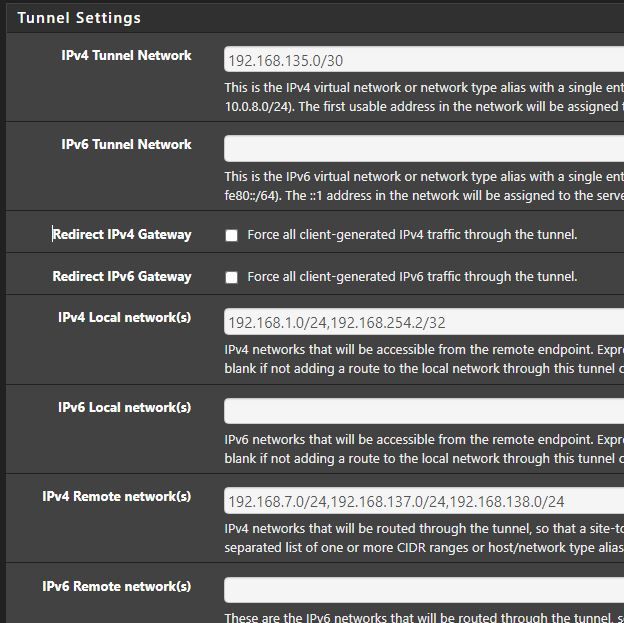
Main Office P2P OpenVPN server CSO
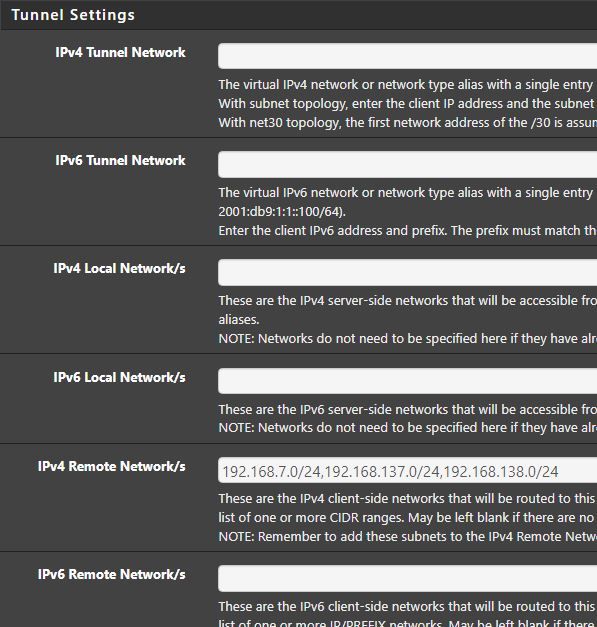
SiteA P2P OpenVPN Client
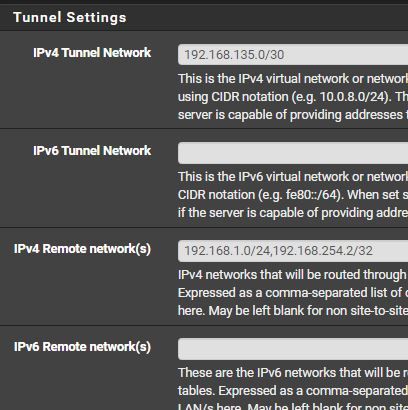
SiteA Mobile OpenVPN Server
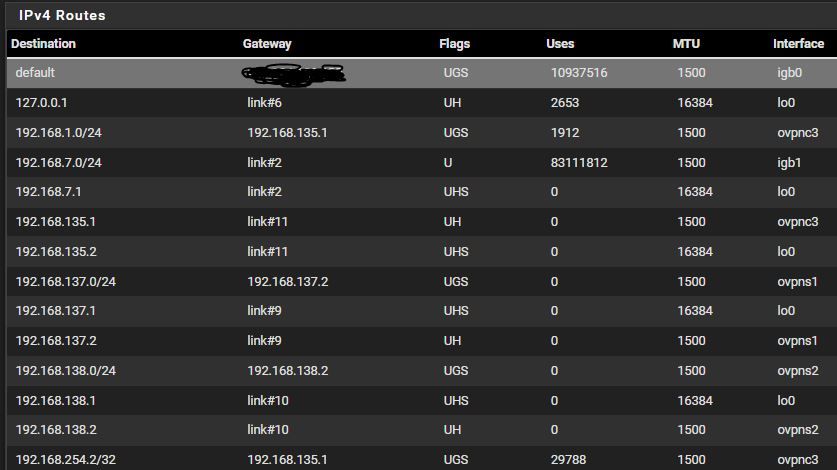
SiteA IPv4 Routes
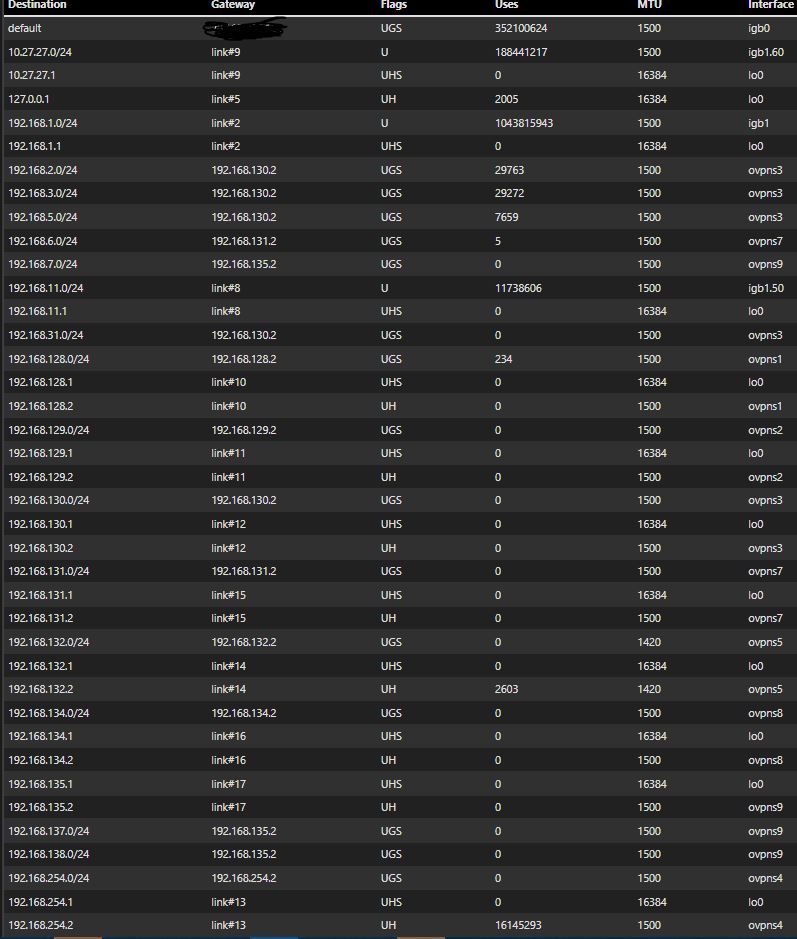
Main Office IPv4 Routes
Thanks again for your help, that's really appreciate!
-
@m0l50n
Well, however, 192.168.1.1 on both sites? That might not be possible.And since you didn't inscribe the images, your settings are still unclear.
Furthermore the routing tables don't match to the map. 192.168.135.2 (the p2p clients virtual IP) is shown in the upper table as local address, which let me assume that it belongs to the client and site B. But the access servers virtual IP 192.138.137.2 is also shown in the same table which should be at A.
Sorry, I'm lost with this. -
@viragomann
I just modify my post and inscribe images .... sorry! I've done that quickly and I though the images name appeared, and the name was to describe!And another error from me : site A pfsense is 192.168.7.1!!!!
Thanks
-
@m0l50n
According to the routing tables the access from mobile clients to the main office should work.
However, the CSO is not needed for a P2P VPN, since with a /30 tunnel the remote endpoints IP is clear. So you should remove it.Also there will be no need to access the P2P tunnel IPs from the mobile client. So you can remove 192.168.135.0/30 from "Local Networks" of SiteA Mobile OpenVPN Server.
Can you access the main office LAN from site A LAN?
Also consider that 192.168.1.0/24 is a broadly used network segment. It's default on many consumer routers.
Imagine the mobile client resides within a wifi using this subnet, he would be unable to access the main office LAN over the VPN in this case. -
@viragomann
According to the routing tables the access from mobile clients to the main office should work.However, the CSO is not needed for a P2P VPN, since with a /30 tunnel the remote endpoints IP is clear. So you should remove it.
I disable the CSO and nothing has changedAlso there will be no need to access the P2P tunnel IPs from the mobile client. So you can remove 192.168.135.0/30 from "Local Networks" of SiteA Mobile OpenVPN Server.
I just removed it ... that was a try I've done yesterday.Can you access the main office LAN from site A LAN?
Yes I can access everything from site A LAN to main office.Also consider that 192.168.1.0/24 is a broadly used network segment. It's default on many consumer routers.
Imagine the mobile client resides within a wifi using this subnet, he would be unable to access the main office LAN over the VPN in this case.I know, that's really bad. But when I was engaged in that company, that's already was like that and I'm always postpone that job because I miss some time to manage all my networks and systems + cybersecurity for 250 employees!!! A lot impacts to change that main Network!After some little modification you just asked, nothing as changed about access to Main Office from Mobile VPN ... but after you confirm me my VPN settings are good, I rechecked my Firewall rules. On SiteA pfsense, the first rules for OpenVPN interface was to Allow all ICMP traffic from Any to some specific IP on Lan A (192.168.7.0) and nothing to Main Office network!!!

I've put an "Any to Any" rules on OpenVPN to test and ping start to works!!!
Thanks, with all your help you help me better understand some notions!
Just to finish, I'm in the first stage to securise my VPN. I dont want to start to touch to OpenVPN rules in my Main office for now. I want to securise the Site A pfsense in first try because this one isn't 100% in production right now ... is it a good idea to restrict traffic from Site A to Main office from site A pfsense LAN interface rules, and restrict traffic from MobileVPN and Main Office to Site A from site A pfsense OpenVPN interface rules?
I really Thank you again for everything! Your skills with pfsense are impressive!!!
-
@m0l50n
Glad that you found the culprit at last.Yes, you can define the firewall rules on any interface on the route. It's okay to restrict the traffic on the OpenVPN interface and allow only specific destinations at A and at the main office.
However, from the security point of the main office, it may be desirable to restrict the access on its incoming VPN interface additionally for sure. But if you have full control over both sites and you can say that site A is save as well, that's not really necessary.